Cymulate vs AttackIQ
Go beyond simple validation with AI-driven, actionable remediation guidance.
Don’t Just Test – Prioritize and Mitigate Real Risk
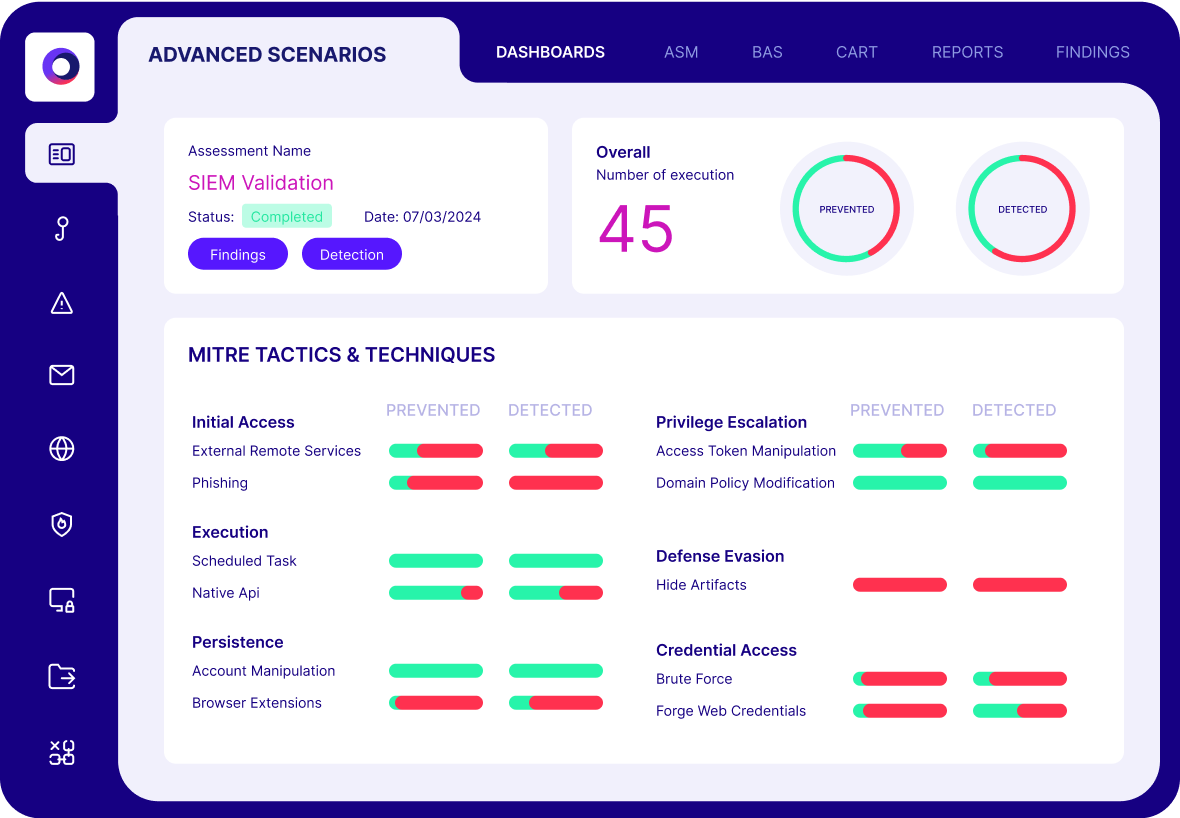
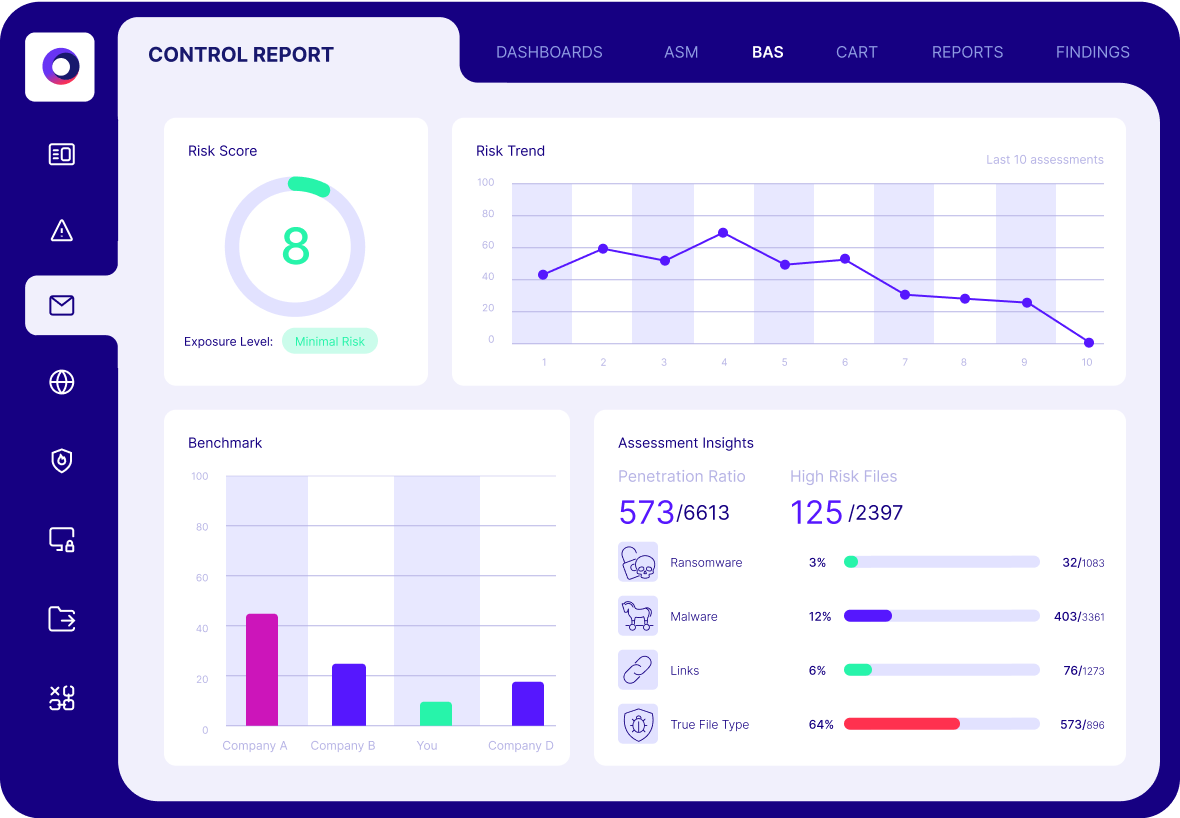
Security teams need more than just control testing – they need a path to optimize security for the latest threats. While AttackIQ executes automated security control assessments, Cymulate takes threat exposure validation to the next level by allowing security teams to focus on their critical cybersecurity gaps based on the latest threat intelligence through prioritized, data-driven remediations.
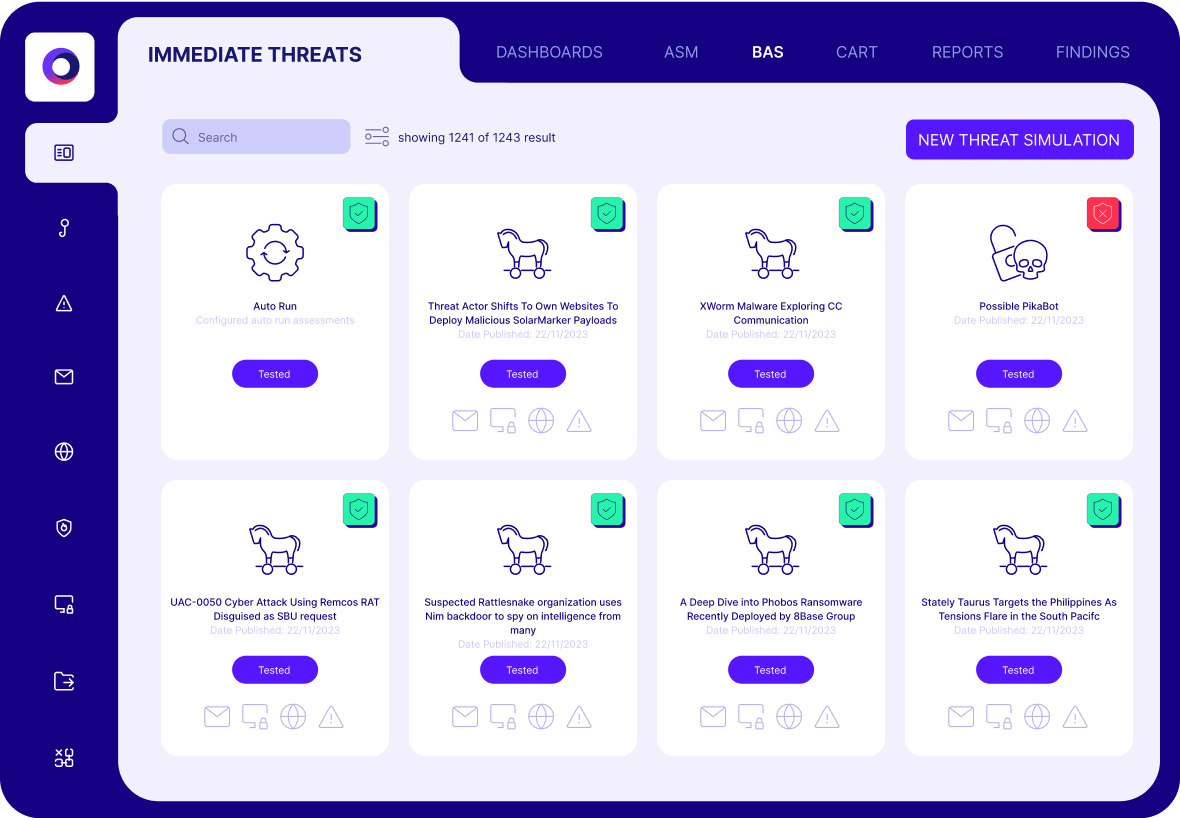
Industry-Leading Attack Scenario Library
Cymulate delivers unmatched automated security control and exposure validation with the industry's most expansive adversary simulation library. Run pre- and post-exploitation simulations across your entire architecture – even the cloud. With the innovative Cymulate AI Copilot, threat intelligence can be easily converted into tailored, automated tests in seconds, streamlining workflows and accelerating response.
