Best Malware Detection Techniques: How to Apply Them
Malware detection is no longer about spotting a virus or two. It’s about defending against a constantly shifting array of potential threats that are smarter, faster and harder to detect than ever before. To keep pace, organizations must adopt layered detection strategies and embrace automation to reduce risk and strengthen resilience.
In this guide, we’ll break down how malware works, explore the most effective malware detection techniques and review how Cymulate can automate and enhance the process.
Key highlights:
- Malware detection is the process of monitoring systems to identify, analyze and remediate potentially malicious software.
- Manual malware detection techniques cannot keep up with the speed and complexity of modern threats.
- Combining approaches to network malware detection, such as signature-based, heuristic, behavioral, sandboxing and AI-driven detection, increases coverage.
- By testing and validating defenses with automated Breach and Attack Simulation, Cymulate ensures malware detection methods remain effective against evolving threats.
What is malware detection?
Malware detection is the process of identifying malicious software on a computer or network. Detection methods can vary greatly, but they all come down to safeguarding systems and data from cyber threats designed to disrupt, damage or gain unauthorized access.
To protect their environments, enterprises need to account for the wide range of evolving techniques attackers use to disguise harmful code. This includes:
- Analyzing structural elements of a file
- Reviewing how programs interact with system resources
- Comparing activity against known indicators of compromise
By grounding detection in both code analysis and behavioral observation, teams can distinguish normal operations from actions indicative of potential malware, strengthening their security posture.
Why is detecting malware important?
Effective network malware detection is critical, as it surfaces risk indicators early, helping security teams validate whether a threat is active and provides the context needed to determine severity and next steps. This real-time insight helps enterprises avoid:
- Data loss and breaches
- Operational disruption
- Financial and reputational damage
According to a U.S. Chamber of Commerce survey, 60% of small businesses say cybersecurity threats, including phishing attacks and ransomware, are a top concern, underscoring that detecting malware has become mission-critical. By treating the process as a continuous visibility layer rather than a one-time scan, organizations can spot abnormalities faster and reduce the window in which incidents can cause damage.
How does malware work?
Malware works by exploiting vulnerabilities in computer systems or networks to perform destructive actions. Once it gains initial access, it begins carrying out tasks that support its objective, whether that’s stealing data, disrupting operations or creating a pathway for additional threats.
Below are the four steps malware generally uses to enter systems:
Step 1: Entry point/infiltration
Malware can enter a system through email attachments, where users inadvertently download the malware disguised as legitimate files. It can also come from infected or compromised websites or spread through USB drives and other removable media containing hidden payloads. Legacy malware still relies heavily on these older delivery paths, often taking advantage of out-of-date software and unpatched systems that leave known vulnerabilities exposed.
Step 2: Execution
Once inside, malware executes its payload, which can vary by type, including data theft, which entails stealing sensitive information like passwords, credit card details, personally identifiable information (PII) and personal health information (PHI).
Other types of execution come in the form of ransomware actions, encrypting files and demanding a ransom for the decryption keys, botnet creation, like distributed denial of service (DDoS), where a threat actor turns an infected machine into a remotely controlled one. And lastly, spying, where keyloggers or webcams are used to monitor activity.
Step 3: Propagation
What makes malware so complex is that it can replicate itself and spread across systems in a worm-like behavior. This often involves lateral movement from one compromised device to another by exploiting internal network connections. It can also spread through social engineering, tricking users into sharing infected files or clicking on malicious links that extend the infection path.
Step 4: Persistence/evading detection
Any good cyber thief aims to avoid getting caught. To prevent triggering network malware detection software, measures can be taken, such as using polymorphic malware, which changes its code each time it infects a new system. There are also rootkits, which hide their presence by modifying system files and processes and finally exploiting trusted applications by disguising themselves as legitimate software to bypass security measures.
Top 8 techniques for malware detection and prevention
Modern environments face a mix of known threats and new, fast-evolving variants, which means relying on a single detection method isn’t enough. Different malware detection techniques offer varying capabilities, from catching familiar malware families to identifying unusual behavior that signals hidden activity.
The eight approaches to malware detection and prevention below outline the most reliable ways teams detect and analyze threats across endpoints, networks and cloud workloads.
1. Signature-based detection
This is a traditional network malware detection technique that involves identifying threats by comparing files to a database of known signatures. While this method is effective for known threats, it struggles with zero-day attacks, new or previously unidentified malware that does not yet have a signature.
2. Heuristic analysis
Using algorithms to analyze the behavior of programs and identifying suspicious code patterns rather than known signatures, this method of malware protection aims to detect malware based on behavior rather than known signatures. While its strength is often found in catching variants of new or modified malware, its weakness is in false positives due to the methodology.
3. Behavioral analysis
Like heuristic malware detection techniques, behavioral detection focuses on monitoring the actions of programs in real-time, looking to detect anomalous activities. This method can effectively catch malware during its execution, even if it has evaded other detection techniques. Where this method is lacking is that it requires advanced monitoring tools.
4. Sandboxing
This technique runs programs in a virtual environment to observe their behavior without risking the actual system. If a program is suspected of being malware, it can be executed in isolation, allowing analysts to study its actions without affecting the host system. While this technique is very effective, one limitation is the rapid advancements in malware that can evade sandbox environments.
