Credential Dumping
What is Credential Dumping? Techniques, Risks and How to Defend Against It
Credential dumping is an attack technique in which adversaries extract authentication data (usernames, password hashes, Kerberos tickets, etc.) from a system’s memory or storage. In practice, attackers often target Windows systems’ Local Security Authority (LSASS) process or related stores (SAM database, registry) to harvest credentials in cleartext or hashed form.
Once obtained, these credentials can be reused to escalate privileges or move laterally. For example, Mimikatz is a widely used open-source utility that reads LSASS memory to dump plaintext passwords and NTLM hashes.
Other tools include LaZagne, which extracts saved passwords from browsers and applications, and the older Windows Credential Editor (WCE), which similarly dumps password hashes from memory.
Unlike credential stuffing (which tries leaked credentials against unrelated services), credential dumping uses obtained hashes or tickets to access devices within the same network.
Credential dumping is explicitly catalogued by MITRE as ATT&CK Technique T1003 (“OS Credential Dumping”), under the Credential Access tactic.
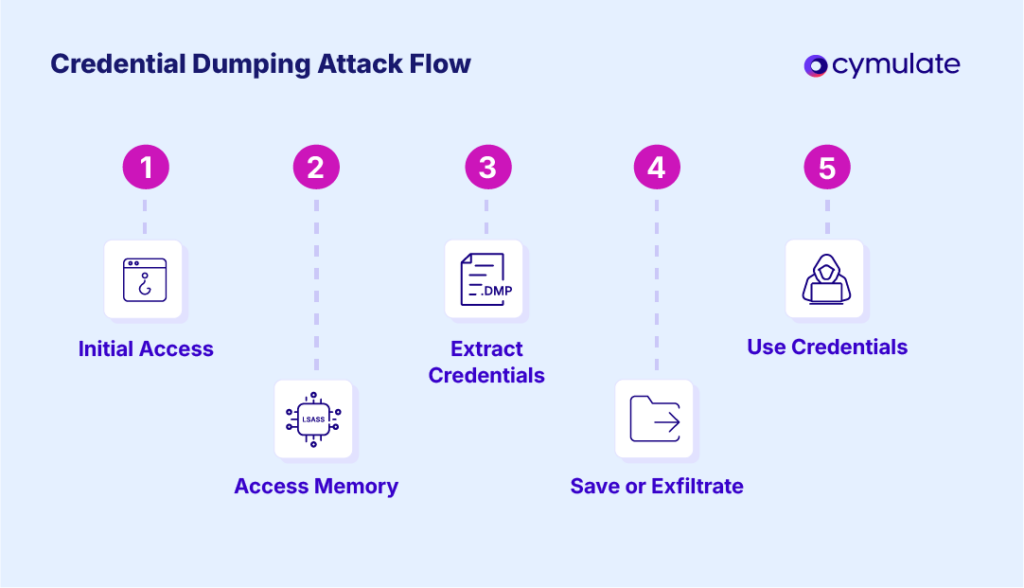
A typical dumping attack proceeds in stages:
- an attacker first gains local access to a machine (often via malware, exploit, or phishing)
- then copies or extracts credentials from system memory or files and
- finally writes those credentials to a file for exfiltration or reuse.
Once these credentials are in hand, the attacker can log into other systems on the network, escalated privileges or even create new domain tickets (Golden Tickets). In short, credential dumping turns a single system compromise into full domain compromise, allowing “the entire network [to be] compromised or taken down” if unchecked.
Common credential-dumping tools and their purposes:
| Tool | Primary Function |
| Mimikatz | Extracts plaintext passwords and hashes directly from Windows memory (LSASS). Enables pass-the-hash and Kerberos ticket forging. |
| LaZagne | Recovers stored credentials (passwords, tokens) from various local stores (browsers, apps, OS) on Windows, Linux, and macOS. |
| Windows Credential Editor (WCE) | A legacy Windows tool that dumps password hashes from LSASS memory. Often used by attackers when Mimikatz is not available. |
| Other tools (examples) | ProcDump or gsecdump (to dump memory), Pwdump (to dump SAM/NTLM), DPAPI tools for decrypting protected data, Kerberoasting scripts, etc. |
These tools operate under the broad “Credential Access” category, extracting account passwords or hashes for offline use. In many attacks, adversaries also misuse legitimate features like Windows Shadow Copies or registry queries to obtain credentials.
