Agentic Cyber
Defense Engineering
Continuously prove, prioritize and adapt your security.
Prove the Threat.
Build Exposure-Informed Defenses.
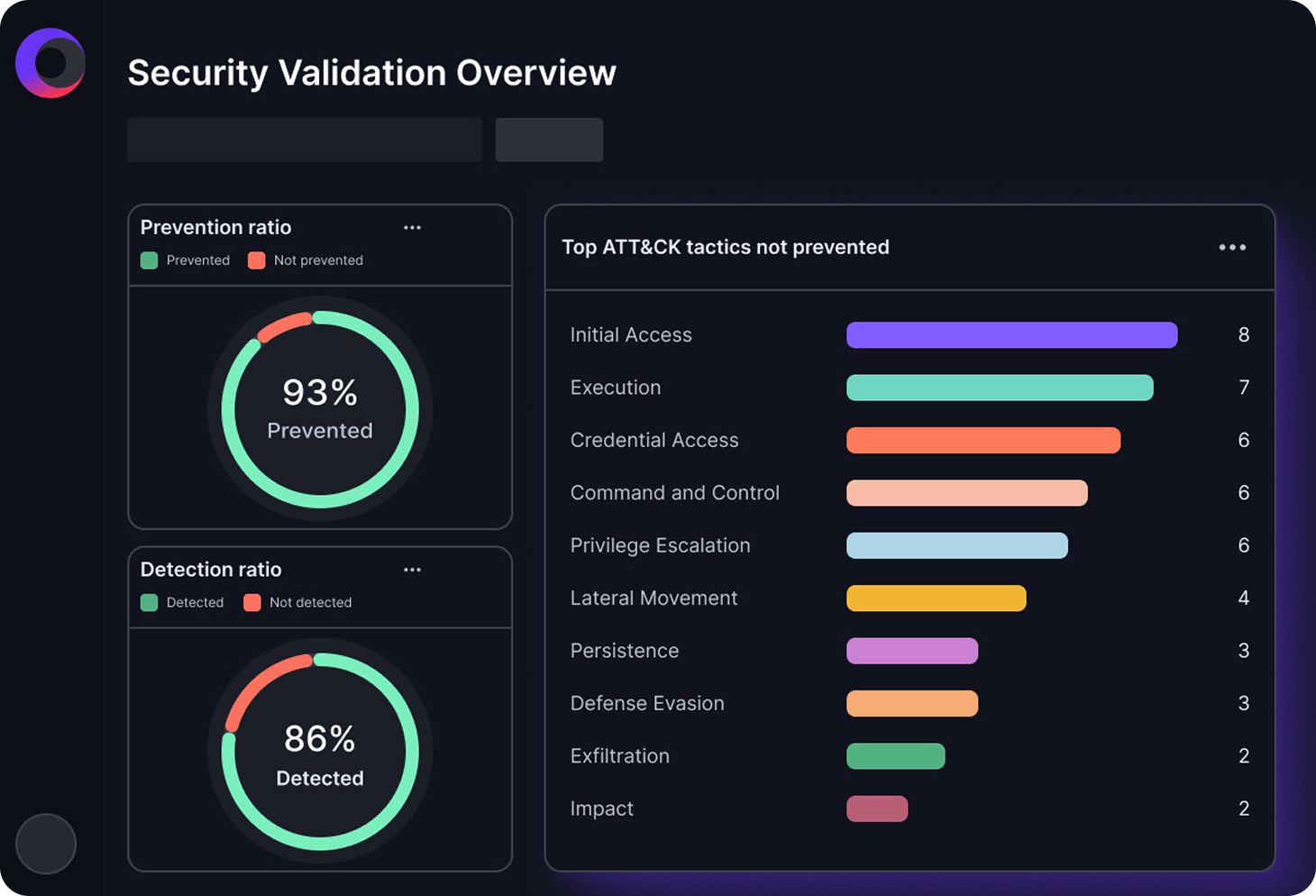
Validate security control effectiveness and test your defenses against the latest threat activity to optimize security before an attack occurs.
The Cymulate Difference
Cymulate turns validation into a continuous, adaptive process of agentic cyber defense engineering. This proactive approach to security includes industry-best adversarial exposure validation, intelligent integrations to the security stack and AI-powered workflows to go beyond validation and engineer security that adapts to your threat exposure.
Beyond validation.
Agentic cyber defense engineering.
Cymulate turns validation into a continuous, adaptive process for agentic cyber defense engineering.
