Continuous Threat Exposure Management (CTEM) vs. Penetration Testing
Understanding how Continuous Threat Exposure Management (CTEM) compares to penetration testing is essential for building a well-rounded security strategy. While both approaches aim to identify weaknesses in an organization’s defenses, they differ in objectives, execution, and outcomes.
The following breakdown outlines the distinctions between the two and explains how they can work together to strengthen security posture.
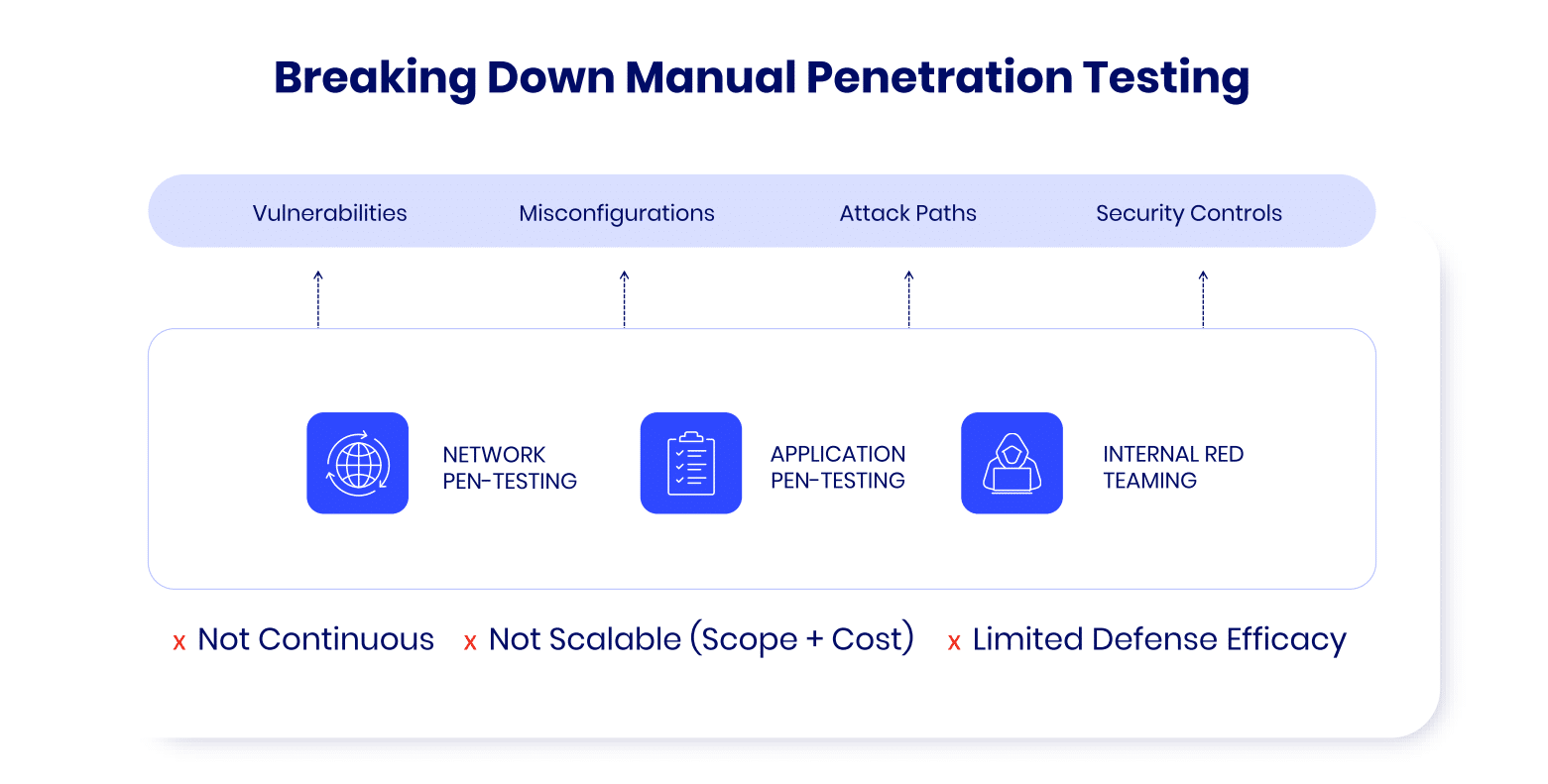
Defining Penetration Testing
Penetration testing is a human-driven offensive test that attempts to achieve a specific goal, such as capturing a specific system or removing a particular file or set of files. It is human-driven because the tester may encounter circumstances that require non-linear thinking, where the direct path is not the right path. An experienced pen-tester can shift and pivot at each step along the way – sometimes mid-step – and adapt techniques to reach the stated goal. This leads to a curious pattern: once a pen-tester overcomes a security control, they’re not performing all the other potential attacks they could have used – they’ve already overcome the control, and then move on.