Rated #1 in Exposure Management by G2
Cymulate Named Exposure Management Leader with 18 G2 Badges
Cymulate Named a Customer’s Choice
2025 Gartner® Peer Insights™ Voice of the Customer for
Adversarial Exposure Validation
Cymulate vs AttackIQ Comparison Chart
Use Case | Capabilities | AttackIQ |
Defensive Posture Optimization | Security controls integrations | Deep control integrations to validate detection and prevention with out-of-the-box connectors that just work. | Deployments and integrations are difficult with limited technical documentation, often requiring advanced technical expertise. | ||
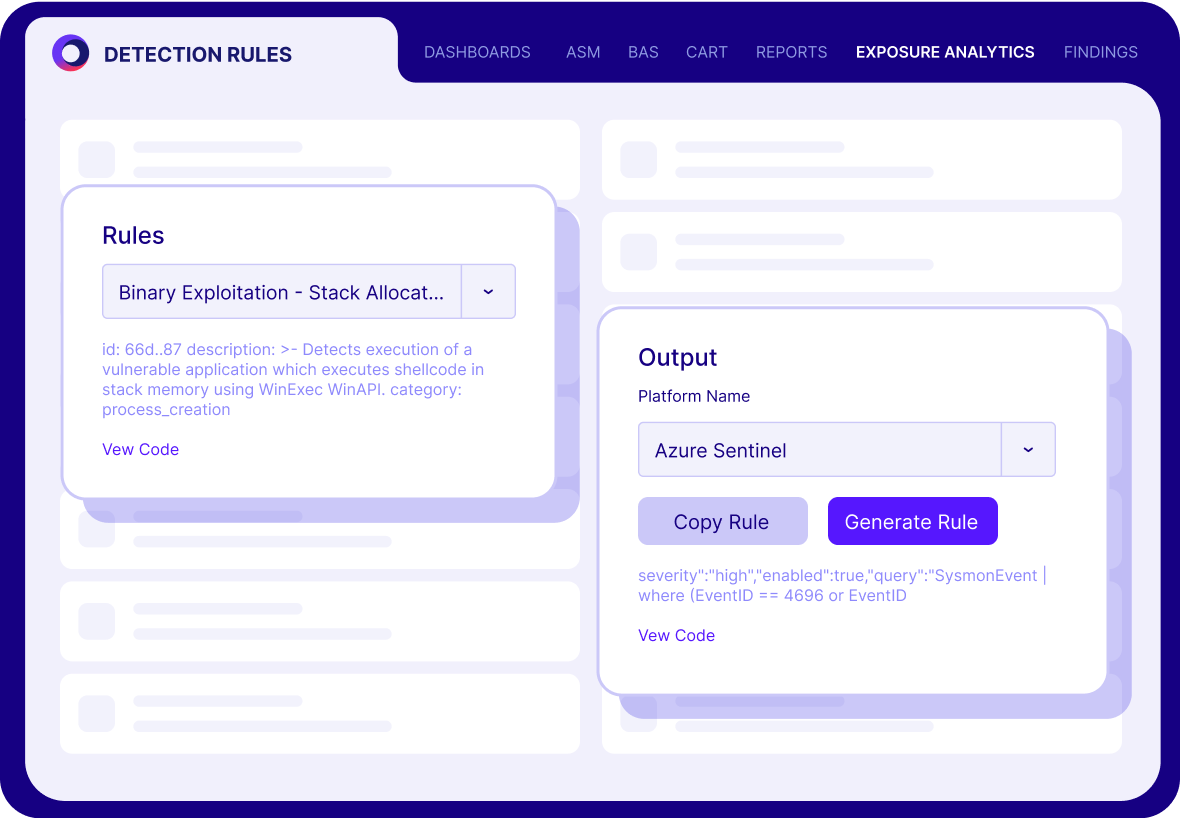
Threat-informed defenses | Automates IoC updates to controls. Custom detection rules for EDR, SIEM and XDR Control tuning guidance. | Missed detection rules are auto-generated, but sorting through remediations is time-consuming for users. | |||
