Handala Hack: From Regional Disruption to Digital Destruction — Why Security Validation Matters Now

After years of battling ransomware and financially motivated threats, security teams must now increase their focus to defend against digital destruction. Iranian-backed Handala Hack highlighted the growing threat with its claimed attacks against a U.S.-based medical equipment maker, with reports of widespread deletion of data on devices managed by Microsoft Intune.
While the hot war may be contained to the Middle East, this cyberattack raises the alarm about the likelihood of future attacks targeting U.S. and Western organizations, where the objectives are more likely to be disruption, denial-of-service, and maximum damage.
It’s time for security teams to take a threat-informed approach security and harden their defenses against wiper campaigns, boot record corruption and system recovery sabotage.
Who is Handala Hack?
Handala Hack is widely assessed to be aligned with Iranian regime interests or operating in support of Iranian strategic objectives. Research reporting connects the group’s targeting, narratives and operational patterns to Iran-linked activity, with a long-running focus on Israeli organizations and entities in the broader Middle East.
Unlike for-profit threat actors, Handala aims to disrupt operations and missions while publicly announcing its claimed victims to amplify psychological and reputational impact.
What attack tactics and techniques are used?
According to industry threat research, Handala campaigns combine destructive malware, scripted execution and coordinated information operations to maximize operational and psychological impact. The actor typically employs system discovery, lateral movement and defense-evasion techniques before deploying wiper malware intended to disrupt and render targeted systems.
A typical Handala playbook includes:
- Script-driven execution, including PowerShell and Windows command shell (BAT) activity to stage, automate and execute actions
- Defense impairment steps intended to reduce visibility or response capability before destructive execution
- Discovery and lateral movement behaviors allowing for broader reach and faster disruption inside a network
- High-tempo public claims and information operations (e.g., leak announcements) to magnify impact
Why does this threat matter now — and who is at risk?
U.S. organizations should maintain heightened awareness and readiness as recent activity indicates that Handala is now targeting entities within the United States. Their malicious threat campaigns stand out for two reasons: 1. disruptive/destructive intent and 2. comparatively consistent public claims that often align with real operational impact.
U.S. defenders, specifically in the below industries, should remain vigilant and be prepared with the assumption the objective is an outage and major operational disruption, not negotiation.
- Healthcare and medical technology
- Financial services and payment ecosystems
- Manufacturing and industrial operations
- Critical infrastructure and public sector
- Large enterprises with complex IT/OT footprints
How Cymulate helps you prepare and prove readiness
Cymulate enables security teams to move from threat awareness to measurable readiness by validating prevention and detection against adversary behaviors in a controlled, safe way.
Cymulate AI for continuous threat alignment. With Cymulate AI cutting-edge capabilities, security teams can ingest new threat intelligence and automatically generate a threat-centric view of current coverage, highlighting where prevention and detection is strong and where it needs tuning. This accelerates alignment as Handala (and the broader threat landscape) evolves.
See how Cymulate AI converts threat intel into custom threat validation assessments.
Built-in Handala-aligned templates. The Cymulate platform has ready-to-run assessments aligned to the techniques commonly reported in Handala campaigns (e.g., PowerShell abuse, lateral movement techniques and destructive impact behaviors). This allows teams to test controls immediately without building custom simulations from scratch – start assessing and validating now.
IOC validation and mitigation testing. Beyond simulating techniques, Cymulate tests known indicators associated with Handala that may be reused. Security teams can rapidly validate that their controls block or alert on these indicators across security controls (endpoint, network, SIEM) and confirm the end-to-end workflow from detection to response.
