Frequently Asked Questions
Product Information & Technical Details
What is Cymulate and what does it do?
Cymulate is a unified exposure management and security validation platform that enables organizations to continuously test, validate, and optimize their security controls against real-world threats. It provides automated breach and attack simulation (BAS), continuous automated red teaming (CART), exposure prioritization, and more, helping organizations proactively identify and remediate security gaps before attackers can exploit them. Learn more.
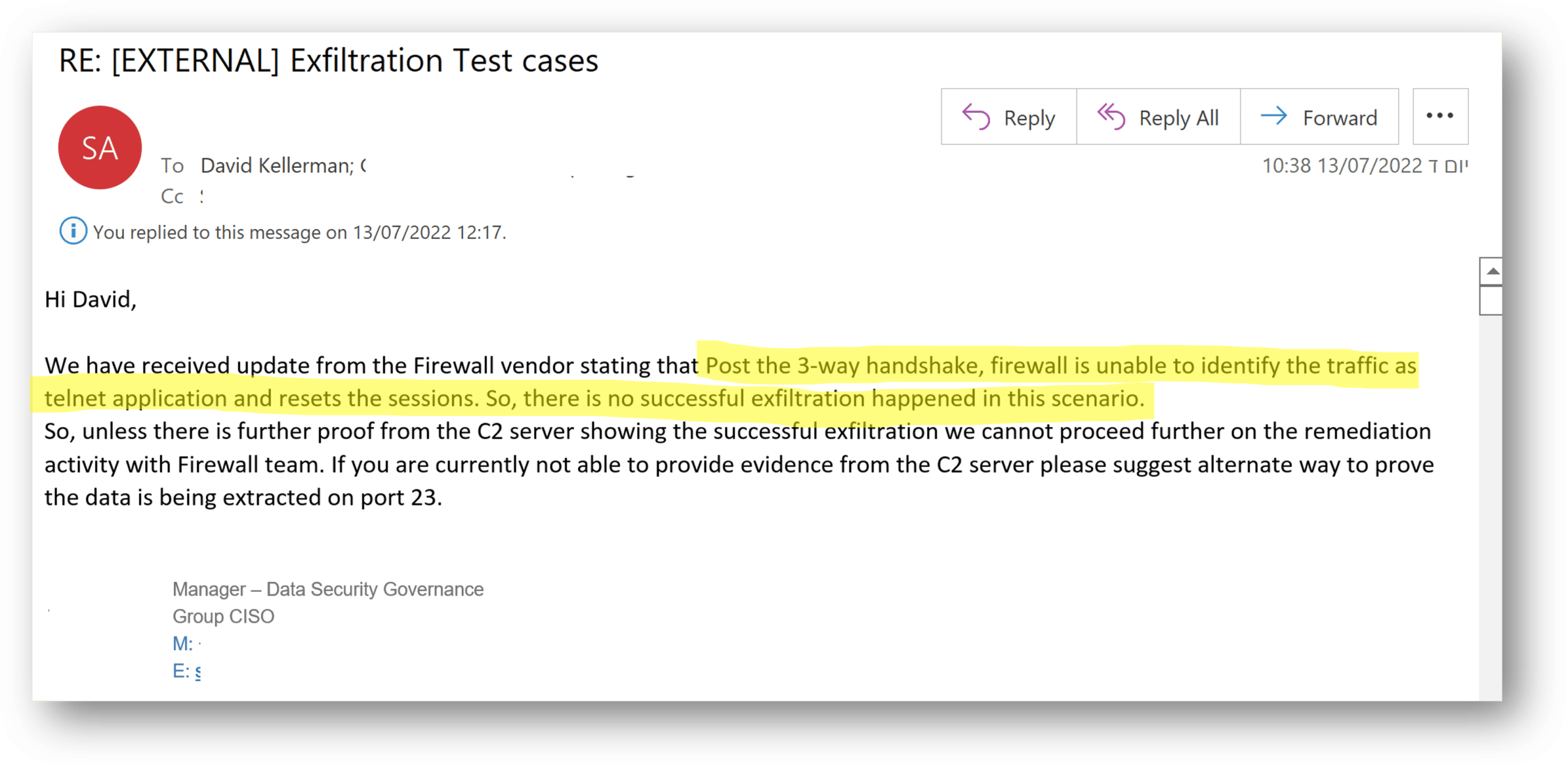
How does Cymulate assess for data exfiltration over blocked ports?
