Clone Phishing
Clone phishing is a sophisticated email phishing attack that deceives recipients by replicating a legitimate email they previously received. Attackers craft a near-exact copy of an authentic email, modifying only certain elements—like links or attachments—to redirect users to malicious sites or install malware.
Clone phishing works by leveraging familiarity and trust, making it a challenging threat to detect and prevent.
How Does Clone Phishing Work?
Clone phishing attacks use a series of calculated steps to deceive the target. Here’s a detailed breakdown:
- Interception of the original email: The attacker begins by intercepting or accessing a legitimate email, often containing a link or attachment that the recipient interacted with before. This email might be a previous invoice, shipping confirmation, or other transactional messages.
- Cloning the email: Next, the attacker creates a nearly identical copy of the original email. This cloned email replicates every detail, including the subject line, formatting, and sender details. The attacker may use a lookalike email address with slight variations, making it hard to distinguish from the original.
- Replacing links or attachments: The attacker replaces legitimate links or attachments in the cloned email with malicious ones. The links may lead to fake login pages for credential harvesting, or the attachments could contain malware to infect the recipient’s system.
- Sending the clone email: The attacker sends the cloned email to the target, often posing it as a follow-up or resend of the original message. This tactic influences the recipient’s trust in the original sender, making them more likely to interact with the content.
- User interaction: If the target opens the malicious attachment or clicks the altered link, the attacker gains access to their information or network. This could result in credential theft, malware infection or other security breaches.
- Psychological tactics: Clone phishing relies on exploiting the recipient’s familiarity and trust in the original email. Attackers may use urgent language such as “urgent,” “resend,” or “follow-up” to prompt a quick response, making the recipient less likely to notice minor discrepancies in the email.
Recognizing a Clone Phishing Email: Key Phishing Signs to Watch For
While clone-phishing emails are crafted to appear genuine, there are several phishing signs to watch out for that can help preventing falling victim to a phishing scam:
- Sender email discrepancies: Clone phishing emails often use subtle variations in the sender’s address, like an added character or a different domain. Always double-check the sender’s email address for slight changes.
- Suspicious or pressuring language: Urgent or pressuring language, like “Please respond ASAP” or “Action Required,” is often a red flag in phishing emails. These tactics push recipients to act quickly without examining the email closely.
- Unexpected resends or follow-ups: Receiving an “unexpected resend” or follow-up email for a message you’ve already seen can indicate clone phishing. If you’re unsure of the legitimacy of the resend, verify with the sender.
- Modified links: Hover over any links in the email to reveal the URL. Clone phishing emails may use lookalike domains with slight changes (e.g., .com vs. .net). Always check that links direct you to the correct website.
- Altered attachments or filenames: Attackers may slightly change filenames or use uncommon formats like .exe instead of .pdf to bypass filters or trick recipients into downloading malware.
Clone Phishing vs. Spear Phishing: Key Differences
Clone phishing and spear phishing are both targeted email phishing techniques, but they differ in execution:
Clone phishing: In clone phishing, attackers copy an existing email from a recognized source, modifying it with malicious elements. Clone phishing emails are often used for larger-scale attacks, as they can replicate messages from well-known brands or services, making them appear trustworthy.
Spear phishing: Spear phishing involves crafting highly targeted messages for specific individuals or small groups. These emails contain personal information or context that makes them appear genuine, leveraging the individual’s job role, recent activity, or other specific details.
For example, a clone phishing attack might impersonate a common transactional email, such as a shipment notification. In contrast, spear phishing might target an executive with a fake email about an internal document, including personal or work-specific details, to increase credibility.
What to Do if You Receive a Clone Phishing Email
If you suspect you’ve received a clone phishing email, take immediate steps to protect both yourself and network. Start by alerting your IT or security team; reporting the suspicious email allows them to investigate and potentially halt the attack's spread within your organization. Next, change any account passwords you believe might be compromised, choosing strong, unique passwords to limit further unauthorized access.
It’s also essential to review recent account activity, checking for any unusual logins or setting changes that could indicate a breach. If you think others may have received the cloned email, notify your contacts to prevent them from interacting with it. Finally, run a full security scan on your device using antivirus or anti-malware software to ensure no malicious software has been installed.
Preventing Clone Phishing
Effective phishing prevention involves training, technology, and validation measures. Here are several proactive defenses:
1. Multi-Factor Authentication (MFA): MFA adds a crucial layer of security, making it harder for attackers to access accounts even if they have obtained credentials. Implementing MFA is a vital step in email security.
