10 Types of Network Attacks: Common Threats and How to Prevent Them
Network attacks have evolved far beyond simple brute-force intrusions or spam. Threat actors now employ complex, multi-vector tactics that can infiltrate even the most fortified infrastructures.
As attack surfaces grow with cloud adoption, remote work and third-party integrations, defending the network edge has become both more critical and more complex.
According to Akamai, 16% of organizations encountered command and control (C2) traffic in their network and 42% of overall web traffic originates from botnets. These are sobering reminders that threats come from just about anywhere.
Understanding the most common types of network attacks—and how to detect and prevent them—is essential for security leaders, architects, and defenders across SOCs and red teams.
Visibility alone is no longer sufficient; organizations must actively validate their defenses to stay resilient against emerging threats. Let’s look at 10 types of network attacks and what your organization can do to fight back against them.
Understanding Today’s Most Common Network Attacks
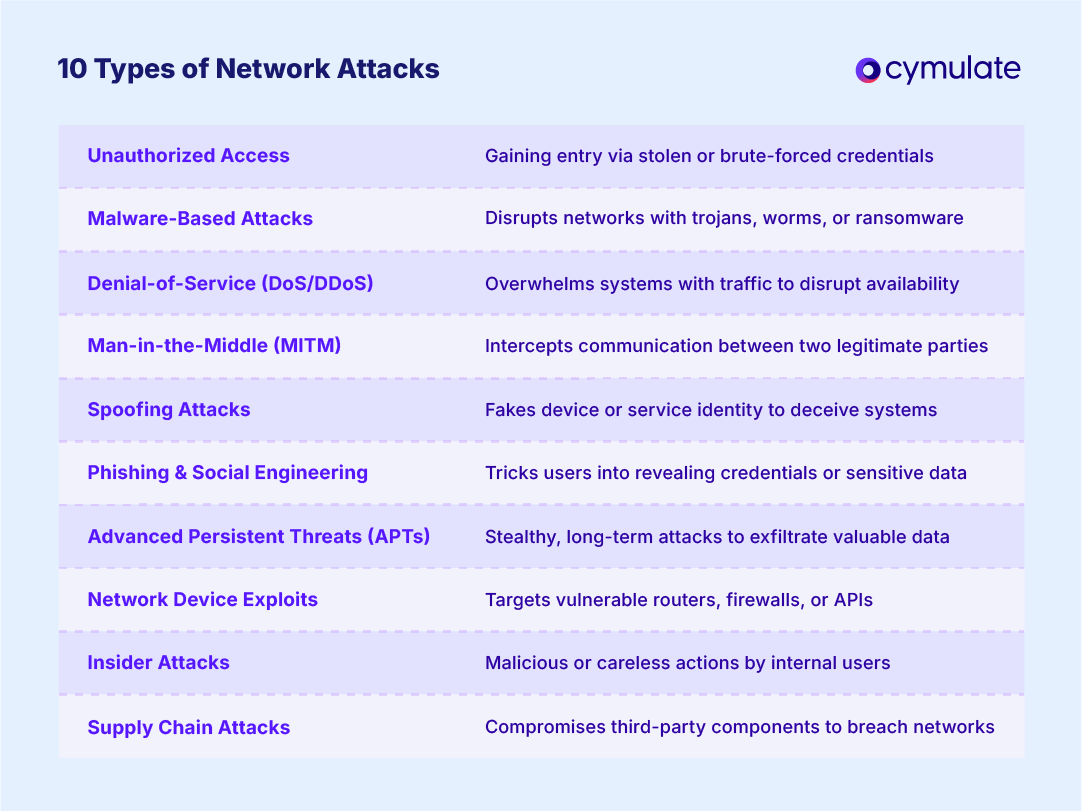
1. Unauthorized Access Attacks
These attacks aim to gain access to network systems without permission, either through stolen credentials, brute force, or malicious insiders.
Variants:
- Brute-force attacks: Automated scripts try multiple password combinations to gain access.
- Credential stuffing: Stolen credentials from one breach are reused across multiple systems.
- Insider threats: Legitimate users misuse access for malicious purposes or unintentionally introduce risk.
Prevention Tips:
- Enforce MFA and strong password policies
- Monitor for anomalous login behavior
- Use network segmentation and least privilege access
2. Malware-Based Attacks
Malware disrupts or damages networks through payloads like trojans, ransomware and worms.
Variants:
- Worms: Self-replicating code that spreads across networks without user action
- Trojans: Disguised as legitimate software to create backdoors
- Ransomware: Encrypts network data and spreads laterally to maximize damage
Prevention Tips:
- Deploy advanced endpoint detection and response (EDR)
- Regularly patch systems and monitor for anomalous activity
- Validate lateral movement controls
3. Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS)
This attack floods network resources with traffic to disrupt availability and functionality.
