July 13th, 2023
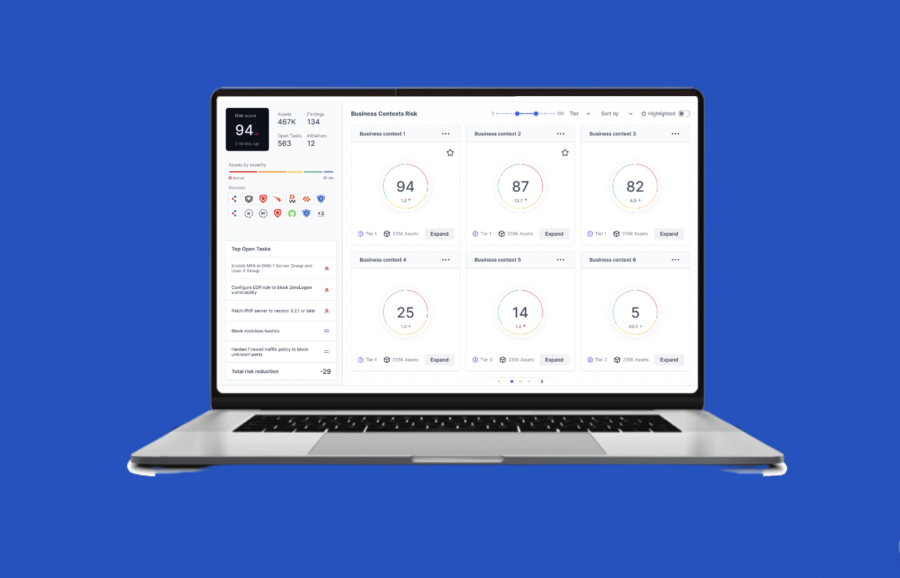
Exposure Analytics: Cybersecurity Evolves to Understand Business Context

July 3rd, 2023
Cyber Threat Breakdown June 2023

June 29th, 2023
Looking Back on the 2023 Dell Technologies World Conference

June 23rd, 2023
Understanding the Ins and Outs of Cybersecurity Exposure Management

June 16th, 2023
Cymulate Responds to cl0p MoveIT Attacks

June 1st, 2023
Cyber Threat Breakdown May 2023

May 21st, 2023
A New Advanced Scenario for Testing Defenses Against Lateral Movement

May 18th, 2023
It’s Time for an Upgrade: The Huawei HG532 Remote Code Exploit
May 11th, 2023
How BAS and CART Improve Incident Response and Recovery

May 9th, 2023
RSA Conference 2023 Was a Coming Out Party for Exposure Management

May 4th, 2023
Cyber Threat Breakdown April 2023

April 27th, 2023
APAC Cybersecurity Wake-Up Call: Reinforcing Resilience is Key

April 20th, 2023
ChatGPT and Data Leakage: Everything Old is New Again

April 16th, 2023
Introducing Internal Asset Discovery and Unified Attack Path Mapping

April 6th, 2023









