Prove. Prioritize. Adapt.
Validate Threats. Build Exposure-Informed Defenses.
Beyond Validation.
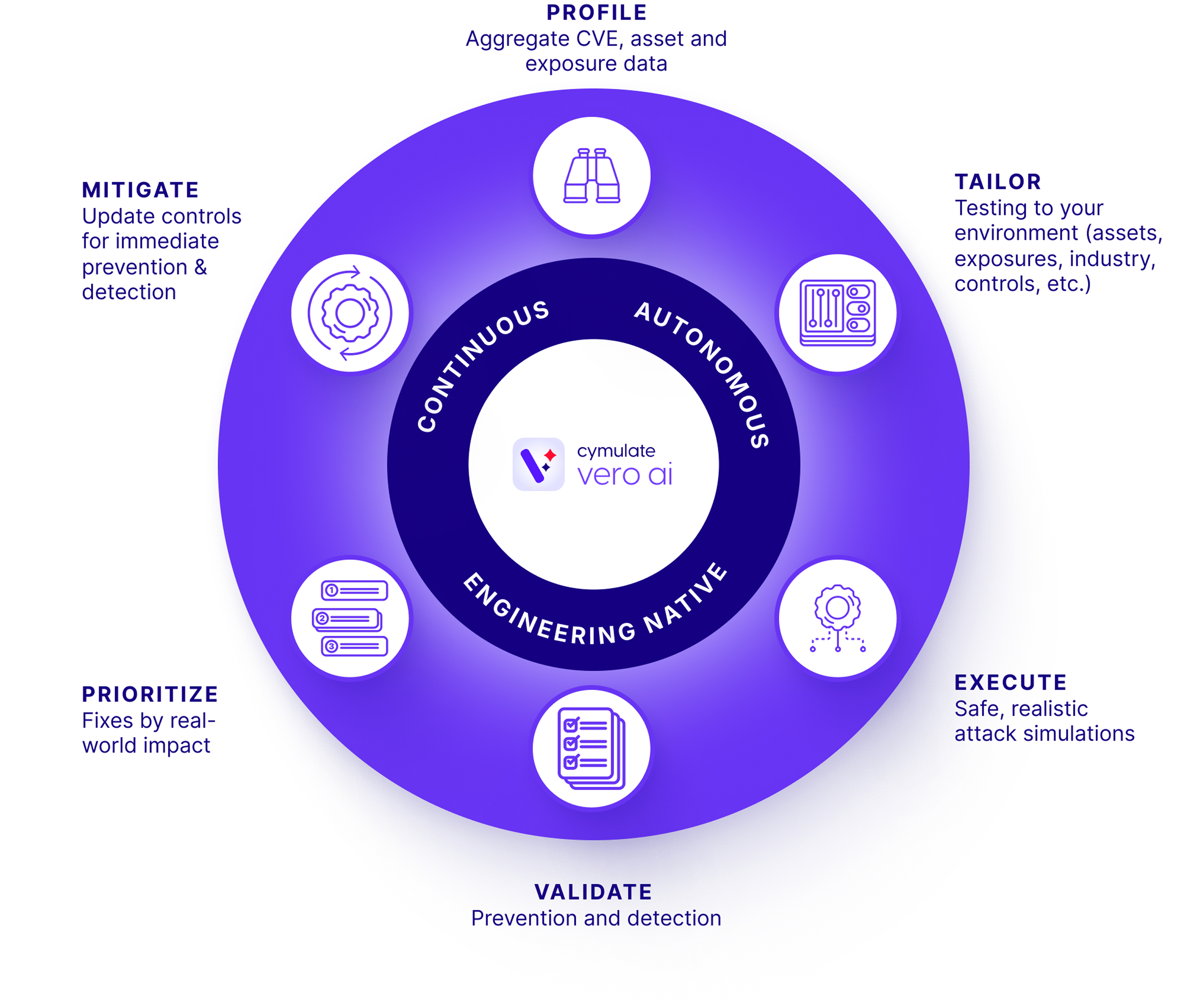
Agentic Cyber Defense Engineering.