The other hallmark of a pen test is that Rules of Engagement (ROE) are absolutely necessary to ensure that business operations are not disrupted, and no vital data is put at risk. Since a pen-tester may take paths that carry significant risks in pursuing their goal, knowing what is fair game – and what is off-limits – is critical to ensuring the test doesn’t do more harm than good.
Defining Continuous Threat Exposure Management (CTEM)
A CTEM approach consists of mapping an infrastructure's exposure, correlating the uncovered exposure to the exposed assets' values or the extent of the potential damage to business continuity and such. Whereas a pen tester is focused on achieving a specific goal, a CTEM approach is focused on identifying and preventing as many as possible of pen testers or attackers attempts to achieve an adversarial goal.
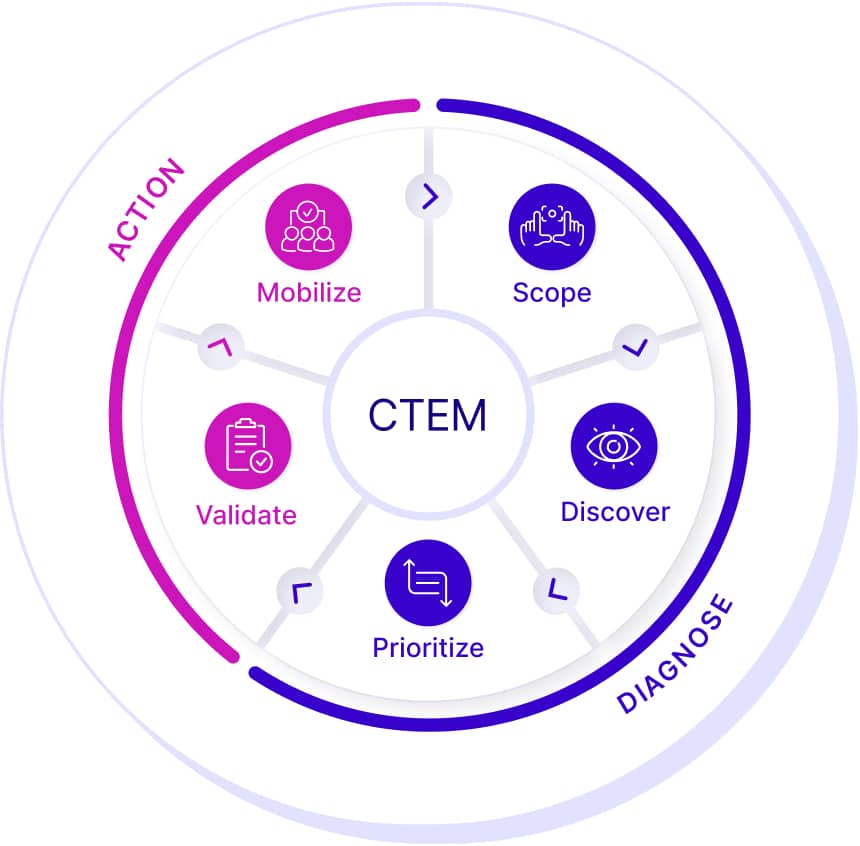
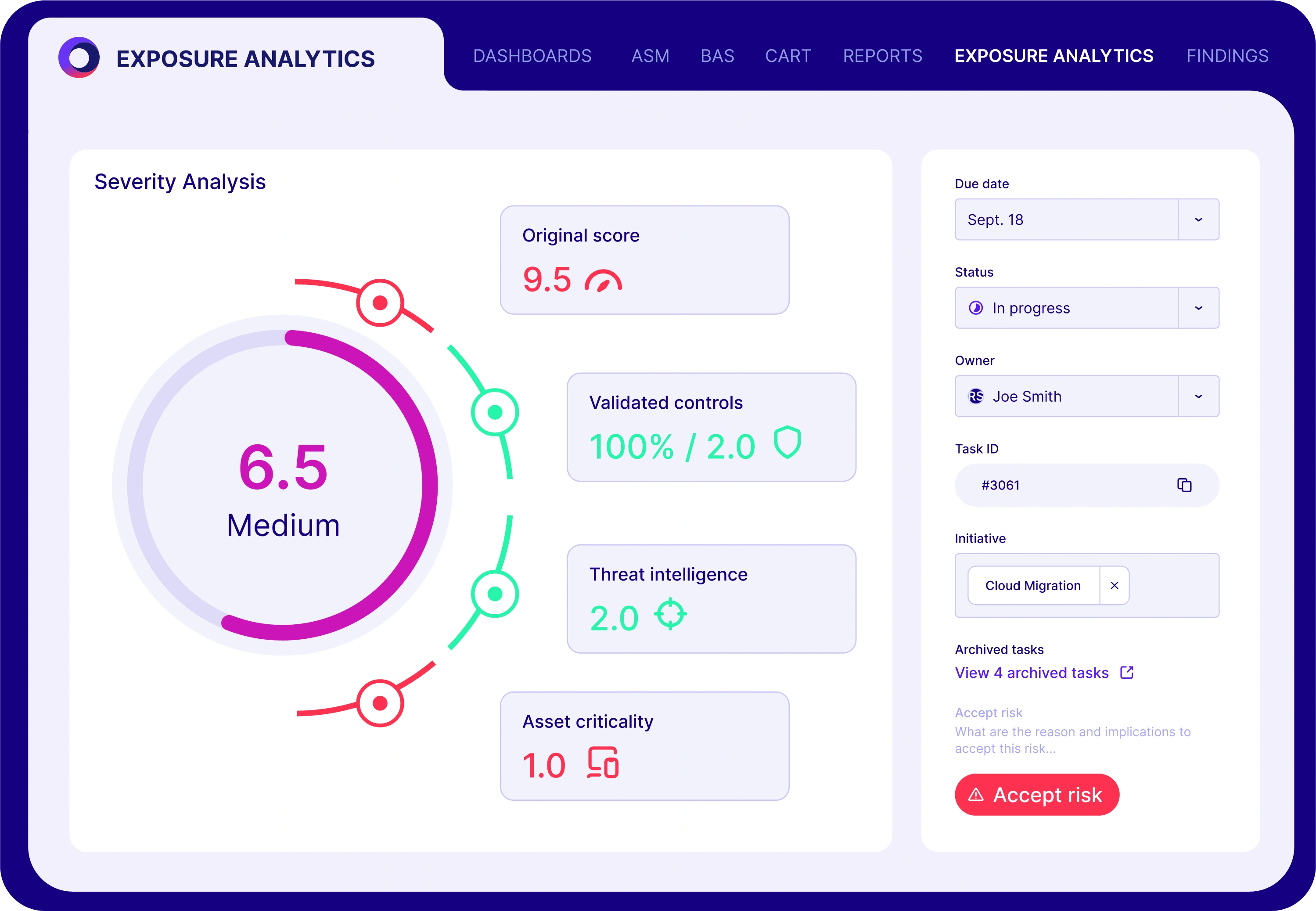
How Cymulate Implements CTEM
The Cymulate Exposure Management and Security Validation platform can implement a CTEM approach by validating the efficacy of security controls and uncovering security gaps. Instead of attempting to reach a specific goal, the Cymulate platform runs hundreds or thousands of simulation operations to map out the strengths and weaknesses of a set of security controls – such as endpoint defensive solutions or email gateway defenses, etc. Each layer of security is tested in-depth, and while the ability to look across layers of controls most definitely exists, the goal is a validation of the controls, not the pursuit of a targeted goal.