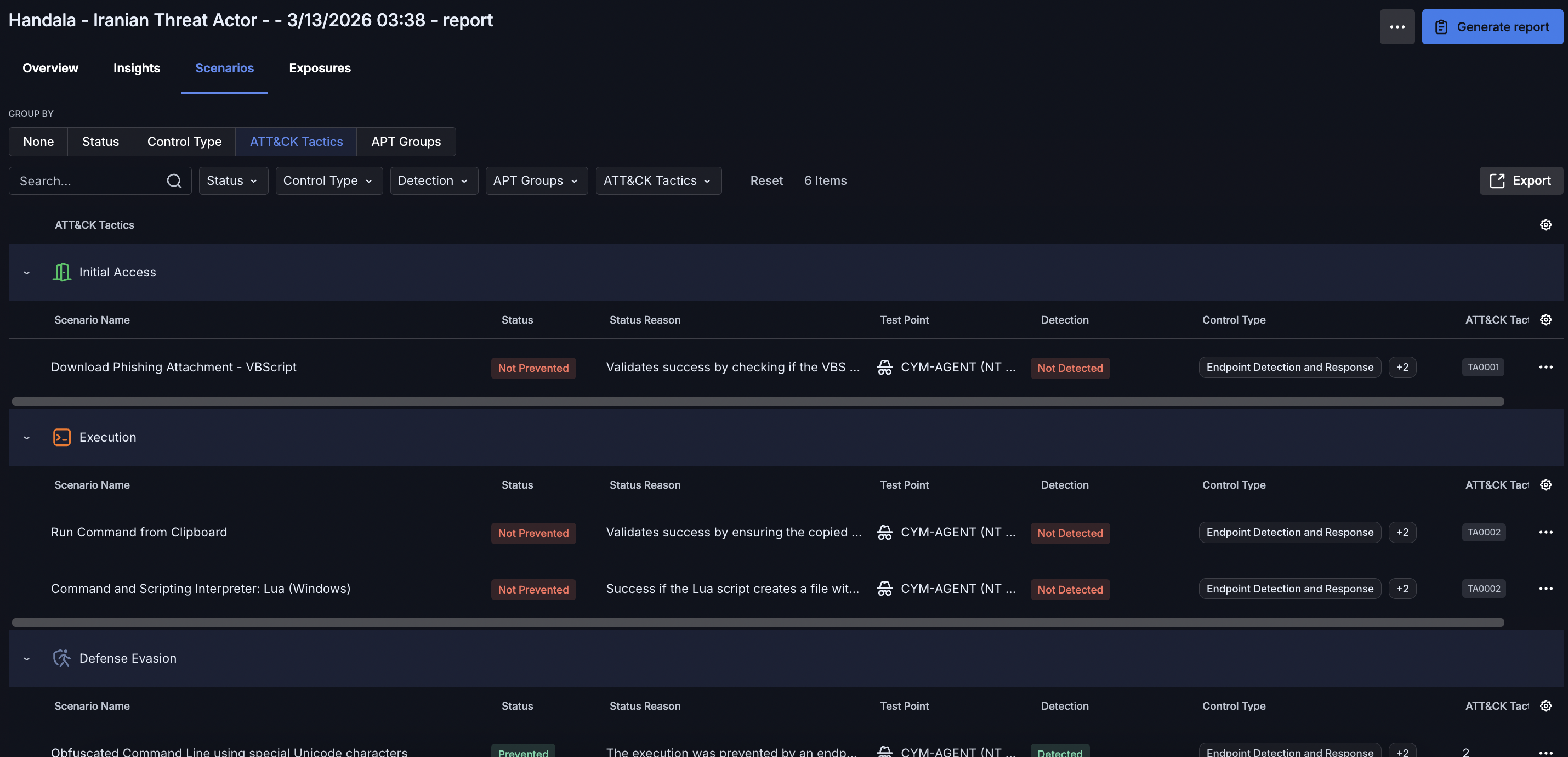
Cymulate threat validation proves prevention and detection for specific MITRE ATT&CK tactics techniques.
Actionable remediation outputs. For each validated prevention and detection gap, Cymulate helps teams quickly mitigate these findings. This includes auto-mitigation pushes of IOCs to controls and automatically generated vendor-specific detection logic for EDRs and SIEMs. Security remediation is concrete, actionable and trackable. Cymulate enables organizations to quickly validate their posture and improve their threat resilience, which reduces operational risk.
