New Cymulate WAF Rules: Turn Validation Gaps Into Actionable Defense

Yahav Levin, Research Team Lead
Idan Sherman, Infosec Researcher
Modern web applications are constantly exposed to threats such as SQL injection, cross-site scripting (XSS) and malicious API abuse. Web Application Firewalls (WAFs) are designed to protect against these attacks, but deploying a WAF does not automatically mean it is effective.
One question comes up again and again after running a WAF assessment: How do you know your WAF is actually preventing the attacks that matter, and what do you do when it doesn’t?
This is where many teams hit a wall. Validation is clear. Remediation is not.
That’s why Cymulate is introducing WAF rules: Ready-to-use WAF rules that help teams move from identifying gaps to taking concrete action.
Key highlights
- Cymulate WAF assessments identify security gaps and provide mitigation guidance in the form of vendor-specific WAF rules, helping teams move from validation results to practical improvements.
- WAF rules are derived from the exact attack payloads used during Cymulate WAF scenarios, ensuring detection logic reflects how web and API attacks behave in practice.
- Cymulate mitigation guidance has historically included rules expressed in regular expressions and now incorporates structured WAF rules translated for select platforms such as F5 and ModSecurity.
- WAF rules extend our existing approach to providing actionable detection rules for EDR and SIEM technologies, bringing the same validation-driven guidance to the application layer.
How Cymulate evaluates WAF effectiveness
Cymulate evaluates WAF effectiveness by conducting controlled attack simulations against web-facing applications and APIs. These simulations align with OWASP Top 10 techniques and common application exploits and focus exclusively on externally accessible components, so no internal test points or agents are required.
Security teams provide Cymulate with the URLs or endpoints of the applications to be tested, typically public-facing assets protected by a WAF. Cymulate then launches simulated exploit payloads directly against those endpoints, replicating techniques such as SQL injection (SQLi), cross-site scripting (XSS), remote file inclusion (RFI) and command injection.
The assessment observes how the application and its application-layer defenses respond to these requests. By analyzing response behavior, including HTTP status codes, error handling and whether malicious payloads are allowed to reach or execute within the application, Cymulate determines whether attacks are detected or prevented. This outcome-based approach allows teams to validate WAF effectiveness without requiring direct integration with the WAF itself.
When your WAF doesn’t stop the attack
When a Cymulate WAF assessment identifies a finding labeled Insufficient Web Application Firewall (WAF) Protection, it means a simulated attack was able to pass through application-layer defenses without being detected or blocked.
This typically indicates that relevant WAF logic is missing, incomplete or not properly configured for the specific attack technique being tested. Rather than relying on configuration assumptions, the finding is based on observed behavior, confirming where WAF protections did not function as expected.
Traditionally, Cymulate did not stop at identifying the gap. The platform provided mitigation guidance in the form of regular expressions and text-based recommendations to help teams understand how to detect or block an attack. However, applying that guidance still required teams to translate the logic into their specific WAF product, determine where to implement it and assess how it would behave in their environment.
Cymulate WAF rules build on this foundation by making that guidance more targeted, structured and directly usable.
Introducing Cymulate WAF rules
To help teams remediate WAF findings more effectively, Cymulate now delivers WAF rules directly inside the mitigations section of relevant findings.
Previously, mitigation guidance was provided in the form of generalized detection logic, typically expressed as regular expressions. While this helped teams understand what needed to be detected, it still required manual interpretation and product-specific implementation.
With WAF rules, Cymulate takes the next step, delivering detection logic directly tied to the validated attack, structured for real WAF products and ready to be deployed as a starting point for detection. As a best practice, Cymulate recommends that customers first deploy the WAF rules in detection mode and, once validated, deploy them in prevention mode.
What are Cymulate WAF rules, and why do they matter?
Cymulate WAF rules are detection rules to identify malicious web and API traffic. They are based on real attack payloads used during Cymulate WAF scenarios, ensuring the detection logic reflects how attacks behave in practice.
Each WAF rule provides structured, actionable guidance that makes it clear what needs to be detected and how that logic can be implemented. Every rule includes:
- Universal mitigation logic — a standardized rule format Cymulate uses as a baseline across vendors
- Built-in translation into supported WAF formats
- A rule quality ranking to help teams understand confidence levels and tuning requirements
This capability builds on the mitigation guidance Cymulate has long provided. Previously, Cymulate supplied regular expression–based detection logic to help teams understand how attacks could be identified. WAF rules take this a step further by making that guidance more targeted and directly usable within real WAF products.
WAF rules also extend an approach Cymulate already applies to other security controls. Today, Cymulate delivers actionable detection rules for EDR and SIEM technologies as part of its validation workflows. With the introduction of WAF rules, the same practical approach is now extended to the application layer, providing teams with consistent, structured guidance to improve detection and prevention across endpoints, logs and web applications.
Most importantly, these rules turn WAF validation into action. Instead of only reporting a gap and providing a regex for implementation, Cymulate now helps teams understand exactly which detection logic is required to address the gap and how to implement it safely.
With WAF rules, teams can:
- Improve WAF detection and prevention coverage faster
- Validate changes by re-running WAF assessments
- Strengthen web and API security in a controlled, measurable way
Rule translation for vendor-specific deployment
To reduce friction during implementation, Cymulate provides rule translation into vendor-specific formats.