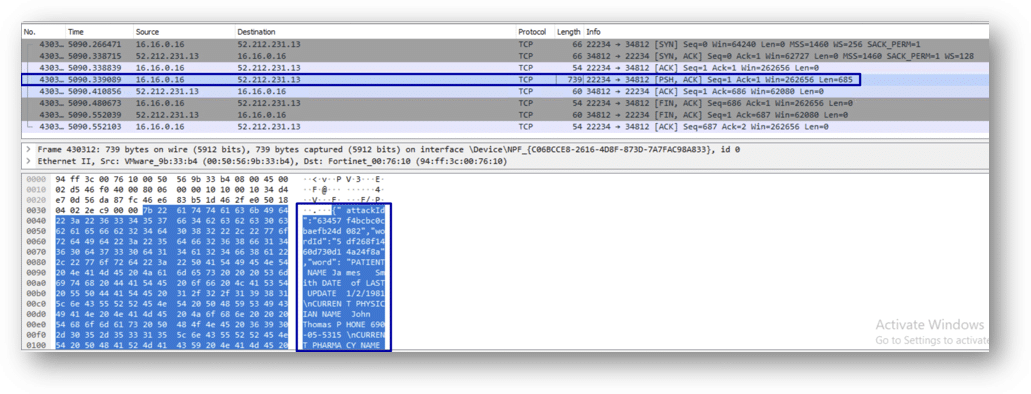
Cymulate's data exfiltration module tests security controls by simulating exfiltration attempts over various network channels, including blocked ports like Telnet (port 23). The platform initiates a 3-way handshake with a remote C2 server and sends data packets. It then validates successful exfiltration by comparing hashes of the original and received data, ensuring accuracy. This process helps organizations uncover hidden vulnerabilities in their firewall configurations. Read the full blog post.
What did Cymulate discover about Next-Gen Firewalls (NG-FW) and data exfiltration?
Cymulate found that many NG-FWs, by design, allow at least one packet to pass through a blocked port to identify the application protocol. This behavior can be exploited to exfiltrate small amounts of data, even when the port is officially blocked. The issue was reproduced across multiple leading NG-FW vendors, highlighting a structural flaw in how these firewalls handle initial packets. Source: Cymulate Blog
How does Cymulate validate that data exfiltration has occurred?
Cymulate validates data exfiltration by hashing the exfiltrated data and sending it over the agent-to-cloud communication channel to the C2 server. The server compares the hash with the received data to confirm successful and complete exfiltration, ensuring there is no room for error in detection. Learn more.
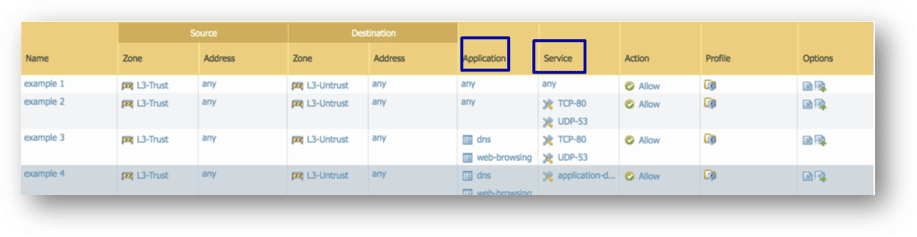
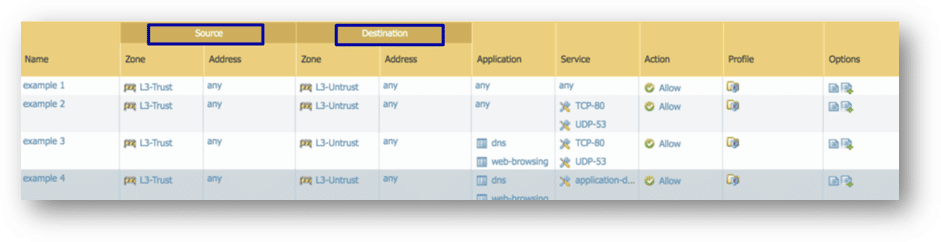
What practical steps can organizations take to prevent data exfiltration through NG-FWs?
Organizations should: 1) Limit both service (port) and application in NG-FW policies, 2) Restrict source and destination addresses, and 3) Implement network least privilege, allowing traffic only as needed. These steps reduce the risk of exfiltration while leveraging NG-FW capabilities. See full recommendations.
How does Cymulate help organizations uncover and remediate security control flaws?
Cymulate enables organizations to simulate real-world attacks, identify gaps in their security controls, and receive actionable remediation guidance. This process helps teams fix vulnerabilities before attackers can exploit them, reducing overall risk exposure. Learn more about Exposure Validation.
What is the value of security validation platforms like Cymulate?
