Frequently Asked Questions
Security Testing Methods & Comparisons
What are the main security testing methods organizations use today?
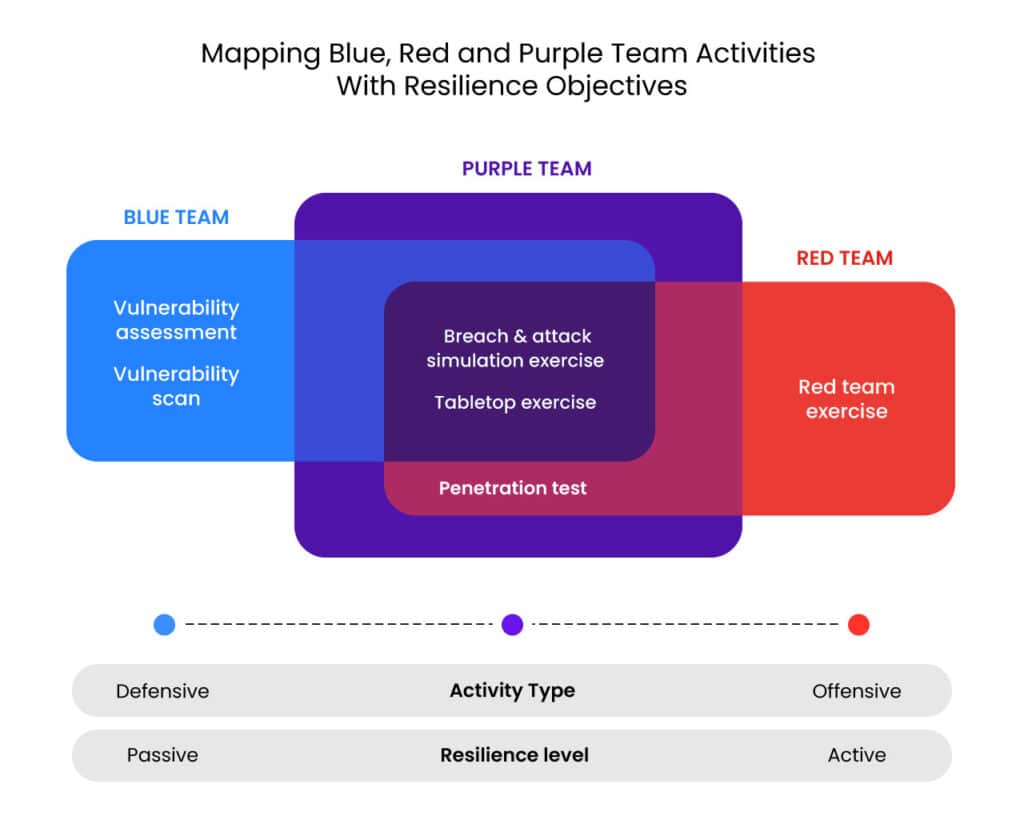
The main security testing methods include vulnerability scanning, penetration testing, red/blue teaming, and breach and attack simulation (BAS). Each method offers different levels of depth, automation, and frequency for validating an organization's security posture. (Source: Cymulate Blog)
How does vulnerability scanning work and what are its limitations?
Vulnerability scanning uses automated tools to check for known vulnerabilities in networks and host systems. It's fast, cost-effective, and can scan thousands of vulnerabilities, but it often produces a high rate of false positives (30-60%) and only provides a snapshot in time, lacking full insight into issues. It may also stress production environments, potentially causing downtime. (Source: Cymulate Blog)
What is penetration testing and when is it typically used?
Penetration testing is performed by expert testers who attempt to exploit vulnerabilities to assess how far they can penetrate an organization's security infrastructure. It's valuable for identifying high-risk weaknesses and is often required for compliance, typically conducted quarterly or semi-annually. However, results depend on tester skill, are limited in scope, and reports can take weeks to deliver. (Source: Cymulate Blog)
How do red and blue teaming exercises differ from other testing methods?
Red and blue teaming exercises simulate real-world attacks to test both the organization's defenses (blue team) and offensive capabilities (red team). They uncover unknown vulnerabilities and measure readiness to detect, contain, and mitigate attacks. These exercises are resource-intensive and cannot be conducted regularly. (Source: Cymulate Blog)
What is Breach and Attack Simulation (BAS) and how does Cymulate implement it?
