Frequently Asked Questions
Exposure Validation Fundamentals
What is exposure validation in cybersecurity?
Exposure validation is a systematic process used to ensure that exposure data—such as vulnerabilities and attack surfaces—is accurate, reliable, and relevant. It involves steps like defining objectives, collecting and analyzing data, comparing results to standards, and implementing findings to strengthen an organization's security posture. This process helps organizations make informed decisions, comply with regulations, and safeguard assets and reputation.
Why is exposure validation important for organizations?
Exposure validation is critical because it helps organizations identify vulnerabilities early, assess risk accurately, meet compliance requirements (such as GDPR and HIPAA), enhance their security posture, build trust with stakeholders, and allocate cybersecurity resources more efficiently. By validating exposures, organizations can prevent costly breaches and maintain regulatory compliance.
What are the main steps involved in exposure validation?
The exposure validation process typically includes: 1) Defining objectives, 2) Developing a validation plan, 3) Collecting exposure data, 4) Analyzing the data, 5) Comparing with standards or benchmarks, 6) Reviewing and validating findings, 7) Documenting results, and 8) Implementing findings for continuous improvement. Each step ensures data quality and actionable outcomes for security and compliance.
How does exposure validation help with regulatory compliance?
Exposure validation supports compliance with industry regulations (such as GDPR and HIPAA) by ensuring that sensitive information is protected and that organizations can demonstrate robust cybersecurity practices. Meeting these requirements helps avoid fines, legal issues, and reputational damage.
What are the benefits of exposure validation for risk assessment?
Exposure validation enables organizations to identify vulnerabilities and attack surfaces early, allowing for informed risk assessment and resource allocation. This proactive approach helps prevent exploitation by threat actors and supports strategic decision-making across the security organization.
How does exposure validation contribute to cost-effectiveness in cybersecurity?
By validating exposures and prioritizing remediation, organizations can allocate resources more efficiently, focusing on the most critical vulnerabilities. This targeted approach leads to long-term cost savings by preventing breaches and optimizing cybersecurity investments.
How does exposure validation help build trust with customers and stakeholders?
Organizations that prioritize exposure validation and can demonstrate robust cybersecurity practices build trust with customers, partners, and stakeholders. This trust is essential for maintaining business relationships and protecting the organization's reputation.
What types of data are used in exposure validation?
Exposure validation uses various data types, including vulnerability scans, attack path analysis, compliance benchmarks, and real-world attack simulations. Data collection methods may involve direct measurement, modeling, statistical analysis, and quality control to ensure accuracy and relevance.
How does exposure validation support continuous improvement in cybersecurity?