Why Credential Dumping is Particularly Dangerous
Credential dumping poses a significant cybersecurity threat because it allows attackers to escalate privileges and gain deep access to internal networks. Once attackers extract credentials—such as password hashes or Kerberos tickets—they can impersonate legitimate users and move laterally across systems, often undetected.
Immediate Privilege Escalation
Stolen credentials enable attackers to escalate their privileges quickly. For example, if an attacker obtains a domain administrator's hash from the LSASS (Local Security Authority Subsystem Service) process on a domain controller, they can impersonate any user on the network. This opens the door to high-level system control without the need for plaintext passwords.
Attackers frequently use techniques like pass-the-hash or pass-the-ticket. These allow them to inject stolen hashes or Kerberos tickets into sessions and navigate across systems as if they were authorized users. Tools like Mimikatz, originally developed to support pass-the-hash attacks, remain popular for facilitating this kind of lateral movement.
Golden Ticket Attacks
If attackers manage to dump the KRBTGT account’s hash—the key used to sign Kerberos Ticket Granting Tickets (TGTs)—they can forge a Golden Ticket. This forged TGT effectively grants unrestricted access across the entire domain.
According to MITRE, obtaining the KRBTGT hash through credential dumping is a common precursor to Golden Ticket attacks. This method allows threat actors to bypass authentication mechanisms entirely and persist in the environment undetected for extended periods.
Facilitating Lateral Movement
Credential dumping is also a gateway to lateral movement. Attackers use the stolen hashes to authenticate with other systems on the network, masquerading as legitimate users. Once on a new host, they repeat the dumping process—harvesting more credentials and further expanding their control.
Cymulate warns that this tactic allows attackers to “infect other devices on the same network and escalate [their] privileges by stealing more valuable account credentials.” With this technique, a single foothold can lead to total domain compromise.
Used by Advanced Threat Actors
Many advanced persistent threat (APT) groups and ransomware operators use credential dumping as a key tactic. For example:
- FIN6 and FIN8, financially motivated cybercrime groups, are known to run Mimikatz or Windows Credential Editor on compromised systems to steal domain credentials.
- The Chinese-linked group GALLIUM has used custom builds of Mimikatz and PowerShell scripts to dump LSASS memory and extract credentials.
Once credentials from even a single machine are dumped, attackers can often compromise the entire network.
Detection and Indicators of Credential Dumping
Detecting credential dumping relies on careful monitoring of system behavior, especially around processes that access sensitive memory like LSASS. While some legitimate tools interact with LSASS, malicious activity often follows recognizable patterns that defenders can track using system telemetry, behavioral analytics and modern endpoint detection solutions.
LSASS Access Monitoring
A primary indicator of credential dumping is unusual access to the LSASS process (lsass.exe), which stores credentials in memory. Tools like Mimikatz typically open a full-access handle to LSASS to extract sensitive data.
- Sysmon (System Monitor), when properly configured, can detect this behavior.
- Event ID 10 (Process Access) logs whenever one process accesses another.
- According to Red Canary, “LSASS abuse often involves a process accessing LSASS to dump its memory contents” and such access will show up in these logs.
Security analysts should watch for nonstandard processes (e.g., powershell.exe, unknown binaries) accessing lsass.exe with full privileges. Routine system management tools may access LSASS occasionally, but any unexpected process doing so should trigger an alert.
Suspicious DLL Loads and File Creation
Credential dumping tools often load specific DLLs or create dump files during execution:
- Sysmon Event ID 7 logs image loads.
- Event ID 11 logs file creation.
