Healthcare in the Cloud: Why Exposure Validation is Essential for Protecting Patient Data

Cloud computing is transforming the healthcare industry, allowing medical teams to share urgent medical details right away, speeding up response times and saving lives. But the reliance on cloud infrastructure comes at a price.
Healthcare systems are a frequent target for cyberattacks aimed at accessing sensitive data or disrupting operations. Because a breach can disrupt clinical workflows, robust data protection s a critical foundation for modern medicine.
This article explores the critical threats to healthcare in the cloud and explains how to validate your defenses with an exposure validation platform.
Key highlights:
- Healthcare in the cloud enables medical teams to share vital information instantly to improve patient care, but it requires robust security to protect sensitive records from cybercriminals.
- Major security threats include ransomware, phishing and insider attacks, which can freeze hospital networks and jeopardize life-saving treatments.
- Essential data protection demands strict adherence to regulations such as HIPAA and GDPR, requiring encryption, access controls and regular compliance monitoring to avoid fines.
- The Cymulate Exposure Management Platform moves organizations from reactive defense to proactive resilience by simulating attacks to identify and fix vulnerabilities before hackers exploit them.
What is cloud security in healthcare?
Cloud security in healthcare refers to the specialized strategies, policies and technologies used to protect sensitive patient data, applications and infrastructure within cloud computing environments.
Unlike general cloud security, healthcare environments prioritize securing electronic protected health information (ePHI) to meet strict regulatory requirements such as the Health Insurance Portability and Accountability Act (HIPAA) and the General Data Protection Regulation (GDPR).
Core objectives:
- Data protection: Ensuring the confidentiality, integrity and availability of ePHI through strong encryption and tokenization.
- Regulatory compliance: Meeting federal standards for data privacy and security to avoid heavy fines and legal ramifications
- Operational continuity: Maintaining the availability of critical medical services during outages or cyberattacks.
Why healthcare cloud security matters
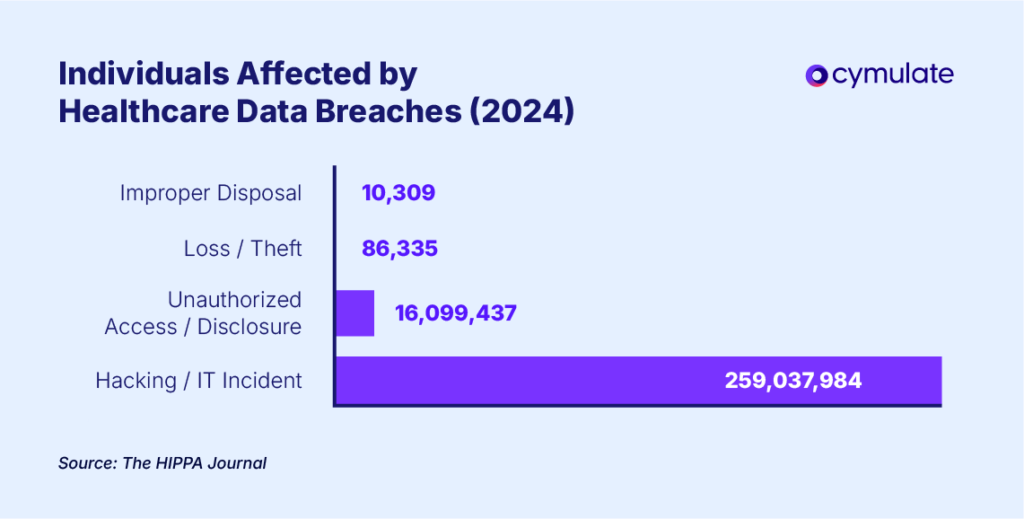
Healthcare cloud security matters because the stakes are uniquely high. According to the HIPAA Journal, 82% of the United States population had their medical records exposed, stolen, or disclosed in 2024.
Attackers are motivated by the high value of healthcare data and the operational pressure healthcare organizations face. Healthcare providers are often more likely to pay a ransom to restore their systems. For example, Change Healthcare admitted to paying a $22 million ransom to hackers during their targeted attack.
Patient data, including protected health information (PHI), personally identifiable information (PII) and insurance details, is a a valuable asset that attackers can use to steal identities, commit fraud, or launch larger-scale attacks for identity theft, fraud or broader cyber activity. Cloud computing introduces complex vulnerabilities additional complexity. A security breach can affect both patients and healthcare providers.
Examples include:
Data breaches
Due to the immense volume of data that flows through healthcare systems, ransomware and data breaches can occur if security controls are insufficient. These breaches often lead to the unauthorized exposure of personal health records (PHR), PHI and PII.
Through phishing attacks, or vulnerability exploits, attackers can force healthcare organizations to make difficult operational decisions, potentially impacting trust and service continuity.
Regulatory concerns
Protecting patient data and ensuring it is managed securely is a legal obligation in healthcare. HIPAA and GDPR mandate how organizations store, move and protect patient data.
Healthcare organizations must invest in secure cloud systems, backup solutions and breach-detection protocols to ensure they meet all required regulatory standards. If they fail to meet these standards, they could be hit with significant fines and experience reputational damage.
