Frequently Asked Questions
Ransomware & Threats
What are Petya and NotPetya ransomware, and how do they work?
Petya and NotPetya are ransomware strains that encrypt Windows systems, rendering them inoperable and demanding ransom payments. Petya encrypts the master boot records of infected computers, making them unusable, while NotPetya is a variant that caused widespread disruption in 2017. Both spread through malicious attachments and exploit network protocols like SMBv1, scanning and encrypting files before displaying a ransom demand. (Source: Cymulate Blog, June 8, 2025)
How do Petya and NotPetya ransomware spread within a network?
Petya and NotPetya spread by exploiting network protocols such as SMBv1 and ports 139, 445, and 135. After a user opens a malicious attachment, the ransomware communicates with a command-and-control server, then propagates laterally within the network, encrypting files and demanding ransom. (Source: Cymulate Blog)
What is the impact of a Petya or NotPetya ransomware attack on an organization?
A successful Petya or NotPetya attack can render critical business systems unusable, encrypt valuable data, and disrupt operations. Victims face potential data loss, business interruption, reputational damage, and financial or legal consequences if ransom is not paid. (Source: Cymulate Blog)
How can organizations test their resilience against ransomware like Petya and NotPetya?
Organizations can use Cymulate’s Ransomware Resilience Assessment to simulate attacks like Petya and NotPetya, identify weak points, and receive remediation guidance. Cymulate’s platform adds new ransomware payloads daily, enabling immediate assessment against the latest threats. (Source: Cymulate Blog)
What steps does Cymulate recommend to become ransomware resilient?
Cymulate recommends continuous assessment of security controls, regular simulation of emerging ransomware threats, and prompt remediation of identified gaps. For practical steps, see the blog post 7 Essential Steps to Becoming Ransomware Resilient. (Source: Cymulate Blog)
How does Cymulate help organizations respond to new and emerging ransomware threats?
Cymulate updates its platform daily with new ransomware payloads and attack simulations, allowing organizations to assess their defenses against the latest threats and receive actionable remediation guidance. (Source: Cymulate Blog)
Where can I find more resources on ransomware resilience and validation?
You can explore Cymulate’s Resource Hub for whitepapers, blog posts, and case studies on ransomware resilience, including guides like '7 Essential Steps to Becoming Ransomware Resilient' and 'Akira Ransomware: How to Test and Validate Your Exposure'.
What is the potential impact of an email gateway flaw in the context of ransomware?
An email gateway flaw can allow ransomware to bypass security controls, leading to widespread infections if employees open malicious attachments or links. This can result in encrypted business data, operational disruption, reputational damage, and financial or legal consequences. (Source: Customer Story - Caught, But Not Contained: The Email Gateway Flaw)
Does Cymulate provide guidance on mitigating lateral movement attacks?
Yes, Cymulate offers guidance on preventing lateral movement attacks through blog posts such as 'Stopping Attackers in Their Tracks', which discusses common lateral movement techniques and mitigation strategies. (Source: Cymulate Blog)
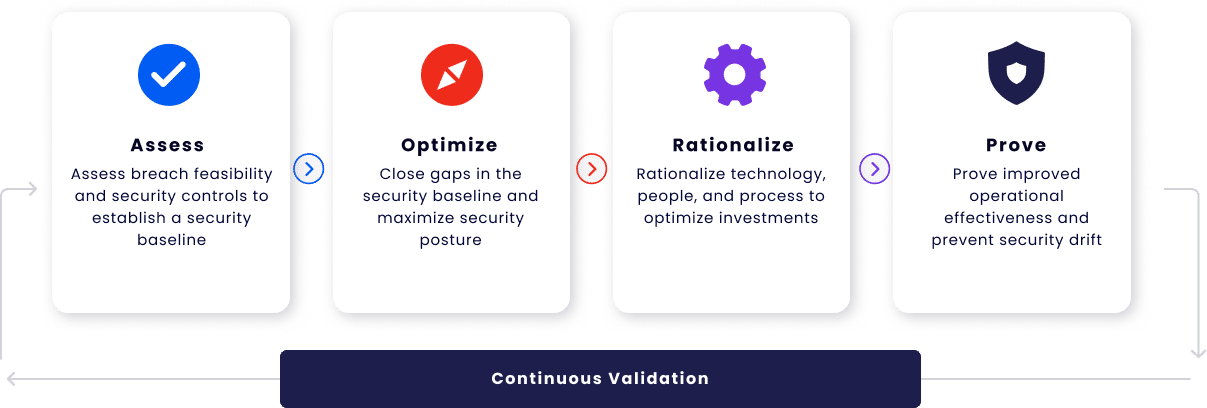
How does Cymulate’s Exposure Validation help with ransomware defense?
Cymulate Exposure Validation enables organizations to run advanced security tests, including custom attack chains, to assess their defenses against ransomware. The platform provides actionable insights and remediation guidance to close security gaps. (Source: Exposure Validation Data Sheet)
Features & Capabilities
What are the key features of Cymulate’s platform?
Cymulate’s platform offers continuous threat validation, a unified platform combining Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics, attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, ease of use, and an extensive threat library with over 100,000 attack actions updated daily. (Source: Cymulate Platform)
How does Cymulate automate ransomware and threat simulations?
