Frequently Asked Questions
Product Information & Kubernetes Detection
What is the importance of validating detection in Kubernetes environments?
Validating detection in Kubernetes environments is crucial because Kubernetes is highly dynamic and complex, making it susceptible to security risks such as unauthorized access, privilege escalation, misconfiguration, and insufficient logging. Without proper validation, these risks can go unnoticed, potentially leading to data breaches or loss of control over your clusters.
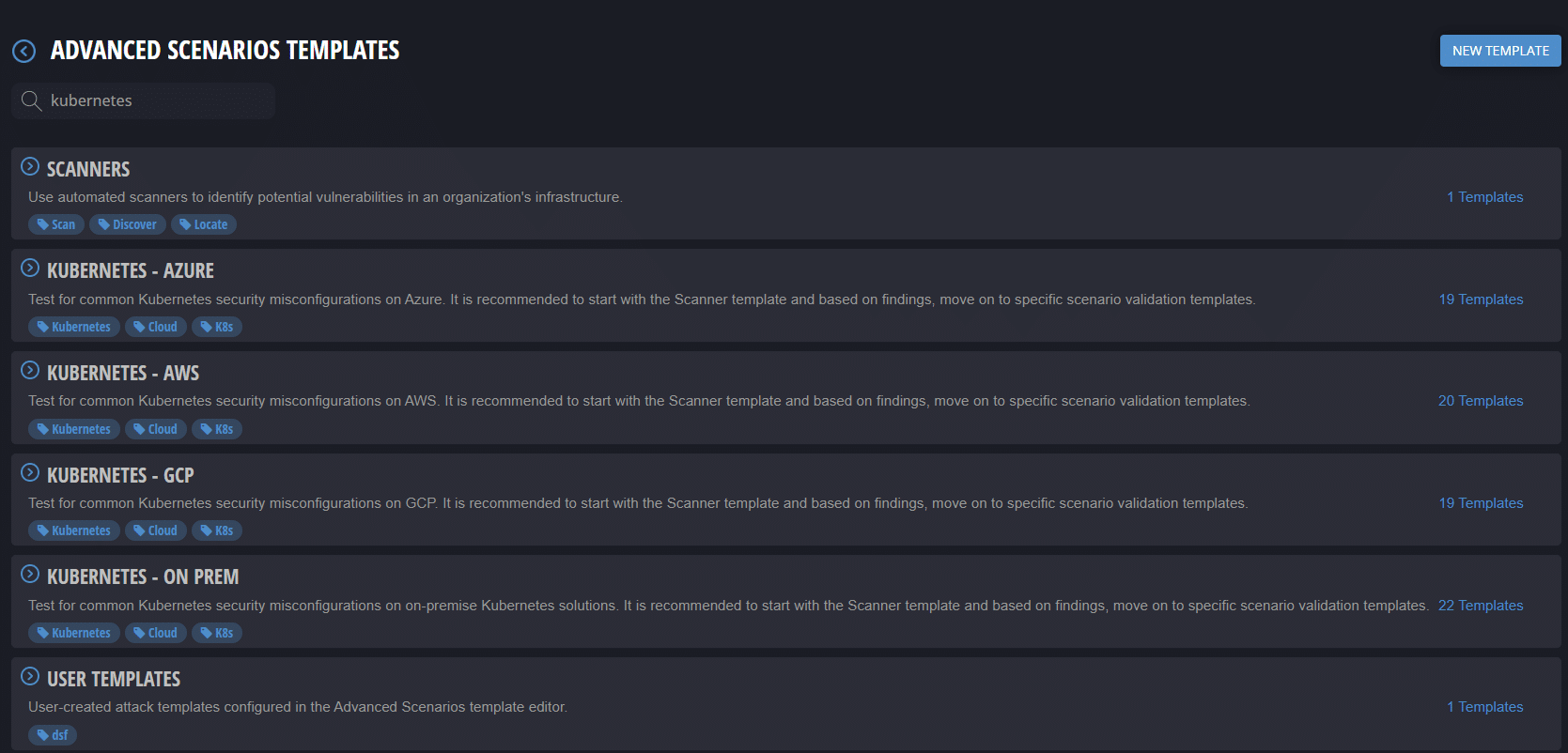
What are Cymulate queries for Kubernetes?
