Security Control Validation for Healthcare
Book a demo to see how Cymulate automates advanced offensive testing with the latest threats activity facing the healthcare industry.
Healthcare Industry Under Attack
Cyber attackers have increasingly targeted the healthcare sector, not only due to the high value of compromised patient data but also because of its extreme sensitivity to disruptions.
Threat actors know that healthcare providers will pay millions more in ransom payments to recover or maintain critical services.
Average Healthcare
Data Breach Cost
$10.93M
Adopt the Attacker’s View to Harden Defenses
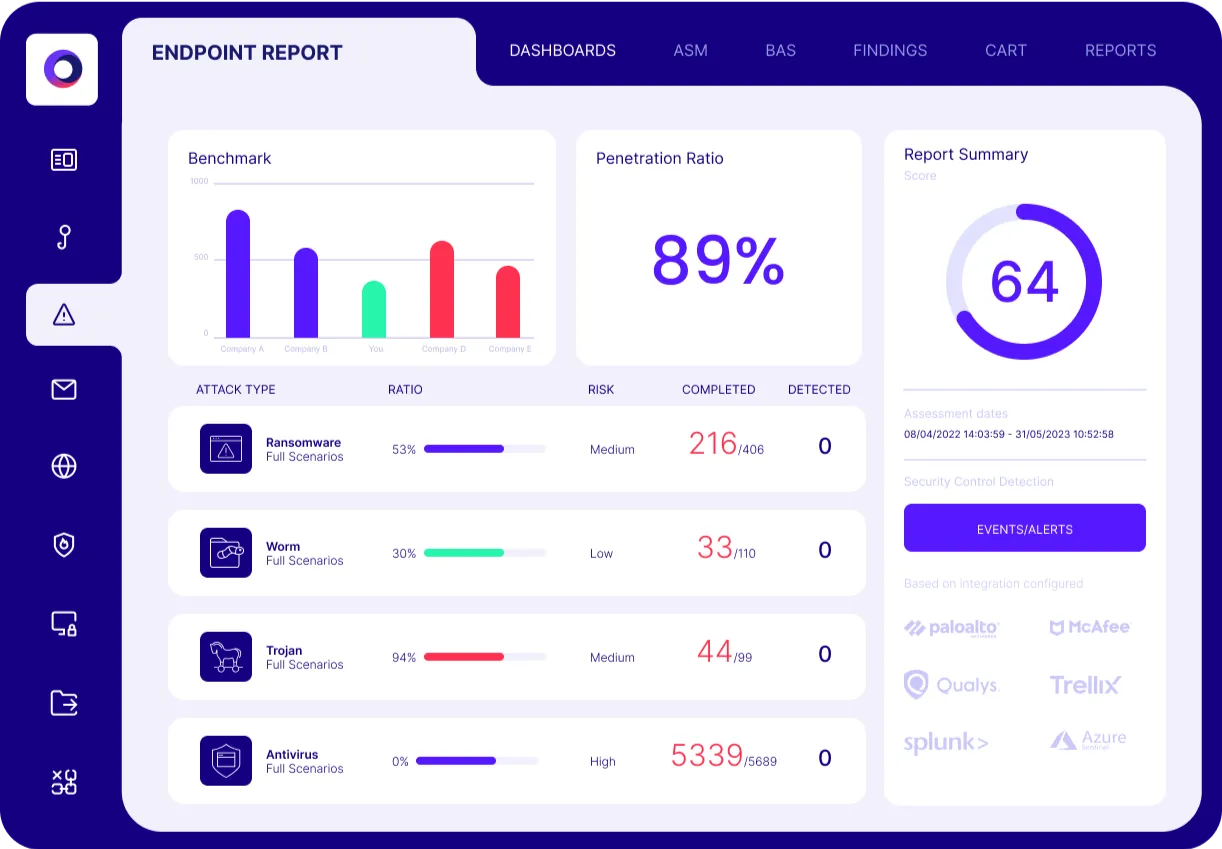
