Frequently Asked Questions
Product Overview & Purpose
What is Cymulate's Network Security Validation?
Cymulate's Network Security Validation is an automated solution that simulates both external (north–south) and internal (east–west) network traffic to test and optimize your security controls. It enables organizations to validate the effectiveness of web gateways, firewalls, intrusion prevention/detection systems, network segmentation, lateral movement controls, and data loss prevention mechanisms.
What is the primary purpose of network security validation with Cymulate?
The primary purpose is to proactively validate your network security controls against real-world attack scenarios, identify vulnerabilities, and optimize your defenses to reduce exposure risk and prevent data loss.
How does Cymulate simulate network attacks?
Cymulate uses packet capture (PCAP) files to replay both malicious and non-malicious network traffic, simulating real-world attack scenarios and exploits such as Print Nightmare, SIGRed, and Log4j. This approach provides insights into potential weaknesses in your network infrastructure.
What types of network traffic does Cymulate validate?
Cymulate validates both north–south (external to internal and vice versa) and east–west (internal) network traffic, covering a wide range of attack vectors and lateral movement scenarios.
How does Cymulate help organizations stay ahead of emerging threats?
Cymulate continuously updates its threat library and simulates the latest attack techniques, ensuring your network defenses are tested against current and emerging threats. The platform provides actionable insights and mitigation guidance to address new vulnerabilities as they arise.
Features & Capabilities
What are the key features of Cymulate's Network Security Validation?
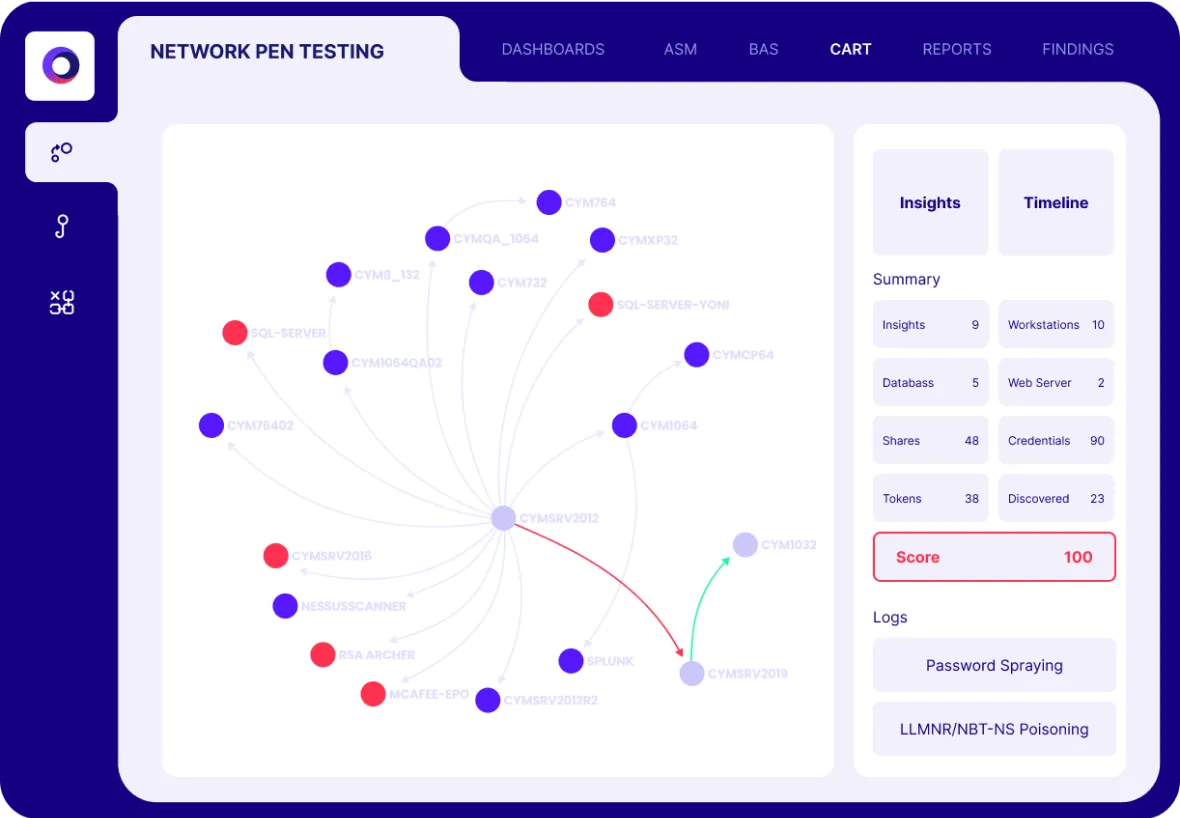
Key features include simulation of network traffic using PCAP files, network segmentation and penetration testing, validation of resilience to known exploits, detailed results dashboards and heatmaps, automated security validation, and continuous measurement of data loss exposure.