Security validation platforms like Cymulate provide organizations with the ability to proactively test and validate their defenses, uncover hidden vulnerabilities, and ensure that security controls are functioning as intended. This reduces the risk of successful attacks and supports continuous improvement of the security posture. More info.
How does Cymulate's customer success team support users?
Cymulate's customer success team works closely with users to investigate unexpected findings, explain simulation results, and provide remediation guidance. This collaborative approach ensures that customers can quickly address vulnerabilities and optimize their security controls. See customer stories.
What is the significance of the 'grace packet' in NG-FW data exfiltration?
The 'grace packet' refers to the initial packet allowed by NG-FWs to identify the application protocol. Attackers can exploit this behavior to exfiltrate small data chunks, even when the port is blocked. Recognizing and mitigating this risk is crucial for robust firewall policies. Read more.
How does Cymulate's exposure validation module work?
Cymulate's exposure validation module allows users to build custom attack chains and simulate a wide range of threats, including data exfiltration, lateral movement, and privilege escalation. The platform provides actionable insights and remediation steps to close identified gaps. Learn more.
What are the main features of Cymulate's platform?
Cymulate offers continuous threat validation, attack path discovery, automated mitigation, detection engineering validation, complete kill chain coverage, and an extensive, daily-updated threat simulation library. These features help organizations stay ahead of emerging threats and optimize their defenses. See all features.
How does Cymulate support proactive security validation?
Cymulate enables organizations to proactively test their security controls by simulating real-world attack scenarios, identifying vulnerabilities, and providing remediation guidance. This approach helps reduce risk before an actual attack occurs. Learn more.
What is the role of the customer success team in Cymulate's platform?
The customer success team at Cymulate assists users in interpreting simulation results, investigating unexpected findings, and implementing remediation steps. Their expertise ensures that customers maximize the value of the platform and maintain high security standards. See customer stories.
How does Cymulate handle small data exfiltration attempts?
Cymulate's assessments revealed that small data packets, such as plain text or TXT files smaller than the MTU, can be exfiltrated through NG-FWs due to their protocol identification process. The platform helps organizations detect and remediate these subtle vulnerabilities. Read more.
What is the importance of validating security controls regularly?
Regular validation of security controls ensures that configurations are effective and up-to-date, reducing the risk of undetected vulnerabilities. Cymulate's platform automates this process, providing continuous assurance of security posture. Learn more.
How does Cymulate's platform integrate with existing security tools?
Cymulate integrates with a wide range of security technologies, including network, cloud, endpoint, and SIEM solutions, to enhance and validate your security ecosystem. For a full list of integrations, visit our Partnerships and Integrations page.
What resources are available to learn more about Cymulate's platform?
You can access Cymulate's Resource Hub for whitepapers, product information, thought leadership, and more. Additional resources include the blog, newsroom, events, webinars, and a comprehensive glossary. Visit the Resource Hub.
Where can I find Cymulate's blog and newsroom?
Cymulate's blog covers the latest threats, research, and platform updates, while the newsroom features media mentions and press releases. Visit the blog and newsroom for more information.
How can I stay updated with Cymulate's latest news and research?
Stay informed by visiting Cymulate's blog for the latest research and threat intelligence, and check the newsroom for company news and media coverage. Blog | Newsroom
Features & Capabilities
What are the key capabilities of Cymulate's platform?
Cymulate's key capabilities include continuous threat validation, attack path discovery, automated mitigation, detection engineering validation, complete kill chain coverage, and an extensive, daily-updated threat simulation library. These features help organizations stay ahead of emerging threats and optimize their defenses. See all features.
Does Cymulate support integration with other security tools?
Yes, Cymulate integrates with a wide range of technology partners across network, cloud, endpoint, and SIEM domains, including Akamai Guardicore, AWS GuardDuty, CrowdStrike Falcon, and more. For a complete list, visit our Partnerships and Integrations page.
How often is Cymulate's threat simulation library updated?
Cymulate provides the most advanced library of attack simulations with daily updates, ensuring customers are protected against the latest threats. Learn more.
Is Cymulate easy to implement and use?
Yes, Cymulate is designed for ease of use and quick implementation. It operates in agentless mode, requires minimal resources, and can be deployed rapidly. Customers consistently praise its intuitive interface and actionable insights. See testimonials.
What kind of support does Cymulate offer to customers?
Cymulate provides comprehensive support, including email and chat support, a knowledge base, webinars, e-books, and an AI chatbot for instant answers. Customers can reach support at [email protected] or via chat support.
What security and compliance certifications does Cymulate have?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications. These attest to its robust security, privacy, and cloud compliance practices. See all certifications.