If a tool like procdump.exe or a custom script loads dbghelp.dll or writes a large file sourced from LSASS memory, it’s likely a dump attempt. It looks for suspicious DLLs often used by dumpers (e.g., dbgcore.dll, dbghelp.dll).
Unusual Authentication and Lateral Movement
Credential dumping often leads to lateral movement, and defenders should track related indicators:
- A spike in authentication failures, or an account suddenly logging in from unfamiliar systems, could signal hash reuse.
- Monitor for internal RDP, SMB, or WinRM sessions originating from compromised hosts.
- Behavioral analytics and User and Entity Behavior Analytics (UEBA) tools may flag accounts accessing new hosts or performing privileged actions not seen before.
For example, if an account that usually logs into one workstation suddenly logs into five servers in quick succession, it may be the result of stolen credentials in use.
MITRE ATT&CK Framework Mapping
Credential dumping is categorized under MITRE ATT&CK Technique T1003, with important sub-techniques including:
- T1003.001 – LSASS Memory
- T1003.002 – SAM Database
Each sub-technique has documented detection methods. Windows 10 and later support LSA Protected Process Mode, which limits LSASS access—even from SYSTEM-level processes—when enabled via features like Credential Guard.
According to MITRE, enabling Attack Surface Reduction (ASR) rules can also prevent untrusted code from interacting with LSASS. These system-level configurations are strong proactive defenses.
Role of Endpoint Protection and SIEM
Modern Endpoint Detection and Response (EDR) solutions and antivirus tools offer built-in protections. Microsoft Defender for Endpoint, for instance, logs LSASS access events and can block known tools like Mimikatz.
Platforms like SentinelOne are capable of terminating malicious processes that interact with credential storage.
Security teams should configure their Security Information and Event Management (SIEM) systems to alert on:
- Event ID 10 access anomalies
- Abnormal DLL loads
- Suspicious binaries reading from memory
Red Canary advises building detection logic around “obviously suspicious” handle accesses and correlating them with lateral movement behavior.
By running these controlled tests, security teams can ensure that SIEM rules, endpoint agents and behavioral analytics systems trigger alerts appropriately. This proactive approach builds confidence in an organization’s ability to detect and respond to real-world threats.
Prevention and Mitigation for Credential Dumping
Preventing credential dumping is ultimately about reducing the attack surface and credentials available to steal. Key strategies include:
- Protect LSASS and credentials in memory
- On Windows 10 and later, enable Credential Guard (which uses virtualization to isolate secrets) and configure LSA as a protected process. As MITRE advises, use Windows Attack Surface Reduction rules to block untrusted reads of LSASS.
- Ensure security updates are applied, since Microsoft periodically patches privilege escalation bugs that enable dumper tools to bypass protections.
- Use application whitelisting
- Prevent unauthorized tools from running. For example, AppLocker or Software Restriction Policies can block executables like Mimikatz or LaZagne by default.
- Blocking known credential-dumping binaries forces attackers to use more complex methods (which are easier to detect).
- Red Canary’s analyses also note that enforcing whitelists for utilities that can read the registry or memory is an effective defense.
- Patch and update systems
- Many credential dumping attacks exploit unpatched vulnerabilities (e.g. in LSASS handling, or remote code execution on domain controllers).
- Always apply security updates promptly. If an attacker cannot get initial admin access, they cannot dump credentials.
- Enforce strong authentication and least privilege
- Use unique, strong passwords and change default passwords. 1Kosmos warns that if one leaked password is reused across systems, a single dump compromises them all. Require multi-factor authentication (especially for remote and admin logins) so that a dumped hash alone is not enough.
- Apply the principle of least privilege: limit domain admin and local admin accounts, remove unnecessary privileges, and consider Privileged Access Workstations for admins. Secrets sprawl also invites attack: store admin passwords securely (e.g. with Microsoft’s LAPS) and avoid shared accounts.