2. Phishing awareness campaigns: Regular training and phishing awareness campaigns educate employees on phishing tactics, including clone phishing, and the SLAM method—an approach for identifying suspicious sender details, links, attachments, and messages. Equipping employees to recognize these phishing signs is essential for preventing attacks.
3. Anti-phishing software: Email security solutions with anti-phishing capabilities can detect and block clone phishing emails. These tools scan for modified links, attachments, and other red flags to prevent malicious emails from reaching the inbox.
4. Security control validation: Regularly testing and validating security controls can ensure your defenses are up-to-date against clone phishing and other threats. Security control validation from Cymulate allow organizations to assess the effectiveness of their email security measures in real-time.
Organizations can significantly reduce the risk of clone phishing attacks by implementing these phishing prevention strategies.
How Cymulate Can Help Prevent Phishing Attacks
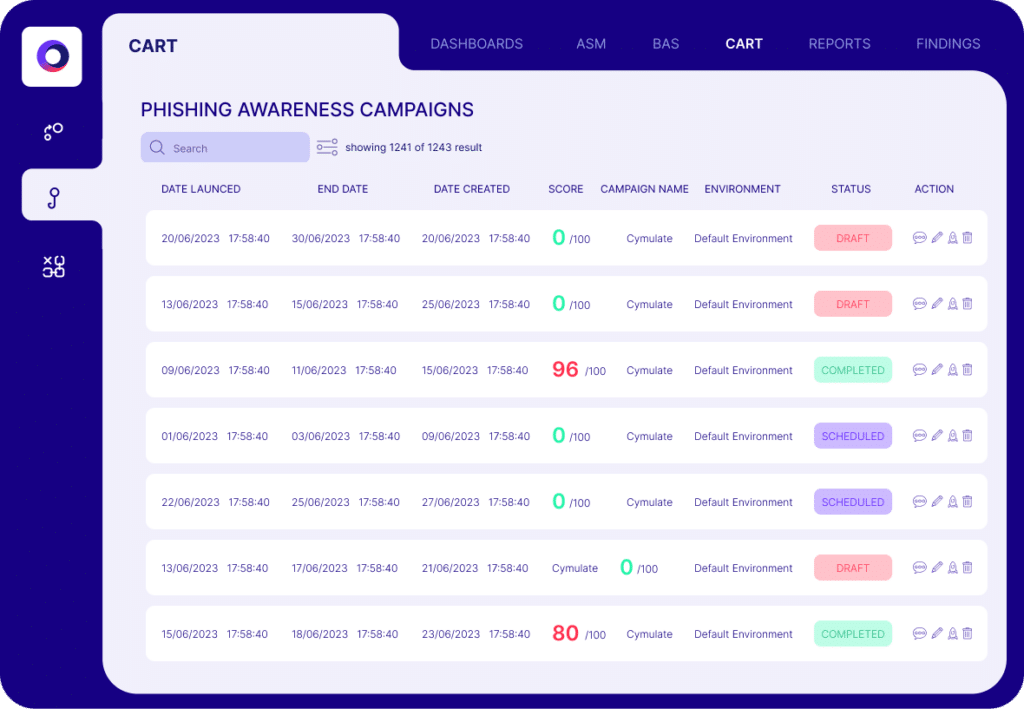
Cymulate's Phishing Awareness campaigns evaluate employees' security awareness levels by simulating phishing attacks and identifying potential target opportunities.
Creating a customized phishing simulation with the user-friendly drag-and-drop menu is quick and easy. Options include the selection of email text, attachments with production-safe payloads, fake landing pages, and more.
Employees' interactions with the mock phishing emails are automatically recorded, logging hazardous behaviors such as clicking links or entering credentials. This identifies employees in need of additional phishing awareness training.
Key Takeaways
- Clone phishing is a targeted email phishing tactic that involves duplicating a legitimate email and modifying it to include malicious links or attachments.
- Recognizing phishing signs such as sender discrepancies, urgent language, unexpected follow-ups and modified links can help individuals identify clone phishing emails.
- Phishing prevention strategies, such as multi-factor authentication, phishing awareness campaigns, anti-phishing software and security control validation are critical to defending against clone phishing.
- The role of Cymulate in clone phishing prevention includes phishing simulations and security control validation, providing organizations with tools to continuously test and improve their email security.
By recognizing clone phishing and implementing effective prevention measures, individuals and organizations can enhance their email security and minimize the risk of phishing-related breaches.
