11 Email Threats Your Organization Needs to Know
Email remains the primary entry point for cyberattacks. From nation-state actors to low-level cybercriminals, adversaries continually exploit the ubiquity and human trust inherent in email communication.
Malicious emails can lead to operational paralysis, financial loss and reputational damage. Despite advancements in secure email gateways and filtering technologies, email threats continue to evolve in complexity and evasiveness.
What are Email Threats?
Email-based threats are tactics used by threat actors to infiltrate organizations via email communication channels. These threats exploit human psychology, technical misconfigurations and lapses in email security controls.
Attackers leverage various payload delivery mechanisms, social engineering techniques and evasion tactics to bypass defenses.
The increasing sophistication of these threats underscores the need for proactive security validation and continuous assessment of email security configurations.
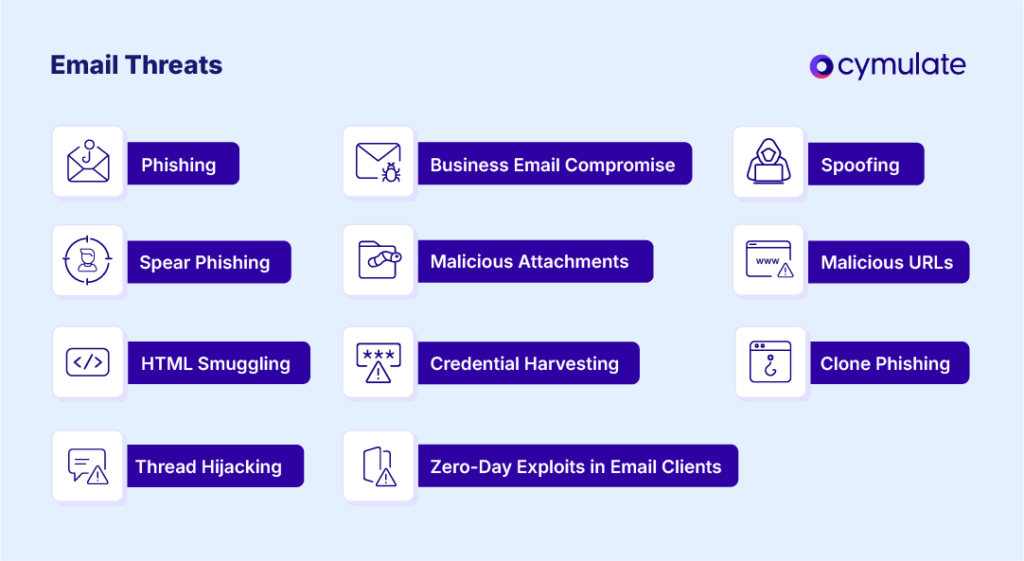
Breaking Down the Most Common Email Threats
Let’s look at 11 different email threats your organization must understand. Knowledge of these threats can help minimize their impact if your organization gets hit. We’ll also share how using Cymulate’s Exposure Validation platform can help ensure your security controls are prepared to handle such attacks.
1. Phishing
- Definition: A form of social engineering where attackers trick recipients into clicking malicious links or downloading attachments by masquerading as a legitimate source.
- Example: A fake email from a bank prompting users to verify their account by clicking on a credential-harvesting link.
- Challenge: Generic phishing is widespread and can overwhelm users and filtering systems alike.
- Control Validation: Cymulate's phishing simulation capabilities allow security teams to test and measure user susceptibility and email gateway effectiveness.
2. Spear Phishing
- Definition: Spear phishing is a targeted version of phishing that uses personalized information to increase credibility.
- Example: An attacker poses as a company executive and sends an urgent email to the finance department requesting a wire transfer.
- Challenge: Spear phishing emails often bypass traditional filters due to their personalized and context-aware nature.
- Control Validation: Testing tailored attack scenarios with Cymulate’s BAS platform uncovers blind spots in detection logic and employee awareness.
3. Business Email Compromise (BEC)
- Definition: An attack in which threat actors spoof or take over a legitimate business email account to manipulate internal communications.
- Example: An attacker impersonates a CEO to instruct finance to send funds to a fraudulent account.