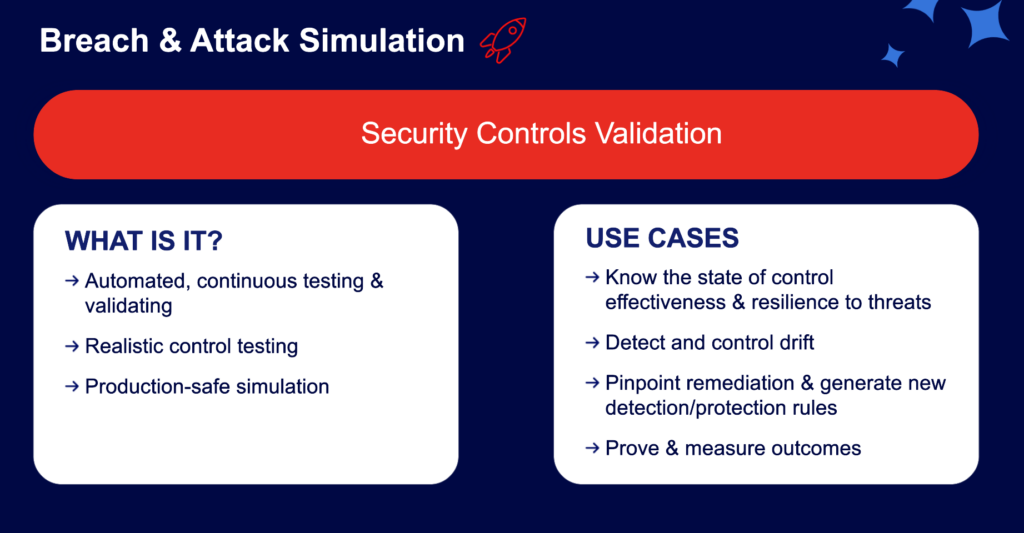
Breach and Attack Simulation (BAS) is an automated approach to continuously test, measure, and optimize the effectiveness of security controls. Cymulate's SaaS-based BAS platform allows organizations to run thousands of attack simulations with just a few clicks, providing continuous, fast, and actionable insights into security gaps. (Source: Cymulate Blog)
How does Cymulate's approach to security validation differ from traditional methods?
Cymulate's approach is fully automated, customizable, and continuous. Unlike traditional methods that are periodic and manual, Cymulate enables organizations to test their defenses any time, all the time, across the full attack kill chain, with integrations to SIEM and vulnerability scanners for deeper context and prioritization. (Source: Cymulate Blog)
What are the main advantages of using Cymulate over manual penetration testing?
Cymulate offers continuous, automated testing with immediate results, while manual penetration testing is periodic, resource-intensive, and dependent on tester skill. Cymulate provides actionable insights in real time, enabling organizations to address vulnerabilities faster and more efficiently. (Source: Cymulate Blog)
How does Cymulate help organizations prioritize remediation efforts?
Cymulate integrates with SIEM and vulnerability scanners to correlate attack simulations with real events and vulnerabilities, providing context on how vulnerabilities are exploited and helping organizations prioritize mitigation based on actual risk. (Source: Cymulate Blog)
Can Cymulate be used by red teams for offensive testing?
Yes, red teams use Cymulate to uncover a wide set of vulnerabilities and launch customized attacks, leveraging the platform's extensive library of simulated threats and automation capabilities. (Source: Cymulate Blog)
How does Cymulate support blue teams in validating detection capabilities?
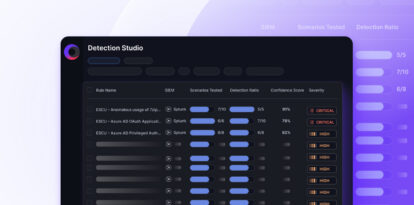
Cymulate integrates with SIEM vendors to correlate simulated attacks with events and alerts, enabling blue teams to validate that their SIEM systems are properly configured and effective at detecting threats. (Source: Cymulate Blog)
What is the kill chain and how does Cymulate test across it?
The kill chain refers to the sequence of stages in a cyberattack. Cymulate challenges security controls across the full kill chain with thousands of simulated threats, both common and novel, to identify gaps at every stage of an attack. (Source: Cymulate Blog)
How easy is it to use Cymulate for security testing?
Cymulate is designed to be simple and user-friendly, allowing users to initiate thousands of attack simulations with just a few clicks. The platform is fully automated and customizable, making advanced security testing accessible to all skill levels. (Source: Cymulate Blog)
What types of threats can Cymulate simulate?
Cymulate can simulate thousands of attack scenarios, including both common and novel threats, across the entire cyber kill chain. This comprehensive coverage helps organizations identify and address a wide range of vulnerabilities. (Source: Cymulate Blog)
How does Cymulate integrate with other security tools?
Cymulate integrates with SIEM vendors and vulnerability scanners, providing context to vulnerabilities and correlating simulated attacks with real events and alerts. This integration enhances prioritization and remediation efforts. (Source: Cymulate Blog)
What is the main benefit of continuous security validation?
Continuous security validation enables organizations to stay ahead of emerging threats by regularly testing and optimizing their defenses, rather than relying on periodic, point-in-time assessments. This proactive approach helps reduce risk and improve resilience. (Source: Cymulate Blog)
How does Cymulate help organizations address unknown vulnerabilities?
Cymulate's red team simulations use attacker techniques to uncover unknown vulnerabilities in unknown locations, providing organizations with insights into gaps that traditional methods may miss. (Source: Cymulate Blog)
What makes Cymulate's platform innovative compared to other BAS solutions?
Cymulate's platform is SaaS-based, fully automated, customizable, and integrates with existing security tools. It enables continuous, comprehensive testing with actionable insights, making advanced security validation accessible and efficient. (Source: Cymulate Blog)
How does Cymulate empower organizations to improve their security posture?