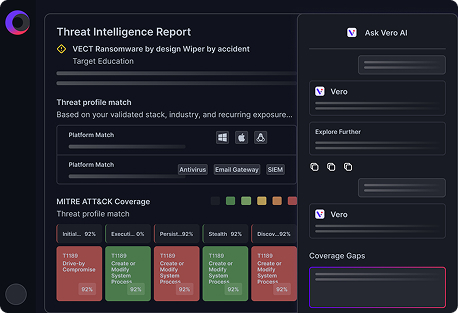
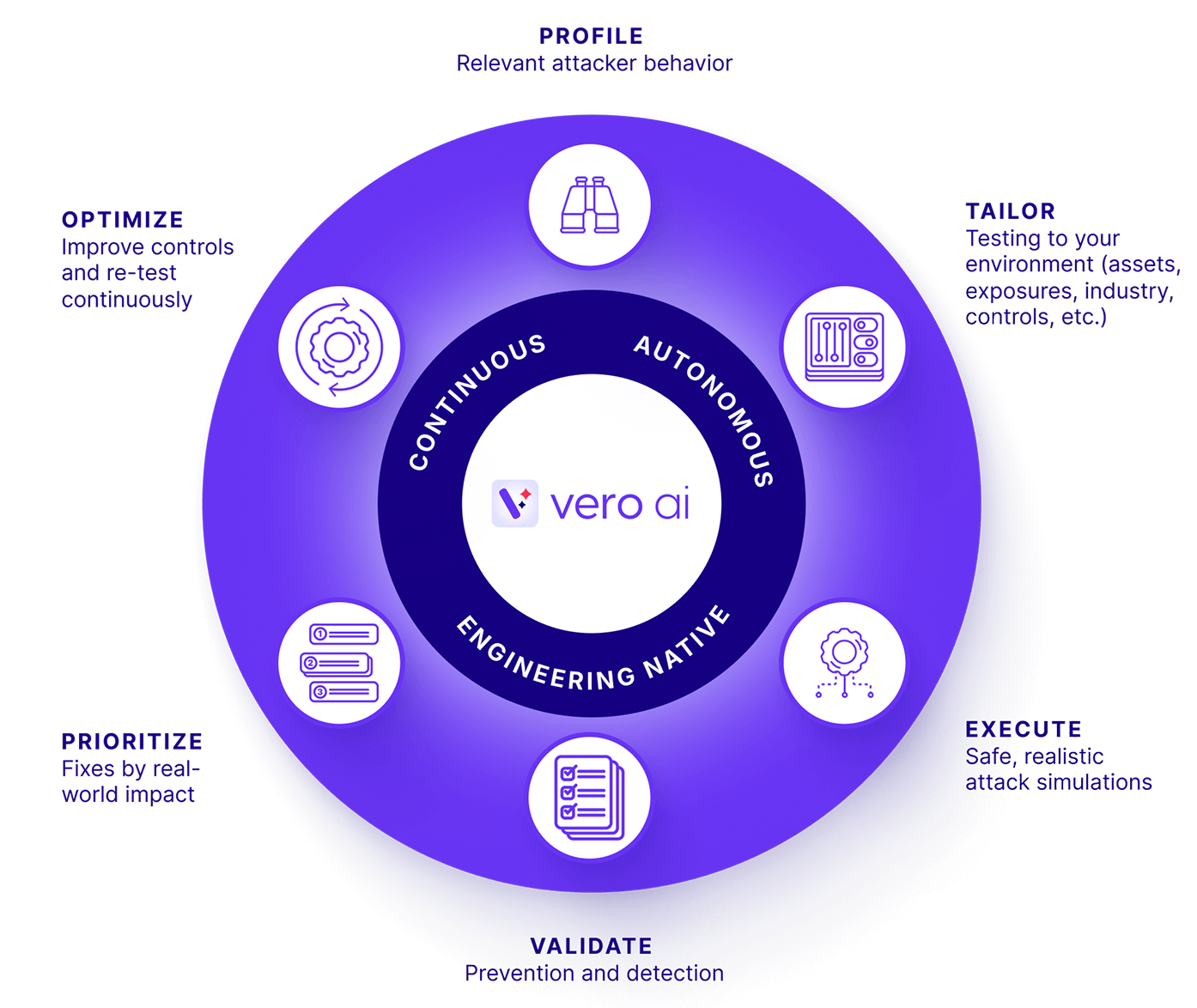
With Vero AI, Cymulate understands new threats and tailors validation specific to your environment – plus the intelligence to turn findings into prioritized actions and automated security control updates.
Cymulate Delivers Powerful Impact
— and Measurable ROI
90%
Threat prevention
AVG. of CYMULATE CUSTOMERS
50%
Better threat detection
AVG. of CYMULATE CUSTOMERS
60%
Boost to team efficiency
FINANCE COMPANY
The Cymulate Platform
See the Cymulate Platform in Action
Cymulate Platform FAQs
Cymulate is built for security teams that need continuous validation across their environment, including security operations, detection engineering, red teams and exposure management teams. It supports organizations of all sizes, from mid-market to enterprise, especially those with complex or evolving security stacks.
