Frequently Asked Questions
Email Gateway Attack Simulation: Fundamentals
What is an email gateway attack simulation?
An email gateway attack simulation is a process that attempts to sneak simulated malicious emails past your organization's email security filters and directly into user mailboxes. These simulations mimic real-world threats—such as phishing links, malware attachments, and spoofed emails—to test whether your email gateway can detect and block them. The goal is to identify weaknesses in your email security controls before actual attackers can exploit them. (Source)
How do email gateways work to protect organizations?
Email gateways are software or appliances that sit between inbound emails and user mailboxes. They evaluate each email for phishing language, malicious links, malware attachments, and spoofing attempts. Advanced gateways may use sandboxing to open and analyze attachments in a safe environment, ensuring they don't harm the organization if opened by users. (Source)
What challenges can arise with email gateway security?
Challenges include misconfiguration of settings, outdated detection algorithms, and the complexity of managing advanced gateways with many moving parts. These issues can cause the filtration system to miss critical threats, allowing malicious emails to reach user mailboxes. (Source)
How does Cymulate's Email Gateway Vector work?
Cymulate's Email Gateway Vector uses a designated test email account set up by your organization. Simulated threat emails are sent to this account, and if any reach the mailbox, a mail-forwarding rule sends them to Cymulate’s analytics servers for analysis. This process helps identify weaknesses in your email security controls without disrupting normal business operations. (Source)
What happens if a simulated attack email reaches the test mailbox?
If a simulated attack email reaches the test mailbox, it indicates a gap in your email security controls. Cymulate provides remediation suggestions, such as blocking certain file types or tightening filter settings, and allows you to re-run the simulation to confirm the issue is resolved. (Source)
How does email gateway attack simulation differ from phishing awareness simulation?
Email gateway attack simulation tests the ability of your email security software to block threats, using a test mailbox. Phishing awareness simulation, on the other hand, sends simulated phishing emails to actual users to test whether they fall for the trick. Both are important: one tests your systems, the other tests your people. (Source)
Why is regular email gateway attack simulation important?
Regular simulation ensures both your email security systems and your users are prepared to defend against evolving threats. It helps identify configuration gaps, outdated detection, and user vulnerabilities before attackers can exploit them. (Source)
What types of threats can email gateway attack simulation help detect?
Simulations can help detect threats such as phishing emails, malicious links, malware attachments, spoofed sender addresses, and advanced attacks that may bypass traditional filters. (Source)
How does Cymulate help remediate email security weaknesses?
Cymulate provides detailed findings for each simulation, including how the attack worked and specific remediation guidance—such as blocking risky file types or adjusting filter settings. After remediation, you can re-run simulations to confirm the issue is fixed. (Source)
What is the role of sandboxing in email gateway security?
Sandboxing allows advanced email gateways to open and run executable code from attachments in a controlled environment. This helps detect malicious behavior that might not be caught by traditional scanning methods. (Source)
How does Cymulate ensure simulations do not disrupt business operations?
Cymulate uses a designated test email account for simulations, so regular user mailboxes and business workflows are not affected. Any simulated attack that reaches the test mailbox is analyzed without risk to the organization. (Source)
Why is it important to test both email gateways and user awareness?
Testing both ensures comprehensive security: email gateway simulations validate your technical controls, while phishing awareness simulations assess user susceptibility to social engineering. Both are critical for reducing risk from email-borne threats. (Source)
How does Cymulate's Email Gateway simulation help prevent malicious payloads?
Cymulate’s Email Gateway simulation exposes vulnerabilities in your email security framework, helping you prevent malicious payloads and phishing attacks by identifying and addressing weaknesses before attackers can exploit them. (Source)
What percentage of cyberattacks originate from email?
Over 75% of cyberattacks worldwide originate from malicious email, making email gateway security and regular simulation critical for organizational defense. (Source)
How does Cymulate provide remediation guidance after a failed simulation?
Cymulate details how each simulated attack worked and offers actionable remediation steps, such as blocking specific file types or tightening filter rules. You can then re-run the simulation to verify the fix. (Source)
What is the difference between testing email gateways and testing users?
Testing email gateways focuses on the effectiveness of your technical controls, while testing users (phishing awareness) evaluates whether employees can recognize and avoid phishing attempts. Both are necessary for a robust security posture. (Source)
How does Cymulate's Email Gateway Vector minimize risk to users?
By using a designated test mailbox and only simulating threats, Cymulate ensures that no real users are exposed to risk during simulations. Any simulated attack is safely analyzed and remediated. (Source)
What is the remediation process after a simulation identifies a weakness?
Cymulate provides remediation suggestions tailored to the specific scenario, such as adjusting filter settings or blocking file types. After implementing the fix, you can re-run the simulation to ensure the vulnerability is closed. (Source)
How does Cymulate help organizations stay ahead of email-borne threats?
Cymulate continuously assesses and validates your email security posture with up-to-date simulations, helping you identify and remediate vulnerabilities before attackers can exploit them. (Source)
What is the main benefit of using Cymulate for email gateway attack simulation?
The main benefit is proactive identification and remediation of weaknesses in your email security controls, reducing the risk of successful phishing and malware attacks. (Source)
Features & Capabilities
What are the key features of Cymulate's Email Gateway Validation solution?
