Frequently Asked Questions
Log4Shell Vulnerability & Prevention
What is the Log4Shell vulnerability and why is it significant?
The Log4Shell vulnerability (CVE-2021-44228) is a critical flaw in the Apache Log4j 2 Java-based logging package. It allows unauthenticated attackers to execute remote code on affected systems, potentially disrupting operations and exposing sensitive data. Its widespread use in major technology platforms makes it a high-impact threat. Learn more on MITRE.
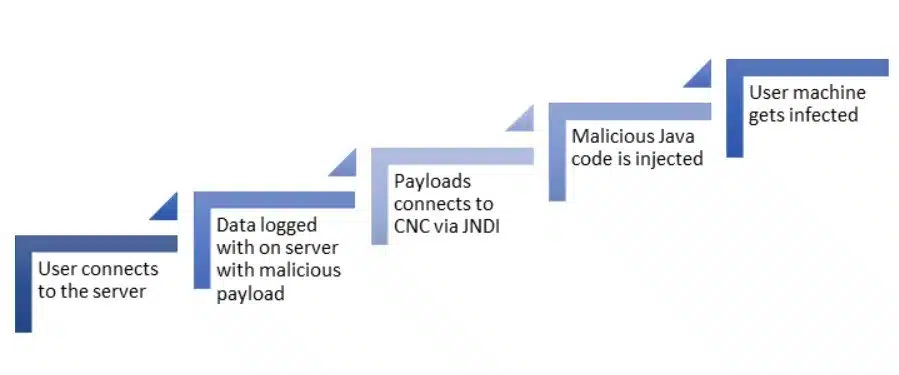
How does the Log4Shell exploit work?
The vulnerability exists in the Java Naming and Directory Interface (JNDI) implementation of Log4j. Attackers can trigger it using a specially crafted LDAP request, causing Log4j to retrieve and execute a remote payload. This enables remote code execution (RCE) on the target system.
What steps should organizations take to prevent Log4Shell attacks?
Organizations should:
- Identify all internal and third-party usage of Log4j.
- Apply the official patch from the Apache Software Foundation as soon as possible (Log4j Security Updates).
- Test defenses using simulated attacks to ensure controls detect and block exploitation attempts.
How can Cymulate help test defenses against Log4Shell?
Cymulate enables customers and prospects to simulate attacks against their Apache servers and infrastructure, testing whether the Log4Shell vulnerability can be exploited. This helps organizations validate their cyber defenses before threat actors do. Test now.
What modules in Cymulate address Log4Shell and similar threats?
Cymulate has added attack simulations for Log4Shell to its Immediate Threats Intelligence Module and WAF Module. Customers licensed for the Advanced Scenarios Module (formerly Purple Team) also have access to a new template simulating this attack. These modules help validate that security controls detect and prevent exploitation attempts.
How quickly did Cymulate respond to the Log4Shell vulnerability?
Cymulate responded immediately to the Log4Shell notification by ensuring the vulnerability did not exist in its own infrastructure and by adding relevant attack simulations to its platform modules for customer use.
Where can I find official information about the Log4Shell CVE?
Official details about CVE-2021-44228 are available on the MITRE website.
What is the importance of continuous security validation in preventing attacks like Log4Shell?
Continuous security validation helps organizations keep up with the constant drift in their security posture. By regularly running simulated attacks and mapping the attack surface, organizations can quickly identify and address vulnerabilities before attackers exploit them.
How fast do attackers exploit newly disclosed vulnerabilities like Log4Shell?
Attackers often begin scanning for and exploiting new vulnerabilities within hours of public disclosure, making rapid response and validation critical for organizations.
How can I test my Apache servers for Log4Shell vulnerability using Cymulate?
Cymulate customers can use the Immediate Threats Intelligence Module and WAF Module to safely simulate Log4Shell exploitation attempts against their Apache servers, validating whether their security controls detect and block the attack.
What lessons can be learned from the Log4Shell incident?
The Log4Shell incident highlights the need for proactive security, rapid patching, and continuous validation. Even third-party code can introduce critical risks, so organizations must maintain high visibility and readiness to respond to emerging threats.
How does Cymulate ensure its own platform is secure from vulnerabilities like Log4Shell?
Cymulate immediately investigates and remediates any reported vulnerabilities, ensuring that issues like Log4Shell do not exist in its cloud, agent, or infrastructure. The company follows a strict Secure Development Lifecycle (SDLC) and conducts regular third-party penetration testing.
What is the role of the Cymulate Research Lab in addressing threats like Log4Shell?
The Cymulate Research Lab continuously monitors the cyber-threat landscape, analyzes new vulnerabilities, and rapidly develops attack simulations to help customers validate their defenses against the latest threats, including Log4Shell.
How can I learn more about threat-informed defense and the MITRE ATT&CK framework?
You can learn more about threat-informed defense and operationalizing the MITRE ATT&CK framework for security validation on the Cymulate MITRE ATT&CK page.