Exposure validation is an ongoing process that incorporates feedback and monitoring to continually improve data accuracy and relevance. By regularly validating exposures, organizations can adapt to evolving threats and maintain a strong security posture over time.
What are the key takeaways from implementing exposure validation?
Key takeaways include improved decision-making based on trustworthy data, enhanced compliance, better resource allocation, and a more resilient security posture. Exposure validation is fundamental for protecting health, safety, and economic stability in any organization.
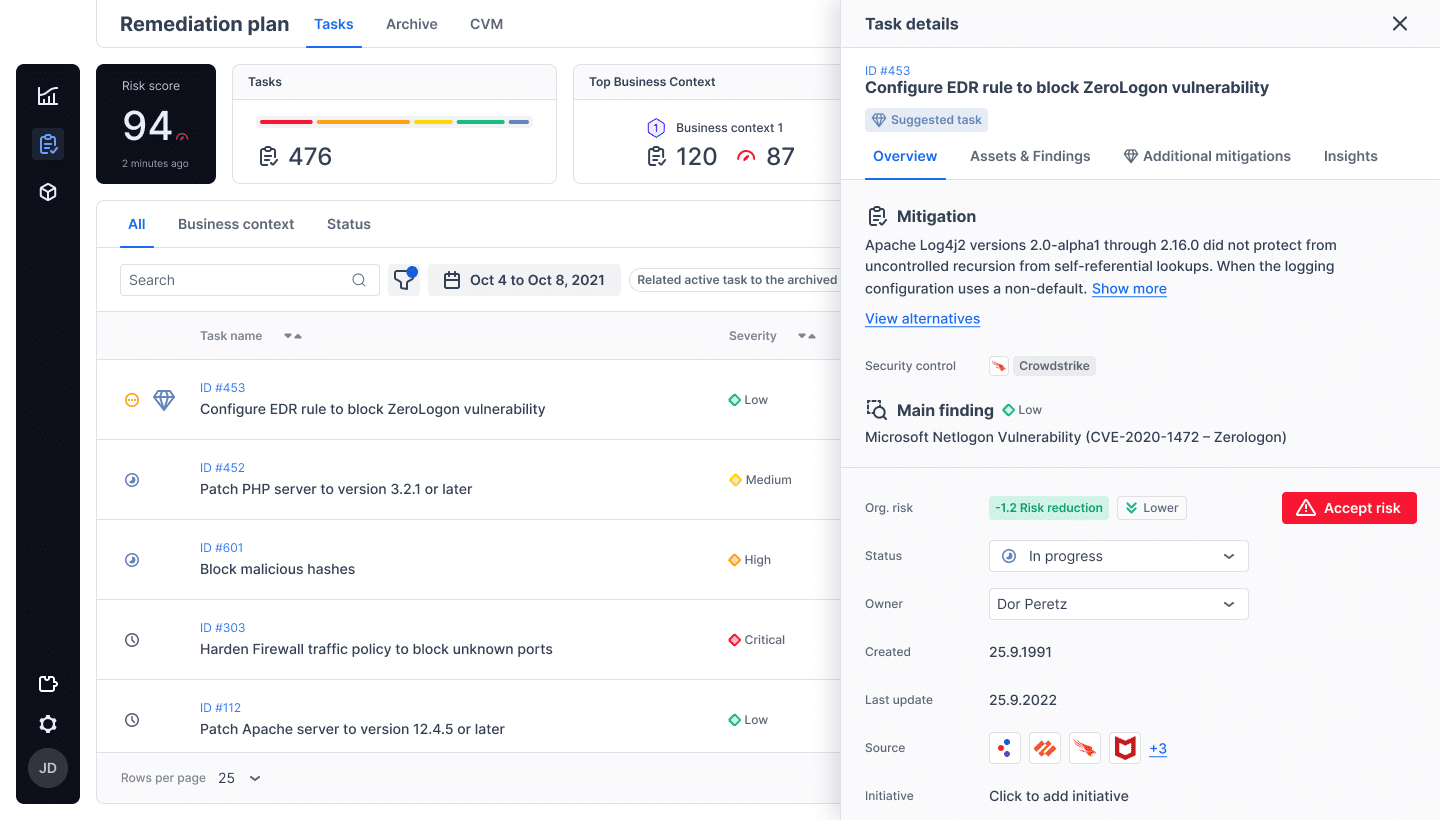
Cymulate Exposure Validation Platform
How does Cymulate perform exposure validation?
Cymulate uses a simulation platform to automatically test and validate security controls across an entire IT environment. It exposes risky threats, dangerous attack paths, and unknown gaps, then provides actionable recommendations to remediate issues before a breach occurs. This continuous attack simulation approach ensures real-time validation and resilience against emerging threats. Learn more.
What are the main features of Cymulate's exposure validation solution?
Cymulate's exposure validation solution offers continuous threat validation, automated attack simulations, attack path discovery, integration with security controls for automated mitigation, and actionable insights for remediation. The platform covers the full attack lifecycle and provides a unified view of exposures for efficient risk management. See platform details.
How does Cymulate help organizations prioritize exposures?
Cymulate validates the exploitability of exposures and ranks them based on prevention and detection capabilities, business context, and threat intelligence. This prioritization enables organizations to focus remediation efforts on the most critical vulnerabilities, improving overall security posture. Learn more.
What types of organizations benefit from Cymulate's exposure validation?
Cymulate's exposure validation is suitable for organizations of all sizes and industries, including finance, healthcare, retail, media, transportation, and manufacturing. It is designed for CISOs, SecOps teams, Red Teams, and Vulnerability Management teams seeking to improve threat resilience and operational efficiency. See more.
How does Cymulate's exposure validation differ from traditional vulnerability management?
Unlike traditional vulnerability management, which often relies on periodic scans and manual processes, Cymulate provides continuous, automated attack simulations and real-time validation. This approach enables organizations to stay ahead of emerging threats and validate the effectiveness of security controls across the entire attack lifecycle. Learn more.
What integrations does Cymulate support for exposure validation?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. These integrations enhance exposure validation by leveraging existing security controls. See full list.
How easy is it to implement Cymulate's exposure validation platform?
Cymulate is designed for rapid, agentless deployment with minimal setup. Customers can start running simulations almost immediately, with no need for additional hardware or complex configurations. Comprehensive support and educational resources are available to help users get started quickly. Book a demo.
What customer feedback is available about Cymulate's exposure validation?
