Sigma Rules: Revolutionizing SOC Efficiency and Lightening Engineers' Workloads

With SOC operations consistently burdened by heavy workloads, sigma rules are a boon to accelerate their operation, potentially even allowing SOC engineers some much-needed downtime.
The chronic SOC engineers’ heavy workload stems from three main reasons:
- Endemic skill shortage: the demand for experienced SOC engineers continues to far exceed the pool of available talent
- Event Volume levels are on an exponential growth curve that shows no sign of leveling out
- Tool sprawl and underutilized SIEM and SOAR fail to noticeably lighten SOC engineers’ workload
The first two are unlikely to get better any time soon. The last one can considerably benefit from a Continuous threat Exposure Management (CTEM) approach, but, regardless, Sigma Rules greatly accelerate SOC engineers’ work.
What are Sigma Rules?
Sigma Rules are YAML-written textual signatures designed to identify suspicious activity potentially related to cyber threat anomalies in log events. One of the main advantages of these rules is their standardized format that permits writing the rule once and applying it across various SIEM products without needing to rewrite the rule.
The main focus of Sigma rules is to detect log events matching criteria established by the SoC engineer. This is especially useful for creating Incident Response detection or automated responses.
So yes, such rules can considerably lighten the SOC engineer workload, from reducing false-positive alerts to granularly automating response.
Yet, these rules still have to be written, or imported from an open-source library, costing the time to identify the adequate sigma rule for a specific case.
How to write a Sigma Rule
The first step to writing a Sigma rule is to define your goal. The goal can be any number of things, such as monitoring occurrences or a specific log event to detecting instances of a string associated with an exploit, for example.
Regardless of its goal, a rule consists of a few required sections and several optional ones. As Sigma is a very flexible standard, there is no fixed format, which provides infinite freedom but also requires rules writers to be self-disciplined, focused, and combine being exhaustive with being minimalist to avoid unnecessary clutter.
Basic Structure of a Sigma Rule
- Header: Contains metadata about the rule.
- Log Source: Specifies the type of log data the rule applies to.
- Detection: Defines the conditions that need to be met for the rule to trigger.
- Fields: Lists the fields to be returned in the event of a match.
- Tags: Used for categorization and linking to external references.
Example:
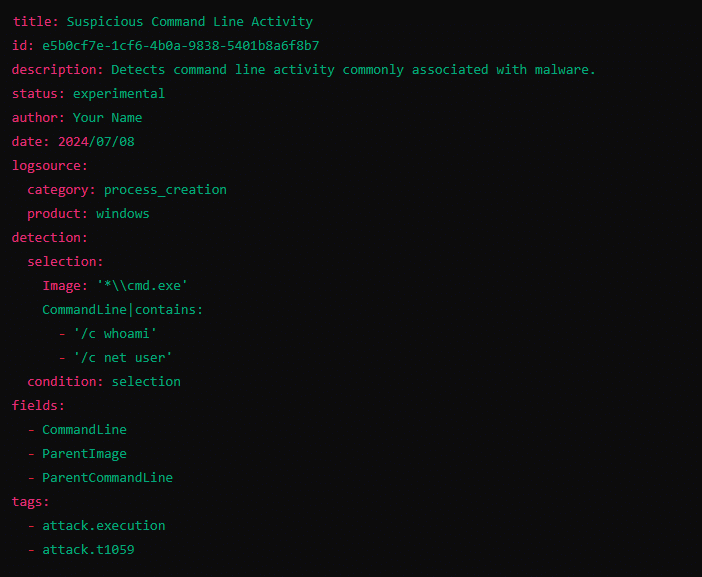
Breakdown of each section
1. Header:
- title: Descriptive name for the rule.