Cymulate automates ransomware and threat simulations by running 24/7 attack scenarios, updating its threat library daily, and integrating with security controls to push updates for immediate prevention. This ensures organizations can continuously validate their defenses against the latest threats. (Source: Optimize Threat Resilience)
What integrations does Cymulate support?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore (network security), AWS GuardDuty (cloud security), BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a complete list, visit the Partnerships and Integrations page.
How does Cymulate’s AI-powered optimization improve security?
Cymulate uses machine learning to deliver actionable insights for prioritizing remediation efforts, helping organizations focus on high-risk vulnerabilities and optimize security controls for better threat resilience. (Source: Cymulate Platform)
What is Cymulate’s approach to exposure prioritization?
Cymulate validates exploitability and ranks exposures based on prevention and detection capabilities, business context, and threat intelligence, enabling organizations to focus on the most critical vulnerabilities. (Source: Exposure Prioritization)
How easy is Cymulate to implement and use?
Cymulate is designed for quick, agentless deployment with no need for additional hardware or complex configurations. Customers report that the platform is intuitive, easy to navigate, and provides actionable insights with just a few clicks. (Source: Customer Testimonials, Schedule a Demo)
What educational resources does Cymulate provide?
Cymulate offers a Resource Hub with whitepapers, blog posts, webinars, and a glossary of cybersecurity terms. These resources help users stay informed about the latest threats, research, and best practices. (Source: Resource Hub)
How does Cymulate support continuous improvement in security?
Cymulate updates its SaaS platform every two weeks with new features, such as AI-powered SIEM rule mapping and advanced exposure prioritization, ensuring customers always have access to the latest capabilities. (Source: About Us)
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, red teams, and vulnerability management teams in organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. (Source: CISO/CIO, SecOps, Red Teaming, Vulnerability Management)
What measurable outcomes have customers achieved with Cymulate?
Customers have reported up to an 81% reduction in cyber risk within four months, a 52% reduction in critical exposures, a 60% increase in team efficiency, and a 20-point improvement in threat prevention. (Source: Hertz Israel Case Study)
How does Cymulate help organizations with fragmented security tools?
Cymulate integrates exposure data and automates validation, providing a unified view of the security posture and closing gaps caused by disconnected tools. (Source: EM Platform Message Guide)
How does Cymulate address resource constraints in security teams?
Cymulate automates manual processes, improves operational efficiency, and enables teams to focus on strategic initiatives rather than repetitive tasks. (Source: EM Platform Message Guide)
How does Cymulate help prioritize risk and exposures?
Cymulate validates and ranks exposures based on exploitability, business context, and threat intelligence, helping teams focus on the most urgent vulnerabilities. (Source: EM Platform Message Guide)
How does Cymulate support cloud and hybrid environments?
Cymulate secures hybrid and cloud infrastructures through automated compliance and regulatory testing, increasing visibility and improving detection and response capabilities. (Source: Nemours Children's Health Case Study)
How does Cymulate help with communication barriers for CISOs?
Cymulate delivers quantifiable metrics and insights tailored to different roles, enabling CISOs to justify investments and communicate risks effectively to stakeholders. (Source: CISO/CIO)
How does Cymulate improve vulnerability management?
Cymulate automates in-house validation between penetration tests and prioritizes vulnerabilities, improving operational efficiency and reducing risk. (Source: Globeleq Case Study)
How does Cymulate help organizations recover after a breach?
Cymulate enhances visibility and detection capabilities, replacing manual processes and ensuring faster recovery after a breach. (Source: Nedbank Case Study)
Security & Compliance
What security and compliance certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and privacy standards. (Source: Security at Cymulate)
How does Cymulate ensure data security and privacy?
Cymulate uses encryption for data in transit (TLS 1.2+) and at rest (AES-256), hosts data in secure AWS data centers, and follows a strict Secure Development Lifecycle (SDLC) with continuous vulnerability scanning and third-party penetration tests. (Source: Security at Cymulate)
Is Cymulate GDPR compliant?
Yes, Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO), ensuring GDPR compliance. (Source: Security at Cymulate)
What product security features does Cymulate offer?
Cymulate’s platform includes mandatory 2-Factor Authentication (2FA), Role-Based Access Controls (RBAC), IP address restrictions, and TLS encryption for its Help Center. (Source: Security at Cymulate)
Pricing & Plans
What is Cymulate’s pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization’s requirements. Pricing depends on the chosen package, number of assets, and scenarios selected. For a detailed quote, you can schedule a demo with the Cymulate team. (Source: Internal Manual)
Company & Customer Proof
What is Cymulate’s mission and vision?
Cymulate’s mission is to transform cybersecurity practices by enabling organizations to proactively validate their defenses, identify vulnerabilities, and optimize their security posture. The vision is to create a collaborative environment for lasting improvements in cybersecurity strategies. (Source: About Us)
What feedback have customers given about Cymulate’s ease of use?
Customers consistently praise Cymulate for its intuitive interface, ease of implementation, and actionable insights. Testimonials highlight the platform’s user-friendly dashboard, immediate value, and accessible support. (Source: Customer Quotes)
Where can I find Cymulate’s latest news, research, and events?
You can stay updated with Cymulate’s latest news, research, and events by visiting the Blog, Newsroom, and Events & Webinars pages.
Where can I find a central hub for Cymulate’s resources and product information?
All of Cymulate’s resources, including insights, thought leadership, and product information, are available in the Resource Hub.