Cymulate queries are specialized tools designed to validate the detection of executions in Advanced Scenarios Kubernetes assessments. They help ensure that your security products are functioning as intended and can detect potential security threats within your Kubernetes clusters, whether in cloud environments like AWS, Azure, GCP, or on-premises.
What risks do organizations face if they do not validate detection in Kubernetes?
Organizations that do not validate detection in Kubernetes face risks such as unauthorized access to sensitive services (like Kubelet), privilege escalation, unnoticed misconfigurations, and insufficient logging and monitoring. These gaps can allow attackers to exploit vulnerabilities and remain undetected within the environment.
How do Cymulate queries help secure Kubernetes environments?
Cymulate queries help secure Kubernetes environments by validating that security controls and SIEM systems are detecting critical execution events. This ensures that monitoring and logging mechanisms are working, and that potential threats are identified and addressed promptly.
What are some examples of Cymulate queries for AWS Kubernetes environments?
Examples of Cymulate queries for AWS Kubernetes environments include:
- Kubernetes - Anonymous Access to Kubelet Service → AWS GuardDuty - Anonymous Access to Kubelet Service
- Kubernetes - Host IPC Privilege → AWS GuardDuty - Kubernetes Host IPC Privilege
- Kubernetes - Writable Host Path Mount → AWS GuardDuty - Writable Host Path Mount
These queries help ensure your AWS environment is protected against Kubernetes-related vulnerabilities.
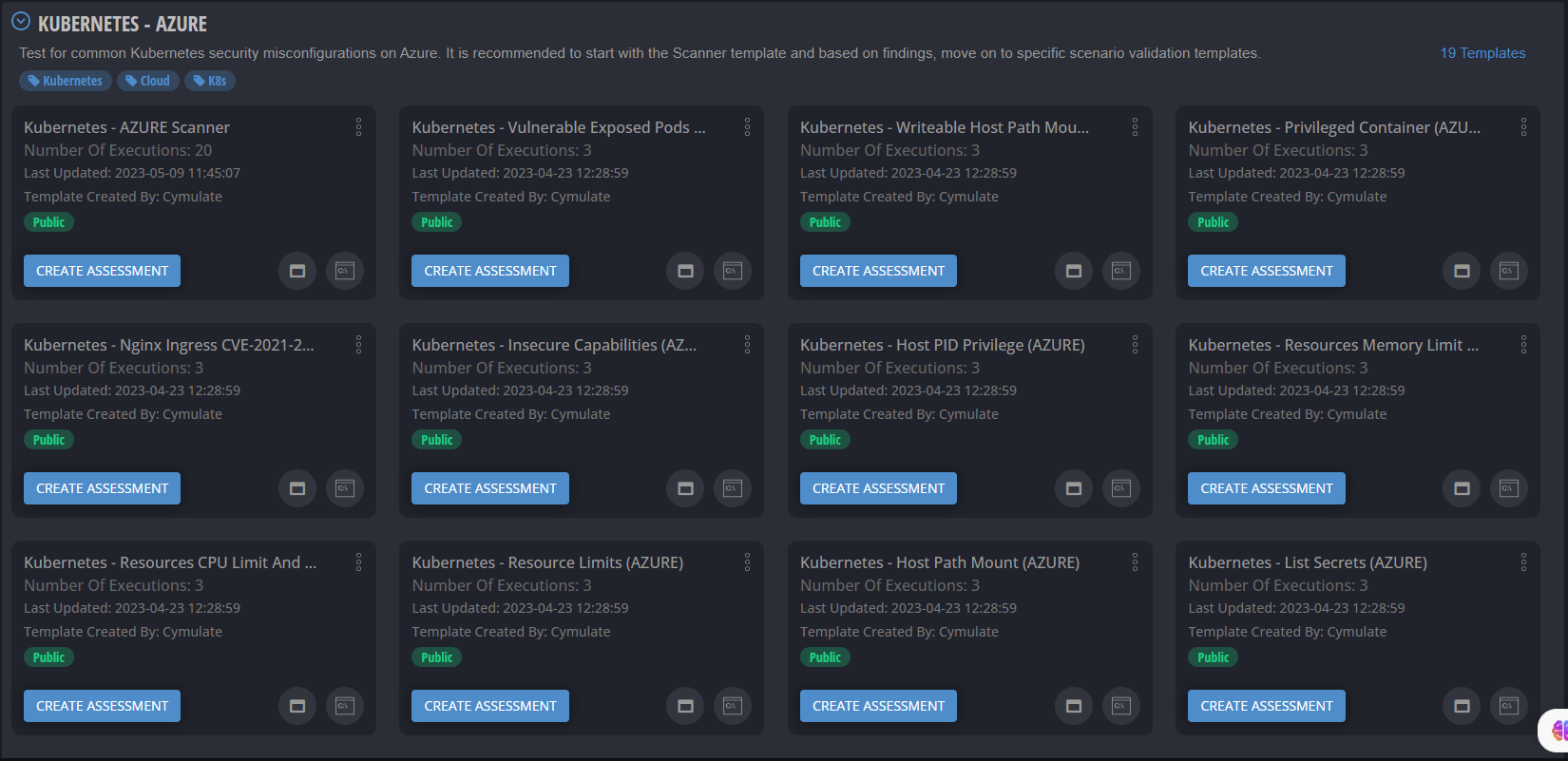
What are some examples of Cymulate queries for Azure Kubernetes environments?