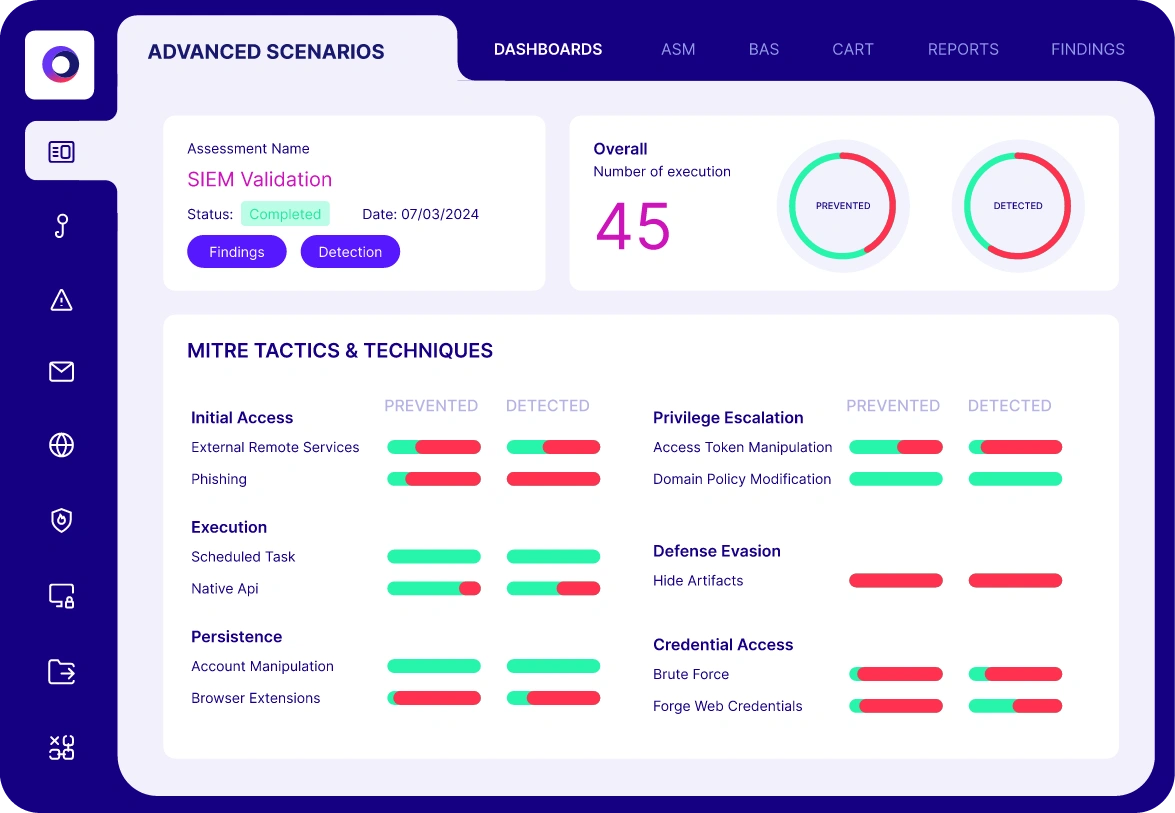
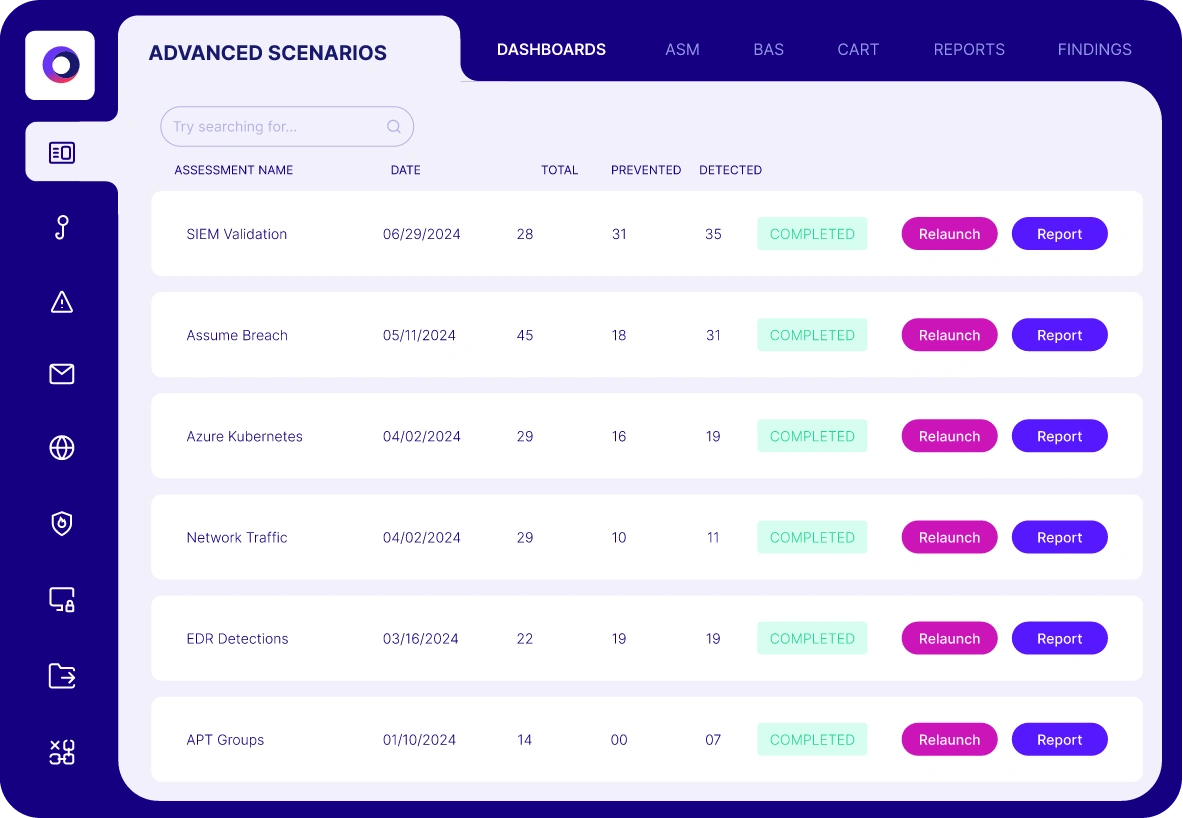
Does Cymulate provide dashboards and reporting for network security validation?
Yes, Cymulate offers detailed dashboards and heatmaps that display strengths and weaknesses in your network's prevention and detection capabilities, mapped to the MITRE ATT&CK® framework. These reports help you quickly identify and address security gaps.
How does Cymulate validate network segmentation and lateral movement controls?
Cymulate tests your internal network configuration and segmentation policies by simulating lateral movement using various techniques and protocols. This helps identify risks related to privilege escalation, detection evasion, and the spread of threats within your network.
Can Cymulate validate resilience to specific exploits like Print Nightmare or Log4j?
Yes, Cymulate can simulate network traffic exploits and vulnerabilities such as Print Nightmare, SIGRed, Log4j, and other CVEs to assess your network's resilience against known security weaknesses.
What benefits does automated network security validation provide?
Automated validation enables continuous testing of data exfiltration methods and transport protocols, identifies gaps in data loss prevention, optimizes security controls, and reduces exposure risk by continuously measuring and improving your network's defenses.
How does Cymulate help optimize data loss prevention (DLP) controls?
Cymulate identifies weaknesses in your DLP measures and provides mitigation guidance, enabling you to configure and tune your solutions for better protection against data leakage.
What metrics demonstrate the effectiveness of Cymulate's Network Security Validation?
Organizations have seen a 91% improvement in malicious file detection post-mitigation, a 50% improvement in the prevention of known exploit techniques, and up to 168 exploits prevented from a single policy change (Source: Cymulate Solution Results).
What integrations are available for network security validation?
Cymulate integrates with Akamai Guardicore for network security validation. For a full list of integrations, visit the Cymulate Partnerships and Integrations page.
Use Cases & Benefits
Who can benefit from Cymulate's Network Security Validation?
Organizations of all sizes and industries—including finance, healthcare, retail, media, transportation, and manufacturing—can benefit. Key roles include CISOs, security leaders, SecOps teams, red teams, and vulnerability management professionals.
What problems does Cymulate's Network Security Validation solve?
It addresses fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies in vulnerability management, and post-breach recovery challenges.
Are there real-world examples of Cymulate improving network security?
