Frequently Asked Questions
Vulnerability Management & CTEM
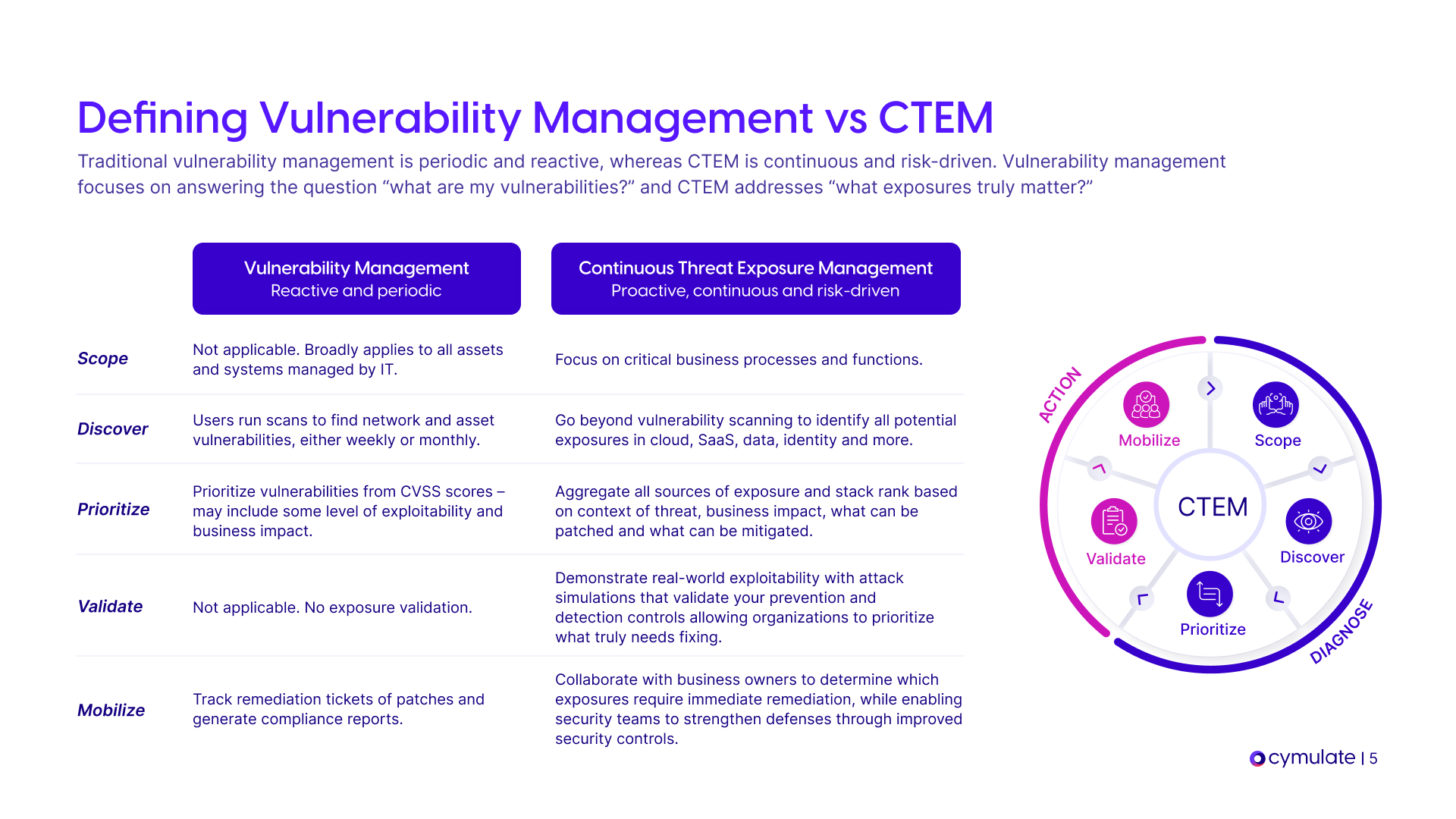
What is the main difference between traditional Vulnerability Management (VM) and Continuous Threat Exposure Management (CTEM)?