Today, WAF rule translation is supported for:
- F5
- ModSecurity
Teams can select their WAF product, copy the translated rule and deploy it directly into their environment. Where vendor-specific requirements exist, such as saving F5 rules in XML format, Cymulate provides clear guidance to help teams implement correctly.
Support for additional WAF platforms will be added over time.

F5 Rule for “Encoded JavaScript Event Handler XSS Attack via Invalid Input Event” WAF Simulation Deployed in F5
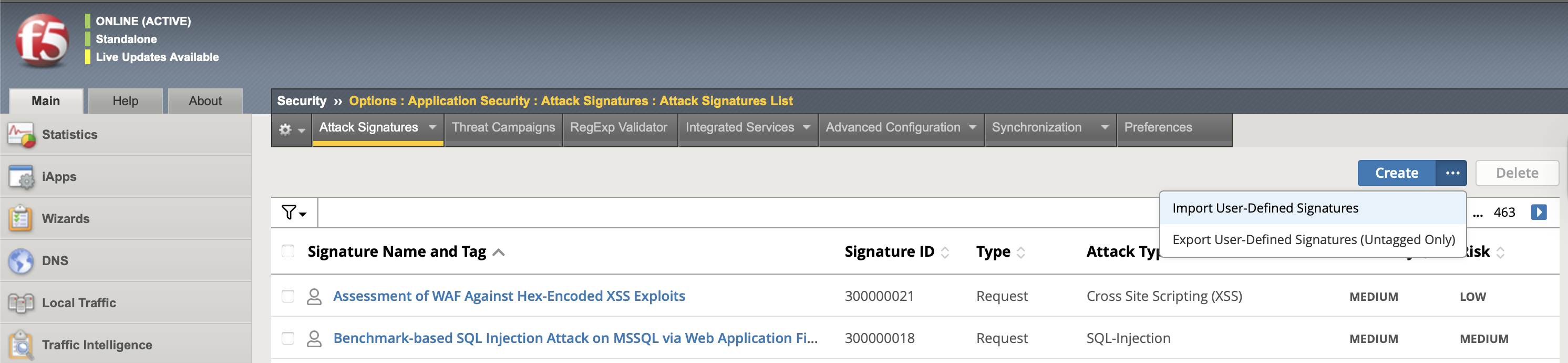
Adding the Cymulate Rules to the F5 platform via Import User-Defined Signatures
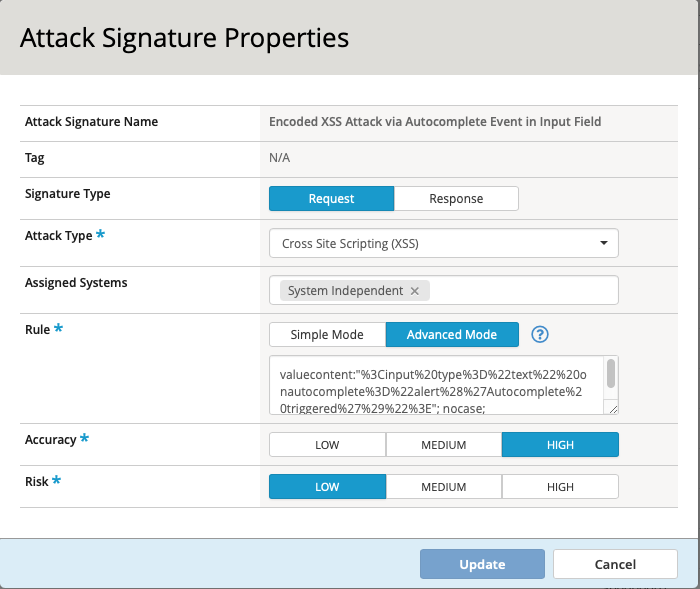
Viewing the created rule in F5
Understanding rule quality rankings
Every WAF Rule includes a quality ranking to help teams balance detection coverage and operational risk.
Higher-ranked rules use more specific detection logic, targeting known malicious behavior with minimal risk of false positives. Lower-ranked rules provide broader coverage and may require tuning, especially in environments with complex or diverse application traffic.
This transparency helps teams make informed decisions about how and when to deploy each rule.
Built through deep research and real-world WAF expertise
Delivering actionable WAF rules required significant research and engineering effort. The Cymulate Research Labs analyzed how WAF rules should be structured to be effective, precise and deployable across real customer environments.
Each Cymulate WAF scenario was examined to identify the exact detection logic required to stop the simulated attack. These rules were then consolidated into a universal mitigation format and translated into vendor-specific implementations based on deep analysis of platforms such as F5 and ModSecurity.
This approach ensures that WAF rules are not only technically accurate but also aligned with how WAFs operate in real production environments.
Extending detection validation across layers
Cymulate continues to expand its validation-driven approach across security controls, helping teams test and improve detection and prevention logic wherever attacks may surface, from endpoints and logs to web applications and APIs.
For Cymulate customers, you can get started immediately using the Ask AI feature in the Cymulate Platform. Ask AI provides step-by-step guidance for reviewing WAF findings, understanding recommended detection logic and implementing improvements as part of your broader validation efforts.
For security teams evaluating Cymulate, request a demo to see how the platform supports detection validation across multiple layers of the environment, helping teams move from test results to meaningful defensive improvements.
The goal remains consistent: to continuously prove, prioritize and improve your cyber defenses.