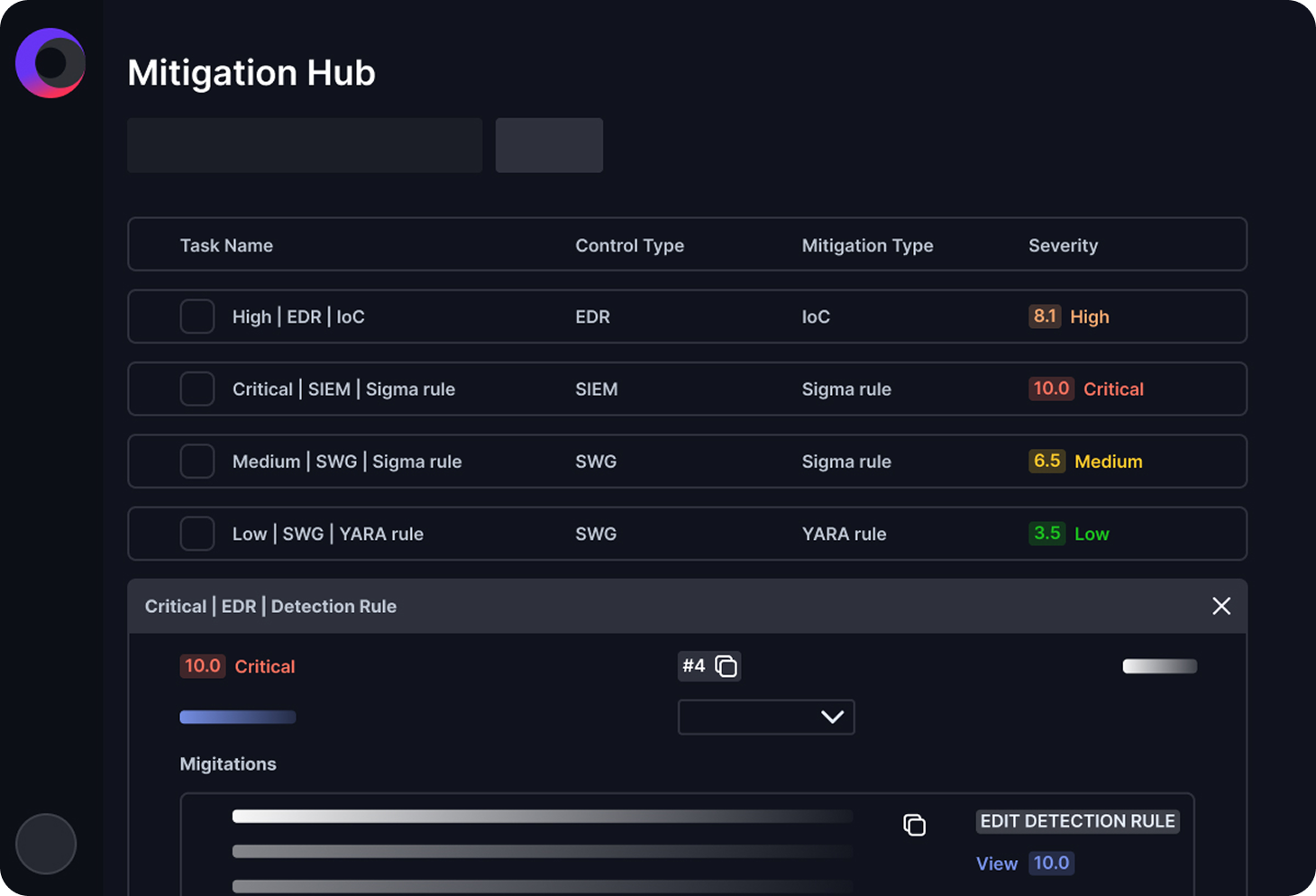
Cymulate turns validation into a continuous, adaptive process for agentic cyber defense engineering.
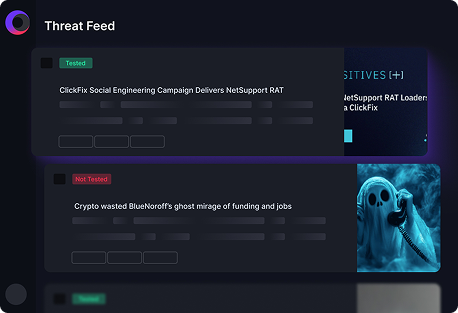
With Vero AI, Cymulate understands new threats and tailors validation specific to your environment – plus the intelligence to turn findings into prioritized actions and automated security control updates.
Threats and your attack surface evolve daily.
How do your 40+ security tools keep up?
<24 hours
One third of exploited CVEs are targeted within 24 hours of disclosure.
Source: Vulncheck
29 minutes
Attacks move from exploit to lateral movement in <0.5 hour.
Source: Crowdstrike
2-3 days
Manual testing and control updates can take days to adapt to new threats.
Source: Cymulate research
How We Help
Cymulate Delivers Powerful Impact
— and Measurable ROI
90%
Threat prevention with existing controls – proven against real threats.
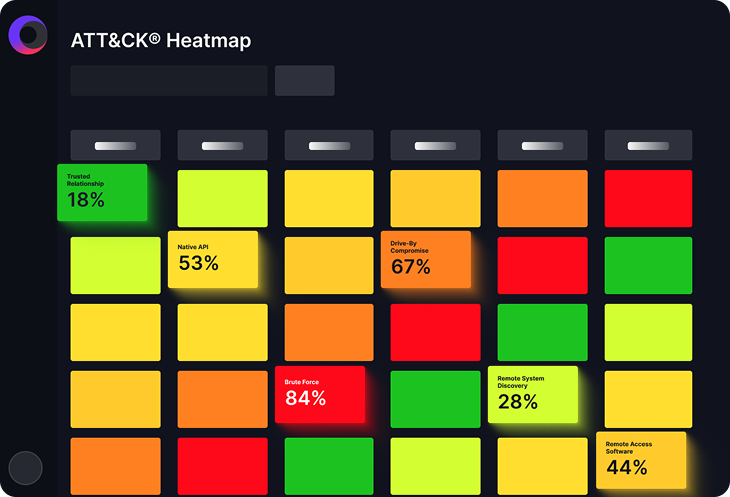
50%
Improvement in threat detection and MITRE ATT&CK coverage.
60 hrs
Saved testing new threats and updating controls each month.
Collaborate to Build
Threat-Informed Cyber Defenses
Cymulate empowers executives, security operations and your whole security program to continuously prove, prioritize and adapt security for your specific threats and exposures.

See What Cymulate Can Do For You
“Cymulate provides us with the visibility and standardization we were missing. The platform’s analytics and reporting make providing a holistic view of our cyber security posture to management and the board easier.“
- Renaldo Jack, Group Cybersecurity Head at Globeleq