Frequently Asked Questions
Automated Mitigation: Features & Capabilities
What is Cymulate Automated Mitigation?
Cymulate Automated Mitigation is a feature that enables organizations to build threat resilience and eliminate threat exposure by automatically updating security controls. It integrates with your existing security controls to push updates for immediate threat prevention, reducing manual intervention and accelerating response to new threats. [Source]
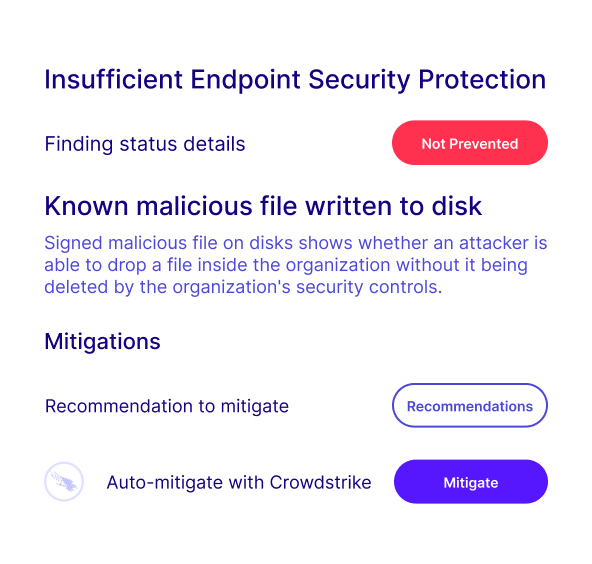
How does Cymulate Automated Mitigation work?
Cymulate Automated Mitigation works by validating exposures and identifying security gaps, then deploying targeted threat updates—such as indicators of compromise (IoCs) like file hashes, registry keys, and URLs—directly to connected security controls. This process can be triggered individually, in bulk, or automatically based on predefined rules, ensuring immediate threat prevention. [Source]
What are the main benefits of using Automated Mitigation?
The main benefits include faster mitigation of threats, optimized prevention by pushing updates directly to controls, operationalizing Continuous Threat Exposure Management (CTEM), and reducing dwell time by creating self-improving defenses that adapt to evolving threats. [Source]
How does Automated Mitigation reduce manual work for security teams?
Automated Mitigation eliminates the need for manual updates to security controls by automating the process of converting exposure validation into immediate threat resilience. Security teams can review findings and push mitigations with a click, aggregate bulk updates, or set up auto-fix rules for hands-off operation. [Source]
What types of updates can be pushed to security controls with Cymulate Automated Mitigation?
Cymulate can push indicators of compromise (IoCs) such as file hashes, registry keys, and URLs directly to connected security controls for immediate threat prevention. [Source]
How does Cymulate validate that mitigation actions are effective?
After threat updates are pushed to relevant controls, Cymulate automatically retests those defenses to confirm that the mitigation is effective, providing immediate validation and proof of improved resilience. [Source]
Can I automate mitigation actions based on specific rules or triggers?
Yes, you can predefine rules and parameters—such as time-based triggers, control types, or mitigation categories—to govern automatic updates, enabling hands-off, policy-driven mitigation. [Source]
How does Cymulate Automated Mitigation support bulk updates?
Cymulate allows you to aggregate mitigations from an assessment or multiple assessments and group recommended IoCs into a single bulk update, streamlining the process of updating multiple controls at once. [Source]
What is the average improvement in threat prevention with Cymulate Automated Mitigation?
Cymulate customers report an average of 30% better threat prevention after implementing Automated Mitigation. [Source]
How much faster is threat validation with Cymulate Automated Mitigation?
Threat validation is up to 40 times faster with Cymulate Automated Mitigation compared to manual methods, according to customer averages. [Source]
What reduction in pen test findings can be expected with Cymulate Automated Mitigation?
IT solutions customers have reported up to 70% fewer pen test findings after using Cymulate Automated Mitigation. [Source]
How does Cymulate Automated Mitigation integrate with security controls?
Cymulate integrates with security controls via API integrations, allowing direct communication for pushing threat updates and automating mitigation actions. For a full list of integrations, visit the Partnerships and Integrations page.
What are some real-world examples of Cymulate Automated Mitigation in action?
Customers in financial services, civil engineering, and law enforcement have reported that Cymulate Automated Mitigation automatically uploads critical threat data to their XDR and other controls, ensuring rapid detection and prevention of new threats without manual intervention. [Source]
How does Cymulate Automated Mitigation support Continuous Threat Exposure Management (CTEM)?