Executive-ready communication. To quickly and easily communicate threat readiness, Cymulate uses AI to build custom dashboards and reports to quickly summarize testing results and findings for specific threats.
See how Cymulate uses AI to create custom dashboards.
Closing thought
When destructive actors, such as Handala, broaden their targeting, reactive posture is not enough. Readiness must be continuously tested and validated against the techniques that matter. The most important question for defenders is simple: if Handala tested your environment tomorrow, would you already know the outcome?
MITRE ATT&CK mapping for Handala tradecraft
The table below maps commonly reported Handala behaviors and activity to MITRE ATT&CK tactics and techniques, and what defenders must be validating in their environment.
| Technique ID | Technique | How Handala Uses It | What to Validate |
|---|---|---|---|
| Initial Access | |||
| T1566 | Phishing | Spear-phishing to deliver payloads or enable credential access | Email security efficacy; attachment/link detonation; user reporting workflow |
| T1190 | Exploit Public-Facing Application | Exploitation of exposed services for foothold | WAF efficacy; patch exposure; exploitation detection |
| Execution | |||
| T1059.001 | PowerShell | Encoded/obfuscated PowerShell used for staging and execution | EDR detections for encoded commands; suspicious flags; script block logging |
| T1059.003 | Windows Command Shell | BAT/cmd execution to automate steps | Command-line auditing; parent/child process anomalies |
| Persistence | |||
| T1053 | Scheduled Task/Job | Scheduled tasks to re-run scripts or stages | Alert on new tasks; anomalous task creators; task execution lineage |
| T1547 | Boot or Logon Autostart Execution | Autostart persistence mechanisms | Run keys/startup folder monitoring; registry auditing |
| Privilege Escalation | |||
| T1068 | Exploitation for Privilege Escalation | Elevation after foothold to expand control | Privilege escalation detections; exploit telemetry |
| Defense Evasion | |||
| T1027 | Obfuscated/Compressed Information | Obfuscated scripts and encoded payloads | Command-line detections; AMSI/script deobfuscation coverage |
| T1562 | Impair Defenses | Security control tampering prior to impact | Service stop detections; tamper protection validation |
| T1070 | Indicator Removal on Host | Clearing logs/artifacts to reduce visibility | Detect log clearing; retention/forwarding resiliency |
| Discovery | |||
| T1082 | System Information Discovery | Host reconnaissance prior to impact | Detect unusual enumeration; correlate with other stages |
| T1018 | Remote System Discovery | Network discovery to identify reachable systems | SMB/RPC discovery monitoring; anomaly detection |
| Lateral Movement | |||
| T1021 | Remote Services | Use of remote services for movement | Remote execution monitoring; admin share controls |
| T1570 | Lateral Tool Transfer | Transfer payloads/tools across hosts | File transfer telemetry; share write monitoring |
| Impact | |||
| T1485 | Data Destruction | Wipers overwrite files/disks | Detect mass destructive patterns; rapid isolation playbooks |
| T1490 | Inhibit System Recovery | Shadow copy deletion / recovery inhibition | Block/alert on vssadmin/bcdedit misuse; backup hardening |
| T1529 | System Shutdown/ Reboot | Forced restarts as part of impact chain | Correlate coordinated shutdowns; containment procedures |
IOC and detection validation
Handala infrastructure can rotate quickly, so behavioral indicators are often more durable than static domains or IPs. Still, organizations should validate both: (1) behavioral detections that map to the techniques above, and (2) blocking and alerting for known or newly ingested IOCs.
References
- Check Point Research (2026): Handala Hack: Unveiling Group’s Modus Operandi
- SOCRadar (2026): Dark Web Profile: Handala Hack
- Palo Alto Networks Unit 42 (2026): Handala Hack Wiper Attacks
- Stryker (March 2026): A Message to Our Customers


