Exposure Validation: Continuous Testing Should Drive Continuous Improvement
What’s your end goal? How exactly does this security project make you more secure?
Like any technology initiative, those two questions should drive your evaluation, budgeting and ultimate decision-making around continuous security testing and exposure validation.
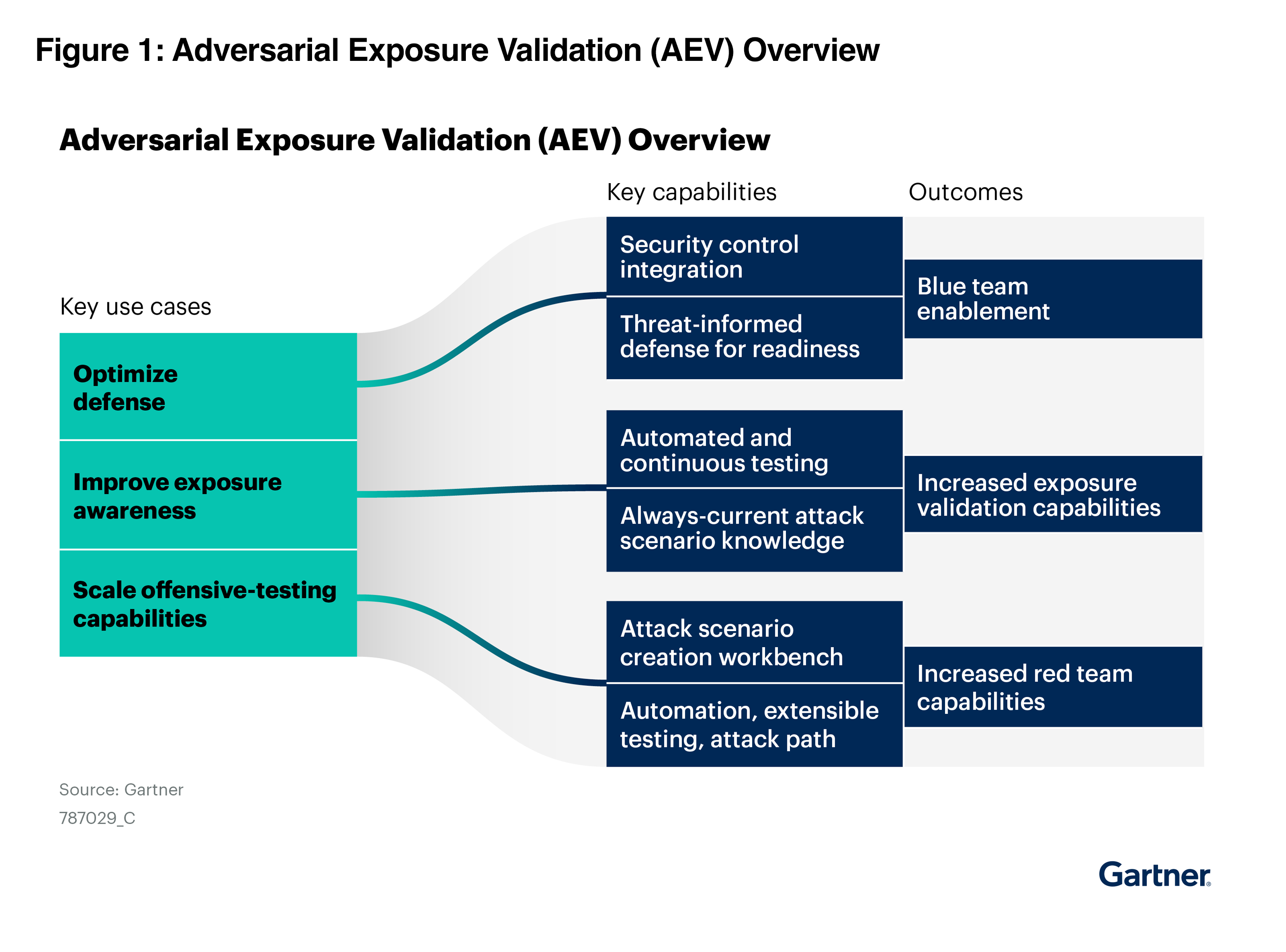
The concept of security validation and the automation of attacker behavior is generally associated with offensive testing and the specialized skills of red teams and penetration testers, but that’s just one of the three core use cases that Gartner highlights in its latest Market Guide for Adversarial Exposure Validation.1
Beyond red teaming, the Gartner market guide highlights use cases of defense optimization and exposure awareness.