5. Machine learning and AI
The popularity of machine learning and AI threat detection has forced its way into being integrated into malware detection systems by analyzing large datasets, identifying patterns, trends and anomalies. A major benefit of machine learning is that it can continuously learn from new data, improving detection capabilities over time and adapting to new threats. However, this adaptation requires extensive skills and training to keep up with the advancements.
6. Static analysis
This malware analysis technique involves analyzing code or binary of a program without actually executing it, allowing the static analysis to identify malicious behavior by studying the structure, functions and code patterns of a file. Since static analysis doesn’t require running the malware, it can be safely and early on in threat detection without risking activating harmful actions. The limitation of this method is against obfuscated or encrypted code due to potential time constraints.
7. Network traffic analysis
Network traffic validation can reveal signs of malware activity, such as unusual data exfiltration or communication with known malicious servers. By analyzing network patterns, organizations can detect malware at the network level even if it makes it past endpoint defenses. This technique, however, requires more resources, as it requires continuous monitoring and can generate large amounts of data.
8. Reputation-based detection
This technique is one that evaluates the trustworthiness of files, programs or websites based on their historical behavior, reputation or association with known threats. Instead of relying on traditional signature- or behavior-based detection, this approach uses trusted threat intelligence databases and blocks files or URLs based on their reputation scores.
Offering low overhead, real-time protection and easily preventing known malicious domains, this technique has a lot to offer. Its weaknesses include being limited to a reputation database and relying on external data.
Best practices for malware threat management
Managing escalating risks requires more than deploying a single tool. It involves building processes that leverage multiple malware detection techniques, helping teams detect issues sooner rather than later, validate suspicious activity and act quickly before threats escalate. The goal is to create a consistent approach that strengthens visibility and reduces the chance of a successful attack.
Here are five best practices for malware threat management:
- Establish behavioral baselines: Create a clear picture of normal activity so deviations stand out quickly.
Patch consistently: Close known vulnerabilities before malware can exploit them. - Monitor endpoints and networks: Track activity across devices and traffic flows to surface unusual patterns.
- Leverage threat intelligence: Stay informed on emerging malware families and attacker techniques.
- Test detection controls regularly: Validate that rules and tools still work as threats evolve.
How to choose the right malware detection tool
Selecting a tool for the detection of malware starts with understanding how threats target your environment and which capabilities will give your team the context needed to execute a response plan. A strong solution should flag indicators clearly, reduce noise and support both known malware identification and the detection of new variants.
Key considerations when evaluating malware detection tools include:
- Coverage across your endpoints, networks and cloud workloads
- Ability to detect both signature-based and behavior-based threats
- Low false positive rates to avoid overwhelming your analysts
- Integration of malware analysis techniques with your existing tools and workflows
- Support for continuous validation to ensure detection accuracy
Automate advanced malware detection with Cymulate
Imagine the time, cost, resource and potential reputational savings that your organization could have with automated malware detection implemented. That wish doesn’t have to be someday; it could be now. With the frequency, sophistication and volume of cyber threats only increasing, manual detection methods can no longer keep up with the scale and complexity of modern malware attacks.
The Cymulate Exposure Management Platform can help with the detection of malware by:
- Identifying and prioritizing exposures
- Evaluating detection techniques
- Prioritizing critical risks
With continuous exposure validation and testing, Cymulate helps ensure your security strategy remains effective and offensive against the latest threats.
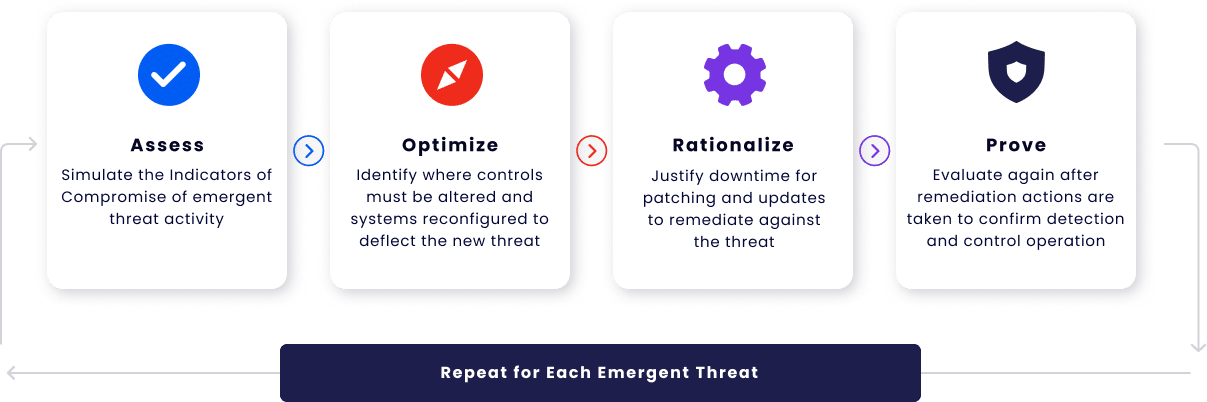
Automated malware detection is no longer a nice-to-have, but a must-have in the modern cybersecurity landscape. Automating with Cymulate allows for faster, more efficient, accurate and scalable detection to continuously ensure your detection methods remain effective against new threats. This is all possible while providing real-time visibility into exploitable vulnerabilities.
Book a demo today, and see how automating malware detection techniques with Cymulate enables efficient, accurate and scalable protection across your environment.