Yes. For example, Hertz Israel reduced cyber risk by 81% in four months using Cymulate. Other organizations have reported measurable improvements in detection, prevention, and operational efficiency. See more case studies at Cymulate Customers.
How does Cymulate support compliance and regulatory requirements?
Cymulate helps organizations meet compliance and regulatory requirements by providing automated, auditable validation of network security controls and generating reports that can be used for internal and external audits.
How does Cymulate help with data loss prevention validation?
Cymulate automates the testing of data exfiltration methods and transport protocols, identifies weaknesses in DLP controls, and provides actionable mitigation guidance to reduce the risk of sensitive data loss.
What customer feedback has Cymulate received for network security validation?
Customers praise Cymulate for its comprehensive and realistic validation, ease of use, and ability to demonstrate risk associated with security controls. Testimonials highlight its effectiveness in identifying gaps and providing actionable insights. (Source: Customer testimonials on Cymulate website)
How does Cymulate help communicate risk to stakeholders?
Cymulate provides easy-to-understand dashboards, reports, and quantifiable metrics that help security teams communicate risk and justify investments to business stakeholders and leadership.
How does Cymulate support continuous improvement in network security?
Cymulate enables ongoing validation and optimization of network security controls, providing actionable recommendations and tracking improvements over time to ensure continuous enhancement of your security posture.
Implementation & Ease of Use
How easy is it to implement Cymulate's Network Security Validation?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment.
What support resources are available for Cymulate users?
Cymulate offers comprehensive support including email, chat, a knowledge base, webinars, e-books, and an AI chatbot for real-time assistance and best practices. Support details are available on the Cymulate website.
Is Cymulate's platform user-friendly?
Yes, customers consistently praise Cymulate for its intuitive, user-friendly interface and dashboard, making it accessible for users of all skill levels. (Source: Customer testimonials)
How quickly can I see results after deploying Cymulate?
Organizations can see actionable results and insights almost immediately after deployment, thanks to Cymulate's agentless architecture and automated testing capabilities.
What are the prerequisites for deploying Cymulate?
The customer is responsible for providing the necessary equipment, infrastructure, and third-party software as per Cymulate’s pre-requisites. However, the platform itself is designed to integrate seamlessly into existing workflows.
Security & Compliance
What security and compliance certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and privacy standards. (Source: Security at Cymulate)
How does Cymulate ensure data security?
Cymulate ensures data security through encryption for data in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, and a tested disaster recovery plan. The platform also includes mandatory 2FA, RBAC, IP address restrictions, and secure development practices.
Is Cymulate GDPR compliant?
Yes, Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO), ensuring GDPR compliance.
How does Cymulate maintain application security?
The platform is developed using a strict Secure Development Lifecycle (SDLC), including secure code training, continuous vulnerability scanning, and annual third-party penetration tests. Employees also undergo ongoing security awareness training and phishing tests.
Pricing & Plans
What is Cymulate's pricing model for network security validation?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, schedule a demo with the Cymulate team.
How can I get a quote for Cymulate's Network Security Validation?
You can request a personalized quote by scheduling a demo with Cymulate. The team will assess your organization's needs and provide a tailored pricing proposal. Visit Cymulate's demo page to get started.
Competition & Differentiation
How does Cymulate's Network Security Validation differ from traditional network security testing?
Unlike traditional point-in-time assessments, Cymulate offers continuous, automated simulations with real-world attack scenarios, actionable dashboards, and integration with the latest threat intelligence. This enables organizations to validate and optimize their defenses in real time.
What makes Cymulate's Network Security Validation unique?
Cymulate stands out for its unified platform, continuous threat validation, AI-powered optimization, ease of use, and proven results such as significant reductions in exposures and improvements in operational efficiency. The platform is also recognized for its extensive threat library and rapid innovation cycle.
What industry recognition has Cymulate received?
Cymulate has been named a Customers' Choice in the 2025 Gartner® Peer Insights™ and recognized as a market leader for automated security validation by Frost & Sullivan. (Sources: Gartner Peer Insights, Frost & Sullivan)
Resources & Further Information
Where can I download the Network Security Validation solution brief?
You can download the solution brief directly from the Cymulate website at Network Security Validation Solution Brief.
Where can I find more resources on network security validation?
Visit the Cymulate Resource Hub for solution briefs, e-books, webinars, and best practices related to network security validation and other security topics.
How can I schedule a personalized demo of Cymulate's Network Security Validation?
You can book a personalized demo by visiting Cymulate's demo page and filling out the request form.