Frequently Asked Questions
Vulnerability Management & Contextual Prioritization
Why is context important in vulnerability management?
Context is essential in vulnerability management because it helps you understand if a vulnerability can be exploited, how it might be leveraged by attackers, which assets are affected, and whether compensating controls are already in place. Without context, you might waste resources patching vulnerabilities that are not exploitable in your environment or overlook low-scoring vulnerabilities that pose significant risk. (Source: Original Webpage)
How does Cymulate use simulated attacks to improve vulnerability management?
Cymulate uses simulated attacks to provide real-world context for vulnerabilities. By emulating attacks, organizations can see which vulnerabilities are actually exploitable in their environment, how attackers might use them for lateral movement or privilege escalation, and whether existing controls are effective. This approach enables more accurate prioritization and efficient use of resources. (Source: Original Webpage)
What is Context Vulnerability Management (CVM) and how does it work?
Context Vulnerability Management (CVM) is an advanced approach that incorporates simulated and emulated attacks into vulnerability management. CVM provides full context for each vulnerability in your specific IT environment, considering compensating controls and business value of assets. This enables organizations to fine-tune patching schedules, maximize risk reduction, and optimize resource allocation. (Source: Original Webpage)
How do simulated attacks help prioritize patching?
Simulated attacks reveal which vulnerabilities are truly exploitable and which assets are at risk, allowing organizations to prioritize patching based on actual exposure rather than just CVSS scores. This means resources are focused on vulnerabilities that matter most, and patching can be scheduled more efficiently. (Source: Original Webpage)
How does Cymulate help measure and communicate the value of vulnerability management?
Cymulate collects data and analytics from simulated attacks, enabling security leaders to measure and communicate the impact of vulnerability management activities. Instead of just reporting the number of patches applied, teams can quantify improvements in security posture and demonstrate the effectiveness of their efforts to executive leadership. (Source: Original Webpage)
How does Cymulate increase team efficiency in vulnerability management?
Cymulate enables organizations to correlate vulnerability criticality with asset value, optimize patching prioritization, and reduce workload. By focusing remediation on assets that appear in multiple simulated attacks, teams can make a significant impact with minimal resources and avoid unnecessary downtime. (Source: Original Webpage)
What are compensating controls and how does Cymulate account for them?
Compensating controls are security measures that reduce the risk of a vulnerability being exploited. Cymulate's simulated attacks analyze whether these controls are effective, allowing organizations to deprioritize vulnerabilities that are already defended and focus on those that truly need remediation. (Source: Original Webpage)
How does Cymulate help avoid unnecessary patching and downtime?
By providing context through simulated attacks, Cymulate helps organizations determine which vulnerabilities require immediate attention and which can be addressed during the next scheduled patching window. This targeted approach reduces unnecessary patching and minimizes business disruption. (Source: Original Webpage)
What is the benefit of correlating vulnerabilities with asset value?
Correlating vulnerabilities with asset value allows organizations to prioritize remediation efforts on assets that are most critical to the business. This ensures that resources are used efficiently and that the most important systems are protected first. (Source: Original Webpage)
How does Cymulate's approach differ from traditional vulnerability management tools?
Traditional vulnerability management tools often rely solely on CVSS scores and do not consider the actual exploitability or compensating controls in place. Cymulate adds context through simulated attacks, enabling organizations to focus on vulnerabilities that pose real risk in their environment and avoid unnecessary remediation. (Source: Original Webpage)
What is the role of Breach and Attack Simulation (BAS) in vulnerability management?
Breach and Attack Simulation (BAS) tools, like Cymulate, validate security controls by simulating real-world attacks. This provides actionable insights into which vulnerabilities are exploitable and how effective current defenses are, enhancing the overall vulnerability management process. (Source: Original Webpage)
How does Cymulate help with lateral movement and privilege escalation risks?
Cymulate's simulated attacks can reveal if a vulnerability allows attackers to escalate privileges or move laterally within your environment. This insight helps prioritize remediation of vulnerabilities that could lead to significant breaches. (Source: Original Webpage)
How does Cymulate support communication with executive leadership?
Cymulate provides quantifiable metrics and analytics from simulated attacks, enabling security teams to communicate the impact of vulnerability management in terms that executives understand, such as risk reduction and improved security posture. (Source: Original Webpage)
What is the impact of production-safe simulated attacks?
Production-safe simulated attacks provide a comprehensive view of your IT environment without disrupting operations. They add context to vulnerabilities, enabling accurate prioritization and effective risk reduction. (Source: Original Webpage)
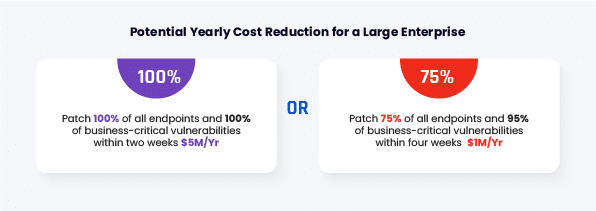
How does Cymulate help maximize risk reduction with limited resources?
