MITRE ATT&CK v19 Unpacked: What Changed and How to Operationalize

MITRE ATT&CK v19 introduces major changes that reshape how organizations understand and validate adversary behavior, including retiring the Defense Evasion tactic and introducing Stealth and Defense Impairment tactics. These updates shift the focus beyond detection alone to ensure that security controls can withstand direct attack and manipulation, whether attackers blend in as legitimate activity to avoid detection or actively break and disable defenses. Organizations must proactively prepare for and operationalize these changes to continuously validate their defenses against evolving tactics, techniques, and real-world threats.
Summary of changes and what you will gain:
- Split of Defense Evasion tactic into 2 tactics: Obtain insights into how the Defense Evasion tactic (a blend of adversary behavior and intent) techniques and sub-techniques have been moved to other tactics, with the majority moved to the newly created tactics: Stealth and Defense Impairment.
- Restructuring of the Impair Defenses technique: Learn about the restructuring of Impair Defenses techniques (T1562) into technique (T1685) and related techniques, highlighting the shift from detection-focused Defense Evasion to Defense Impairment and where organizations must validate that security controls can withstand, detect and recover from direct attacks.
- Introduction of new techniques: Gain visibility into the newly introduced Defense Impairment techniques (including a new sub-technique) and a Stealth technique focused on social engineering to help operationalize and validate defenses against behaviors that disable controls or exploit human trust.
- How to operationalize ATT&CK v19: Learn how to operationalize ATT&CK v19 by updating mappings, prioritizing key technique and sub-technique changes, aligning validation to attacker intent and incorporating new tactics and techniques, while leveraging automation (like Cymulate) to streamline coverage and reduce manual effort.
- Cymulate and MITRE ATT&CK v19 in action: Understand how Cymulate enables organizations to fully prepare for the split of the Defense Evasion tactic, specifically to validate detection logic against low-signal, high-context behaviors, such as masquerading or abuse of legitimate tools (Stealth tactic) and proactively test how resilient their controls are against tampering, logging disruption and EDR interference (Defense Impairment tactic).
What Has Changed with ATT&CK v19
The most notable changes in MITRE ATT&CK v9 include the retirement of the Defense Evasion tactic, the creation of 2 new tactics that replace the Defense Evasion tactic, the restructuring of the Impair Defenses (T1562) technique and the creation of 2 new techniques/sub-techniques focusing on attackers attempting to disable defenses and leverage social engineering.
Change #1: Explanation and impact of the Defense Evasion tactic split
With the retirement of the Defense Evasion tactic, MITRE introduced two distinct tactics: Stealth and Defense Impairment, as shown in the table below. This change introduces a clearer separation based on adversary intent, not just behavior, highlighting two fundamentally different security and threat validation challenges.
| Old Tactic (v18) | New Tactic (v19) | Adversary Intent | Impact to Defenses | Example Behaviors |
|---|---|---|---|---|
| Defense Evasion (TA0005) | Stealth (TA0005) *note – keeps old ID | Blend in to avoid detection | Defenses are running but being deceived; viewed as legitimate behavior | • Hide artifacts • Obfuscation • Masquerading |
| Defense Evasion (TA0005) | Defense Impairment (TA0112) | Break and/or disable defenses | Controls are being disabled and/or broken | • Disable EDR • Modify firewall • Modify cloud compute architecture |
Table 1: New tactics from the retirement of Defense Evasion
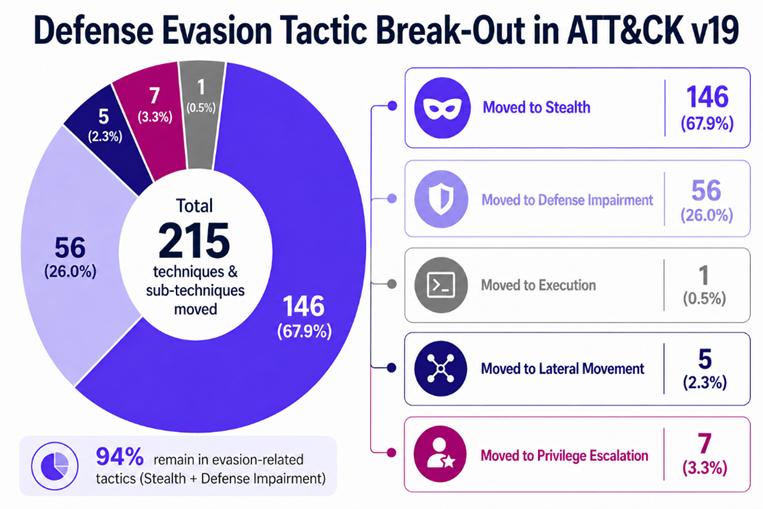