Cymulate empowers organizations by providing continuous assessment and validation of their security posture, enabling them to identify and remediate vulnerabilities proactively and stay ahead of cyber threats. (Source: Cymulate Blog)
Features & Capabilities
What features does Cymulate offer for security validation?
Cymulate offers continuous threat validation, unified BAS, CART, and exposure analytics, attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, ease of use, and an extensive threat library with over 100,000 attack actions updated daily. (Source: Cymulate Platform)
Does Cymulate integrate with other security technologies?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a full list, visit the Partnerships and Integrations page. (Source: Cymulate Knowledge Base)
How does Cymulate help with exposure prioritization?
Cymulate validates exploitability and ranks exposures based on prevention and detection capabilities, business context, and threat intelligence, helping organizations focus on the most critical vulnerabilities. (Source: Cymulate Knowledge Base)
What is the Cymulate threat library and how is it maintained?
The Cymulate threat library contains over 100,000 attack actions aligned to MITRE ATT&CK, with daily updates to ensure coverage of the latest threats and techniques. (Source: Cymulate Knowledge Base)
How does Cymulate support operational efficiency for security teams?
Cymulate automates security validation processes, leading to a 60% increase in team efficiency and saving up to 60 hours per month in testing new threats. (Source: Cymulate Knowledge Base)
What certifications and compliance standards does Cymulate meet?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and compliance standards. (Source: Security at Cymulate)
How does Cymulate ensure data security and privacy?
Cymulate uses encryption for data in transit (TLS 1.2+) and at rest (AES-256), hosts data in secure AWS data centers, and follows a strict Secure Development Lifecycle (SDLC) with regular vulnerability scanning and penetration testing. The platform is GDPR-compliant and includes mandatory 2FA, RBAC, and IP restrictions. (Source: Cymulate Knowledge Base)
How easy is it to implement Cymulate in an organization?
Cymulate is agentless, requiring no additional hardware or complex configuration. Customers can start running simulations almost immediately, with comprehensive support and educational resources available. (Source: Cymulate Knowledge Base)
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and actionable insights. Testimonials highlight its ease of implementation, accessible support, and immediate value in identifying and mitigating security gaps. (Source: Cymulate Knowledge Base)
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries, including finance, healthcare, retail, and more. (Source: Cymulate Knowledge Base)
What problems does Cymulate solve for security teams?
Cymulate addresses fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies, and post-breach recovery challenges. (Source: Cymulate Knowledge Base)
How does Cymulate help organizations improve threat resilience?
Cymulate provides continuous threat validation, exposure prioritization, and automated mitigation, enabling organizations to reduce critical exposures by up to 52% and achieve an 81% reduction in cyber risk within four months. (Source: Cymulate Knowledge Base)
Are there case studies showing Cymulate's impact?
Yes, for example, Hertz Israel reduced cyber risk by 81% in four months, and a sustainable energy company scaled penetration testing cost-effectively with Cymulate. More case studies are available on the Cymulate Customers page. (Source: Cymulate Knowledge Base)
How does Cymulate support compliance and regulatory requirements?
Cymulate automates compliance and regulatory testing, helping organizations in regulated industries demonstrate security control effectiveness and meet audit requirements. (Source: Cymulate Knowledge Base)
How does Cymulate help with post-breach recovery?
Cymulate enhances visibility and detection capabilities after a breach, enabling faster recovery and improved protection by replacing manual processes with automated validation. (Source: Cymulate Knowledge Base)
How does Cymulate address the needs of different security personas?
Cymulate tailors solutions for CISOs (metrics and risk prioritization), SecOps (automation and efficiency), red teams (offensive testing), and vulnerability management teams (validation and prioritization). (Source: Cymulate Knowledge Base)
What are the measurable outcomes of using Cymulate?
Organizations using Cymulate have reported a 52% reduction in critical exposures, a 60% increase in team efficiency, and an 81% reduction in cyber risk within four months. (Source: Cymulate Knowledge Base)
How does Cymulate help organizations communicate risk to stakeholders?
Cymulate provides quantifiable metrics and actionable insights, enabling CISOs and security leaders to justify investments and communicate risk effectively to stakeholders. (Source: Cymulate Knowledge Base)
Pricing & Plans
What is Cymulate's pricing model?
Cymulate uses a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, organizations can schedule a demo with Cymulate. (Source: Cymulate Knowledge Base)
Competition & Comparison
How does Cymulate compare to other security validation platforms?
Cymulate stands out with its unified platform combining BAS, CART, and exposure analytics, continuous automated testing, AI-powered optimization, complete kill chain coverage, ease of use, and proven customer outcomes. It is recognized as a market leader by Frost & Sullivan and a Customers' Choice in Gartner Peer Insights 2025. (Source: Cymulate Knowledge Base)
Resources & Support
Where can I find Cymulate's blog, newsroom, and resource hub?
You can access the latest threats, research, company news, and product information through the Cymulate Blog, Newsroom, and Resource Hub. (Source: Cymulate Knowledge Base)
How can I get support or a demo for Cymulate?
Organizations can schedule a personalized demo or reach out to Cymulate's support team via email or chat for assistance. (Source: Cymulate Knowledge Base)