Scale Offensive Testing | Attack Scenario creation workbench | Build custom attack chains from a library of >100,000 attack actions. Create custom scenarios/ attack actions. AI attack planner converts threat advisories and plain language prompts into custom attack chains. | Attack sequence scenario workflows are cumbersome and lack AI automation to convert threat intel to attack scenarios. | ||
Automation, extensible testing | Out-of-the box templates for threats, controls, cloud, Kubernetes and more. Modify templates and best practices for your specific environment (OS, cloud, databases, SaaS, etc.) | Adversary testing is limited in scope and lacks testing of cloud security controls. | |||
Attack paths | Automated red teaming provides white box testing to validate attack paths. | Recently added ASM capability to map attack paths, but lacks validation and asset correlation. | |||
Exposure Awareness | Automated & continuous testing | Easy and automated testing for continuous validation of threats, security controls, threats and response capabilities. | Provides automated and continuous testing, but limited flexibility in scheduling and setting no-testing blackout periods. | ||
Always current attack scenario knowledge | Daily updates of the latest threats and continuously adding new assessments. | New attack tests are infrequent, and updating on-premise solutions to gain the latest threat intel is very difficult. |
Exposure validation that filters out the noise, so you can focus on the exploitable.
Validate Controls
Find and fix your gaps
Validate Threats
Know your risk
Validate Response
Battle test your SOC
Why Companies Choose Cymulate Over AttackIQ
Immediate value with AI-guided workflows
Scale advanced custom testing
Ease of use
Clear, focused remediation
What our customers say about us
Organizations across all industries choose Cymulate for exposure validation, proactively confirming that defenses are robust and reliable-before an attack occurs.
Upgrading from AttackIQ to Cymulate is easy.
We’ve helped numerous clients upgrade from AttackIQ to Cymulate. We’ll help you build and customize production-safe assessments for all your environments (adding to the ones that AttackIQ covered), optimize your controls and reduce exposure risk.