Cymulate enables organizations to focus on vulnerabilities that pose the greatest risk, allowing teams to achieve significant risk reduction with less time and manpower. By automating attack simulations and prioritizing remediation, resources are used more efficiently. (Source: Original Webpage)
How does Cymulate's Exposure Validation feature work?
Cymulate Exposure Validation makes advanced security testing fast and easy by allowing users to build custom attack chains and validate exposures in one place. This helps organizations quickly identify and address vulnerabilities. (Source: Original Webpage)
How does Cymulate correlate simulated attack results with business value?
By correlating the results of simulated attacks with the business value of assets, Cymulate enables organizations to fine-tune patching prioritization and maximize the impact on risk exposure while staying within defined risk tolerance limits. (Source: Original Webpage)
How does Cymulate help organizations remain within risk tolerance limits?
Cymulate provides visibility into the effectiveness of compensating controls and the actual risk posed by vulnerabilities, allowing organizations to prioritize remediation and patching in line with their defined risk tolerance. (Source: Original Webpage)
What is the advantage of using Cymulate for vulnerability management over relying solely on CVSS scores?
Cymulate adds real-world context to vulnerability management by simulating attacks and considering compensating controls, asset value, and exploitability. This approach enables more accurate prioritization and risk reduction compared to relying solely on CVSS scores. (Source: Original Webpage)
Features & Capabilities
What are the key capabilities of Cymulate's platform?
Cymulate offers continuous threat validation, a unified platform combining Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics, attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, ease of use, and an extensive threat library with over 100,000 attack actions updated daily. (Source: Knowledge Base)
Does Cymulate integrate with other security tools?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a complete list, visit the Partnerships and Integrations page. (Source: Knowledge Base)
How easy is Cymulate to implement and use?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately, and the platform is praised for its intuitive, user-friendly interface. (Source: Knowledge Base)
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its ease of use, intuitive dashboard, and actionable insights. Testimonials highlight its user-friendly portal, excellent support, and the ability to quickly identify and mitigate threats. (Source: Knowledge Base)
What security and compliance certifications does Cymulate hold?
Cymulate holds several key certifications, including SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to robust security and compliance standards. (Source: Knowledge Base)
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and compliance with GDPR. The platform also features mandatory 2FA, RBAC, IP address restrictions, and a dedicated privacy and security team. (Source: Knowledge Base)
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, you can schedule a demo with the Cymulate team. (Source: Knowledge Base)
How does Cymulate compare to traditional vulnerability management tools?
Traditional tools focus on scanning and patching, often lacking context on exploitability. Cymulate provides continuous, automated exposure validation, prioritizing risks based on what is genuinely exploitable and integrating with existing security controls for a unified view. (Source: Knowledge Base)
What makes Cymulate different from other security validation platforms?
Cymulate stands out with its unified platform combining BAS, CART, and Exposure Analytics, continuous threat validation, AI-powered optimization, complete kill chain coverage, ease of use, and measurable outcomes such as up to 81% reduction in cyber risk within four months. (Source: Knowledge Base)
What types of organizations benefit from Cymulate?
Cymulate is designed for organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. It serves CISOs, SecOps teams, Red Teams, and Vulnerability Management teams. (Source: Knowledge Base)
How does Cymulate address common pain points in vulnerability management?
Cymulate addresses fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies, and post-breach recovery challenges through automation, integration, and actionable insights. (Source: Knowledge Base)
Are there case studies showing Cymulate's effectiveness?
Yes, for example, Hertz Israel reduced cyber risk by 81% in four months using Cymulate. Other case studies include organizations in finance, energy, and healthcare improving visibility, efficiency, and compliance. See more at the Cymulate Case Studies page. (Source: Knowledge Base)
What support and educational resources does Cymulate provide?
Cymulate offers email and chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers. The Resource Hub provides access to whitepapers, reports, and more. (Source: Knowledge Base)
Where can I find Cymulate's blog, newsroom, and resource hub?
You can find the latest insights, research, and company news on the Cymulate Blog, Newsroom, and Resource Hub. (Source: Knowledge Base)
Does Cymulate provide resources for understanding cybersecurity terms?
Yes, Cymulate offers a comprehensive Cybersecurity Glossary explaining terms, acronyms, and jargon. (Source: Knowledge Base)
What is Cymulate's overarching mission and vision?
Cymulate's mission is to transform cybersecurity practices by enabling organizations to proactively validate defenses, identify vulnerabilities, and optimize their security posture. The vision is to create a collaborative environment for lasting improvements in cybersecurity strategies. (Source: Knowledge Base)