Simulate
Simulate attacks
across any vector.
Evaluate
Know where your
company is exposed.
Remediate
Fix your
security gaps.
Strong defense starts with the challenge of offense
Validate your security posture and the effectiveness of your controls with efficiency and automation across every environment, every day.

Know
Discovery and Risk-Profiled Inventory
Test
Offensive Security Assessments

Prove
Source of Truth Metrics
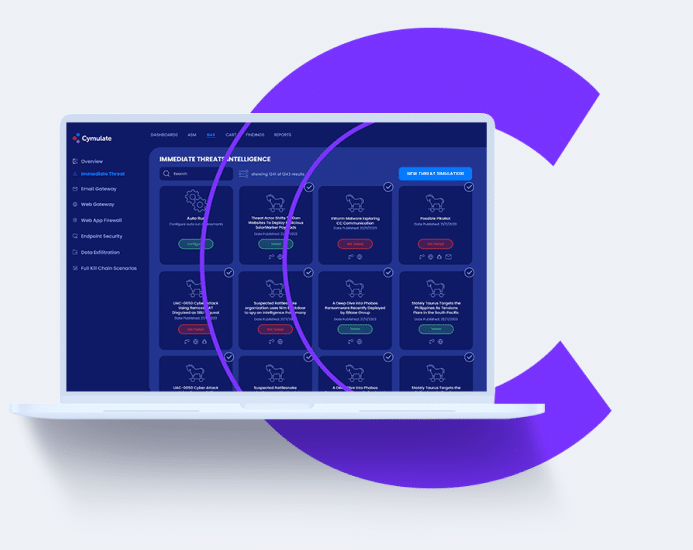
Check Your Security
Posture Now
Book a demo and see the power of Cymulate
security control and threat
validation on-prem and in the cloud
“Cymulate has been helping me to evaluate my security posture against behavior based as well zero day threats.”
– IT Security & Risk Management Associate
“Technical capabilities provided are outstanding, customer service is highly responsive and product mgmt. is flexible in supporting us with our requests.”
– Security Operations Analyst
“The Cymulate BAS is delivering excellent outcomes, contributing significantly to enhancing my security effectiveness.”
– IT Security & Risk Management Associate
“My experience with the platform was exceptional. It delivers on its promises with easy navigation, effective mitigation steps, and top-notch after sales support.”
– Chief Risk Manager
“Always willing to help offering training sessions and encourage use of the product’s additional available features.”
– Senior Software Engineer
“I believe that Cymulate brings a vision of risks, vulnerabilities and actions that we are unable to pay attention to in our work day.”
– Security Operations Specialist
“The range and breadth of attack scenarios, potential targets and how well each tool integrates is really excellent.”
– Penetration Tester
“We had an excellent experience with Cymulate, from product deployment to while using the platform.”
– Senior Cybersecurity Engineer
“Awesome customer Support and techniques used by Cymulate to identify security gaps.”
– IT Security & Risk Management
Learn More

Globee Awards
Gold Winner
2024 Leader
for ASM

Most Innovative
Tech Company

Best Breach and
Attach Simulation
Platform

Top 100
Cybersecurity
Startups

Top 100
Cybersecurity
Startups

Best Breach and
Attach Simulation
Platform