Security Segmentation Validation in the Banking Industry
Banking firms have cybersecurity needs that blend traditional financial concerns with retail concerns. This leads to unique cybersecurity issues as IT and Security teams attempt to determine how an attacker could leverage well-known infiltration points (phishing, USB devices, etc.) with industry-specific entry areas such as ATM’s.
Lateral Movement Simulation enables thorough testing of security controls and segmentation policies that are designed to prevent network propagation of a threat actor between secured network zones. Let’s look at the most common Lateral Movement threat methods relevant to the banking industry.
Attack Spread Beyond the DMZ
A Demilitarized Zone (DMZ) is a vulnerable point in the security controls of any organization since by nature, it bridges the greater Internet and internal platforms that hold and control company confidential and sensitive data.
Web servers and services located within the DMZ must be accessible to the general public and 3rd party entities. DMZ systems must often communicate with protected resources to facilitate business processes. This combination makes the DMZ a primary target of threat actors, as finding a method to enter a DMZ is much easier than attempting to directly infiltrate more protected networks and systems within the security perimeter.
Communications between systems in the DMZ and internal systems are restricted through strict security controls and policies, combined with physical networking segregation wherever possible. Due to the nature of a DMZ; however, it is possible for both purposeful and accidental connectivity to exist between the DMZ and sensitive network segments - especially when changes to the overall business platforms, networking hardware, and application systems occur as a normal result of upgrades and business development.
Additionally, DMZ and related inter-networking systems can suffer from vulnerabilities in operating systems and software platforms, creating potential security gaps even when all the operational controls and policies are perfectly enforced.
Attacks Spreading from User Systems
Through social engineering or brute force, an attacker may gain a foothold on one or more user devices within the general user network of the bank’s central operations systems. Through these compromised devices, an attacker can attempt to intercept credential sets and survey the overall environment to determine the location of valuable resources. Moving laterally with this obtained information, the attacker can attempt to compromise Domain Controllers or attempt a business email compromise to gain further access to secure systems and data.
While user networks are generally separated from critical infrastructure in banking environments, having the right credentials or control over a Domain Controller can allow an attacker to overcome this segmentation by masquerading as a legitimate user with access to additional subnets and systems. A business email compromise can pave the way for attackers to instruct technical teams to grant them additional access. Through these techniques, an attacker can compromise DMZ systems, ATM networks, and other direct platforms to create disruptions or steal funds.
From a Branch to the Main Network
Attackers are aware that critical data systems and facilities will have significantly higher security protocols and monitoring than some branch operations. This makes branch operations a regular target for many threat actors. By moving laterally from an initial compromise of one branch system, an attacker can attempt to compromise more critical systems that manage intercommunication between the branch and centralized data processing or operations locations.
If the attacker is able to gain sufficient credentials or perform a business email compromise of the correct branch operations, they can masquerade as a legitimate employee or data system to piggyback their way into the main data systems - moving laterally to further compromise operations and perform financial or data theft.
ATM Networks are Another Key Target
As many ATMs, especially older models, are designed around embedded operating systems that may not receive updates and upgrades as often as other systems, attackers view these machines as a primary starting point for Lateral Movement.
An ATM is both a data system and a physical appliance - and both are directly accessible to the public. While well-fortified and closely monitored, if an attacker can compromise an ATM physically or digitally; the now compromised platform becomes a starting point for Lateral Movement into the ATM’s back-end systems.
From here, an attacker can propagate control into additional secured systems, or simply interact with the ATM network to produce the desired goal directly - such as theft of funds or alteration of transactions.
Using Security Systems to Attack
One often-overlooked system that threat actors have begun to target more directly is security cameras. Cameras are networked over Internet Protocol (IP) links, and therefore have connectivity to other networked resources in the same way as DMZ servers and other public-facing platforms.
Unfortunately, the Operating Systems of security cameras are significantly more simplistic - and therefore more difficult to secure than servers and ATMs. Techniques used to compromise Internet of Things (IoT) devices can be utilized to compromise the cameras themselves, allowing an attacker to move laterally into security monitoring network segments.
From here, and by masquerading as command and control traffic for the camera network - an attacker can move throughout additional networks and gain more sensitive credentials to perpetrate an attack on more significant data systems.
If the attacker does not render the camera offline, their activity may go undetected by network security tools as the events and logs provided by the cameras themselves (as opposed to their control platforms) is limited.
Difficulties in Preventing Lateral Movement Attacks
Network classification and segmentation of users and data based on trust is a best practice for building a secure network architecture. Preventing lateral movement between differently classified networks is a critical issue for banking organizations to address; though with more potential points of initial compromise it can be a difficult issue to address completely.
Due to the significant amount of systems that are either accessible to the public (websites, ATMs, etc.) or that interact with public and 3rd party systems (data platforms, wire transfer systems, etc.), there is a wealth of targets for attackers to begin infiltration from.
Once a foothold is established, attackers can move within an organization by masquerading as legitimate users and systems to gain higher privileges until they can achieve their goal. With so many different network segments managed by many different tools, platforms, and users; it can be easy to accidentally weaken critical security segmentation between them; allowing an avenue for Lateral Movement to span across networks and systems.
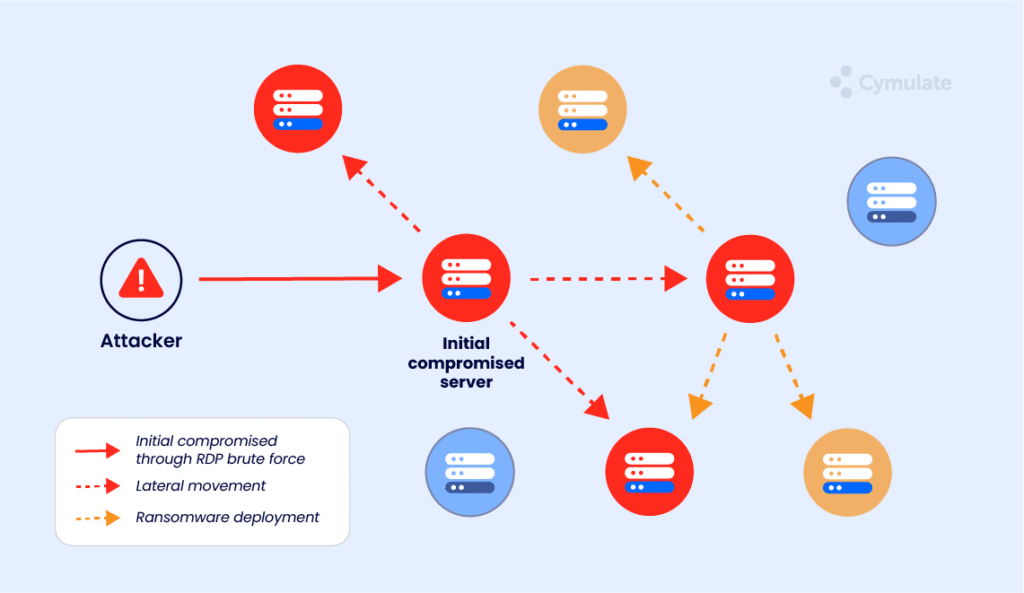
Cymulate’s Lateral Movement Test Vector Simulation
Lateral Movement Simulation (LMS) can show the bank when and where segmentation and access control weaknesses exist. Performing LMS at different times during production operations and across different network segments allows the bank to gain a much better picture of avenues of attack, and work to close those avenues without disruption of business operations.
Cymulate’s Lateral Movement vector challenges internal networks against different techniques and methods used by attackers to gain access, escalate privileges and control additional systems on a network, following the initial compromise of a single system.