- Challenge: These attacks typically do not contain malicious payloads, making them difficult for secure email gateways to detect.
- Control Validation: Cymulate validates whether detection and workflow controls are capable of identifying and mitigating anomalous BEC activity.
4. Spoofing
- Definition: Email spoofing involves forging email headers to make messages appear as if they come from a trusted source.
- Example: An email appears to originate from a known partner domain but is actually sent from an attacker-controlled server.
- Challenge: Without proper SPF, DKIM and DMARC configurations, spoofed emails can reach the inbox.
- Control Validation: Cymulate’s configuration assessments help ensure email authentication protocols are enforced correctly.
5. Malicious Attachments
- Definition: Emails containing attachments that, when opened, execute malicious code on the recipient’s device.
- Example: A disguised resume document containing embedded macros that deploy a remote access Trojan (RAT).
- Challenge: File obfuscation and evasion techniques often bypass antivirus and sandboxing.
- Control Validation: Cymulate evaluates how effectively email gateways and endpoint solutions identify and block malicious payloads.
6. Malicious URLs
- Definition: Embedded links in emails that direct users to credential harvesting sites or initiate malware downloads.
- Example: A seemingly benign link that redirects to a phishing page mimicking a Microsoft 365 login portal.
- Challenge: Shortened URLs and redirect chains can bypass URL filters.
- Control Validation: Cymulate’s attack simulations test link-based threat detection across security controls and user behavior.
7. Credential Harvesting
- Definition: Attacks designed to trick users into providing login credentials via fake login pages.
- Example: An attacker sends an email pretending to be IT support asking the user to reset their password on a spoofed site.
- Challenge: Sites are often hosted on compromised domains and designed to look legitimate.
- Control Validation: Cymulate’s simulations help measure the ability of Secure Email Gateway (SEG) solutions and users to identify credential theft attempts.
8. Clone Phishing
- Definition: Clone phishing is a type of phishing where attackers duplicate a legitimate email previously sent and replace legitimate links or attachments with malicious versions.
- Example: An attacker replicates a real company newsletter but modifies the URLs to point to malicious destinations.
- Challenge: High familiarity makes it harder for users to detect subtle changes.
- Control Validation: Clone phishing tests with Cymulate expose gaps in both technical and human defenses.
9. Thread Hijacking
- Definition: Attackers gain access to email threads and insert malicious content within ongoing conversations.
- Example: A compromised partner account sends malware within an existing project discussion thread.
- Challenge: The context and legitimacy of the thread make malicious activity less suspicious.
- Control Validation: Cymulate assesses whether email security and detection systems can identify anomalous behavior in legitimate threads.
10. HTML Smuggling
- Definition: A technique that delivers malicious payloads via HTML and JavaScript within email attachments or links.
- Example: A .html file attachment that, when opened, reconstructs and downloads a malicious file in the browser.
- Challenge: It bypasses perimeter defenses by avoiding traditional download mechanisms.
- Control Validation: Cymulate can simulate this attack vector to test browser isolation, SEG filtering, and endpoint controls.
11. Zero-Day Exploits in Email Clients
- Definition: Exploits targeting unknown or unpatched vulnerabilities in email clients.
- Example: An email exploiting a zero-day in a popular email reader that triggers remote code execution.
- Challenge: Zero-day vulnerabilities lack immediate signature-based detection.
- Control Validation: Cymulate’s continuous testing helps identify residual risk exposure and validates layered defenses.
How Cymulate Helps Validate Your Security Controls Against Email-Based Threats
Cymulate’s platform offers a comprehensive suite of tools to test, validate, and optimize defenses against email threats. The Email Gateway Validation module evaluates the effectiveness of Secure Email Gateways (SEGs) against known and emerging threats by simulating real-world attacks. The platform supports:
- Phishing and spear phishing simulations to test user behavior and endpoint detection.
- Malware and payload delivery assessments to evaluate content and attachment filtering.
- BEC and spoofing simulations to validate business process controls and identity protection.
- Configuration drift analysis for SPF, DKIM, and DMARC enforcement.
By continuously testing controls under real-world conditions, Cymulate enables SecOps and IR teams to uncover misconfigurations, identify exposure points and harden their defenses against advanced email-based attacks.