Frequently Asked Questions
Product Information & Overview
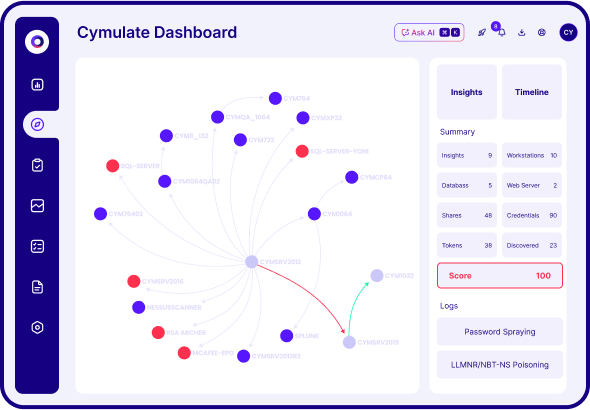
What is Cymulate Attack Path Discovery?
Cymulate Attack Path Discovery is a platform feature that automates offensive testing to discover lateral movement, remediate misconfigurations, and improve threat resilience. It visualizes all potential attack paths, tests privilege escalation, and assesses how attackers could exploit exposures to reach critical assets. Learn more.
What is the primary purpose of Attack Path Discovery?
The primary purpose of Attack Path Discovery is to help organizations proactively identify and visualize all potential lateral movement attack paths, validate network segmentation, and prioritize mitigation of exposures to strengthen threat resilience before an attacker can exploit them.
How does Attack Path Discovery work?
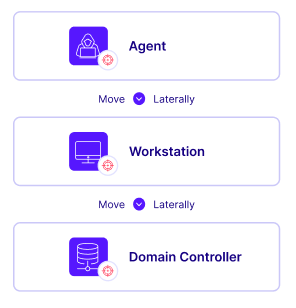
Attack Path Discovery automates offensive testing by running attack simulations that map potential adversary advancement paths, validate network segmentation and access control policies, and deliver actionable mitigation guidance. It uncovers how attackers could move laterally within your environment and reach critical assets. View the data sheet.
What are the main functions of Cymulate Attack Path Discovery?
The main functions include mapping attack paths, testing privilege escalation, targeting crown jewels (critical assets), validating segmentation, revealing hidden exposures, and prioritizing mitigations. These capabilities help organizations visualize risks and take action to reduce their attack surface.
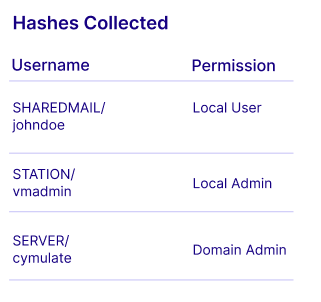
How does Cymulate Attack Path Discovery help with lateral movement detection?
It automates the discovery of lateral movement exposures by simulating how attackers could move across machines, servers, and domain controllers, identifying which endpoints are compromised and what sensitive data is exposed.
What types of exposures can Cymulate Attack Path Discovery reveal?
It identifies access control misconfigurations, weak credentials, trust relationship exposures, and vulnerabilities that could allow privilege escalation or lateral movement within your network.
How does Attack Path Discovery validate network segmentation?
It assesses attack paths across the entire architecture to validate security controls for each segment, ensuring that segmentation and access control policies are effective and resilient against lateral movement attacks.
What is meant by 'targeting crown jewels' in Attack Path Discovery?
'Targeting crown jewels' refers to assessing how attackers can exploit exposures to reach an organization's most critical data and assets, allowing security teams to prioritize protection for high-value resources.
How does Cymulate Attack Path Discovery support continuous resilience?
It enables organizations to validate access control and segmentation policies, strengthen threat resilience, and monitor for drift from the security baseline through ongoing automated testing and actionable guidance.
What out-of-the-box templates are available in Attack Path Discovery?
Cymulate provides out-of-the-box templates for common attack techniques such as SMB Pass-the-Hash and LLMNR Poisoning, making it easy to simulate and test for these exposures.
Features & Capabilities
What are the key benefits of using Cymulate Attack Path Discovery?
Key benefits include automated offensive testing, visualization of lateral movement paths, validation of segmentation, identification of hidden exposures, and actionable mitigation guidance to improve protection for high-risk assets.
Does Cymulate Attack Path Discovery integrate with other Cymulate solutions?
Yes, Attack Path Discovery is an integral part of the Cymulate Exposure Management Platform and can be combined with Exposure Validation for full awareness of your threat exposure, enabling more effective exposure prioritization and remediation. Learn more.
How does Attack Path Discovery help prioritize mitigations?
It assesses, prioritizes, and provides guidance to mitigate security gaps, focusing on exposures that pose the highest risk to critical assets, so organizations can allocate resources efficiently.
What is the difference between Attack Path Discovery and traditional penetration testing?
Attack Path Discovery automates offensive testing and provides continuous, real-time visibility into lateral movement exposures, whereas traditional penetration testing is typically manual, point-in-time, and may not cover the full attack lifecycle or provide ongoing validation.
Can Attack Path Discovery validate access control policies?
Yes, it validates access control and segmentation policies by simulating attack paths and identifying misconfigurations or weaknesses that could be exploited by attackers.
How does Cymulate Attack Path Discovery support red teams?
It allows red teams to execute lateral movement and control evasion techniques, map attack paths, understand the potential blast radius of an attack, and identify routes to critical assets within the network. Learn more.
Where can I find more technical details about Attack Path Discovery?
You can find detailed information about Attack Path Discovery on the Cymulate Attack Path Discovery page and in the data sheet.
Does Cymulate Attack Path Discovery offer actionable mitigation guidance?
Yes, the platform delivers actionable mitigation guidance based on the exposures and attack paths it identifies, helping organizations remediate vulnerabilities efficiently.
