A New Way to Automate and Simplify Threat Detection
Yoni Harris
Avigayil Stein
Detection engineering isn’t just building new rules; it's optimizing the ones you have.
Threat detection is never set-it-and-forget-it. With default settings, the average SIEM covers less than 20% of MITRE ATT&CK techniques – and 20% of detections will never fire because of missing data and other blind spots.
To bridge this gap in threat detection, the Cymulate Exposure Validation Platform introduces AI-powered security information and event management (SIEM) rule validation, a major advancement in how security teams validate, tune and strengthen their existing detection rules. This new capability highlights that, alongside building new rules, a critical part of detection engineering is making sure existing ones are effective against today’s threats.
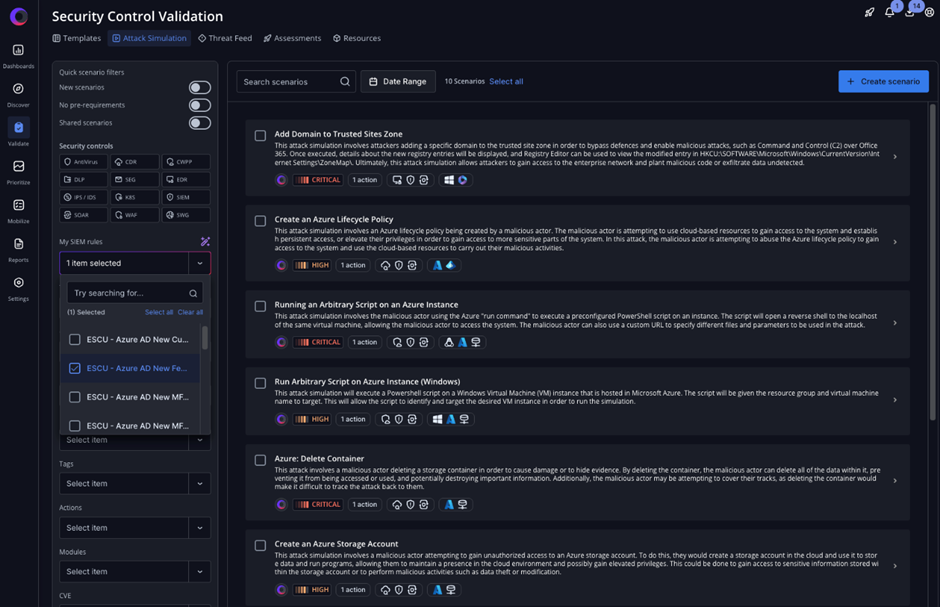
Leveraging native SIEM integrations and advanced AI analysis, Cymulate now automatically maps your existing SIEM rules to relevant attack scenarios based on multiple attributes, including tactics, techniques and procedures (TTPs), rule name, description and query. Previously, mapping detection rules to relevant threats required hours of manual effort; reviewing rule logic, identifying threat coverage and testing scenarios one by one. Cymulate eliminates that friction by automating the correlation and validation process, enabling SecOps teams to identify coverage gaps and tune rules in minutes.
This new capability reduces the risk of cyber threats slipping through detection blind spots and escalating into material breaches. By automating the correlation between detection rules and Cymulate attack scenarios, organizations can now ensure their SIEM rules are continuously validated against real-world threats and optimized with precision.
A Smarter, Faster Path to Detection Confidence
AI-powered SIEM rule validation delivers a fully automated workflow to accelerate detection engineering:
- Integrate – Cymulate connects to your SIEM and automatically retrieves existing detection rules.
- Correlate – An advanced AI correlation engine maps each rule to relevant attack scenarios from the platform’s extensive library of over 100,000 simulations.
- Validate – Targeted simulations are run to confirm whether rules trigger as expected, revealing detection gaps.
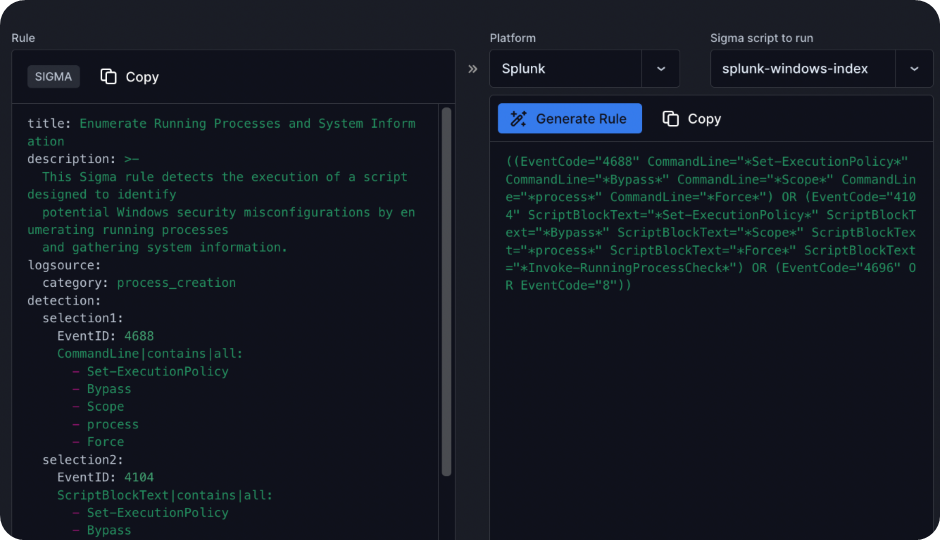
- Tune – Cymulate recommends vendor-specific detection rules to close those gaps, formatted for easy implementation.
