Digital Operational Resilience Act (DORA)
What is the Digital Operational Resilience Act?
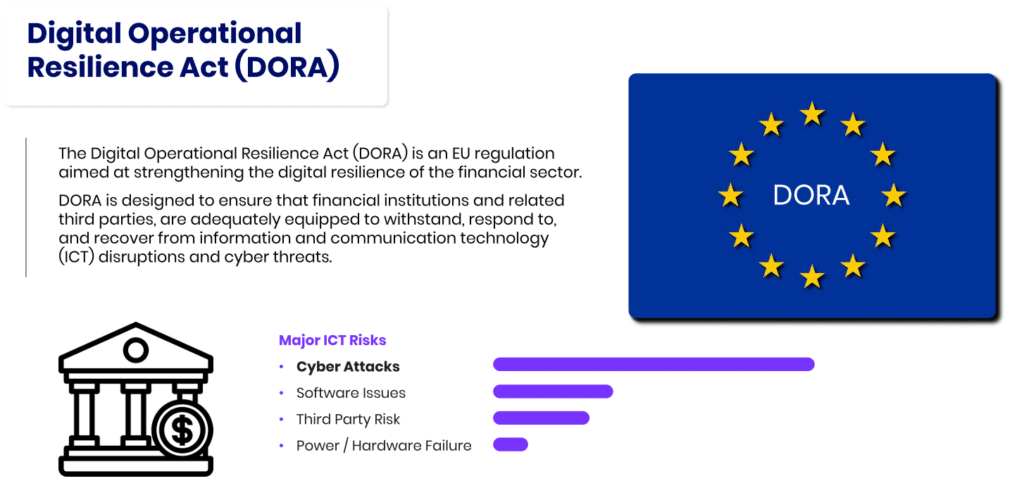
The European Union (EU) has changed the regulatory world before with GDPR, so it comes as no surprise that in November of 2022 they adopted the Digital Operational Resilience Act (DORA) as part of its broader Digital Finance Strategy. This piece of legislation is aimed directly at protecting financial institutions that may find themselves vulnerable. Financial entities have until January 17, 2025, to be in compliance with DORA before enforcement begins.
DORA’s focus is financial entities, such as banks, insurance companies and investment firms. The regulation is intended to ensure that these entities are protected and can respond quickly and with flexibility to the wide range of disruptions and cyber threats that often come their way. These areas of disruptors are called ICT or Information and Communication Technology. As part of a larger effort in the EU to strengthen its overall financial security posture, DORA’s key objectives include the following:
- Financial institutions will now have a strengthened risk management policy in place as well as comprehensive risk management frameworks to address ICT-related risks. This could include ensuring that an organization’s IT system and networks are able to withstand a disruption or cyber threat while remaining secure.
- In the event of a potential threat, organizations must be able to report incidents in a timely and effective manner. It is critical that businesses establish incident reporting procedures related to significant ICT-related incidents to regulators.
- Managing third-party service providers can pose their set of risks. This is why DORA imposes third-party risk management requirements on financial institutions to help manage any risks associated, especially those providing critical IT services.
- In order to ensure that systems and teams are at the ready to handle an ICT event at any given time, operational resilience testing is required.
- It is crucial that institutions have the internal governance and oversight structures in place to manage and oversee ICT risks daily.
Why does DORA matter to global organizations?
With financial institutions being one of several backbone industries in the world, if and when an institution was heavily disrupted or under cyber attack, the results could be financially and operationally globally catastrophic. For global businesses operating within the EU or with EU-based clients, DORA represents a crucial regulatory compliance framework that must be adhered to. Compliance to DORA ensures that these businesses have all met stringent standards for digital resilience and will avoid any potential fines or sanctions for non-compliance.
Due to these same stringent policies, DORA reinforces a thorough ICT risk management criterion, which remains critical for safeguarding against disruptions and cyber threats. By enforcing enhanced security, a financial institution can strengthen its cybersecurity posture, protect sensitive data and ensure business continuity.
For global institutions that must adhere to DORA, this will give a significant competitive advantage in the marketplace. By demonstrating that a financial institution can be compliant with rigorous standards such as DORA, it helps set a business apart from its competitors both in reputation and in best business practices that it takes digital security seriously.
Many global financial institutions work with third-parties for a variety of services. DORA’s third-party risk management requirements ensure that effective oversight of third-party providers remains a strength and another competitive advantage to clients rather than a vulnerability.
What are DORA’S Compliance Requirements?
- ICT Risk Management Framework: Financial institutions must implement comprehensive frameworks for management ICT risks, including: identifying, assessing and mitigating risks associated with their information and communication systems.
- Incident Reporting: Entities are required to report significant ICT-related incidents to their national competent authorities (NCAs) within strict deadlines. This includes providing details about the incident, its impact and remediation steps.
- Operational Resilience Testing: Regular testing of the ICT systems is mandatory, including conducting vulnerability assessments, penetration testing and stress testing to ensure that systems can uphold to disruptions and attacks.
- Business Continuity: Businesses must have business continuity plans in place to ensure that critical functions can continue operating or be quickly restored in the event of an ICT disruption. This includes backup systems, disaster recovery plans and continuity steps and employee training on all.
- Cross-Border Cooperation: For institutions operating across different EU member states, there must be cooperation and coordination with relevant authorities to ensure compliance and manage ICT risks effectively.
What happens if an institution is found non-compliant?
The Digital Operational Resilience Act (DORA) is compliance requirements for financial institutions designed to improve digital operational resilience and manage ICT risks effectively. As mentioned above, institutions have until February 17, 2025, to update all DORA frameworks and be compliant before enforcements begin. Regulatory fines can be quite harsh for good reason. DORA allows leaders to impose financial penalties on ICT providers amounting to 1% of the provider’s average daily worldwide turnover in the previous business year. Providers can be fined every day for up to six months until achieve compliance, making this a very costly mistake.
Fines are in place for several reasons:
- Deterrence: The literal financial cost of failing to comply and adhere to the regulations is significant and therefore motivating to an institution to get and remain in good standing.
- Accountability: This helps ensure that ICT providers are held accountable for their role in maintaining best security practices to remain resilient and secure.
- Encouragement of Best Practices: By enforcing fines of non-compliance, it encourages ICT providers to invest in better security measures and operational practices.
One key factor to keep in mind is regulations are in place to keep organizations safe and secure, not just their employees and clients, but their secure data, money, physical goods, and all digital assets. By remaining compliant an organization is also protecting their reputation, because if and when a disruption or cyber threat happens, response time and knowing exactly what to do can be the difference between an ordinary day and front-page news for something completely avoidable.