Most techniques and sub-techniques previously categorized under Defense Evasion (94%) have been redistributed into the new Stealth and Defense Impairment tactics. However, MITRE also used this opportunity to reassign a smaller subset to other existing tactics, such as Lateral Movement, Privilege Escalation, and Execution, where they more accurately reflect adversary intent. The visual below illustrates how Defense Evasion previously grouped a wide range of attacker behaviors, and how this reclassification now better aligns with real-world activity.
Change #2: Restructuring of the Impair Defenses technique
The T1562 parent technique (Impair Defenses) and several of its sub-techniques have undergone significant restructuring. T1562, along with T1562.001 and T1562.006, has been merged into a new parent technique, T1685: Disable or Modify Tools, while the remaining sub-techniques have been revoked and reissued under new IDs within the Defense Impairment tactic.
This change goes beyond simple renaming. It reflects a shift in how defenders should think about these behaviors. Previously, many of these activities were grouped under Defense Evasion as individual sub-techniques, often treated primarily as detection challenges. In v19, they are explicitly categorized as Defense Impairment, emphasizing that these actions are not just about hiding, but about actively degrading or disabling security controls.
Ultimately, this change reinforces a critical shift for organizations. It is not enough for security teams to merely detect adversary activity; they must also ensure that their defensive controls remain continuously operational and withstand and recover from direct attacks.
Change #3: Introduction of new techniques/sub-techniques
This release introduced three new techniques/sub-techniques highlighted in the table below. Security teams must operationalize these new techniques and sub-techniques by validating that they have the necessary mitigations and detection strategies in place. Learn more in the following section on operationalizing strategies.
| New Technique | Tactic | Technique Type | Description |
|---|---|---|---|
| Disable or Modify System Firewall: Windows Host Firewall (T1686.003) *(T1686 parent) | Defense Impairment (TA0112) | New sub-technique | Adversaries may disable or modify the Windows host firewall to bypass controls limiting network usage and further advance their mission, such as enabling remote access. |
| Exploitation for Defense Impairment (T1687) | Defense Impairment (TA0112) | New technique | Adversaries may exploit vulnerabilities in security software, infrastructure, or defensive components to degrade, disable, or otherwise continue to impair their ability to prevent, detect, or respond to malicious activity. |
| Social Engineering (T1684) | Stealth (TA0005) | New technique | Adversaries may use social engineering techniques to influence users to take actions that result in unauthorized access, approval of changes, disclosure of sensitive information, or execution of adversary-supplied instructions, while minimizing indicators |
Table 2: Description of new techniques and sub-techniques
How to Operationalize ATT&CK v19
For organizations that leverage the MITRE ATT&CK® framework to guide security validation and control coverage, ATT&CK v19 introduces major changes that require both mapping updates and a shift in how controls are evaluated.
Organizations using Automated Exposure Validation (AEV) platforms, such as Cymulate, will benefit from automatic crosswalk updates, ensuring that techniques, sub-techniques, and tactics are seamlessly realigned to v19 with minimal effort. This eliminates manual re-mapping and helps teams quickly understand how their existing coverage translates to the new framework. One caveat is that for the new techniques introduced, it is paramount to simulate new attack scenarios that map to these to evaluate their prevention and detection coverage.
