Validate What Matters: Simulate Real-World Identity and Privilege Attacks in AD and Entra ID
Identity is the new perimeter. The move to the cloud and remote work creates new security boundaries based on users and services operating across cloud and hybrid environments, making continuous validation of identity and privileges essential to prevent unauthorized access and stop attackers from exploiting misconfigurations and excessive permissions.
Cymulate Exposure Validation now expands identity security validation with real-world attack simulations across on-prem Active Directory, Microsoft Entra ID and cloud environments. These assessments emulate the techniques attackers use to exploit privilege escalation, token abuse and hybrid trust weaknesses, enabling teams to validate not just configuration posture but whether identity controls and cloud detection mechanisms actually stop or surface abuse.
This expansion delivers measurable business value by strengthening identity security while improving operational efficiency:
- Reduce risk – Continuously identify excessive privileges, misconfigurations and trust weaknesses before they are exploited
- Improve efficiency and scale – Replace manual, point-in-time audits with automated, repeatable identity attack simulations
- Lower cost and optimize effort – Prioritize remediation based on proven exploitability and detection gaps to focus resources where they matter most
Identity is the primary attack surface
Recent industry surveys show that 99 percent of cloud-related breaches originate from insecure identities. Rather than exploiting complex software vulnerabilities, adversaries focus on stealing credentials, abusing tokens and manipulating authentication flows to gain legitimate access and operate with little resistance.
High-profile incidents at organizations such as Snowflake, Cloudflare and Okta followed this exact pattern. In these cases, attackers did not rely on novel exploits or malware. They leveraged stolen credentials or hijacked session tokens to directly access internal systems and customer environments. Once inside, identity sprawl and excessive privileges enabled rapid lateral movement, persistence and escalation. The damage was not caused by a single flaw but by the cumulative effect of trusted identities operating exactly as designed.
Security research over the past year reinforces this shift toward identity abuse as many of the most impactful discoveries target identity infrastructure, particularly Azure Entra ID and Active Directory integrations. For example, Cymulate Research Labs demonstrated Kerberos relay attacks and remote code execution in Azure Windows Admin Center. Other notable findings include Dirk Jan’s Actor Token Global Admin abuse and Semperis’s SyncJacking. These attacks do not bypass security controls; they exploit trusted authentication mechanisms, keys and roles.
This reality changes the CISO role. It is no longer enough to define policies, deploy identity tools and assume coverage. You must prove your defenses work in practice. You need clear answers to basic questions, such as:
- Are we vulnerable right now?
- Can we detect identity abuse when it happens?
- Did our remediation actually remove the risk?
- Will configuration drift, new users, or new integrations silently reintroduce exposure?
Identity risk evolves constantly and static reviews or audits cannot keep up. This can only be achieved through identity exposure validation.
Cymulate enables this validation through real-world identity attack simulation. The platform safely emulates advanced identity threats directly against your environment and security controls, executing the same techniques that attackers use. It shows whether an exposure is exploitable, whether exploitation attempts are detected through identity logs, native alerts or SIEM workflows and whether remediation reduces risk in a measurable way. Testing is continuous, repeatable and aligned to real attacker behavior rather than compliance checklists.
New identity-focused exposure validation
The new Cymulate identity-focused offensive content includes 72 attack scenarios organized into 5 templates that make the advanced attack simulations easy and safe for security teams to validate identity security – both what an attacker can accomplish and the telemetry and detection provided by a SIEM.