Traditional Vulnerability Management (VM) focuses on identifying and ranking vulnerabilities but often lacks context and validation. Continuous Threat Exposure Management (CTEM) expands this by continuously identifying, testing, and validating exposures across your environment—enabling you to focus mitigation on what truly poses a risk. CTEM shifts from a patch-all mindset to one rooted in real-world exploitability and business impact. Learn more.
Why should vulnerability management evolve to CTEM?
Vulnerability management must evolve to CTEM because traditional VM often results in overwhelming lists of critical patches, resource constraints, and ineffective prioritization. CTEM helps teams decide what to patch immediately, verify existing mitigations, and proactively strengthen threat resilience by focusing on validated, exploitable risks. Read the guide.
How does CTEM help vulnerability management teams prioritize what to patch?
CTEM enables vulnerability management teams to prioritize by continuously validating which vulnerabilities are exploitable in their environment, considering business context and threat intelligence. This allows teams to focus on what must be patched now versus what can be scheduled for later, reducing unnecessary workload and improving security outcomes. Learn more.
What questions can CTEM help vulnerability management teams answer?
CTEM helps VM teams answer: What must be patched now versus scheduled for the next update? Is the perceived severity already mitigated with existing security controls? How can security teams proactively build threat resilience through mitigation? These questions are addressed through continuous validation and contextual risk analysis. Read the guide.
How does Cymulate support the evolution from VM to CTEM?
The Cymulate Exposure Management Platform provides AI-powered CTEM with threat validation through real-world examples. It enables organizations to continuously discover, validate, and prioritize exposures, bridging the gap between detection and remediation. Learn more.
Where can I download the 'Vulnerability Management Must Evolve to CTEM' guide?
You can download the 'Vulnerability Management Must Evolve to CTEM' guide directly from Cymulate's website. The document will open in a new tab. Download Now.
What is exposure validation and why is it important for vulnerability management?
Exposure validation is the process of testing and confirming which vulnerabilities are truly exploitable in your environment. It is important because it helps cut through vulnerability noise, allowing teams to prioritize and focus on real, exploitable risks rather than theoretical ones. Learn more.
How does Cymulate help teams proactively build threat resilience?
Cymulate enables teams to proactively build threat resilience by continuously validating exposures, verifying the effectiveness of existing security controls, and providing actionable insights for mitigation. This approach ensures that security efforts are focused on the most critical risks. Read more.
What are the main challenges vulnerability management teams face today?
Vulnerability management teams face overwhelming lists of critical patches, resource constraints, ineffective prioritization, and a lack of visibility into which patches are most critical. CTEM addresses these challenges by providing continuous validation and prioritization based on real-world exploitability. Learn more.
How does Cymulate validate the effectiveness of existing security controls?
Cymulate continuously tests and validates the effectiveness of existing security controls by simulating real-world threats and exposures. This helps teams determine if perceived vulnerabilities are already mitigated and where additional action is needed. Learn more.
What is the focus of the guide 'Vulnerability Management Must Evolve to CTEM'?
The guide 'Vulnerability Management Must Evolve to CTEM' shows how Continuous Threat Exposure Management (CTEM) helps Vulnerability Management (VM) teams decide what to patch immediately, verify existing mitigations, and proactively strengthen their threat resilience. Read the guide.
How can I learn more about exposure validation for vulnerability management?
You can learn more about exposure validation for vulnerability management by reading the guide 'Vulnerability Management Requires Exposure Validation', which explains how to cut through vulnerability noise by validating, prioritizing, and focusing on real exploitable risks. Learn more.
What is the business impact of evolving from VM to CTEM?
Organizations that evolve from VM to CTEM can expect improved threat prevention (up to 30%), a 52% reduction in critical exposures, a 60% increase in operational efficiency, and an 81% reduction in cyber risk within four months, as demonstrated by customer case studies. Read the Hertz Israel case study.
How does Cymulate help with operational inefficiencies in vulnerability management?
Cymulate automates processes, integrates Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics into a single platform, reducing manual efforts and improving operational efficiency for vulnerability management teams. Learn more.
How does Cymulate address communication barriers for CISOs?