However, for organizations that rely on manual ATT&CK mapping or semi-automated tools, a more deliberate update process is required as outlined below:
1. Re-map retired defense evasion content
With the retirement of the Defense Evasion tactic, teams must review all existing mappings in their tools and processes and:
- Re-assign techniques to Stealth (TA0005) or Defense Impairment (TA0112) based on adversary intent
- Identify and reassign techniques that have moved to other tactics, such as Execution, Lateral Movement or Privilege Escalation
- Update any internal documentation, dashboards and reporting that reference TA0005, and create dashboards and documentation for TA0012.
2. Prioritize high-impact changes (e.g., T1562)
Special attention should be given to techniques that were revoked, merged or re-issued, particularly:
- T1562 (Impair Defenses) and its sub-techniques in MITREv18 have been significantly restructured into T1685 (Disable or Modify Tools).
- Any detections, controls, or test scenarios tied to these IDs will now require new mappings and validation logic to ensure threat resilience and defenses are not disabled and are actively working.
3. Align validation to intent, not just technique
The v19 update introduces a more meaningful distinction between:
- Stealth Tactic → validating detection gaps (can you see the attacker trying to hide?)
- Defense Impairment Tactic → validating control resilience (can your defenses be disabled, and can you detect attackers trying to disable them?)
Organizations should take this opportunity to reassess whether their validation programs are focused only on detection, and understand if they are also testing the resilience and integrity of security controls under attack
4. Incorporate new and reorganized techniques
Security teams should review and integrate the newly introduced techniques (e.g., T1685, T1687, T1684) and re-organize areas like Social Engineering, which is now consolidated under the Stealth tactic to ensure coverage reflects current adversary behaviors, not legacy classifications.
Cymulate and MITRE ATT&CK v19 in Action
Cymulate is fully aligned with the MITRE ATT&CK framework through its continuous security validation approach, which maps attack simulations directly to the tactics, techniques and sub-techniques. The platform inherently mirrors this structure, allowing organizations to safely simulate real-world attacker behaviors, validate control effectiveness and measure coverage across the full ATT&CK matrix, which includes identification of prevention and detection gaps and risk quantification.
Cymulate will enable organizations to fully prepare for the split of Defense Evasion into Stealth and Impair Defenses tactics.
- Stealth tactic: Enables organizations to validate detection logic against low-signal, high-context behaviors, such as masquerading or abuse of legitimate tools.
- Defense Impairment tactic: Allows teams to proactively test how resilient their controls are against tampering, logging disruption and EDR interference, as a few examples.
Ensuring resilience against both tactics is critical, as modern attackers often combine them in a single campaign, requiring defenses that can detect subtle anomalies while also verifying control integrity and availability.
For both restructuring defense-impairment behaviors and introducing new techniques and sub-techniques, Cymulate empowers security teams to reassess their detection coverage and validation strategies. Cymulate directly addresses this need by continuously updating its simulation library to reflect the latest ATT&CK mappings, enabling organizations to test newly defined or reclassified techniques as they emerge. Security and risk teams are equipped to quickly operationalize ATT&CK changes by validating existing controls and new detections against evolving adversary tactics without disrupting SOC workflows.
Interested in Learning More about Cymulate ATT&CK Alignment?
Cymulate has already begun rolling out the new MITRE alignment in the product content and features..
Our commitment is simple: deliver industry-standard ATT&CK mapping, behavior-driven analytics, and comprehensive technique coverage. By staying in lockstep with the MITRE ATT&CK evolution, Cymulate helps organizations turn framework updates into real, measurable improvements in threat resilience.
Want to see it in action? Discover how Cymulate continuously aligns with MITRE ATT&CK and gives you clear visibility into your prevention and detection coverage across the entire adversary lifecycle.
Sign up for a demo and see how the platform can validate and measure your threat resilience.