Customers consistently praise Cymulate for its ease of use, intuitive dashboard, and actionable insights. Testimonials highlight the platform's user-friendly interface, rapid implementation, and effective support. For example, Raphael Ferreira, Cybersecurity Manager, noted, "Cymulate is easy to implement and use—all you need to do is click a few buttons, and you receive a lot of practical insights into how you can improve your security posture." See more testimonials.
What measurable outcomes have organizations achieved with Cymulate's exposure validation?
Organizations using Cymulate have reported significant improvements, such as an 81% reduction in cyber risk (Hertz Israel, four months), a 52% reduction in critical exposures, a 60% increase in team efficiency, and up to 60 hours per month saved in testing new threats. Read case study.
Security, Compliance & Certifications
What security and compliance certifications does Cymulate hold?
Cymulate holds several industry-leading certifications, including SOC2 Type II (covering security, availability, confidentiality, and privacy), ISO 27001:2013 (Information Security Management), ISO 27701 (Privacy Information Management), ISO 27017 (Cloud Services Security Controls), and CSA STAR Level 1. These certifications demonstrate Cymulate's commitment to robust security and compliance standards. Learn more.
How does Cymulate ensure data security and privacy?
Cymulate ensures data security through encryption in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, and a tested disaster recovery plan. The platform is developed using a secure development lifecycle, continuous vulnerability scanning, and annual third-party penetration tests. GDPR compliance is maintained with a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO). More details.
What product security features does Cymulate offer?
Cymulate's platform includes mandatory 2-Factor Authentication (2FA), Role-Based Access Controls (RBAC), IP address restrictions, and TLS encryption for its Help Center. These features help ensure secure access and protect sensitive information. See security details.
How does Cymulate support GDPR compliance?
Cymulate incorporates data protection by design and maintains a dedicated privacy and security team, including a Data Protection Officer (DPO) and Chief Information Security Officer (CISO). The platform's processes and controls are aligned with GDPR requirements to ensure customer data privacy. Learn more.
Use Cases, Pain Points & Benefits
What common pain points does Cymulate's exposure validation address?
Cymulate addresses pain points such as fragmented security tools, resource constraints, unclear risk prioritization, cloud complexity, communication barriers, inadequate threat simulation, operational inefficiencies in vulnerability management, and post-breach recovery challenges. The platform provides unified visibility, automation, and actionable insights to solve these issues. See case studies.
How does Cymulate's exposure validation help different security roles?
Cymulate tailors its solutions for CISOs (providing metrics and risk prioritization), SecOps teams (automating processes and improving efficiency), Red Teams (offensive testing with a large attack library), and Vulnerability Management teams (automated validation and prioritization). Each role benefits from features designed to address their unique challenges. Learn more.
What are some real-world use cases for Cymulate's exposure validation?
Use cases include reducing cyber risk (Hertz Israel, 81% reduction in four months), scaling penetration testing (sustainable energy company), improving SecOps with live-data exercises (credit union), increasing visibility in hybrid/cloud environments (Nemours Children's Health), and proving compliance for audits (Saffron Building Society). Explore case studies.
How does Cymulate's exposure validation improve operational efficiency?
Cymulate automates exposure validation processes, saving up to 60 hours per month in testing new threats and increasing team efficiency by 60%. Automation allows security teams to focus on strategic initiatives rather than manual tasks. Learn more.
What are the key benefits of using Cymulate for exposure validation?
Key benefits include continuous threat validation, improved security posture (up to 52% reduction in critical exposures), faster threat validation (40X faster than manual methods), cost savings, enhanced threat resilience, and better decision-making with actionable insights. See platform benefits.
Pricing, Support & Resources
How is Cymulate's exposure validation platform priced?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements. Pricing depends on the chosen package, number of assets, and scenarios selected for validation. For a personalized quote, schedule a demo with the Cymulate team.
What support options are available for Cymulate customers?
Cymulate provides comprehensive support, including email support ([email protected]), real-time chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers and guidance. Explore resources.
Where can I find educational resources about exposure validation and cybersecurity?
Cymulate offers a Resource Hub with insights, thought leadership, and product information, as well as a blog, case studies, webinars, e-books, and a continuously updated cybersecurity glossary. Visit the Resource Hub or see the glossary.
Is there a glossary of cybersecurity terms available?
Yes, Cymulate provides a comprehensive glossary of cybersecurity terms, acronyms, and jargon. The glossary is continuously updated and can be accessed at cymulate.com/cybersecurity-glossary/.
Where can I find Cymulate's case studies and customer success stories?
Cymulate's case studies and customer success stories are available on the Customers page. These resources showcase real-world outcomes and industry-specific examples of exposure validation in action.