Whitepaper
December 3rd, 2023
Continuous Threat Exposure Management (CTEM): From Theory to Implementation
Whitepaper Translate cyber risk into language that leadership can use…

Whitepaper
March 29th, 2023
The Benefits of Integrating Security Intelligence with Security Validation
Whitepaper As the saying goes, keep your friends close and…

Whitepaper
October 26th, 2022
Healthcare Sector
Threat Exposure Management
Whitepaper The healthcare sector’s rate of data production is higher…

Whitepaper
October 23rd, 2022
APT-Ready
in Four Steps:
Your Action Plan
How can you tell if your security can withstand an…

Whitepaper
September 6th, 2022
Securing Software Supply Chain with Continuous Security Validation
See what it takes to secure your organization against supply…

Whitepaper
September 3rd, 2022
Four Cyber Security Essentials for the Board
Get the four timely cyber security risk metrics, aligned with…

Whitepaper
August 22nd, 2022
Understanding Vulnerability Prioritization Technologies
How does Vulnerability Technology Prioritization make patching easier and more…

Whitepaper
July 3rd, 2022
Outsmart Ransomware with Security Controls Validation
Learn the many faces of ransomware and how to avoid…

Whitepaper
March 22nd, 2022
Are Cyber-Insurance Models Broken?
Understanding how the cyber-threat landscape affects policies and claims for…

Whitepaper
December 8th, 2021
ESG – Helping Organizations Create a Threat-informed Cyber Defense
ESG Report Certainty and confidence in cybersecurity are possible. By…

Whitepaper
May 31st, 2021
Frost & Sullivan Whitepaper on Continuous Security Validation
Get the whitepaper from Frost & Sullivan on how they…

Whitepaper
May 18th, 2021
How to Stay Ahead of Cybercriminals in Financial Services
Download this whitepaper now and learn how to protect your…
Whitepaper
April 28th, 2021
SANS – Contextualizing the MITRE ATT&CK® Framework
Think of ATT&CK as a dictionary and keep in mind…

Whitepaper
February 25th, 2021
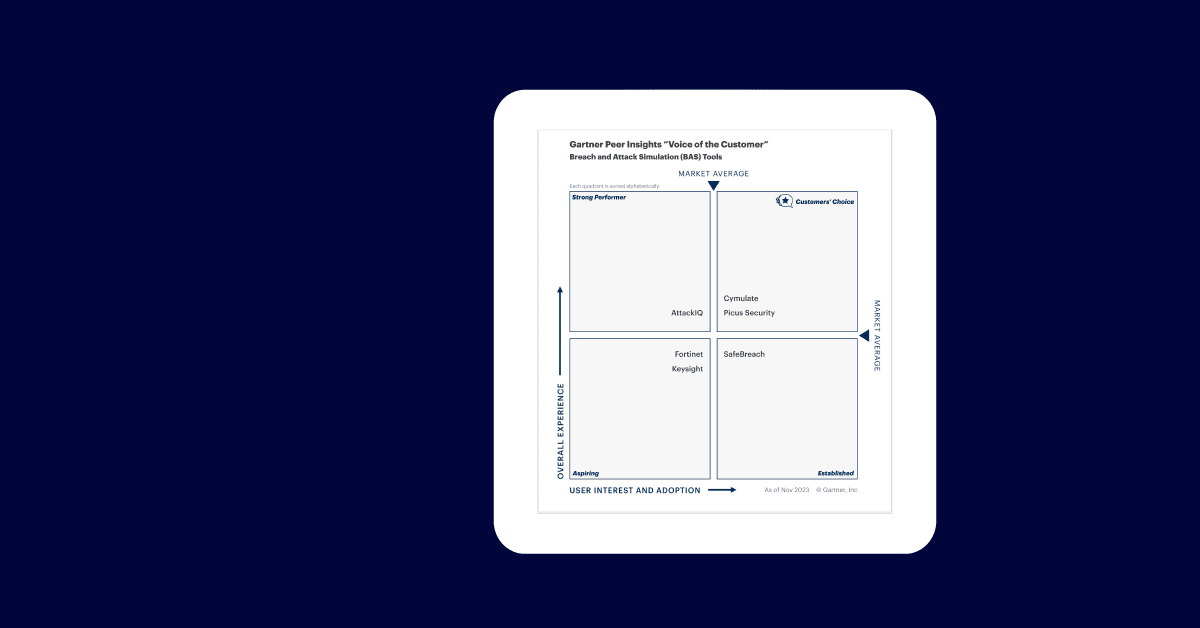
The 3 Approaches to Breach & Attack Simulation Technologies
Which Breach and Attack Simulation approach is best for your…

Whitepaper
February 15th, 2021
Enhance Supply Chain Security with Continuous Security Validation
Integrate automated security validation into enterprise security assurance programs to…