Continuous Automated
Red Teaming (CART)
Accelerate and automate realistic offensive testing and remediate exposures before adversaries can exploit them.
Threats don’t wait for your next pen test.
Replace manual, infrequent red teaming and penetration tests with continuous automated offensive testing and exposure validation.
Custom attack chains
Build custom offensive testing to simulate the latest advanced threats.
Attack paths
Map attack paths to reveal exposed routes to reach critical assets.
Blast radius and impact
Safely execute lateral movement and test privilege escalation.
Continuous Automated Red Teaming Benefits
With automation and AI, Cymulate transforms red teaming from a periodic exercise into a continuous, proactive defense strategy. Cymulate scales advanced testing for active campaigns and custom threats that target users, systems and networks. Cymulate applies real-world techniques that validate attacks and threats across the adversary lifecycle.
Simplify and automate offensive testing
Increase efficiency
Improve threat detection
Continuously prove threat resilience
Red Team at Scale with AI and Automation
Accelerate continuous automated red teaming (CART) with industry-leading technology: Breach and attack simulation (BAS), attack path discovery and custom attacks. Leverage AI-driven automation and the latest threat intelligence to automate production-safe, live-date adversary TTPs at scale. Prove where attackers are successful by validating controls across the entire kill chain and uncover hidden exposures.
Breach and attack simulation
- Continuously run realistic attack tests to exploit just like a red teamer
- Choose from most extensive attack scenario library with over 100k tests
- Uncover security gaps by running the latest attacks updated daily
Attack path discovery
- Enhance automated red teaming with increased exposure visibility
- Reveal all potential attack paths and where attackers are successful
- Discover what data can be exploited at each attack path compromise
Custom attacks and scenarios
- Easily customize existing attacks to ensure relevancy
- Quickly build your own advanced attack tests, chained or individual
- Utilize user-friendly attack workbench to customize inputs and resources
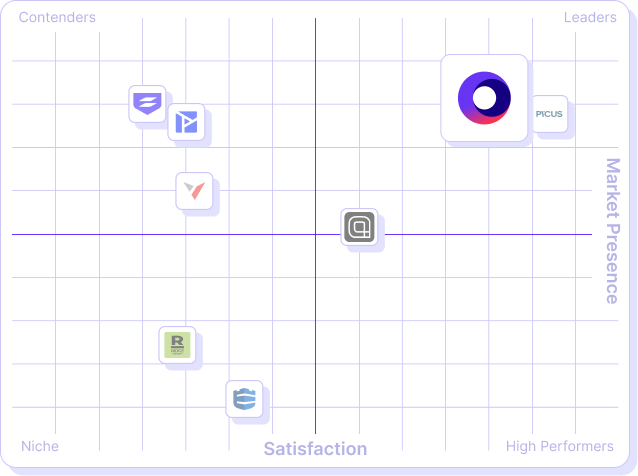
What our customers say about us
Organizations across all industries choose Cymulate for automated cybersecurity validation, proactively confirming that defenses are robust and reliable – before an attack occurs.
Frequently asked questions
Red teams in cybersecurity are a group of authorized security professionals who simulate a potential adversary’s attack on an organization to test its defenses.
In other words, red teaming involves emulating real-world attacker tactics, techniques and procedures (TTPs) in a controlled manner to identify weaknesses across people, process and technology, then report what worked (and what didn’t).
Continuous automated red teaming (CART) is an offensive security approach that uses automated tools to continuously simulate real-world cyberattacks against a targeted environment and potentially defined assets.
CART adds automation to scale the testing of traditional red team exercises to validate entire attack paths from infiltration to actions on objectives. This proactive approach to security testing involves regularly automating and simulating real-world attacks on an organization’s systems and applications. The simulations attempt to breach an organization by autonomously deploying attack techniques that penetrate and gain an initial foothold within the network.
A red team is the offensive side in cybersecurity testing that emulates an attacker attempting to breach the environment, whereas a blue team is the defensive side responsible for detecting, responding to and mitigating attacks.
In practice, a red team will execute stealthy attacks using adversary tradecraft, while the blue team works to defend, monitor, log, detect and respond. Together, they assess how effective the organization really is while under attack.
Cymulate makes adversarial simulation simple to deploy and broad in coverage, so security teams can test real-world threats safely and repeatedly. You can simulate attacks with:
- Easy deployment: Cymulate is cloud-based, accessible through a web browser, and requires only one lightweight agent per environment, eliminating the need for on-premises installation.
- Network propagation: It simulates how attacks can spread inside the network to uncover critical assets and vulnerabilities.
- Kill-chain coverage: CART tests techniques at every stage of the cyber kill-chain, from initial infiltration to lateral movement and actions on objectives.
- Flexible testing: Security teams can use predefined attack templates or create custom attack scenarios to perform penetration testing at scale.
Breach and attack simulation (BAS) and CART are two different approaches to security testing:
- BAS tests the effectiveness of security controls against known attack vectors, while CART focuses on if and how an adversary can breach an organization’s defenses by identifying and safely exploiting vulnerabilities.