- id: A unique identifier for the rule (UUID format is recommended)
- description: A brief explanation of what the rule detects
- status: The maturity level of the rule (e.g., experimental, stable)
- author: The author of the rule
- date: The date the rule was created or last modified
2. Log Source:
- category: The type of log (e.g., process_creation, file_event)
- product: The platform or application the log comes from (e.g., windows, linux)
3. Detection:
- selection: The specific conditions to be matched in the log data
- condition: How to evaluate the conditions (e.g., selection, selection1 and selection2)
4. Fields:
- fields: The fields to display when a log entry matches the rule
5. Tags:
- tags: Keywords for categorization and linking to frameworks like MITRE ATT&CK
Benefits of Sigma Rules
In a nutshell, Sigma rules provide the following benefits for simplifying threat detection:
- Standardization: A unified format for creating and sharing detection rules
- Compatibility: Works with multiple SIEM and log management platforms
- Flexibility: Applicable to various log sources and customizable for specific needs
- Efficiency: Enables automated detection and reduces manual log analysis
- Improved Incident Response: Generates actionable alerts with specific information
- Cost-Effectiveness: Reduces false positives and optimizes resource use
- Scalability: Suitable for large and diverse IT environments
- Continuous Improvement: Regular updates and enhancements from community feedback
As an open-source community project, Sigma rules enable security operations teams to create queries in the Sigma rule format instead of vendor-specific SIEM languages. This means that a single rule is automatically translated into SIEM-specific code with a single click.
For example, this rule, written to detect access to printconfig.dll, an activity to would put the printer at risk of being breached, and thus potentially leak confidential information, would read as follow for Azure Sentinel SIEM tool,
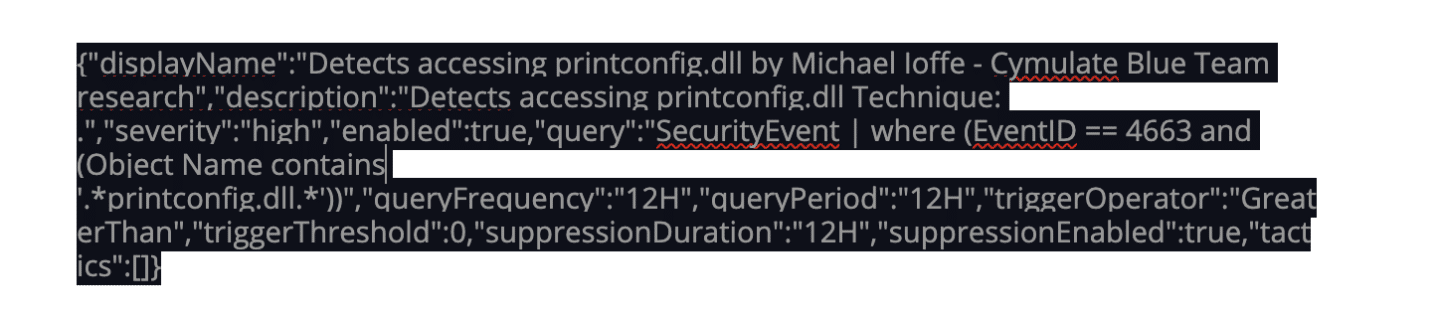
and the same rule would automatically be translated into the following code for Splunk

In practice, this means that a rule available on open-source for one specific SIEM in Sigma rule format is immediately available for everyone, regardless of the SIEM tool they use.
Why Cymulate's Off-the-Shelf Sigma Rules are a Game-Changer for SOC Teams
So now that it is clear that Sigma rules are a game-changer and can save SOC engineers considerable time, let’s consider how to further accelerate the Mean Time to Remediate (MTTR).
Once Cymulate’s assessment detects a security gap, it is listed in the report and includes a complete breakdown of the assessment’s attack technique that breached your infrastructure.
The technical information card for that emulated attack includes a full description, a list of detection commands, API calls, events, and more to monitor, mitigation recommendations, an analysis of the attack, the related tags, a list of the data sources involved and, most notably for this blog post, a ready-made sigma rule to include in your SIEM.
To create a rule, all your SOC engineer has to do is navigate to the scenario summary technique information card’s Sigma Rules tab and then select the relevant SIEM tool and click the Generate button.
For example, suppose an assessment detected a security gap, and your defensive array uses ArcSight and Sumo Logic SIEM software. In that case, all that is required is to select them one after the other from the drop-down menu and generate the rule.