Automated Mitigation operationalizes CTEM by automating the mitigation of validated threat exposures, reducing friction between teams, accelerating action, and freeing up resources for more complex needs. [Source]
What technical documentation is available for Cymulate Automated Mitigation?
Technical documentation includes the Automated Mitigation Data Sheet, which details how to add automated remediation to the Cymulate platform, and other resources available in the Resource Hub.
How does Cymulate Automated Mitigation compare to traditional remediation workflows?
Traditional remediation workflows require manual copying or downloading of content to apply to security controls. Cymulate Automated Mitigation streamlines this by automating the process, allowing direct API-based updates and reducing manual effort. [Source]
How does Cymulate Automated Mitigation help reduce dwell time?
By automating the process of updating security controls and validating mitigations, Cymulate Automated Mitigation creates self-improving defenses that evolve in response to changing threat landscapes, thereby reducing the time threats remain undetected (dwell time). [Source]
Can Cymulate Automated Mitigation be used for both individual and bulk mitigation actions?
Yes, Cymulate Automated Mitigation allows users to review individual findings and select specific mitigations or aggregate multiple findings for bulk updates, providing flexibility in how mitigations are applied. [Source]
How does Cymulate Automated Mitigation help optimize threat prevention?
By pushing threat updates directly to security controls, Cymulate Automated Mitigation blocks threats that have been proven to bypass existing defenses, ensuring that prevention mechanisms are continuously optimized. [Source]
Integrations & Technical Requirements
What security controls and technologies does Cymulate Automated Mitigation integrate with?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a complete list, visit the Partnerships and Integrations page.
Is technical documentation available for integrating Cymulate Automated Mitigation?
Yes, technical guides, data sheets, and solution briefs are available, including the Automated Mitigation Data Sheet and other resources in the Resource Hub.
What are the technical requirements for deploying Cymulate Automated Mitigation?
Cymulate Automated Mitigation operates in an agentless mode, requiring no additional hardware or dedicated servers. Customers are responsible for providing necessary infrastructure and third-party software as per Cymulate’s prerequisites. [Source]
Security, Compliance & Support
What security and compliance certifications does Cymulate hold?
Cymulate holds several key certifications, including SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1, demonstrating adherence to industry-leading security and privacy standards. [Source]
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and compliance with GDPR. The platform also includes mandatory 2FA, RBAC, and IP address restrictions. [Source]
What support options are available for Cymulate Automated Mitigation?
Cymulate offers comprehensive support, including email support at [email protected], real-time chat support, a knowledge base, webinars, and e-books to help customers get started and optimize their use of the platform. [Source]
Use Cases, Customer Proof & Business Impact
Who can benefit from Cymulate Automated Mitigation?
Cymulate Automated Mitigation is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. [Source]
What business impact can be expected from using Cymulate Automated Mitigation?
Customers can expect up to a 52% reduction in critical exposures, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months, along with cost savings from tool consolidation and faster threat validation. [Source]
Are there customer testimonials or case studies for Cymulate Automated Mitigation?
Yes, customers from financial services, civil engineering, and law enforcement have praised Cymulate Automated Mitigation for its ease of use, automation, and effectiveness in improving threat detection and prevention. Case studies and testimonials are available on the Customers page.
How easy is it to implement Cymulate Automated Mitigation?
Cymulate Automated Mitigation is designed for quick and easy implementation, operating in agentless mode and requiring minimal resources. Customers can start running simulations and pushing updates almost immediately after deployment. [Source]
What feedback have customers given about Cymulate Automated Mitigation?
Customers have consistently praised Cymulate for its ease of use, intuitive interface, and the immediate value it provides in identifying and mitigating threats. Testimonials highlight the platform's automation and actionable insights. [Source]
Pricing & Competition
What is Cymulate's pricing model for Automated Mitigation?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements, including the chosen package, number of assets, and scenarios. For a detailed quote, schedule a demo with the Cymulate team.
How does Cymulate Automated Mitigation compare to competitors?
Cymulate stands out for its unified platform, continuous innovation, ease of use, and comprehensive automation. It offers a larger attack library, more frequent updates, and deeper integration with security controls compared to competitors like AttackIQ, Mandiant Security Validation, Pentera, Picus Security, SafeBreach, and Scythe. For detailed comparisons, visit the Why Cymulate page.
Why should organizations choose Cymulate Automated Mitigation over other solutions?
Organizations should choose Cymulate Automated Mitigation for its unified approach, continuous threat validation, AI-powered optimization, ease of use, measurable results, and proven customer outcomes such as significant reductions in exposures and increased operational efficiency. [Source]