Cymulate provides validated exposure scoring and quantifiable metrics tailored to CISOs, enabling better communication and alignment with business objectives. This helps CISOs justify investments and communicate risk to stakeholders. Read the GUD Holdings case study.
What are some real-world examples of organizations benefiting from CTEM?
Hertz Israel reduced cyber risk by 81% within four months, Nemours Children's Health improved visibility and detection, and Banco PAN optimized security controls and prioritization using Cymulate's CTEM approach. See more case studies.
How does Cymulate help with cloud complexity in vulnerability management?
Cymulate provides dedicated validation features for hybrid and cloud environments, addressing new attack surfaces and validation challenges introduced by cloud adoption. Read the LV= case study.
How does Cymulate integrate with other security tools for exposure validation?
Cymulate integrates with a wide range of technology partners across network, cloud, endpoint, SIEM, and vulnerability management domains, including Akamai Guardicore, AWS GuardDuty, CrowdStrike Falcon, Rapid7 InsightVM, and more. See the full list of integrations.
What certifications does Cymulate hold for security and compliance?
Cymulate is certified for SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to industry-leading security and privacy standards. Learn more.
How easy is it to implement Cymulate for exposure management?
Cymulate is known for its quick and seamless implementation. It offers agentless deployment, requires minimal resources, and provides comprehensive support and educational resources to ensure a smooth onboarding process. Book a demo.
What support resources are available for Cymulate users?
Cymulate provides email and chat support, a knowledge base with technical articles and videos, webinars, and e-books on security validation best practices. See webinars.
How does Cymulate compare to other exposure management solutions?
Cymulate stands out with its unified platform, continuous threat validation, AI-powered optimization, complete kill chain coverage, ease of use, and extensive threat library. It is recognized for measurable outcomes such as a 52% reduction in critical exposures and an 81% reduction in cyber risk within four months. See competitor comparisons.
What is Cymulate's pricing model for exposure management?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and scenarios selected for testing and validation. For a detailed quote, you can schedule a demo with Cymulate's team. Schedule a demo.
Who can benefit from using Cymulate for exposure management?
Cymulate is designed for CISOs, Security Operations teams, Red Teams, and Vulnerability Management teams across industries such as finance, healthcare, retail, and technology. Its solutions address universal cybersecurity challenges and are tailored to different roles. Learn more.
What technical documentation is available for Cymulate's exposure management platform?
Cymulate offers a product whitepaper, custom attacks data sheet, technology integrations data sheet, solution briefs, and analyst reports such as the Gartner Market Guide for Adversarial Exposure Validation. See all resources.
How does Cymulate ensure product security and compliance?
Cymulate follows a strict Secure Development Lifecycle (SDLC), uses secure AWS data centers, enforces 2-Factor Authentication, Role-Based Access Controls, IP restrictions, and TLS encryption, and provides ongoing employee security training. Learn more.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive design and ease of use. For example, Raphael Ferreira, Cybersecurity Manager, stated, 'Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture.' Read more testimonials.
What is Cymulate's mission and vision?
Cymulate's mission is to empower organizations worldwide against threats and make advanced cybersecurity as simple and familiar as sending an email. The company aims to revolutionize how businesses approach cybersecurity by fostering a proactive stance against threats. Learn more.
How does Cymulate address fragmented security tools in vulnerability management?
Cymulate integrates Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics into a single platform, reducing complexity and improving efficiency compared to using disconnected tools. Learn more.
What are the key capabilities of Cymulate's exposure management platform?
Cymulate offers continuous threat validation, exposure awareness, defensive posture optimization, scalable offensive testing, cloud validation, team collaboration, and comprehensive integration of BAS, CART, and Exposure Analytics. See a demo.
How does Cymulate help with unclear prioritization in vulnerability management?
Cymulate ranks vulnerabilities based on exploitability, business context, and threat intelligence, enabling focused remediation efforts and evidence-based prioritization. Learn more.
What are the main pain points Cymulate solves for vulnerability management teams?
Cymulate addresses overwhelming threat volumes, lack of visibility, unclear prioritization, operational inefficiencies, fragmented tools, cloud complexity, and communication barriers for vulnerability management teams. Learn more.