A New Advanced Scenario for Testing Defenses Against Lateral Movement
In this blog series, we examine security validation techniques for the preemptive protection of networks, applications, and data. The scenario templates for various threats are based on the most popular ones used among our customers.
In the previous series’ posts, we delved into the dark corners of credential dumping executions leading to initial foothold abuse, data exfiltration executions culminating in data theft, and command and control tactics potentially leading to overtaking a system.
The fourth advanced scenario template in this series is dedicated to a critical and often overlooked aspect of cyber attacks: Lateral Movement.
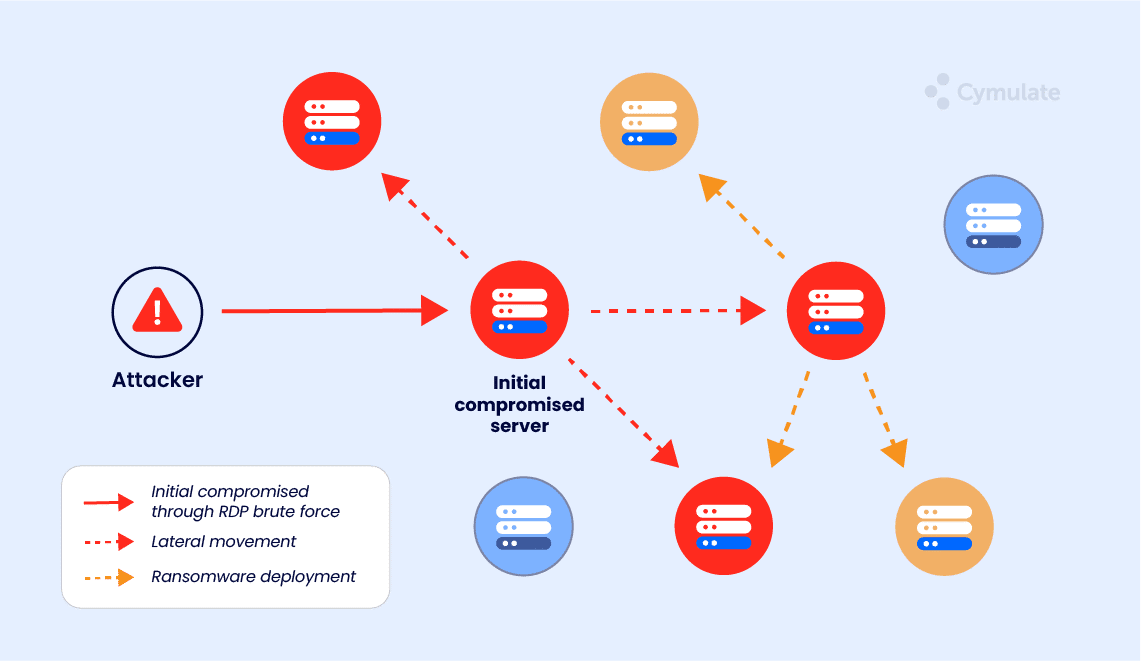
Lateral Movement's aim is to enable attackers to traverse a network, exploiting system vulnerabilities and compromised credentials to gain access to valuable data or assets. Essentially, successful lateral movement allows attackers to advance their objectives in a network, ranging from data theft to establishing persistence for future attacks.
Most Popular Lateral Movement Techniques
Here are some of the most frequently used lateral movement executions:
1. Invoke-TheHash: WmiExec Pass the Hash Attack – Authentication Test
This technique involves using stolen hashed credentials to authenticate and execute commands on a remote system using Windows Management Instrumentation (WMI).
- Recommended Prevention: Monitor for unusual WMI requests and restrict access to WMI where possible.
2. Rubeus: Kerberoasting
Rubeus, a C# toolset, is often used for Kerberoasting, a technique that exploits the Kerberos protocol’s service ticket encryption to retrieve plaintext credentials.
- Recommended Prevention: Regularly review and update service account passwords; monitor for unusual Kerberos requests.
3. Invoke-TheHash: WmiExec Pass the Hash Attack – Bruteforce (Credential Pairs)
This technique involves automated attempts of different credential pairs (username and password combinations) to gain unauthorized access to systems via WMI.
- Recommended Prevention: Implement account lockout policies and two-factor authentication.
4. Psexec: Remote Credential Dump using Mimikatz
Mimikatz, a tool often used for credential dumping, can be combined with PsExec to execute commands on remote systems and gather credentials for lateral movement.
- Recommended Prevention: Implement the Least Privilege Principle and monitor for unusual network connections.
5. SharpRDP
SharpRDP is a tool that allows attackers to execute commands on remote systems via a headless (non-GUI) Remote Desktop Protocol (RDP) session.
- Recommended Prevention: Disable RDP where not needed and enforce strong RDP credentials.
6. Mimikatz Pass the Hash
This technique involves using Mimikatz to extract credential hashes from memory and reusing them to authenticate to remote systems.
- Recommended Prevention: Enforce strong password policies and limit local admin rights.
7. Execute Remote Process using Outlook Remote COM Object
This technique exploits Outlook’s Component Object Model (COM) objects to execute a process on a remote system.
- Recommended Prevention: Restrict and monitor the use of COM objects.
8. Lateral Movement using DCOM ServiceStart
Attackers can use the Distributed Component Object Model (DCOM) to execute arbitrary functions, such as ServiceStart, on remote systems, aiding in lateral movement.
- Recommended Prevention: Limit DCOM permissions and monitor for unusual DCOM activity.
9. Using Psexec with Multiple Targets
PsExec is a tool that allows attackers to execute processes on other systems and can be used to execute commands or scripts across multiple targets simultaneously.
- Recommended Prevention: Implement strict access controls and monitor for unusual PsExec usage.
10. RDP to Server
RDP is a protocol that allows users to connect to remote systems. Attackers often use RDP to move laterally through a network, especially when RDP is enabled on a server.
- Recommended Prevention: Limit RDP access and monitor for unusual RDP activity.
Preventing Lateral Movement Attacks
The best defense against lateral movement attacks involves a multi-pronged approach, leveraging both proactive security measures and robust detection capabilities.
Most recommended prevention techniques against lateral movement include strict access controls, robust password policies, limiting local admin rights, and monitoring for suspicious activity. Intrusion detection system (IDS), intrusion prevention system (IPS), and application control and execution prevention tools can also be used to block unauthorized apps or code from executing.
However, these tools need to be correctly configured to match the environment in which they're active. Manually configuring these systems can be resource-intensive and potentially error-prone, often leading to postponements due to lack of resources.
Preemptively running the Cymulate Lateral Movement advanced scenario template with the ten executions listed above, either chained or atomically, is an easy-to-implement and effective proactive measure. Additionally, simulating these techniques can be used to test lateral movement-specific incident response plans and identify areas for improvement.
Stay tuned for our next post in this series, where we'll delve into another critical aspect of network security.