Examples of Cymulate queries for Azure Kubernetes environments include:
- Kubernetes - Host IPC Privilege → Azure Microsoft Cloud Defender - Kubernetes - Privileged container detected
- Kubernetes - Writable Host Path Mount → Azure Microsoft Cloud Defender - Kubernetes - Writable Host Path Mount
These queries help validate that your Azure environment is secure and that executions are being detected by your SIEM system.
What cloud security products must be activated to use Cymulate queries in AWS?
To use Cymulate’s AWS Kubernetes queries, you must activate Amazon’s native cloud security products such as CloudTrail, CloudWatch, or GuardDuty in your AWS testing account and connect your Kubernetes cluster with these services. This ensures proper monitoring and logging for query validation.
What cloud security products must be activated to use Cymulate queries in Azure?
To use Cymulate’s Azure Kubernetes queries, you need to activate at least one of Microsoft’s native cloud security products, such as Log Analytics or Microsoft Defender for Cloud, in your Azure testing account and connect your Kubernetes cluster with these services.
How does validating detection in Kubernetes support proactive security?
Validating detection in Kubernetes supports proactive security by identifying and mitigating risks before they can be exploited. It ensures that monitoring systems are effective, helps meet regulatory requirements, and provides confidence that your Kubernetes clusters are being properly protected.
How does Cymulate Exposure Validation make advanced security testing easier?
Cymulate Exposure Validation centralizes advanced security testing, allowing users to build custom attack chains and validate exposures in one place. This streamlines the process and makes it more accessible for security teams to assess and improve their defenses.
What expertise does the Cymulate Research Lab bring to Kubernetes security?
The Cymulate Research Lab consists of experienced researchers with backgrounds in private security, military, and intelligence. They continuously analyze the cyber-threat landscape, providing in-depth visibility into current threats and the actors behind them, which informs Cymulate’s Kubernetes security solutions.
Where can I find more resources on validating detection in Kubernetes?
You can find more resources, including demos and whitepapers, on the Cymulate website. Featured resources include demos like 'From Vulnerability to Validation' and 'Threat Validation Demo,' which show how Cymulate connects vulnerabilities to real attack scenarios and validates protection against new threats. Visit the Resource Hub for more.
How does Cymulate help with misconfiguration risks in Kubernetes?
Cymulate helps address misconfiguration risks in Kubernetes by validating detection and ensuring that misconfigurations do not go unnoticed. This proactive approach helps organizations identify and remediate configuration issues before they can be exploited by attackers.
How does Cymulate support compliance in Kubernetes environments?
By validating detection and ensuring proper monitoring and logging, Cymulate helps organizations meet regulatory requirements for Kubernetes environments. This proactive validation demonstrates that security controls are in place and functioning as required by compliance standards.
What is the role of SIEM integration in Cymulate Kubernetes queries?
SIEM integration is essential for Cymulate Kubernetes queries because it allows the platform to validate that security events and executions are being detected and logged. This ensures that your monitoring infrastructure is effective and that threats are not missed.
How does Cymulate help organizations detect privilege escalation in Kubernetes?
Cymulate provides queries that specifically test for privilege escalation scenarios, such as 'Kubernetes - Host IPC Privilege.' By validating that these events are detected, organizations can ensure their security controls are effective against privilege escalation attacks.
How does Cymulate address insufficient logging and monitoring in Kubernetes?