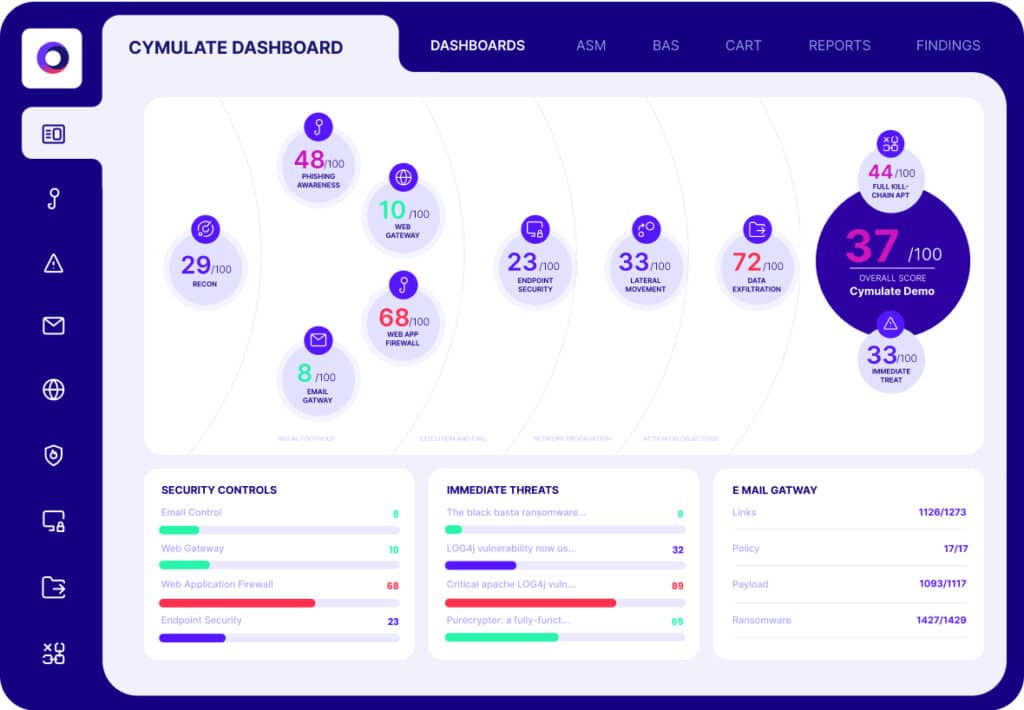
Cymulate's Email Gateway Validation solution offers fully automated assessments, simulating over 10,000 production-safe test emails with the latest ransomware, malware, worms, trojans, and exploits. It provides detailed findings, including risk scores, penetration ratios, attack type breakdowns, and mitigation guidance to optimize your email security investment. (Source)
What integrations does Cymulate support for email and endpoint security?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, and SentinelOne. For a complete list, visit the Partnerships and Integrations page.
How easy is it to implement Cymulate's Email Gateway Validation?
Cymulate is designed for quick, agentless deployment with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately, with comprehensive support and educational resources available. (Source)
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and ease of implementation. Testimonials highlight the platform's simplicity, actionable insights, and accessible support. (Source)
What compliance certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and privacy standards. (Source)
How does Cymulate ensure data security and privacy?
Cymulate uses encryption for data in transit (TLS 1.2+) and at rest (AES-256), hosts data in secure AWS data centers, and follows a strict Secure Development Lifecycle (SDLC) with regular vulnerability scanning and third-party penetration testing. (Source)
What is Cymulate's pricing model for Email Gateway Validation?
Cymulate operates on a subscription-based pricing model tailored to each organization's needs, considering the chosen package, number of assets, and scenarios. For a detailed quote, schedule a demo with the Cymulate team.
How does Cymulate compare to traditional email security testing methods?
Cymulate provides automated, continuous, and production-safe simulations, offering more comprehensive and actionable insights than traditional point-in-time assessments or manual penetration tests. (Source)
What types of organizations can benefit from Cymulate's Email Gateway Validation?
Organizations of all sizes and industries—including finance, healthcare, retail, media, transportation, and manufacturing—can benefit from Cymulate’s Email Gateway Validation to strengthen their email security posture. (Source)
How does Cymulate support compliance and regulatory requirements?
Cymulate helps organizations meet compliance and regulatory requirements by providing automated, auditable testing and reporting aligned with industry standards and frameworks. (Source)
What kind of support and resources does Cymulate offer to customers?
Cymulate provides email and chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers and best practices. (Source)
How does Cymulate help organizations prioritize remediation efforts?
Cymulate uses AI-powered analytics to validate exploitability and rank exposures based on prevention and detection capabilities, business context, and threat intelligence, helping organizations focus on the most critical vulnerabilities. (Source)
Where can I find more resources about Cymulate's Email Gateway Validation?
You can find solution briefs, blog posts, and best practices in the Cymulate Resource Hub and on the Email Gateway Validation page.
How does Cymulate stay up-to-date with the latest email threats?
Cymulate’s threat library is updated daily with the latest attack techniques, ensuring simulations reflect current threat landscapes and helping organizations stay ahead of emerging risks. (Source)