You can download your complimentary copy here.
Clarity from market confusion
You can argue that Gartner added to market confusion when they combined the previous markets of breach and attack simulation (BAS), automated pen testing and continuous red teaming into the new consolidated adversarial exposure validation.
Offensive testing provides a common thread among these three technologies, and the market is evolving where both BAS and auto pen testing vendors offer some form of red teaming tools. However, these technologies are generally targeted at different use cases, leaving buyers to choose from a jumbled list of validation vendors without clarity about each vendor’s core value.
To its credit, the Gartner Market Guide challenges the market to move beyond the technology and focus on the value and outcomes for security teams. The report goes into detail for the mandatory and common features specific to the use cases that you can map different outcomes serving different security teams, including:
- Optimize defense => security operations and blue teams
- Exposure awareness => vulnerability management and continuous threat exposure management (CTEM)
- Scale offensive testing => red teams
Across all three use cases, Gartner highlights the value of exposure validation solutions like Cymulate to “reduce skill and complexity barriers, enabling organizations to test their defenses more effectively and proactively.” 1
Thinking red, acting blue
Offensive security testing has an undeniable cool factor – especially for security engineers who’ve spent countless hours triaging alerts, tuning firewall rules and chasing down vulnerabilities.
We all know the adage that attackers need to be right just once, while defenders need to be right 100% of the time. That’s why security leaders recognize the value and of continuous testing. Testing like an attacker finds the gaps today instead of waiting for next year’s penetration test.
However, finding the exposure is just the starting point. While testing and validation can provide the headlights to see the upcoming cliff drop off, it’s the security engineer and blue teams who sit behind the steering wheel with the experience, ability and most importantly the controls to act swiftly to mitigate the threat exposure.
That’s the role of exposure validation to lead directly toward:
- Tuning security controls to block the threats that matter most to you
- Build and deploy detection logic for the threats that cannot be prevented
- Mobilize the required action to remediate the validated exposure that cannot be mitigated
Go beyond visibility
For more than 20 years and long before the term security posture management, security vendors have sold on the value of visibility. The core idea was that you must first identify the asset, application, vulnerability, attack surface, container, etc., before you can effectively secure it.
When it comes to exposure validation, the Gartner report highlights a few of these visibility values: “service provider performance validation” and “security vendor performance scorecards.” CISOs and security leaders justify the spend on exposure management to: “Improving vendor management by using performance data for infrastructure security controls to better inform product renewals or vendor management strategies.”1
To that end, Cymulate has helped many CISOs use exposure validation to understand their strengths, establish a clear baseline and build a roadmap for strategic investments and improvements. For the security team and their supporting vendors, however, this process can often feel more like an audit than a path to immediate progress.
From continuous testing to continuous improvement
Rather than making this a pass-fail exercise, the most successful security leaders take the opportunity to build a culture of continuous improvement. With continuous testing of threats, security controls, MITRE ATT&CK techniques, SIEM rules and more, validation supports a continuous improvement process with tangible outcomes of:
- Threat prevention tuned for the latest threats
- New detection logic built, deployed and tested
- Maximum coverage of MITRE ATT&CK
The Gartner market guide drives this point home. “Gartner suggests starting with defensive optimization or the fundamentals of a blue team practice. Although having a red team sounds more appealing, it’s not for everyone, and the results are often more elusive to prove.”1
While the identification of security gaps and discovering points of exposure provide necessary visibility, security leaders should expect more from their exposure validation with integrations that directly build better security.
That takes us back to the initial question. How exactly will exposure validation improve your security? I’ll leave you with one more Gartner quote and their strategic planning assumption. “By 2029, 30% of organizations will link AEV results to automated remediation or orchestration workflows, enabling faster treatment of validated exposures.”1
In the end, exposure validation must lead to better security.
I invite you to read the full Gartner Market Guide for Adversarial Exposure Validation. Download your complimentary copy here.
1Gartner®, Market Guide for Adversarial Exposure Validation, Dhivya Poole, Mitchell Schneider, Eric Ahlm, Angela Zhao, 24 March 2026
GARTNER® is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
Gartner® does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.