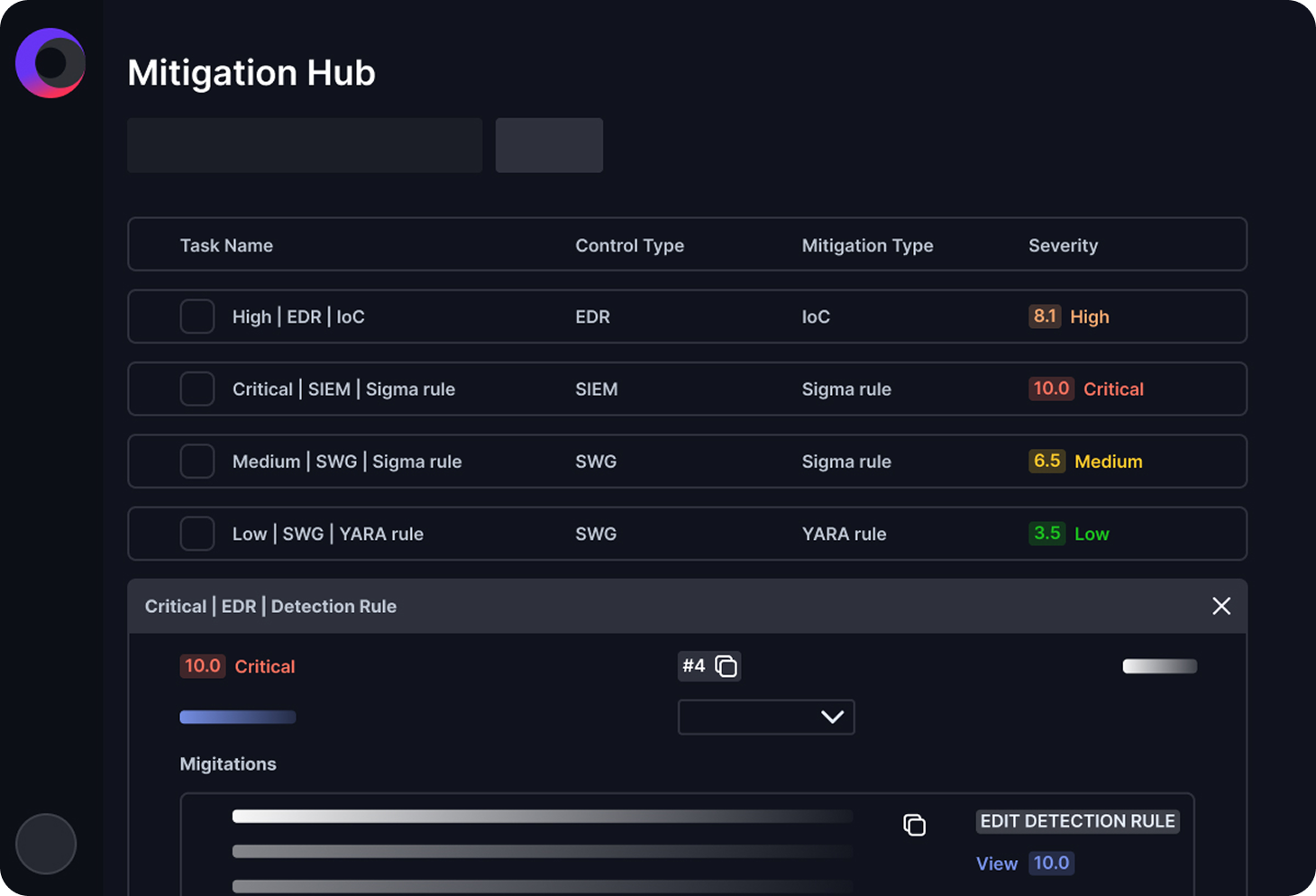
Unlike traditional point-in-time testing tools, Cymulate provides continuous, automated validation. It combines breach and attack simulation, exposure validation and actionable remediation guidance in a single platform, enabling teams to move from reactive testing to proactive security optimization.
Agentic cyber defense engineering is the Cymulate approach to autonomous security validation and improvement. It leverages intelligent, goal-driven automation to continuously test defenses, identify gaps and recommend or execute remediation actions, helping security teams operate more efficiently and stay ahead of evolving threats.