Targets:
- Web servers
- DNS infrastructure
- Firewalls
- API gateways
Prevention Tips:
- Use DDoS protection services and traffic filtering
- Harden endpoints and validate resilience under load
- Implement network segmentation to isolate critical services
4. Man-in-the-Middle (MITM) Attacks
Here, an attacker secretly intercepts and potentially alters communications between two parties.
Techniques:
- Packet sniffing: Captures network traffic to extract credentials or data
- Session hijacking: Takes control of a valid session after authentication
Vulnerabilities:
- Weak encryption protocols
- Misconfigured VPNs
- Public Wi-Fi networks
Prevention Tips:
- Enforce TLS encryption and secure key exchanges
- Use endpoint and network detection tools
- Validate encryption enforcement across all communication paths
5. Spoofing Attacks
The attacker impersonates a legitimate device or service to deceive systems or users.
Types:
- IP spoofing: Sends packets with a forged IP address to bypass filters
- DNS spoofing: Redirects traffic to malicious domains
- DHCP spoofing: Distributes rogue network configurations to devices
Prevention Tips:
- Validate DHCP servers and enforce IP filtering
- Implement DNSSEC and monitor DNS traffic
- Use breach and attack simulation (BAS) tools to test spoofing defenses
6. Phishing and Social Engineering with Network Implications
Attackers deceive individuals into revealing credentials that lead to deeper network intrusions.
Network Impact:
Once access is gained, attackers can move laterally, establish persistence and extract data.
Prevention Tips:
- Conduct regular phishing simulations
- Use behavioral analytics to detect abnormal access patterns
- Continuously validate access controls with tools like Cymulate’ network security validation
7. Advanced Persistent Threats (APTs)
Stealthy, targeted intrusions designed to stay hidden while gathering intelligence or exfiltrating data.
Tactics:
- Custom malware
- Fileless attacks
- Use of zero-day vulnerabilities
Challenges:
Standard detection tools often miss these threats due to their low-and-slow approach.
Prevention Tips:
- Employ continuous validation with breach and attack simulation
- Monitor for command and control (C2) communications
- Isolate sensitive data environments with strict segmentation
8. Network Device Exploits
Exploits that target vulnerabilities in routers, switches, firewalls and other infrastructure.
Common Issues:
- Outdated firmware
- Misconfigured access rules
- Insecure APIs
Prevention Tips:
- Conduct routine configuration audits
- Use red teaming and penetration testing to validate defenses
- Test resilience with Cymulate network security validation
9. Insider Attacks and Misuse
These are ttacks originating from internal actors. Sometimes these attacks happen intentionally, or they can be accidental when a user has the best of intentions, but they do something unsafe or careless.
Risks:
- Privileged users bypassing controls
- Lack of monitoring on internal traffic
- Inadequate segmentation allowing lateral movement
Prevention Tips:
- Enforce least privilege access
- Monitor user behavior with UEBA (User and Entity Behavior Analytics)
- Regularly test segmentation efficacy and access control enforcement
10. Supply Chain Attacks Affecting Network Layers
Exploitation of vulnerabilities in third-party software, hardware or service providers. Many cyberattacks and security breaches have happened through unsecured third parties.
Entry Points:
- Compromised updates
- Embedded malware in third-party devices
- Insecure vendor integrations
Prevention Tips:
- Maintain a vetted list of suppliers
- Isolate and monitor third-party access
- Validate third-party security posture regularly
Proactive Validation Is Essential for Preventing Network Attacks
As network threats grow in complexity and scale, so must an organization’s ability to preemptively detect and neutralize risk. Relying solely on perimeter defenses or periodic assessments is no longer viable. Continuous validation through breach and attack simulation, penetration testing, and exposure management is vital.
Cymulate network security validation provides organizations with the ability to safely emulate real-world attacks, identify gaps and remediate vulnerabilities before they can be exploited.
Cymulate delivers automated security validation to simulate malicious network traffic for both north–south traffic into and out of the network and east–west internal traffic across the network. Network security validation assessments enable you to test the effectiveness of security controls and policies associated with your:
- Web gateways and firewalls
- Intrusion prevention / detection systems
- Network segmentation
- Lateral movement
- Data loss prevention
Solution features include:
Simulate network traffic (PCAP files): Simulate both malicious and non-malicious network traffic using packet capture (PCAP) files to replay network traffic scenarios, providing valuable insights into potential weaknesses in your network infrastructure.
Network segmentation and penetration testing: Test your internal network configuration and segmentation policies against lateral movement using various techniques and protocols to elevate privileges, evade detection, spread within a network and gain control over additional systems.
Validate network resilience to known exploits: Simulate specific network traffic exploits and vulnerabilities like Print Nightmare, SIGRed, Log4j and other CVEs to gauge your network's resilience against known security weaknesses.
View results dashboard and heatmap: View detailed reports, findings and dashboards that highlight strengths and weaknesses in the prevention and detection of different tactics and techniques across the MITRE ATT&CK® framework.
By leveraging proactive, automated validation, security teams can turn their networks from reactive to resilient, closing doors to attackers before they knock.