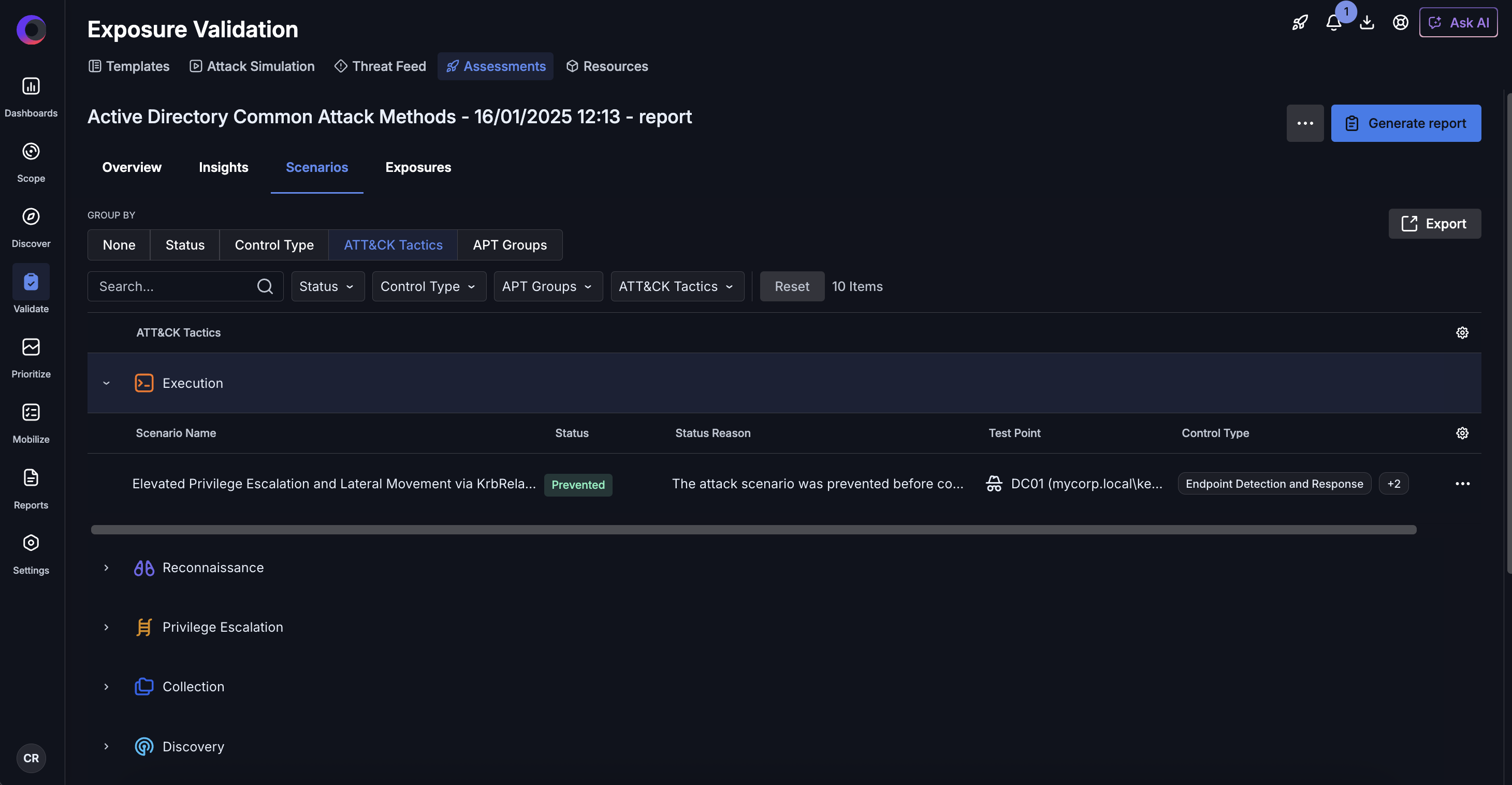
Active Directory common attack methods
- Simulate common AD attacks such as enumeration, credential abuse and privilege escalation
- Safely execute recently discovered AD exploits
- Validate prevention and detection across identity configuration and identity controls
Microsoft Entra ID
- Simulates cloud identity attacks, including high-privilege operations and 3rd party Entra ID Apps abuse
- Tests conditional access, alerting and response effectiveness
- Confirms that Entra ID protections detect and contain identity abuse
Azure and Active Directory hybrid environment
- Validates identity security across integrated AD and Entra ID deployments
- Tests policy enforcement, access controls and monitoring across sync boundaries and identity tokens
- Identifies gaps created by hybrid trust
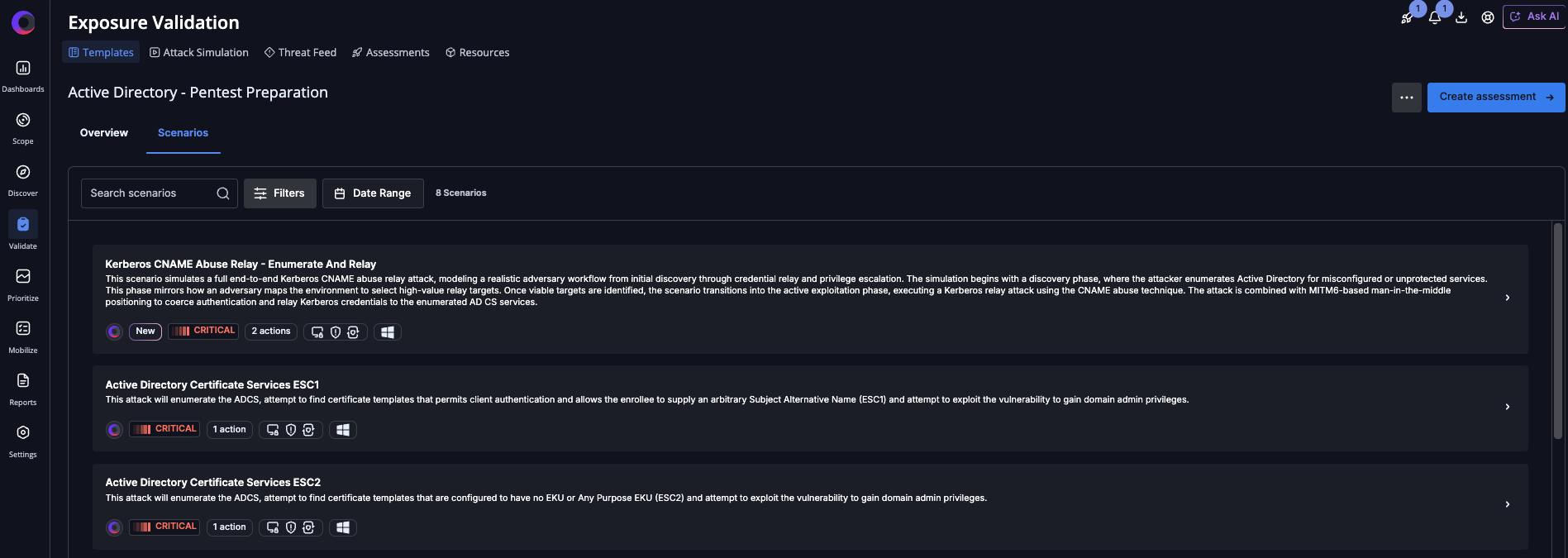
Active Directory pentest preparation
- Executes attack techniques commonly used during AD penetration tests
- Helps teams measure readiness before red team or third-party testing
- Confirms whether security controls block or detect attacks
Active Directory Certificate Services (ADCS)
- Tests abuse methods of ADCS, including mis-issued certificates and privilege escalation
- Validates detection of certificate-based attacks often missed by traditional controls
- Exposes trust weaknesses that enable long-term access
Turn identity risk into proof
Identity attacks are already the dominant breach path, exploiting trust that exists by design. The only way to know whether your identity controls will hold up is to test them the same way attackers do.
For Cymulate customers, now is the time to activate the new identity-focused scenarios and continuously validate your exposure across Active Directory, Microsoft Entra ID and hybrid environments. Run the assessments, review what is detected (and what is not), validate SIEM visibility, confirm that remediation actually reduces risk and schedule recurring assessments to ensure configuration drift or new identities don’t reintroduce exposure.
For security teams evaluating Cymulate, these identity attack scenarios provide a clear, measurable way to assess readiness against today’s most common breach methods. Request a demo to see how our real-world identity attacks are executed safely, how detections surface in logs and SIEMs and how gaps are identified and prioritized for remediation.