- Audit and rotate credentials
- Regularly audit user and service accounts. Disable or rotate old or unused accounts and keys. If an admin account is compromised, consider it breached and rotate its password immediately. Monitor privileged accounts for anomalous activity.
- As a general precaution, treat any exposure of credentials as a serious incident: block them on additional systems and require new authentication factors if possible.
Credential Dumping Simulations with Cymulate
The Cymulate Exposure Validation platform offers a safe and controlled way to simulate credential-dumping attacks, helping organizations test their defenses against real-world techniques.
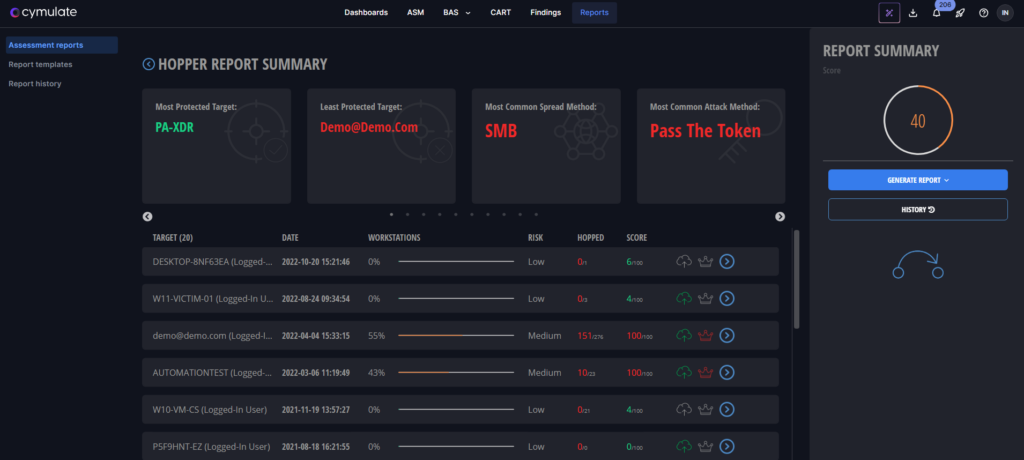
Cymulate's Hopper module ensures a safe testing environment by utilizing non-destructive attack methods exclusively. These methods include activities like credential dumping, pass the hash, and kerberoasting. Cymulate's approach avoids using exploits or Common Vulnerabilities and Exposures (CVEs) that may disrupt normal process execution or business operations.
As soon as the Hopper assessment is completed, or in the case that the connection was lost, an automatic cleanup mechanism is triggered. This cleanup process ensures that no remnants of the assessment activities remain, maintaining the integrity of the environment.
By employing non-destructive attack methods and implementing automatic cleanup mechanisms, Cymulate's Hopper module provides organizations with a safe and controlled way to evaluate their security posture. This approach allows for thorough assessments without causing disruptions or compromising the integrity of the environment being tested.
Mapping Exposure with Lateral Movement Assessments
Beyond isolated dumping steps, Cymulate offers Lateral Movement Assessments. These tests map out how dumped credentials could be used across Active Directory to compromise additional machines and accounts. This helps security teams understand not just if dumping is possible, but how far an attacker could go once credentials are stolen.
Key Takeaways
Credential dumping remains one of the most dangerous attacker techniques because it can escalate a local compromise into full domain control. Effective defense requires both prevention and detection. Organizations must harden LSASS, keep systems patched, enforce least privilege and require multi-factor authentication.
At the same time, they need to monitor LSASS access, detect known dumping tools and investigate abnormal behavior patterns.
Frameworks like MITRE ATT&CK T1003 help structure defenses, while platforms like Cymulate offer safe simulations to test and strengthen protections.
Enabling Windows security features (e.g., Credential Guard, LSA protection, Attack Surface Reduction) and using whitelisting policies can block many dumping attempts. Meanwhile, auditing credentials and continuous validation testing ensure attackers are caught early even if some credentials are compromised.
As Cymulate puts it, these are “hard-to-detect tactics,” so preparation, simulation, and validation are your best defense.