The platform is also designed from the ground up to be non-disruptive and non-destructive, removing the need for ROE without incurring risk to the systems, users, or data of the organization. This way, more systems can be tested, and tested more often, since this doesn’t increase risk or put the business in jeopardy of being offline, and requires minimal resources.
CTEM and Pen Testing: Why You Need Both
One of the most common mistakes made by organizations is to think that one methodology removes the need for the other.
Both CTEM and pen testing have value in a robust cybersecurity operation, and neither should be passed over in favor of the other. The reason is simple, the two methodologies are designed to do different things, and both are critical for knowing how to defend the organization against attacks.
Imagine you are a burglar attempting to steal something from a house. A thief would attempt to force the door open and, if that worked, would move on to try getting past the burglar alarm. If the door did not work, they would attempt entry via a window, and so on. The point here is that the first weakness in home security that works is the one they use as their goal is to steal whatever they are after.
A security contractor, conversely, would attempt to map out all the strengths and weaknesses of the house as a whole. Checking each door, window, storm cellar, a secret tunnel, porch entry, crawlspace, etc. The goal is not to steal but to define all the ways that someone could be successful in the attempt to get into the house to see where gaps exist in the house security.
Both types of operations can tell you a great deal about the overall security of the house. Both can also be used to cross-verify each other – the contractor may say a door is strong, but the thief might know how to pick that particular type of lock easily. Alone, you would have trouble getting the entire picture, but together you know that the house is protected.
Mapping Security Gaps with BAS and ASM
In the same way, using pen-testing and implementing a CREM approach together can allow you to know the complete state of your cybersecurity. Tools such as BAS and ASM map out the strengths and gaps of each layer of security controls while pen-testing along allowed paths (the ROE) allows you to truly battle-test where those gaps may line up to give an attacker an avenue of entry to a specific goal.
There is another reason to use both methodologies – preparation for future events. Implementing a CTEM approach can show you where gaps exist in any given set of security controls, even if those gaps cannot be actively used by an attacker at the current time. For example, a weakness in endpoint security may be compensated for by a strong defense at the network layer and, as such, may never be used by a pen-tester. That situation can change, however. If a new vulnerability is discovered in the networking security controls, that weakness that was unusable by a pen-tester today can suddenly become a huge problem tomorrow; and more to the point, a huge problem during the next pen-test if it isn’t addressed before that point.
Frequency and Timing: One-Time vs. Continuous Testing
While both methodologies are critical for overall cybersecurity, their schedules are vastly different. Pen-testing is a point-in-time operation, usually done once or twice per year. The reasons for this are the need to map out the ROE, along with the highly specialized training and experience a pen-tester must have – after all, with a limited number of experienced professionals, there are only so many tests they can do in a given amount of time. CTEM is designed to be used continually. When a CTEM implementation platform is configured well, you could have simulations of different layers of security across different environments, which result in there being a simulation occurring at any given time of any day of any month – ensuring true continuous assessment of the organization as a whole.
Because of differences in when these methodologies are performed, using just pen testing once a year leaves you with no visibility as to the effectiveness of your security controls the other 11 months of the year. Using both methodologies increases your visibility dramatically, allowing you to take action should any new vulnerabilities or concerns arise.
Integrated Testing for Comprehensive Security
The Cymulate Exposure Management and Security Validation platform gives you ongoing visibility into the strengths and gaps of the security controls throughout your organization. Pen testing provides directed confirmation that the controls work together properly – even when an attacker can change direction and strategy in the middle of the attack. Together, you can manage any gaps, ensure that an attacker would be derailed, and have the documentation to prove it should the need arise.
Cymulate is continuously developing its Exposure Management and Security Validation platform – for example, in the near future, it will be possible to project potential attack paths using the dataset created by assessments across different environments and security control sets. That being said, until AI advances to the point where an automated system can safely perform potentially destructive operations while still holding to a set of Rules of Engagement, the need for implementing both a CTEM approach and running pen-tests will ensure that using both methodologies is going to be the gold standard for some time to come.