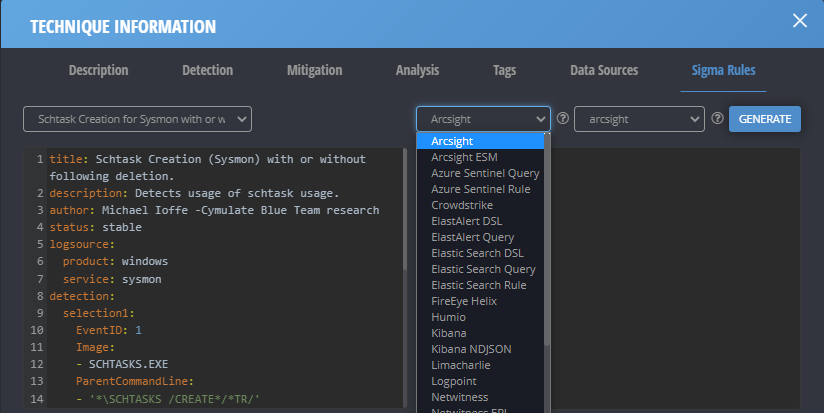
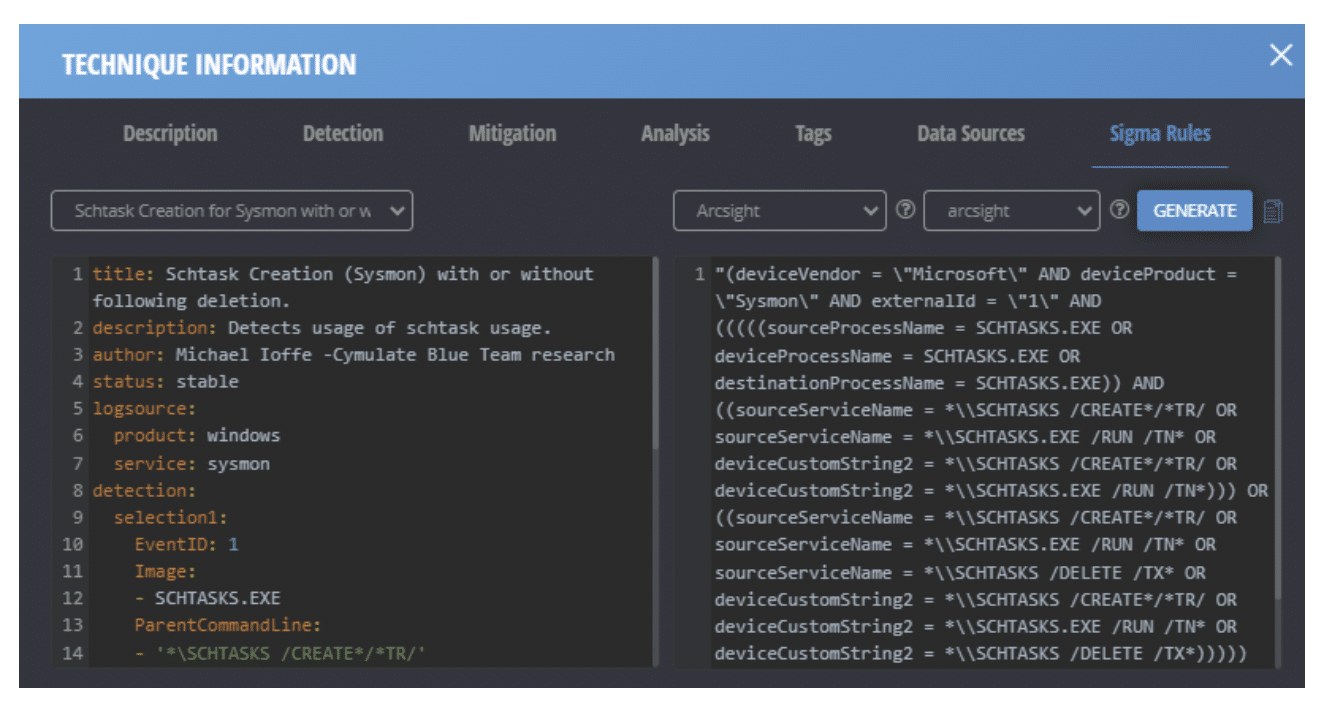
The only remaining action required is to copy-paste the rule into the relevant SIEM tools.
When taking into consideration the number of times this operation has to be repeated, the total work time Cymulate’s built-in Sigma rules save SOC engineers might even let them grab that after-work drink with friends that remained an unattainable dream until now.
Try the Cymulate Exposure Management and Security Validation platform to see CTEM in your unique environment by booking a demo: