Abusing Microsoft Office Online Video
**Updated Note: As of November 12th, 2018, Trend Micro has discovered an in-the-wild sample of this logical bug seen in the TROJ_EXPLOIT.AOOCAI, using it to deliver the URSNIF information stealer (TSPY_URSNIF.OIBEAO).**
Cymulate’s research team has discovered a way to abuse the Online Video feature on Microsoft Word to execute malicious code (Read the press release here).
Attackers could use this for malicious purposes such as phishing, as the document will show the embedded online video with a link to YouTube, while disguising a hidden html/javascript code that will be running in the background and could potentially lead to further code execution scenarios.
This attack is carried out by embedding a video inside a Word document, editing the XML file named document.xml, replacing the video link with a crafted payload created by the attacker which opens Internet Explorer Download Manager with the embedded code execution file.
A workflow of how this security flaw could be produced:
1. Create a Word Document.
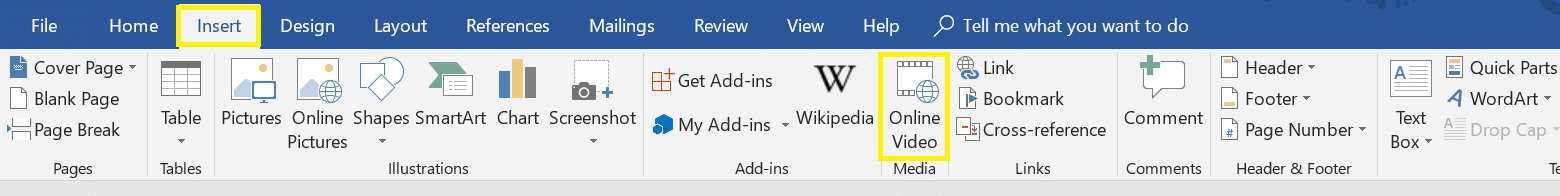
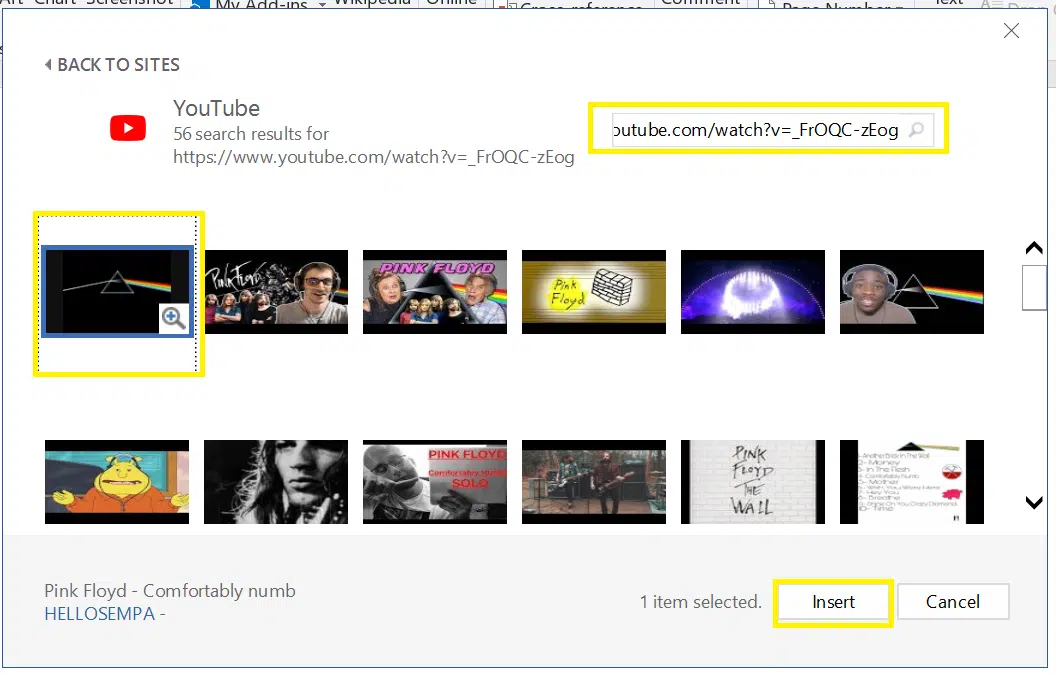
2. Embed an online video: Insert -> online video and add any YouTube video.
3. Save the Word document with the embedded online video.
4. Unpack the Word document:
Docx files are actually a package of all the media files that you may see in a docx file. If you unpack the file – either by using an unpacker or changing the docx extension to zip and unzipping it – there are several files and directories in a single docx file:
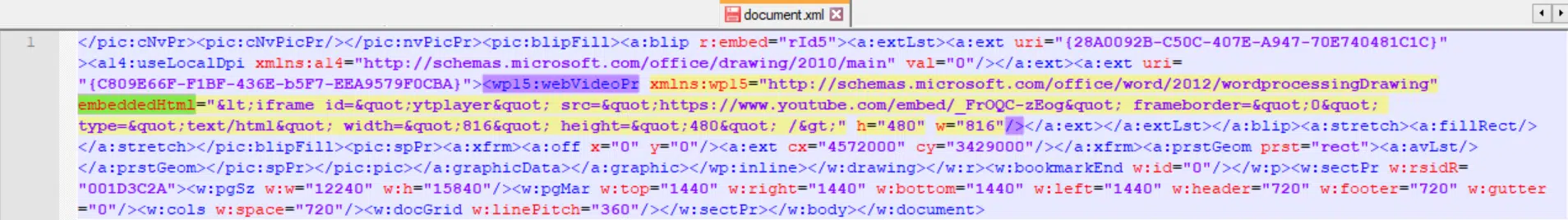
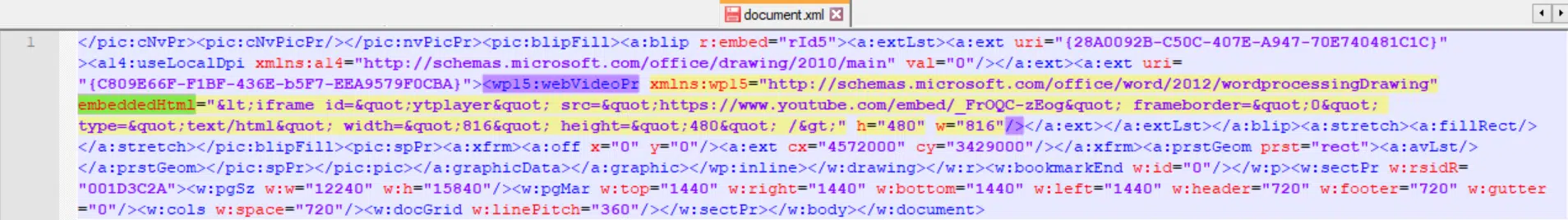
5. Edit the document.xml file under word folder