Cymulate ensures that logging and monitoring are sufficient by validating that all relevant security events are detected and recorded. This helps organizations identify gaps in their monitoring setup and take corrective action before attackers can exploit them.
How does Cymulate help organizations detect anonymous access in Kubernetes?
Cymulate provides queries such as 'Kubernetes - Anonymous Access to Kubelet Service' to test whether unauthorized access attempts are detected by your security controls. This helps ensure that only authorized users can access sensitive Kubernetes services.
How does Cymulate validate writable host path mounts in Kubernetes?
Cymulate includes queries like 'Kubernetes - Writable Host Path Mount' to test whether your security controls can detect when a container is granted write access to host paths, which is a common attack vector in Kubernetes environments.
How does Cymulate support detection engineering in Kubernetes?
Cymulate supports detection engineering by enabling security teams to build, tune, and test SIEM, EDR, and XDR rules for Kubernetes environments. This helps improve mean time to detect and ensures that detection rules are effective against real-world attack scenarios.
Features & Capabilities
What features does Cymulate offer for Kubernetes security validation?
Cymulate offers features such as continuous threat validation, automated attack simulations, exposure validation, and integration with cloud-native security products (AWS GuardDuty, Azure Defender, etc.) to ensure Kubernetes environments are secure and compliant.
Does Cymulate support integration with other security tools?
Yes, Cymulate integrates with a wide range of security technologies, including AWS GuardDuty, Azure Defender, CrowdStrike Falcon, SentinelOne, and more. For a complete list, visit our Partnerships and Integrations page.
How does Cymulate validate detection rules?
You can validate detection rules by conducting simulations of the techniques you want to detect and confirming whether the rules trigger the expected alerts. Cymulate automates this process, making it faster and more reliable than manual validation.
What compliance certifications does Cymulate hold?
Cymulate holds several key security and compliance certifications, including SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1. These certifications demonstrate Cymulate’s commitment to industry-leading best practices. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption for data in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and compliance with GDPR and other privacy standards. The platform also includes 2FA, RBAC, and IP address restrictions.
How easy is it to implement Cymulate for Kubernetes security validation?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately after deployment.
What support resources are available for Cymulate users?
Cymulate offers comprehensive support, including email and chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers and guidance. Visit the Resource Hub for more information.
What feedback have customers given about Cymulate’s ease of use?
Customers consistently praise Cymulate for its intuitive interface and ease of use. For example, Raphael Ferreira, Cybersecurity Manager, said, “Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture.” Read more testimonials.
How does Cymulate help organizations prioritize vulnerabilities in Kubernetes?
Cymulate validates exploitability and ranks exposures based on prevention and detection capabilities, business context, and threat intelligence, helping organizations focus on the most critical vulnerabilities in their Kubernetes environments.
How does Cymulate support collaboration between security teams?
Cymulate enables collaboration between SecOps, Red Teams, and Vulnerability Management teams by providing a unified platform for exposure validation, threat simulation, and actionable insights, ensuring a coordinated approach to Kubernetes security.
What is Cymulate’s pricing model for Kubernetes security validation?
Cymulate operates on a subscription-based pricing model tailored to each organization’s requirements, including the chosen package, number of assets, and scenarios. For a detailed quote, schedule a demo with the Cymulate team.
Who can benefit from using Cymulate for Kubernetes security validation?
Cymulate is designed for CISOs, security leaders, SecOps teams, Red Teams, and Vulnerability Management teams in organizations of all sizes and industries, including finance, healthcare, retail, and more. It is especially valuable for organizations adopting cloud-native and containerized environments.
How does Cymulate compare to other security validation platforms for Kubernetes?
Cymulate stands out by offering a unified platform that integrates Breach and Attack Simulation, Continuous Automated Red Teaming, and Exposure Analytics. It provides continuous, automated attack simulations, AI-powered optimization, and the most advanced library of attack actions, updated daily. Learn more at Cymulate vs Competitors.
What measurable outcomes have customers achieved with Cymulate?
Customers have reported outcomes such as an 81% reduction in cyber risk within four months (Hertz Israel), a 52% reduction in critical exposures, and a 60% increase in team efficiency. See more case studies at Cymulate Customers.
Where can I find Cymulate’s blog, news, and events?
Stay updated with Cymulate’s latest research, news, and events by visiting the Blog, Newsroom, and Events & Webinars pages.