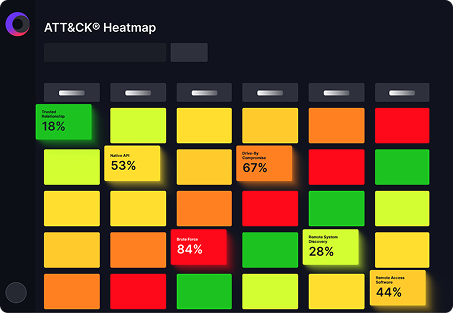
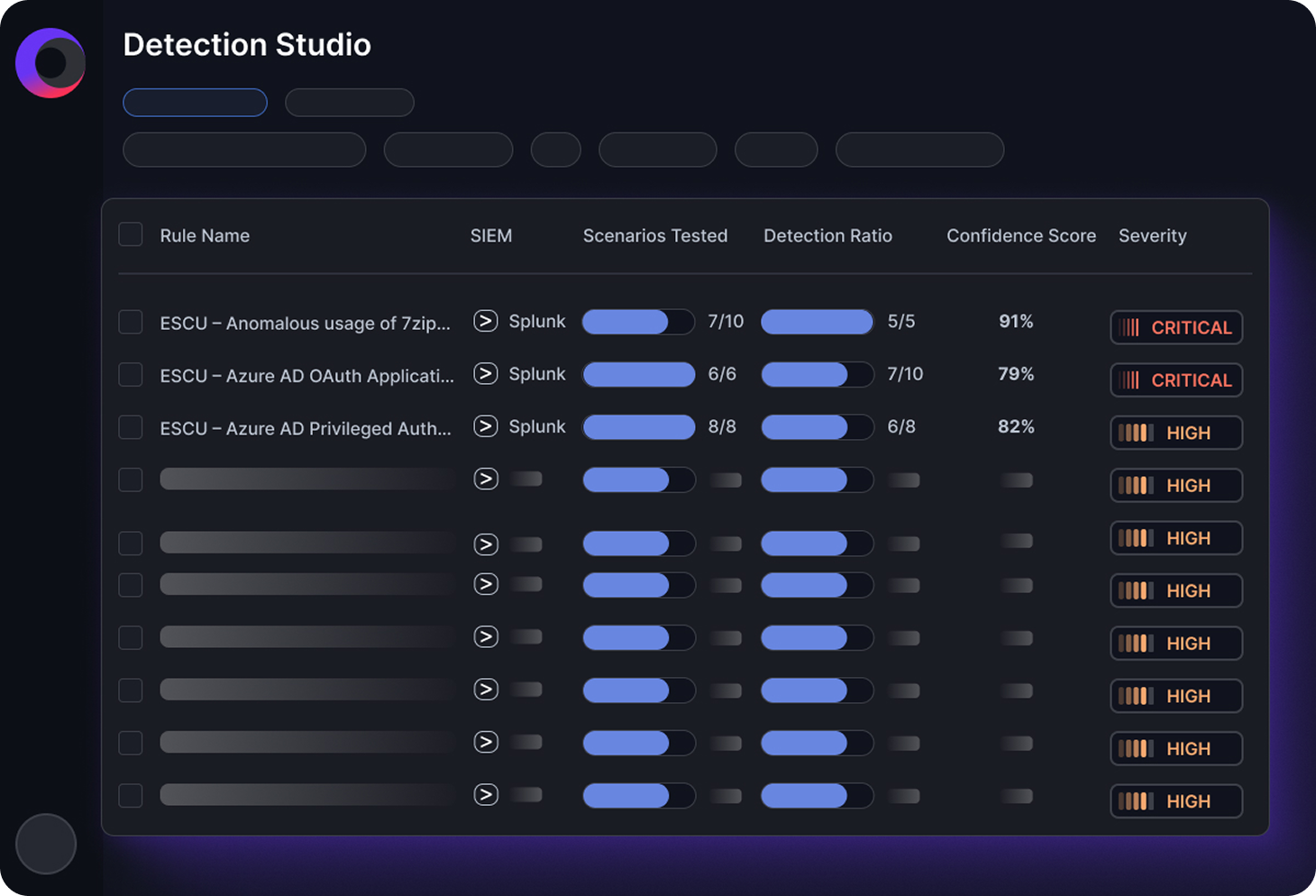
Cymulate safely simulates real-world attack techniques across endpoints, networks, email, web gateways and cloud environments with integrations to the controls and SIEM to prove both prevention and detection. It maps results to frameworks like MITRE ATT&CK, showing how controls perform against known tactics and techniques while providing prioritized remediation steps.
Yes. Cymulate integrates with a wide range of security tools, including SIEM, SOAR, EDR, cloud security, firewalls and email security platforms. These integrations allow organizations to validate how their existing controls perform and to automate response and remediation workflows.
Cymulate operationalizes CTEM by continuously discovering exposures, validating their impact through real-world attack simulations, and prioritizing remediation based on risk. This enables organizations to move beyond static assessments and maintain an ongoing, measurable view of their security posture.
Yes. Cymulate is designed to run safely in production environments without causing disruption. All simulations are controlled, non-destructive, and designed to emulate attacker behavior without impacting business operations or data integrity.