6. Inside the .xml file, look for embeddedHtml parameter (under WebVideoPr) which contains the Youtube iframe code. Replace the current iframe code with any html code / javascript to be rendered by Internet Explorer.
7. Save the changes in document.xml file, update the docx package with the modified xml and open the document.
We’ve created a PoC that contains the embedded executable (as a blob of a base64). Once run, this code will use the msSaveOrOpenBlob method to trigger the download of the executable by opening Internet Explorer Download Manager with the option to run or save the file.
Please note: No security warning is presented while opening this document with Microsoft Word.
Mitigation
You can choose from the following options.
1. Block Word documents containing the tag: “embeddedHtml” in the Document.xml file of the word documents.
**Updated Mitigation: As of November 12th, 2018**
2. Implement the filter with the YARA rule.
This solution was provided by Trend Micro™ XGen™ security.
rule EMBEDDEDHTML_WITH_SCRIPT {meta:description = “possible abuse of Office video embededHtml”strings:$embeddedHtmlre1 = /\sembeddedHtml=”[^”]+/$embeddedHtmlre2 = /\sembeddedHtml='[^’]+/$script = “<script” nocasecondition:(for any i in (1..#embeddedHtmlre1): (for any j in (1..#script): (@embeddedHtmlre1[i] < @script[j] and@script[j] < @embeddedHtmlre1[i] + !embeddedHtmlre1[i])))or(for any i in (1..#embeddedHtmlre2): (for any j in (1..#script): (@embeddedHtmlre2[i] < @script[j] and@script[j] < @embeddedHtmlre2[i] + !embeddedHtmlre2[i])))
Workaround
Block Word documents containing an embedded video.
Test the effectiveness of your security controls against possible cyber threats - book a demo to see Cymulate's platform in action.