How does Attack Path Discovery help with compliance and audits?
By validating segmentation and access control policies and providing detailed reports on exposures and mitigations, Attack Path Discovery supports compliance efforts and helps demonstrate security controls during audits.
Use Cases & Benefits
Who can benefit from Cymulate Attack Path Discovery?
Security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries can benefit from Attack Path Discovery to proactively identify exposures and improve threat resilience. Learn more.
What are some real-world outcomes achieved with Cymulate Attack Path Discovery?
Customers have reported measurable outcomes such as an 81% reduction in cyber risk within four months (Hertz Israel), improved detection and response in hybrid environments (Nemours Children's Health), and cost-effective scaling of penetration testing (sustainable energy company). See case studies.
How do customers describe their experience with Cymulate Attack Path Discovery?
Customers praise Cymulate for its ease of use, actionable insights, and ability to quickly identify and remediate exposures. For example, Globeleq's Cybersecurity Head said, "Cymulate helps understand where our gaps are and what we need to do to prevent a real attacker from moving laterally within our environment to reduce the ‘blast radius’." Read more testimonials.
How does Attack Path Discovery help organizations with limited resources?
By automating offensive testing and providing prioritized, actionable guidance, Attack Path Discovery enables organizations with limited resources to focus on the most critical exposures and efficiently improve their security posture.
Can Attack Path Discovery be used in hybrid and cloud environments?
Yes, Cymulate Attack Path Discovery supports validation in hybrid and cloud environments, helping organizations secure complex infrastructures and improve detection and response capabilities. See Nemours Children's Health case study.
How does Attack Path Discovery support vulnerability management?
It enables vulnerability management teams to validate exposures between penetration tests, prioritize vulnerabilities based on exploitability, and automate remediation efforts for ongoing risk reduction. Learn more.
What pain points does Attack Path Discovery address?
It addresses fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies, and post-breach recovery challenges. See case studies.
How does Attack Path Discovery help with post-breach recovery?
By enhancing visibility and detection capabilities, Attack Path Discovery helps organizations recover faster after a breach and ensures ongoing monitoring for new exposures. See Nedbank case study.
How does Attack Path Discovery support communication with stakeholders?
It provides quantifiable metrics and visualizations that help CISOs and security leaders communicate risks, justify investments, and demonstrate improvements in security posture to stakeholders and auditors.
Implementation & Ease of Use
How easy is it to implement Cymulate Attack Path Discovery?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment.
What support resources are available for Attack Path Discovery users?
Users have access to email and chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers and best practices. See webinars.
How do customers rate the ease of use of Cymulate Attack Path Discovery?
Customers consistently praise Cymulate for its intuitive interface, user-friendly dashboard, and actionable insights. For example, a Senior Security Analyst in retail said, "[The] product has been great and easy to use. Cymulate support is always easily accessible and they are a main contributing factor to why the tool is so easy to use." Read more testimonials.
What is the typical implementation timeframe for Attack Path Discovery?
Implementation is rapid due to the agentless design. Most customers can deploy and begin running simulations within a short period, often the same day as deployment.
Security, Compliance & Integrations
What security certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating compliance with industry-leading security and privacy standards. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate uses encryption for data in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and a dedicated privacy and security team including a DPO and CISO. The platform is GDPR compliant and developed using a secure SDLC.
What integrations are available for Cymulate Attack Path Discovery?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. See all integrations.
Is Cymulate Attack Path Discovery compliant with GDPR?
Yes, Cymulate incorporates data protection by design, is GDPR compliant, and has a dedicated privacy and security team, including a Data Protection Officer (DPO).
What security features are built into Cymulate Attack Path Discovery?
The platform includes mandatory 2-Factor Authentication (2FA), Role-Based Access Controls (RBAC), IP address restrictions, and TLS encryption for its Help Center, ensuring robust access and data security.
Competition & Comparison
How does Cymulate Attack Path Discovery compare to Mandiant Security Validation?
Cymulate offers automated attack path discovery that generates all potential routes an attacker could take for lateral movement, effectively identifying security gaps. Mandiant Security Validation does not have an attack path discovery capability. See comparison.
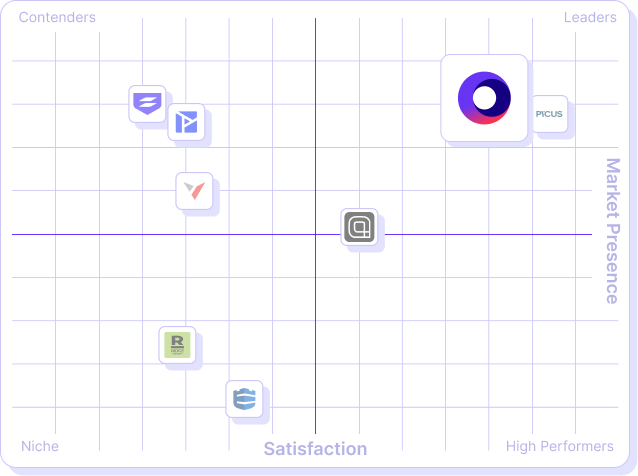
What makes Cymulate Attack Path Discovery unique compared to other solutions?
Cymulate stands out with its unified platform, continuous automated testing, AI-powered optimization, complete kill chain coverage, ease of use, and proven customer outcomes such as significant reductions in cyber risk and increased operational efficiency. See more comparisons.
Pricing & Plans
What is the pricing model for Cymulate Attack Path Discovery?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, schedule a demo.
How can I get a quote for Cymulate Attack Path Discovery?
You can request a personalized quote by scheduling a demo with the Cymulate team. The team will assess your organization's needs and provide a tailored proposal. Book a demo.