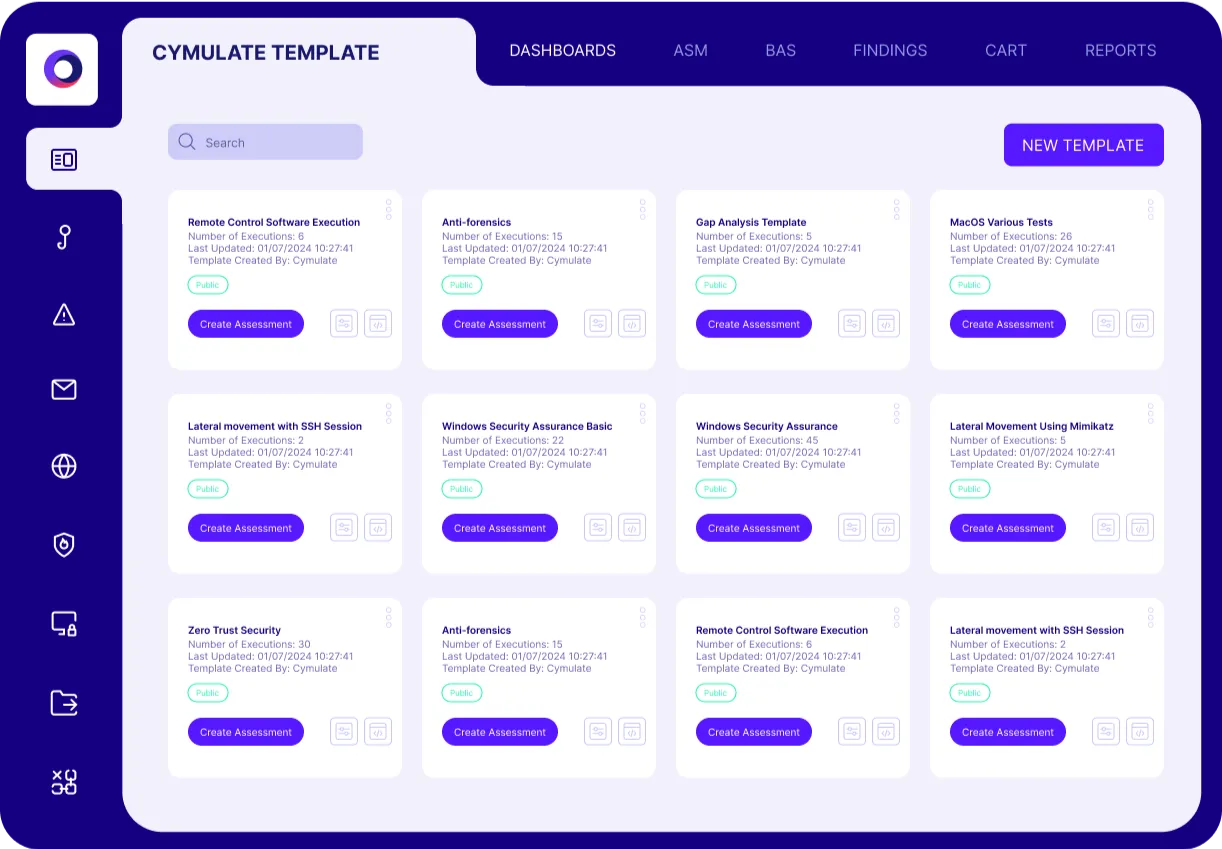
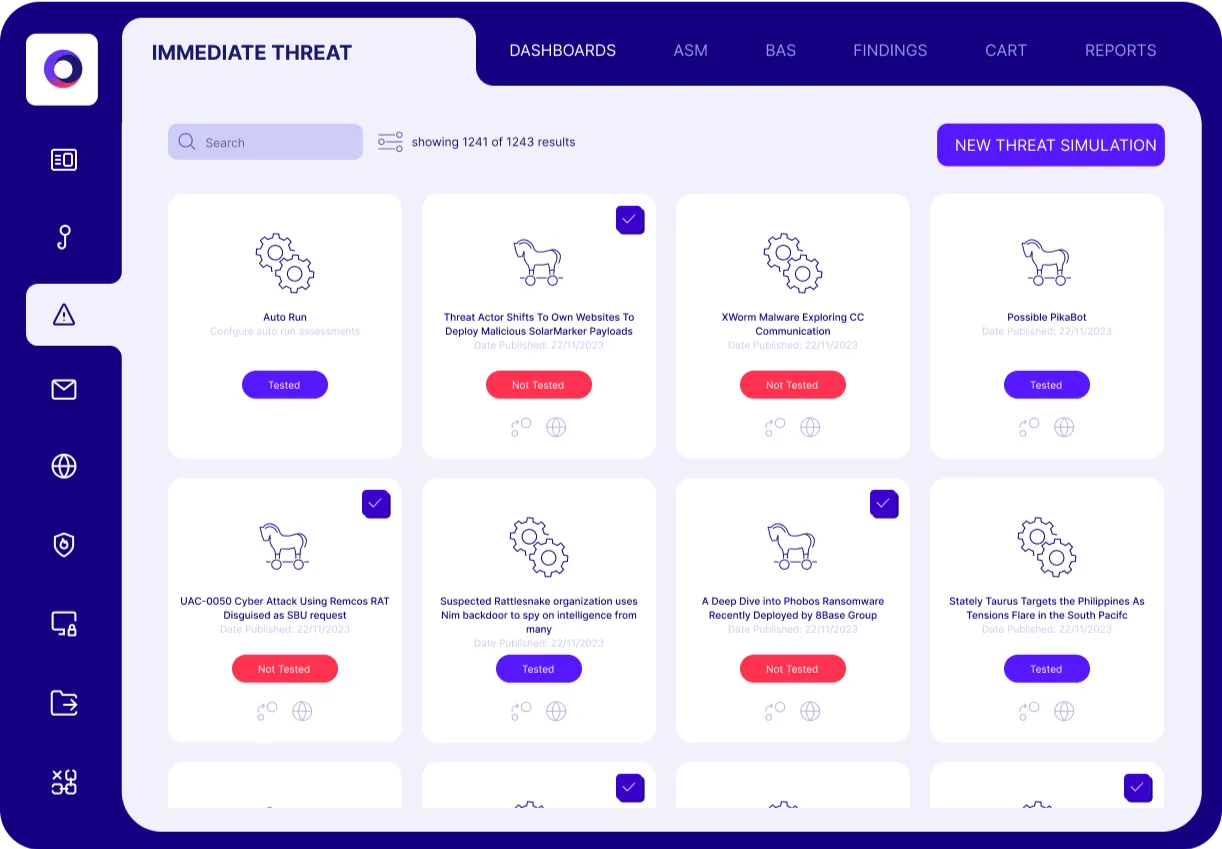
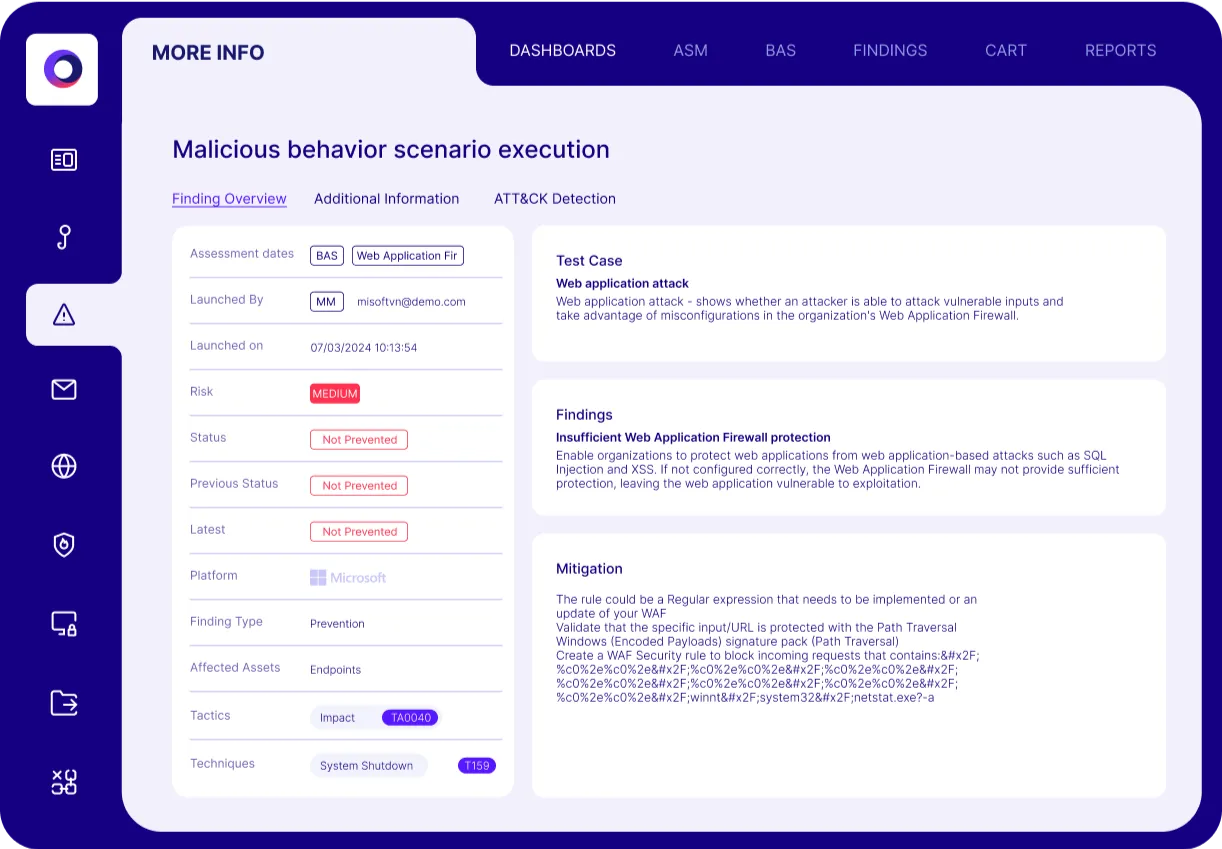
Healthcare organizations like Assuta Medical Center and Elara Caring know they must be prepared for the next attack, so they use Cymulate security control validation to continuously validate their cyber security controls and test their defensive posture. Cymulate automates advanced offensive testing with the latest threat activity facing the healthcare industry. Each assessment includes remediation guidance with specific steps to update security configurations and tune controls.
Breach and Attack Simulation
Automated Red Teaming
Automated Mitigation
Cymulate Healthcare Cybersecurity Solutions
Validate Defenses
against Emergent Threats
Test Continuously
with Automated Testing
Optimize Defenses
with Remediation Guidance
What our customers say about us
Organizations across all industries choose Cymulate for automated cybersecurity validation, proactively confirming that defenses are robust and reliable-before an attack occurs.
See the power of Cymulate security and exposure validation
Book a demo to see how Cymulate automates advanced offensive testing with the latest threats activity facing the healthcare industry.