The Techie Ways to Minimize Phishing Success Rate
- Running phishing awareness training session (Scheduled for October 17)
- Stopping the phish that slipped through (Scheduled for October 31)
Pre-filtering: The First Line of Defense
External Sender Tags: Red Flags in Your Inbox
Limitation and Future Trends of Scanning Attachments
Reporting: Make It Easy and Quick
Alert Channels: Your 24/7 Watchtower
Technology and Integration examples
Teaming together to Stop the PhishThe Rising Threat of Phishing
Phishing scams are becoming increasingly common and sophisticated, posing a serious threat to organizations of all sizes. With phishing attacks often specifically targeting employees through email, it's crucial that companies implement solutions to minimize the chances of a successful phishing attempt. While training employees to identify and avoid phishing is essential, technology plays a key role as well. Organizations need multilayered technological defenses at the inbox level to equip staff against even the sneakiest phishing tactics. This post will explore some of the key technical methods organizations can leverage to enhance phishing awareness, detection, and reporting right at the inbox level, before employees even open suspicious emails. Techniques like pre-filtering dubious emails, flagging external senders, scanning attachments, and enabling simple reporting procedures can all work together to reduce the success rate of phishing campaigns. A technological helping hand is vital given how convincingly deceptive many phishing emails have become.The Tech Arsenal: Techniques to Counter Phishing
This section outlines key technologies designed to bolster your inbox against phishing. We'll cover pre-filtering methods, visual cues for external emails, attachment scanning, reporting protocols, and dedicated alert channels. Each plays a crucial role in a comprehensive anti-phishing strategy.Pre-filtering: The First Line of Defense
Pre-filtering is your first line of defense against phishing attacks. It acts as a gatekeeper, with a goal to ensure that only legitimate emails make it to your inbox. Solutions like Microsoft's Exchange Online Protection (EOP) can provide this type of pre-filtering by identifying and removing outright malicious phishing content using a variety of advanced heuristics and machine learning algorithms.Technologies and Algorithms
- Bayesian Filtering: This statistical method calculates the probability of an email being spam based on its content and the user's past behavior.
- Machine Learning Algorithms: Solutions like TensorFlow have been adapted to recognize phishing attempts based on historical data.
- Heuristic Analysis: This involves rule-based methods that scan the email's content, structure, and other attributes to identify phishing traits.
- DNS-based Blacklists: These are real-time databases that block emails from known spam domains.
External Sender Tags: Red Flags in Your Inbox
Phishing emails most often come from outside an organization, so when an email originates from outside your organization, it's crucial to spot it. External sender tags serve this purpose by providing a visual cue.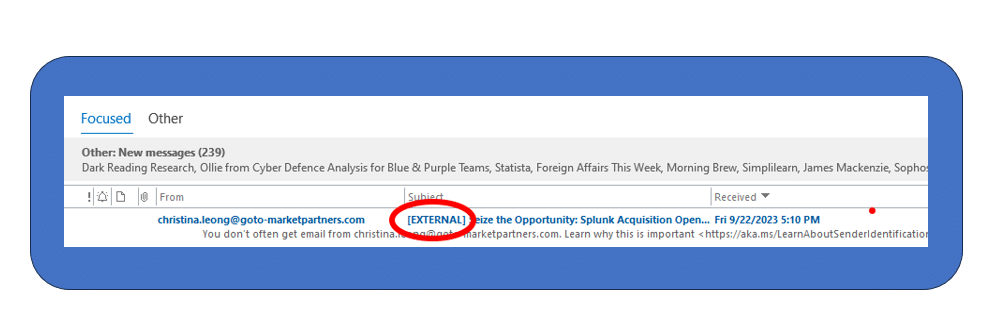
Limitation and Future Trends of Scanning Attachments
- False Positives: Sometimes, legitimate files are flagged.
- Zero-Day Exploits: New malware variants may not be immediately recognized.
- Resource Intensive: Scanning can slow down email delivery.
Reporting: Make It Easy and Quick
Despite it all, some phishing emails will inevitably reach inboxes. In these cases, it is essential to enable employees to easily and quickly report suspected phishing attempts to security teams. Solutions should provide visible "report phishing" buttons right within the email interface, making it seamless to flag suspicious messages.Step-by-Step Guide
- Identify Suspicion: If an email looks dubious, don't interact with it.
- Click 'Report Phishing': Use the built-in feature in your email client.
- Describe the Issue: Optionally, add details about what seemed suspicious.
- Forward to Security Team: If no built-in feature exists, forward the email to your organization's security email.
- Delete the Email: Remove it from your inbox to prevent accidental interactions.
Alert Channels: Your 24/7 Watchtower
Finally, security teams themselves need technical infrastructure that enables prompt alerts and response coordination when phishing attacks occur. Dedicated email addresses, online portals, and communication channels should exist solely for employees to report phishing attempts.Technology and Integration examples
- Email Aliases: Create a specific email like "[email protected]" solely for phishing reports.
- Incident Management Systems: Integrate the reporting channel with tools like Jira or ServiceNow for real-time tracking.
- Automated Analysis: Use machine learning algorithms to prioritize reports based on severity.
- Alerting Mechanisms: Integrate with Slack or Microsoft Teams to alert security personnel immediately upon a report.
