Frequently Asked Questions
About CVE-2022-30190 (Follina) & Vulnerability Details
What is CVE-2022-30190 (Follina) and why is it significant?
CVE-2022-30190, also known as Follina, is a high-severity (CVSS 3.x score 7.8) zero-day remote code execution (RCE) vulnerability in the Microsoft Support Diagnostic Tool (MSDT). It allows attackers to execute arbitrary code via specially crafted Word documents, even without macros enabled. The vulnerability was publicly disclosed on May 27, 2022, and impacts all supported versions of Microsoft Office, making it a critical threat for organizations using Windows environments.
How does the Follina vulnerability exploit MSDT?
Follina exploits the ms-msdt:// protocol handler in Windows. Attackers craft malicious Word (.docx, .rtf, or .doc) files that, when opened—even in protected view—trigger MSDT to execute PowerShell commands. This can result in malware installation, data alteration or deletion, and creation of unauthorized accounts, all without requiring macros to be enabled.
Which Microsoft Office versions are affected by CVE-2022-30190?
CVE-2022-30190 affects Office 2013, 2016, 2019, 2021, Office Pro Plus, and Office 365. Any user opening a malicious Word document on these versions is potentially vulnerable until Microsoft's mitigation steps are applied and validated.
What actions did Microsoft take in response to Follina?
Microsoft published mitigation guidance on May 30, 2022, recommending disabling the MSDT URL protocol to prevent exploitation. Official workarounds and updates are available on the Microsoft Security Response Center's website. Organizations are advised to apply these mitigations and validate their effectiveness.
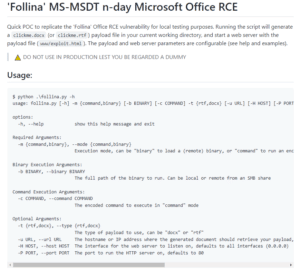
How can organizations test for exposure to CVE-2022-30190?
Organizations can use publicly available proof-of-concept (PoC) tools, such as the one on GitHub, to locally test for the Follina vulnerability. Additionally, Cymulate provides dedicated scenarios and threat intelligence kits to validate defenses against this threat.
What are the recommended mitigation steps for Follina?
Microsoft recommends disabling the MSDT URL protocol to block exploitation. Detailed steps are available in the official guidance from the Microsoft Security Response Center. Organizations should also validate that mitigations are effective using security validation tools like Cymulate.
How quickly did Cymulate respond to the Follina vulnerability?
Cymulate released an Immediate Threat Intelligence Kit for Follina on June 1, 2022, and by June 2, users could access a dedicated purple team scenario to validate defenses against CVE-2022-30190. This rapid response enabled organizations to test and strengthen their security posture within days of public disclosure.
What tools does Cymulate provide to validate defenses against Follina?
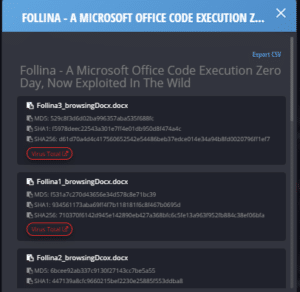
Cymulate offers a dedicated purple team scenario for CVE-2022-30190, an Immediate Threat Intelligence Kit, and the ability to update SIEM signature banks with multiple indicators of compromise (IoCs). These tools help organizations test, detect, and mitigate Follina-specific exploits efficiently.
Can Cymulate validate mitigations for Follina across different environments?
Yes, Cymulate's platform enables organizations to validate their exposure and the effectiveness of mitigations for Follina across all IT environments, including on-premises, cloud, and hybrid infrastructures.
Where can I find a video demonstration of Follina exploitation?
A video demonstration of the Follina proof-of-concept is available at this link as referenced in the Cymulate blog post.
Who discovered the Follina vulnerability?
The Follina vulnerability was initially identified by the Crazyman_Army research team and later uncovered in the wild by security researcher Nao_sec during a VirusTotal search. The vulnerability was reported to Microsoft, but the initial submission was incorrectly classified as fixed.
How can I stay updated on new threats like Follina?
You can stay informed about the latest threats, research, and mitigation strategies by following the Cymulate blog and subscribing to updates from the Microsoft Security Response Center.
What is the impact of Follina on organizational security?
Follina poses a significant risk as it allows attackers to compromise systems simply by convincing users to open a malicious document. This can lead to malware infections, data breaches, and unauthorized access, emphasizing the need for rapid validation and mitigation.
How does Cymulate help organizations respond to zero-day threats like Follina?
Cymulate enables organizations to rapidly validate their defenses against zero-day threats by providing immediate threat intelligence kits, dedicated attack scenarios, and automated validation tools. This allows security teams to assess and remediate vulnerabilities quickly, reducing risk exposure.
Can Cymulate help validate SIEM detection for Follina-related attacks?
Yes, Cymulate allows users to update their SIEM signature banks with multiple indicators of compromise (IoCs) related to Follina, helping organizations validate and enhance their detection capabilities for this specific threat.
Where can I find more resources on exposure validation and threat simulation?
You can access whitepapers, demos, and data sheets on exposure validation and threat simulation in the Cymulate Resource Hub.
How does Cymulate's Exposure Validation help with threats like Follina?
Cymulate Exposure Validation makes advanced security testing fast and easy, allowing organizations to build custom attack chains and validate their defenses against threats like Follina in a single, unified platform.
What is the CVSS score for Follina and what does it mean?
