Managing Your Digital Footprint
We generate a massive amount of data every day. By 2025, the global datasphere is projected to reach a staggering 175 zettabytes—enough data to fill a stack of Blu-ray discs reaching the moon 23 times! Much of this data is our digital footprint—the trail we leave behind as we interact online. With cyber threats on the rise and data breaches becoming increasingly common, it's crucial to understand and manage your digital footprint to protect your privacy and security.
What is a Digital Footprint?
A digital footprint is the trail of data you leave behind when you use the internet, alongside your digital shadow - information others create and share about you. Your digital footprint includes everything from the websites you visit and the emails you send to the information you submit online, such as social media posts, comments, and reviews. Your digital shadow extends this through tags, mentions, and photos others post about you, creating a broader online presence beyond your direct control.
For organizations, a vast digital footprint can expose sensitive information and increase the risk of cyberattacks. Security professionals must manage not only their organization's direct online presence but also its digital shadow - the content created by employees, customers, and third parties that shapes the organization's digital identity.
Personal and organizational digital footprints are distinct but they can also overlap. For example, an employee's social media activity can reflect on the organization's reputation, especially if they are publicly identified as an employee. Similarly, a data breach at an organization can directly impact the individuals whose data is compromised.
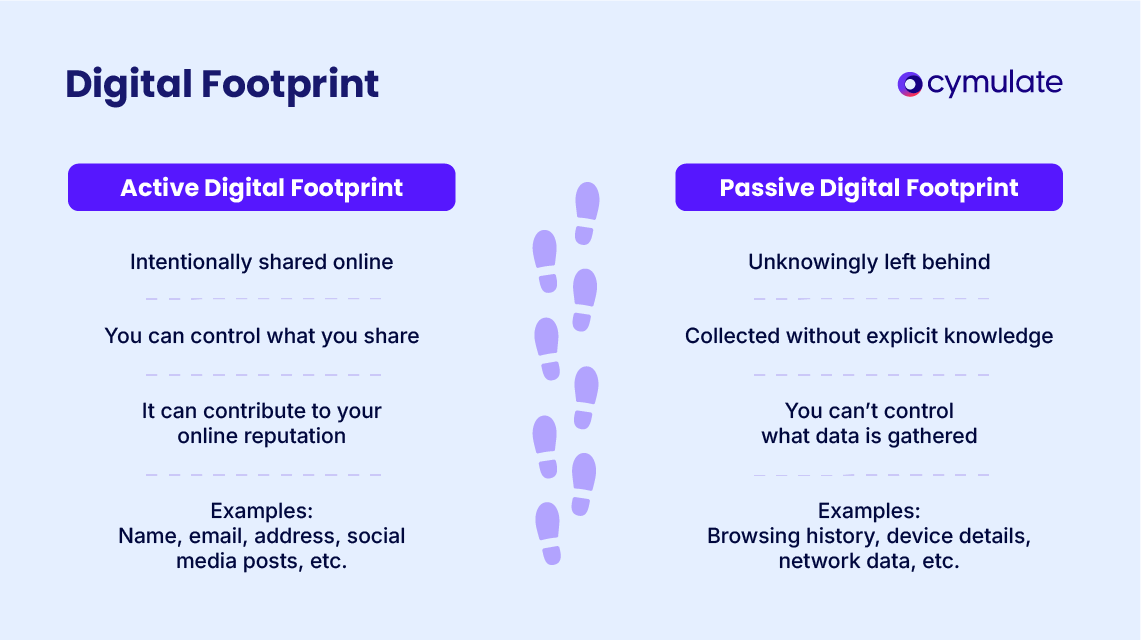
Active and Passive Footprints
There are two main types of digital footprints: active and passive. Active digital footprints encompass the data you intentionally share online. This can be social media posts, likes, comments, shares. It can also be blog posts, online reviews, or emails. If you were the one creating and sharing this information, it's active.
In contrast, passive digital footprints are the data collected about you without your explicit consent. It's the information you don't necessarily intend to share, even if you're aware some entity is collecting it. This includes data like browsing history, search queries, IP address, location data, and how many times you've visited a site.
Who Can See Your Digital Footprint?
Once the information is out there, different entities will want to glean information from it.
- Employers, colleges and landlords (cyber-vetting): Potential employers often use social media and search engines to screen candidates, and this is true for colleges and landlords too. A controversial tweet or inappropriate photo could harm your job prospects.
- Advertisers: Companies track your online activity to target you with personalized ads. This can be helpful, like seeing ads for products you're interested in, but it can also be invasive. Many people report talking to a friend in person about a product and then seeing ads for that product in the following days. While this practice hasn't been confirmed (that our phones are "listening" to us), it's clear that companies are collecting a vast amount of data about our online behavior and using it to target us with ads.