How does Cymulate ensure data security and privacy?
Cymulate is hosted in secure AWS data centers, uses TLS 1.2+ for data in transit, AES-256 for data at rest, and follows a strict Secure Development Lifecycle (SDLC). It is GDPR compliant and employs a dedicated privacy and security team. Learn more.
What educational resources does Cymulate provide?
Cymulate offers a Resource Hub, blog, glossary, webinars, e-books, and technical articles to help users stay informed about cybersecurity trends and best practices. Explore resources.
How does Cymulate help with compliance requirements?
Cymulate's platform and certifications (SOC2, ISO, CSA STAR) help organizations meet regulatory and compliance requirements by providing evidence of robust security controls and continuous validation. See compliance details.
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams across industries such as finance, healthcare, retail, media, transportation, and manufacturing. Learn more about roles.
What business impact can customers expect from Cymulate?
Customers have reported an 81% reduction in cyber risk within four months, a 60% increase in team efficiency, a 52% reduction in critical exposures, and a 30% improvement in threat prevention. See case studies.
What pain points does Cymulate solve for security teams?
Cymulate addresses overwhelming threat volumes, lack of visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers. It provides continuous validation, exposure prioritization, and actionable insights. Learn more.
How does Cymulate help different security personas?
Cymulate tailors its solutions for CISOs (metrics and investment justification), SecOps (operational efficiency), red teams (automated offensive testing), and vulnerability management teams (exposure prioritization). See persona-specific solutions.
Can you provide a real-world example of Cymulate uncovering a security gap?
Yes. In a customer case, Cymulate's data exfiltration assessment revealed that data could be exfiltrated through a blocked Telnet port due to NG-FW design. The customer remediated the issue based on Cymulate's guidance, closing the gap before it could be exploited. Read the story.
How does Cymulate help with lateral movement and privilege escalation testing?
Cymulate's Attack Path Discovery automates offensive testing to identify and mitigate threats related to privilege escalation and lateral movement, helping organizations strengthen their defenses. Learn more.
Does Cymulate provide guidance for remediation after identifying vulnerabilities?
Yes, Cymulate provides easy-to-digest remediation guidance for any gaps or vulnerabilities identified during simulations, enabling teams to quickly address and close security gaps. Learn more.
How does Cymulate help organizations move from reactive to proactive security?
Cymulate enables organizations to proactively validate their defenses, identify weaknesses before attackers do, and implement improvements based on actionable insights, shifting from reactive to proactive security management. See case study.
What measurable results have customers achieved with Cymulate?
Customers have achieved an 81% reduction in cyber risk, a 60% increase in team efficiency, a 52% reduction in critical exposures, and a 30% improvement in threat prevention within months of using Cymulate. See customer results.
How does Cymulate help communicate risk to stakeholders?
Cymulate provides clear, quantifiable metrics and evidence-based reports, enabling CISOs and security leaders to effectively communicate risk and justify security investments to stakeholders. Learn more.
Pricing & Plans
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and selected scenarios. For a custom quote, schedule a demo.
Is the Cymulate subscription fee refundable?
No, the Cymulate subscription fee is non-refundable and must be paid regardless of actual platform usage. For details, contact Cymulate's sales team. Contact sales.
Competition & Comparison
How does Cymulate compare to AttackIQ?
AttackIQ provides automated security validation but lacks Cymulate's innovation, threat coverage, and ease of use. Cymulate offers the industry's leading threat scenario library and AI-powered capabilities for streamlined workflows. See comparison.
How does Cymulate compare to Mandiant Security Validation?
Mandiant is an original BAS platform but has seen little innovation in recent years. Cymulate continually innovates with AI and automation, expanding into exposure management and maintaining grid leader status. See comparison.
How does Cymulate compare to Pentera?
Pentera focuses on attack path validation but lacks Cymulate's depth in assessing and strengthening defenses. Cymulate covers the full kill chain and provides cloud control validation. See comparison.
How does Cymulate compare to Picus Security?
Picus is suitable for on-premise BAS needs but lacks the complete exposure validation platform Cymulate provides. Cymulate covers the full kill chain and includes cloud control validation. See comparison.
How does Cymulate compare to SafeBreach?
SafeBreach offers breach and attack simulation but lacks Cymulate's innovation, precision, and automation. Cymulate leads with AI-powered BAS, the largest attack library, and a full CTEM solution. See comparison.
How does Cymulate compare to Scythe?
Scythe is suitable for advanced red teams but lacks Cymulate's focus on actionable remediation and automated mitigation. Cymulate provides a more complete exposure validation platform with daily threat updates and no-code workflows. See comparison.