Credential dumping is a stealthy tactic used by attackers to extract authentication credentials from systems, posing a serious risk to organizations. To help customers defend against this threat, Cymulate’s Advanced Scenarios templates simulate credential dumping attacks in a controlled environment. This allows organizations to assess their defenses, identify vulnerabilities, and strengthen their security measures against credential theft and lateral movement.
What is Credential Dumping?
Credential dumping, also known as password dumping, encompasses various techniques used by threat actors to extract sensitive authentication credentials such as password hashes and Kerberos tickets. Among these techniques is kerberoasting, a method that specifically targets Kerberos authentication to extract Service Principal Name (SPN) account hashes for offline cracking.
Broadly speaking, this type of attack consists of:
- Gaining unauthorized access to a device, typically its memory where unencrypted usernames and passwords used by the devices’ users may be stored.
- Copying or extracting available credentials.
- Writing this data out to a file that can be readily accessed by the threat actor, or even exfiltrated from the environment.
Once the credentials are obtained, the attacker can use them to access sensitive information on the device or other accounts associated with the stolen credentials. The attacker could also potentially infect other devices on the same network and escalate their privileges by stealing more valuable account credentials, which could lead to the entire network being compromised or taken down. While this outcome (lateral movement) is not simulated in this specific template, it can be simulated with other tools in the Cymulate Platform for further assessment.
Assessing a System’s Resilience to Credential Dumping Attacks
As the primary goal of a credential dumping attack is to obtain data usable at a later stage, it is usually run by stealth and challenging to detect quickly.
The optimal way to defend against credential dumping attacks is to prevent the ability of a threat actor to perform them by building controls and infrastructure that can be observed, tested, and improved upon over time.
While not always possible, this methodology allows the organization to rely less on third-party developers when attempting to combat attacks and has benefits well beyond just preventing credential dumping. Therefore, it remains the best primary methodology for defense.
Simulating Credential Dumping Attacks
The best way to effectively verify that a system is resilient to credential dumping attacks is to run attack simulations that perform the techniques used for credential dumping in a safe and controlled manner. This allows the organization to see how many are capable of completing the dump process, how many are detected, and how many are stopped.
This evidence-based process provides a reliable picture of the system’s resilience to credential dumping attacks, with granular information about the security gaps – if any are discovered – that should be closed to prevent attacks.
Challenges of Simulating Credential Dumping Attacks
Yet, simulating credential dumping attacks can be a time-consuming and resource-intensive process. Accurately testing an organization’s defenses requires careful planning and executing each step of the attack, taking into account the specific technologies and security controls in place. This typically requires skilled professionals to dedicate their expertise to this challenging sequence of tasks at the expense of other operations they could be spending time on. Because of this, either other operations are delayed, or the testing of credential dumping is delayed – with either outcome leading to an unwanted impact on the organization’s security overall.
To aid in avoiding that situation, the Cymulate Advanced Scenarios module offers the ability to create templates that can perform different threat assessments. In the case of credential dumping, Cymulate has created a pre-built template that merely requires some basic variables to be filled in.
Top Credential Dumping Techniques
The credential dumping technique falls under the “Credential Access” category in the MITRE ATT&CK framework and can be launched with a variety of techniques, such as Mimikatz, Pwdump, LSADump, and more.
Cymulate’s Credential Dumping Advanced Scenario template runs the following executions :
- Create Volume Shadow Copy with WMI: This technique involves using Windows Management Instrumentation (WMI) to create a volume shadow copy, which can be used to make a copy of the system’s data and potentially extract credentials.
- Registry dump of LSA secrets: This technique involves accessing the registry on a system and extracting the Local Security Authority (LSA) secrets, which can include password hashes and other sensitive information.
- Registry dump of SAM, creds, and secrets: This technique involves accessing the registry on a system and extracting the Security Account Manager (SAM) database, as well as any stored credentials and secrets.
- Dump All credentials using all LaZagne methods available (Windows): This technique involves using the LaZagne tool to extract all available credentials from a system.
- DCSync using Mimikatz (All users): This technique involves using the Mimikatz tool and the Domain Controller (DC) Sync function to request a copy of the domain’s password hashes.
- DCSync using packed Mimikatz (64): This technique is similar to the previous one but involves using a packed version of Mimikatz specifically designed for 64-bit systems.
- PowerShell DPAPI Unprotect (decrypt) data from file: This technique involves using PowerShell and the Data Protection API (DPAPI) to decrypt data from a file, potentially allowing an attacker to extract credentials.
- Dump SPN user’s hash with Kerberoasting: This technique involves using the Kerberoast tool to request a large number of Kerberos tickets and extract password hashes from them.
- Kerberos ticket with unconstrained delegation: This technique involves obtaining a Kerberos ticket with unconstrained delegation, which can be used to impersonate other users and potentially extract their credentials.
- SpoolSample: This technique involves using the SpoolSample tool to coerce Windows hosts to authenticate to other machines via the MS-RPRN RPC interface, potentially allowing an attacker to extract credentials.
Defending Against Credential Dumping with Cymulate
Cymulate’s Advanced Scenarios module enables organizations to simulate real-world credential dumping techniques, helping identify vulnerabilities in their defenses. By running simulations from the dedicated “Credential Dumping” template, security teams can assess how well their systems withstand common techniques attackers use to extract credentials.
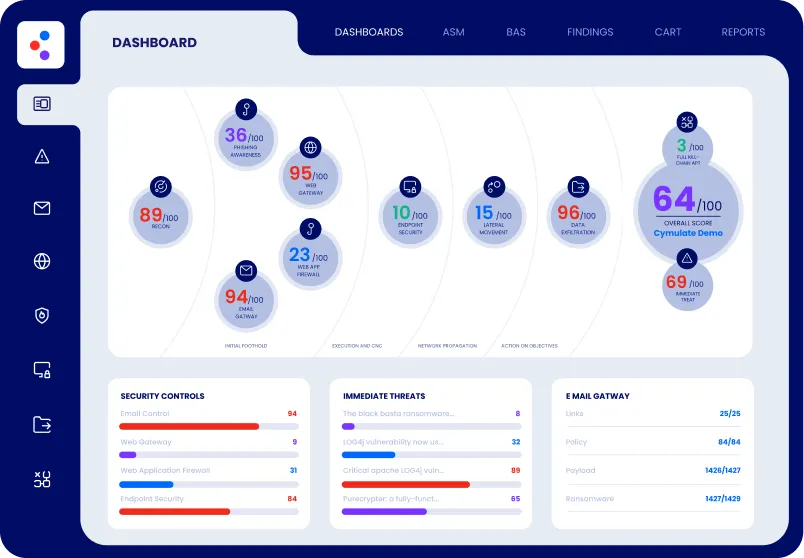
The platform provides detailed results and immediate mitigation guidance, allowing teams to address vulnerabilities quickly. After applying the recommended fixes, organizations can re-run the simulation to ensure the effectiveness of their security measures, maintaining a proactive approach to defending against credential dumping and other credential-based threats.
To see how Cymulate can strengthen your organization’s defenses against credential dumping, book a demo today and experience all the platform’s features in action.