- Cybercriminals: Hackers can use your digital footprint to steal your identity, financial information, or other sensitive data. For example, connecting to a public Wi-Fi network without using a VPN can leave your device vulnerable to attacks, allowing hackers to intercept your internet traffic and potentially steal your personal information.
- Governments: Governments may monitor online activity for national security purposes. In some cases, this can lead to surveillance or censorship, although this scenario is less likely than the others.
Who Might Want to Look Into It?
Marketers actively mine individual digital footprints to create targeted advertising campaigns. They can use any information they have to segment you based on things like demographics, interests and browsing history.
For example, if you frequently search for fitness products, you might start seeing ads for gym memberships or protein supplements. This can help you find good deals, but it can also have more nefarious consequences too. A famous example of this is when Target was able to predict that a teenage girl was pregnant before her parents knew, based on her shopping habits.
Identity thieves and cybercriminals scan social media posts, public records, and data breaches to gather personal information for phishing attacks and fraud. For example, they might be able to breach your security questions like "Name of first pet" or "The street you grew up on" based on what you share online. Data brokers make this practice even more worrying. Today, it's not just individual scammers mining for information but entire cybercriminal networks composing databases of information on individuals and selling it on the dark web.
Organizations face scrutiny from a different set of observers. Competitors systematically analyze public digital footprints to gather business intelligence, monitoring everything from employee movement on LinkedIn to customer sentiment on review sites. Threat actors conduct extensive reconnaissance of organizational digital footprints, searching for vulnerabilities in public-facing infrastructure, exposed credentials, and potential attack vectors. They use this information to plan sophisticated cyber attacks, making every piece of exposed digital information a potential security risk.
The Ramifications of a Digital Footprint
For private individuals, there are significant risks associated with your digital footprint. Your personal information can be misused by advertisers and cybercriminals invading your privacy.
For organizations, a large digital footprint can pose significant risks. Intellectual property theft, like the theft of trade secrets or proprietary software, can lead to loss of competitive advantage and revenue.
Breaches of sensitive customer or employee data, like social security numbers, financial information, or health records, can result in financial loss, reputational damage, and legal consequences. Non-compliance with data protection regulations like GDPR and CCPA can lead to hefty fines. Additionally, a larger digital footprint increases the attack surface for threat actors, making organizations more vulnerable to cyberattacks, such as ransomware, phishing, and DDoS attacks.
Tools and Techniques to Manage Digital Footprints
Organizations can employ many tools and techniques to actively manage their digital footprint. Open-source intelligence (OSINT) tools are particularly useful here. Tools like Shodan, Maltego, and Recon-ng, can gather information from publicly available sources to identify vulnerabilities, track cyber threats, and monitor brand reputation.
And other best practices exist, too:
- Adopt a Zero-
- Implement network segmentation: Networks can be divided into smaller, isolated segments to minimize the impact of potential breaches.
- Conduct regular security audits: Regular security audits are essential to identify vulnerabilities and misconfigurations within systems and networks, ensuring a proactive approach to mitigating potential risks. While traditional tools can automate vulnerability scanning and penetration testing, Cymulate takes it a step further by providing continuous security validation. With Cymulate, organizations can simulate real-world attacks, validate their security controls, and gain actionable insights to strengthen their defenses effectively.
- Adhere to cybersecurity best practices: Organizations can follow industry-standard best practices, like strong password policies, regular software updates, and employee training, to reduce the risk of cyberattacks.
Do You Need to Remove Your Digital Footprint?
You should consider removing your digital footprint after significant events like identity theft or major data breaches. You can't turn back the clock, but you can limit the chances of it happening again in the future.
Organizations may need to remove or reduce their digital footprint during significant transitions, like retiring legacy systems or undergoing mergers and acquisitions. These periods can be particularly vulnerable to cyberattacks, as attackers may exploit instability and confusion to launch targeted attacks. By taking proactive steps to manage their digital footprint, organizations can mitigate risks and ensure a smooth transition.
Taking proactive measures to reduce or remove your digital footprint can help minimize exposure to potential cyber threats and enhance your privacy:
- Clear browser data: Regularly clear your browser's cookies, cache, and browsing history.
- Limit social media sharing: Be mindful of the information you share on social media platforms. Adjust privacy settings to limit visibility.
- Use privacy-focused browsers: Consider using privacy-focused browsers like Brave or Firefox with privacy extensions.
- Use data erasure services: Services like Optery and DeleteMe can help you remove your personal information from search engine results and other online platforms.
For organizations, removing or reducing your digital footprint starts with prioritizing digital hygiene and secure deletion policies:
- De-indexing sensitive data: Implement techniques to de-index sensitive data from search engine results, reducing its visibility.
- Automated security validation tools: Employ automated tools to continuously monitor and validate security configurations, identify vulnerabilities, and mitigate risks.
- Endpoint security measures: Implement strong endpoint security measures, including antivirus software, firewalls, and intrusion detection systems, to protect devices and data.