Cloud security risks in key technologies
Connecting cloud-based medical devices and centralized cloud storage for medical records creates new entry points for attackers. Because different tools have different weaknesses, they require specific defenses. The table below outlines the principal risks and necessary protections for three critical healthcare technologies:
| Cloud-based technology | Primary risk | Key protection |
| Electronic health record (EHR) | Unauthorized access to centralized patient data | Encryption, access controls, audits |
| Telemedicine | Compromised cloud platforms | Encryption, secure protocols, MFA |
| IoT devices | Unauthorized access to connected devices | Device security, cloud security validation |
Essential solutions for cloud security in healthcare
Effective healthcare data security solutions must address both security and compliance. Whether using a public or private cloud service, organizations need these five critical measures.
- Data encryption: Data must be encrypted both in transit and at rest. This ensures that even if a hacker intercepts the files, they cannot read or exploit the information.
- Identity and Access Management (IAM): IAM systems use tools such as Multi-Factor Authentication (MFA) to ensure that only authorized personnel can access sensitive records.
- Network security: Defenses such as firewalls and intrusion detection systems (IDS) are necessary to block malware, ransomware and unauthorized traffic before they breach the network.
- Compliance monitoring: Solutions should include built-in features to track adherence to HIPAA and cloud computing regulations, helping the organization avoid fines and legal issues.
- Backup and disaster recovery: Regular backups ensure that if a system failure or cyberattack occurs, patient data can be restored quickly without disrupting care.
Major threats to healthcare in the cloud
While the cloud offers speed and efficiency, it also opens the door to sophisticated cyberattacks. Understanding these major threats to medical data security is the first step in building a strong cloud security healthcare strategy.
- Ransomware attacks: Cybercriminals target healthcare organizations with malware that encrypts sensitive data and demands a ransom for its release. Healthcare organizations are particularly vulnerable due to the urgency of accessing medical records for patient care.
- Insider threats: Healthcare workers with malicious intent or negligent behavior can unintentionally expose sensitive data or intentionally leak information for personal gain.
- Phishing attacks: Attackers use phishing emails to trick healthcare staff into divulging login credentials, enabling unauthorized access to cloud-based systems.
- Misconfigurations: Incorrectly configured cloud systems can expose sensitive data. For example, cloud storage misconfigurations can result in publicly accessible patient records.
- Advanced Persistent Threats (APTs): APTs involve cybercriminals establishing long-term access to a network with the goal of stealing valuable data over time. These threats often evade traditional security measures.
Cymulate platform strengthens cloud security in healthcare
To ensure healthcare data protection, organizations must move from assuming they are safe to proving it. This is the core of exposure validation.
Unlike traditional scanning, exposure validation proactively tests your network simulating real-world attacks. The test reveals how an attacker could access sensitive data, empowering teams to prioritize remediation. to reach sensitive patient records, empowering your team to fix your vulnerabilities.
The Cymulate Exposure Validation Platform moves healthcare organizations from reactive defense to proactive resilience.
Here is how we strengthen cloud security in five key ways:
- Continuous security testing: The Cymulate platform performs continuous testing to assess cloud security posture and by simulating real-world attack scenarios, healthcare providers can identify vulnerabilities before they are exploited.
- Simulated phishing campaigns: We can simulate a real-life phishing attack and how employees respond to help educate and train staff on best security practices, reducing the risk of human error.
- Identifying misconfigurations: With the Cymulate exposure validation platform, check for commonly misconfigured cloud systems across the entire infrastructure to ensure that sensitive patient data remains protected.
- End-to-end risk assessment: Gain a comprehensive risk assessment that highlights potential threats, whether they come from insiders, outsiders or system failures. This helps organizations prioritize security measures based on potential impact and what steps to take first.
- Incident response preparation: Cymulate can help healthcare organizations assess the effectiveness of their incident response plans by simulating a variety of attack scenarios. This will enable security teams to practice their response to a cyber-attack and refine their processes to ensure they are well-prepared for a real-life incident.
Don't wait for a breach to find out if your security works. See exactly where your vulnerabilities are with a live demonstration of the Cymulate platform. Book your demo now.
Frequently asked questions
Key trends in healthcare cloud security technology focus on zero-trust architectures to enforce strict identity verification and continuous security validation, ensuring defenses actually block real exploits. Because medical data is a high-value target for ransomware, organizations are moving beyond point-in-time audits to automated platforms that optimize incident response and ensure HIPAA compliance.
Explore Cymulate for healthcare.
Cloud security directly impacts patient data protection by ensuring that sensitive records remain private and available only to authorized providers. Without cloud security monitoring, patient data is vulnerable to theft, ransomware and unauthorized changes that can compromise medical care.
Yes, small healthcare providers can implement effective enterprise cloud security measures. The providers should start with the basics: Multi-Factor Authentication (MFA), encryption and staff training. Automated exposure validation tools are also highly effective for small healthcare teams, allowing them to test their defenses like a large enterprise without needing a massive security staff.
To ensure best practices for healthcare cloud security, organizations should enforce strict identity access management (IAM) and conduct continuous security validation. Beyond basic defense measures, organizations must conduct regular phishing simulations and automate compliance checks to meet HIPAA standards.