Follina (CVE-2022-30190) has a CVSS 3.x base score of 7.8, indicating a high-severity vulnerability that requires immediate attention and remediation to prevent exploitation.
How can I validate that my organization is no longer exposed to Follina?
After applying Microsoft's mitigation steps, organizations should use validation tools like Cymulate's dedicated scenarios and threat intelligence kits to test and confirm that their defenses are effective against Follina exploits.
Features & Capabilities
What are the key capabilities of the Cymulate platform?
Cymulate offers continuous threat validation, unified exposure management, attack path discovery, automated mitigation, AI-powered optimization, and an extensive threat simulation library. The platform enables organizations to validate defenses 24/7, prioritize exposures, and automate remediation for improved resilience and operational efficiency. Learn more.
Does Cymulate integrate with other security tools?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a full list, visit the Partnerships and Integrations page.
How does Cymulate help with exposure prioritization?
Cymulate validates the exploitability of exposures and ranks them based on prevention and detection capabilities, business context, and threat intelligence. This helps organizations focus remediation efforts on the most critical vulnerabilities. Learn more.
What is Cymulate's approach to continuous threat validation?
Cymulate runs automated attack simulations 24/7, enabling organizations to validate their security posture in real-time and stay ahead of emerging threats. This continuous validation ensures defenses are always tested against the latest attack techniques. Learn more.
How does Cymulate support detection engineering?
Cymulate enables organizations to build, tune, and test SIEM, EDR, and XDR rules to improve mean time to detect threats. The platform provides actionable insights for optimizing detection engineering processes. Learn more.
What is Cymulate's threat simulation library?
Cymulate provides an advanced library of over 100,000 attack actions aligned to the MITRE ATT&CK framework, updated daily with the latest threat intelligence. This enables comprehensive testing against a wide range of attack techniques. Learn more.
How easy is it to implement Cymulate?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment. Schedule a demo to learn more.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive interface and ease of use. For example, Raphael Ferreira, Cybersecurity Manager, stated, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." Read more testimonials.
What compliance certifications does Cymulate hold?
Cymulate holds several industry-leading certifications, including SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to robust security and compliance standards. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and compliance with GDPR. The platform also features mandatory 2FA, RBAC, and IP address restrictions. Learn more.
What is Cymulate's policy on notifying third-party vendors about vulnerabilities?
Cymulate may notify relevant third-party vendors of critical vulnerabilities discovered during platform use if it is in the public interest and to prevent harm to other users. Notifications are limited to the existence of the vulnerability and do not include customer-specific data. Read the EULA.
Where can I find Cymulate's blog, newsroom, and resource hub?
You can find the latest threats, research, and company news on the Cymulate blog, newsroom, and resource hub.
Does Cymulate provide educational resources like a glossary or webinars?
Yes, Cymulate offers a cybersecurity glossary, webinars, e-books, and a resource hub with technical articles and videos. Explore resources.
How often is Cymulate's SaaS platform updated?
Cymulate updates its SaaS platform every two weeks, introducing new features such as AI-powered SIEM rule mapping and advanced exposure prioritization to keep customers ahead of emerging threats.
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, schedule a demo with the Cymulate team.
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. Learn more.
What core problems does Cymulate solve for security teams?
Cymulate addresses challenges such as overwhelming threat volume, lack of visibility, unclear risk prioritization, resource constraints, and fragmented security tools by providing unified, automated, and continuous validation and prioritization of exposures. Learn more.
How does Cymulate help organizations improve operational efficiency?
Cymulate automates threat validation and exposure management, saving security teams up to 60 hours per month and increasing team efficiency by 60%. This allows teams to focus on strategic initiatives rather than manual tasks.
What measurable outcomes have Cymulate customers achieved?
Customers have reported up to an 81% reduction in cyber risk within four months, a 52% reduction in critical exposures, and a 20-point improvement in threat prevention. See the Hertz Israel case study.
Are there case studies showing Cymulate's impact on real organizations?
Yes, Cymulate features case studies across industries, such as Hertz Israel reducing cyber risk by 81%, a sustainable energy company scaling pen testing, and Nemours Children's Health improving detection in hybrid environments. Browse case studies.
How does Cymulate address the needs of different security personas?
Cymulate tailors solutions for CISOs (metrics and risk communication), SecOps (automation and efficiency), red teams (offensive testing), and vulnerability management teams (validation and prioritization). Learn more.
What pain points does Cymulate solve for organizations?
Cymulate solves pain points such as fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies, and post-breach recovery challenges. Learn more.
How does Cymulate compare to other security validation platforms?
Cymulate stands out with its unified platform combining BAS, CART, and exposure analytics, continuous 24/7 validation, AI-powered optimization, ease of use, and measurable customer outcomes. It is recognized as a market leader by Frost & Sullivan and a Customers' Choice in Gartner Peer Insights 2025. See comparisons.
What is Cymulate's mission and vision?
Cymulate's mission is to transform cybersecurity practices by enabling organizations to proactively validate defenses, identify vulnerabilities, and optimize their security posture. The vision is to create a collaborative environment for lasting improvements in cybersecurity strategies. Learn more.
How does Cymulate support compliance and regulatory requirements?
Cymulate helps organizations meet compliance and regulatory requirements by providing automated validation, quantifiable metrics, and adherence to standards such as SOC2, ISO 27001, and CSA STAR. Learn more.
How can I get started with Cymulate?
You can get started by booking a personalized demo with the Cymulate team at this link. The platform is designed for rapid deployment and immediate value.