- Re-test – Updates can be instantly revalidated, enabling continuous tuning and confidence in rule performance.
By enabling continuous testing and refinement of detection logic against real-world threats, Cymulate helps SecOps teams automate detection tuning, reduce visibility gaps and maximize the value of their SIEM investments.
Detection Logic Remains Private and Secure
The Cymulate commitment to proactive, secure operations extends beyond simulation and validation, it’s embedded into the very infrastructure of the platform. All customer data is handled exclusively within the platform’s dedicated AWS cloud environment, managed end-to-end by Cymulate to ensure maximum control and oversight.
To reduce risk, Cymulate does not transmit customer data to third-party providers. All generative AI capabilities are developed and operated internally. This means sensitive detection logic, validation outputs and telemetry stay entirely within Cymulate’s ecosystem, never transmitted to third-party LLMs or APIs.
Customer data is also strictly isolated. No data is reused across tenants or environments, and nothing is ever repurposed for training. Each organization’s insights remain theirs alone, meeting compliance obligations and reinforcing trust by design.
More Ways Cymulate Supports Detection Engineering
This new capability builds on the growing Cymulate suite of features designed to empower SecOps teams with automated security validation. Here are a few of the other Cymulate features designed to support detection engineering at every stage of the process:
Build and validate new detections for emergent threats
When new threats make headlines, speed matters. With the Cymulate AI Template Creator, SecOps teams can instantly generate assessments by uploading a threat advisory or news article. The platform uses AI to create a custom simulation based on the described threat behavior and allows teams to test current controls within minutes.
This automated process helps teams get ahead of the newest threat and saves them hours of manual work: reviewing the advisory, identifying relevant IOCs and TTPs, performing threat modeling and impact analysis to understand how the threat maps to their environment and which systems may be at risk. And that’s all before beginning to validate detection coverage or coordinate a response.
To accelerate this process further, if detection gaps are found, Cymulate provides tailored detection rules for your SIEM, EDR or XDR platform, making it easy to implement and test improvements. Teams can then re-run the assessment to confirm that alerts trigger correctly and enable a rapid, accurate response to evolving threats.
Baseline and optimize MITRE ATT&CK coverage
Understanding what you can detect is as important as detecting it. The Cymulate MITRE ATT&CK heatmap gives teams a clear visual baseline of their detection coverage, mapped against real-world threat behavior. The heatmap highlights which tactics and techniques are fully covered, partially detected, or completely missing and helps teams prioritize where to create new rules or tune existing ones. With this actionable visibility, SecOps can focus their detection engineering efforts where it counts most.

Test SecOps processes, policies and playbooks
Detection engineering isn’t just about rules, it’s also about how SecOps teams respond during an attack. Cymulate enables organizations to simulate real-world attack scenarios in a controlled environment, testing how well processes, tooling, and playbooks hold up under pressure.
The Cymulate attack scenario workbench makes it easy for SecOps teams to build custom assessments from a library of more than 100,000 attack actions mapped to techniques, threat actors, malware families and more. These tailored assessments help teams evaluate how well their SecOps processes perform in realistic conditions. Cymulate also validates whether integrated controls are preventing, detecting and logging attacks as expected. Additionally, its SOAR integrations go one step further by verifying that incidents are properly registered and the response process is functioning as intended.
These live exercises help surface operational blind spots (such as missing alerts, unclear handoffs, or ineffective escalation paths) before a real incident occurs. By validating not just the detection logic but the full response workflow, Cymulate helps teams improve coordination, reduce mean time to detect and respond, and boost overall operational readiness.
Proven Results That Elevate Your SecOps
By integrating Cymulate into the detection engineering workflow, security teams can dramatically improve both efficiency and effectiveness, and. see many measurable benefits, including:
- Optimized MITRE ATT&CK coverage – Continuous testing ensures better alignment with real-world adversary behaviors, improving visibility across tactics and techniques.
- Faster detection rule development – With automated threat simulation and tailored rule recommendations, teams significantly reduce the time required to build, test and deploy new detections.
- More frequent and reliable rule validation – Cymulate makes it easy to routinely test existing detections, helping teams catch logic gaps or drift before attackers do.
- Fewer false positives – By validating rules against realistic simulations, teams can fine-tune detection logic to reduce noise and focus on real threats.
Ready to See it in Action?
AI-powered SIEM rule validation brings a new level of speed, precision and automation to detection engineering. Whether you're building new detections or optimizing existing ones, Cymulate gives you the tools to stay ahead of threats and maximize your security investments.
Request a demo today to see how Cymulate can transform your detection engineering program.