- BAS testing is typically limited to specific areas of the network or specific applications, and CART testing covers the entire attack surface of an organization’s systems and applications.
Organizations that combine these two approaches can gain a more comprehensive view of their security posture.
This table summarizes the key differences between BAS and CART.
| CART | Breach and attack simulation (BAS) | |
| Primary focus | End-to-end attack emulation that tests an organization’s ability to prevent, detect and respond to complex, multi-stage attack scenarios. | Continuous control validation that verifies whether individual security technologies and configurations are working as intended. |
| Scope | Broad coverage across the full attack chain from initial access to lateral movement and exfiltration, spanning on-premises, cloud and hybrid environments.
|
Targeted focus on specific tactics, techniques or controls (e.g., email gateways, endpoint protection or segmentation). |
| Approach | Emulates realistic adversary behavior using chained tactics and adaptive logic to mimic real-world threat actors and assess operational readiness. | Automates discrete attack techniques aligned to MITRE ATT&CK to continuously test and measure the effectiveness of defensive controls. |
| Frequency | Runs continuously or on-demand to identify new exposures and validate resilience as environments evolve. | Runs continuously or on a defined cadence to provide ongoing assurance that specific controls detect and block known techniques. |
| Best use case | Ideal for assessing real-world exposure, validating blue team detection and response, and measuring overall cyber resilience. | Best for validating control effectiveness, maintaining compliance and ensuring defensive tools perform as expected. |
The difference between CART and red team security testing is that traditional red team testing typically occurs as a discrete, manual, scoped exercise, while CART runs repeatable, automated and covers evolving attack vectors at scale. In essence, the difference is in timing, scale and automation.
Where a red team engagement might occur monthly or quarterly and focus on a snapshot, CART is built to run repeatedly, catch drift, simulate evolving adversaries, test across the full kill-chain and deliver near-real-time insights on exposures.
No, CART does not fully replace traditional red team security testing. While CART delivers continuous, automated validation of controls and identifies new or evolving attack paths, traditional manual red team exercises still bring value through deep, creative human adversary thinking, customized scope and strategic objectives that may be difficult to fully automate.
CART complements and augments red team testing. It handles scale, frequency and automation, while manual red teaming brings human creativity, judgement and custom adversary emulation that automation alone may not replicate.
Cymulate Exposure Validation uses CART technology to provide the following capabilities:
- Reusable templates for baselining and ongoing testing
- Land-and-pivot lateral movement simulations for accurate, detailed results
- Customizable attacks spanning from infiltration to actions on objectives
- Phishing assessments to run internal campaigns and measure employee resilience
- Scalable testing across more environments without increasing staff requirements
The difference between CART and traditional penetration testing is frequency, scope and automation:
- Traditional penetration testing services typically involve a one-time assessment of an organization’s security posture.
- Cymulate provides ongoing, continuous and automated red team security testing and assessments that validate entire attack paths from infiltration to actions on objectives.
This allows businesses to identify and remediate vulnerabilities in real time rather than waiting for an annual or bi-annual assessment. The table below highlights the key differences.
| Cymulate | Traditional penetration testing | |
| Frequency | Runs continuously or on a scheduled, high-cadence basis to detect drift and new exposures in near-real-time. | Typically a point-in-time engagement performed annually, quarterly or ad-hoc that provides a snapshot of risk at that moment. |
| Scope | Broad, platform-wide and repeatable coverage that can exercise many attack chains across networks, cloud, endpoints and controls at scale. | Focused on defined assets, applications or environments agreed with the customer (can be deep but limited in breadth). |
| Approach | Automated, repeatable simulations of adversary TTPs (MITRE ATT&CK-mapped) that validate full attack paths continuously while remaining production-safe. | Manual and exploratory: skilled testers use human creativity and custom techniques to find and exploit vulnerabilities, sometimes including social engineering and physical tests. High-fidelity but not continuous. |
| Resources needed | Lower recurring labor overhead for running tests (automation handles large scale). Internal teams primarily analyze results and remediate. Scales without proportionally increasing human testers. | Higher expert time and cost per engagement. Requires experienced penetration testers (internal or third party), planning, scoping, reporting and often significant remediation validation effort. Cost grows with scope and depth. |
Cymulate supports both offensive (red) and defensive (blue) teams by improving efficiency, collaboration and resilience. Here’s how each group benefits:
Benefits for red teams (offensive security):
- Automate adversarial testing for higher efficiency
- Run highly customizable simulations safely in production
- Optimize and scale red team activities without extra headcount
Benefits for blue teams (defensive security):
- Improve adversarial skills through continuous exposure
- Increase collaboration and response readiness
- Reduce time to mitigation with repeated validation cycles
Benefits for all security teams:
- Maximize impact despite budget cuts and staffing shortages
GET A PERSONALIZED DEMO
Want to test more frequently with automated red testing?
“Through validation, Cymulate helps us understand which vulnerabilities can be exploited in our organization. This helps us focus our limited resources so we can be proactive and remediate before a threat becomes an actual problem.”
– CISO, Law Enforcement