Where can I find demos on how Cymulate validates vulnerabilities like Log4Shell?
You can view demos such as 'From Vulnerability to Validation' and 'Threat Validation Demo' on the Cymulate website, which show how Cymulate connects vulnerabilities to real attack scenarios and validates what’s exploitable. View demo.
How does Cymulate support customers during major vulnerability disclosures?
Cymulate takes immediate action by updating its platform with relevant attack simulations, ensuring its own infrastructure is secure, and providing guidance to customers on testing and remediation steps for new vulnerabilities.
What is the Immediate Threats Intelligence Module in Cymulate?
The Immediate Threats Intelligence Module is a Cymulate platform feature that allows users to simulate the latest real-world attacks, including Log4Shell, to validate their security controls and response capabilities.
How does Cymulate's Advanced Scenarios Module help with threat simulation?
The Advanced Scenarios Module (formerly Purple Team) provides templates for simulating complex attack chains, including those exploiting vulnerabilities like Log4Shell, enabling organizations to test their defenses against sophisticated threats.
What is the WAF Module in Cymulate and how does it relate to Log4Shell?
The WAF Module in Cymulate allows users to validate their Web Application Firewall's effectiveness against attacks like Log4Shell by simulating exploitation attempts and ensuring proper detection and blocking.
Features & Capabilities
What are the key capabilities of the Cymulate platform?
Cymulate offers continuous threat validation, unified Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), exposure analytics, attack path discovery, automated mitigation, AI-powered optimization, and an extensive threat library with over 100,000 attack actions updated daily. Learn more.
Does Cymulate integrate with other security technologies?
Yes, Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. See all integrations.
How easy is it to implement Cymulate?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment. Support is available via email and chat. Schedule a demo.
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and actionable insights. Testimonials highlight its ease of implementation, practical dashboards, and accessible support. For example, Raphael Ferreira, Cybersecurity Manager, said, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." Read more testimonials.
What security and compliance certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and privacy standards. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate uses encryption for data in transit (TLS 1.2+) and at rest (AES-256), hosts data in secure AWS data centers, and follows a robust security program including secure development lifecycle, vulnerability scanning, and annual third-party penetration tests. The platform is GDPR-compliant and includes mandatory 2FA, RBAC, and IP restrictions. Details here.
What is Cymulate's pricing model?
Cymulate uses a subscription-based pricing model tailored to each organization's needs. Pricing depends on the chosen package, number of assets, and scenarios required. For a personalized quote, schedule a demo.
Who is the target audience for Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. Learn more.
How does Cymulate differ from other security validation platforms?
Cymulate offers a unified platform combining BAS, CART, and exposure analytics, continuous 24/7 validation, AI-powered remediation prioritization, complete kill chain coverage, and an extensive, frequently updated threat library. Customers report measurable outcomes such as a 52% reduction in critical exposures and an 81% reduction in cyber risk. See comparisons.
What problems does Cymulate solve for security teams?
Cymulate addresses fragmented tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies in vulnerability management, and post-breach recovery challenges. See case studies.
Are there case studies showing Cymulate's effectiveness?
Yes. For example, Hertz Israel reduced cyber risk by 81% in four months, and a sustainable energy company scaled penetration testing cost-effectively with Cymulate. Read more case studies.
How does Cymulate support different security personas?
Cymulate tailors solutions for CISOs (metrics and risk prioritization), SecOps (automation and efficiency), red teams (advanced attack simulation), and vulnerability management teams (validation and prioritization). Learn more.
What is Cymulate's overarching mission and vision?
Cymulate's mission is to transform cybersecurity by enabling organizations to proactively validate defenses, identify vulnerabilities, and optimize their security posture. The vision is to foster a collaborative environment for lasting improvements in cybersecurity. About us.
Where can I find Cymulate's latest news, research, and resources?
Stay updated via the Cymulate blog, newsroom, events & webinars, and the Resource Hub.
Does Cymulate provide educational resources like a blog or glossary?
Yes, Cymulate offers a blog for threat research, a glossary for cybersecurity terms, and a Resource Hub for whitepapers, reports, and more.
Where can I find information about preventing lateral movement attacks?
Cymulate has a blog post titled 'Stopping Attackers in Their Tracks' that discusses lateral movement attacks and prevention strategies. Read the blog post.
What is Cymulate's approach to product security and compliance?
Cymulate follows a comprehensive security program with industry certifications, data encryption, secure AWS hosting, secure development practices, ongoing employee training, and GDPR compliance. Security at Cymulate.
Where can I find Cymulate's Resource Hub?
The Resource Hub is available at cymulate.com/resources/ and includes insights, thought leadership, and product information.
Where can I find a video about the AWS SSM Agent Vulnerability discovered by Cymulate?
You can watch the video AWS SSM Agent Vulnerability: Cymulate Researcher Uncovers Critical Flaw for more information.