Input Validation
Input Validation Vulnerabilities: What They Are and How to Avoid Them
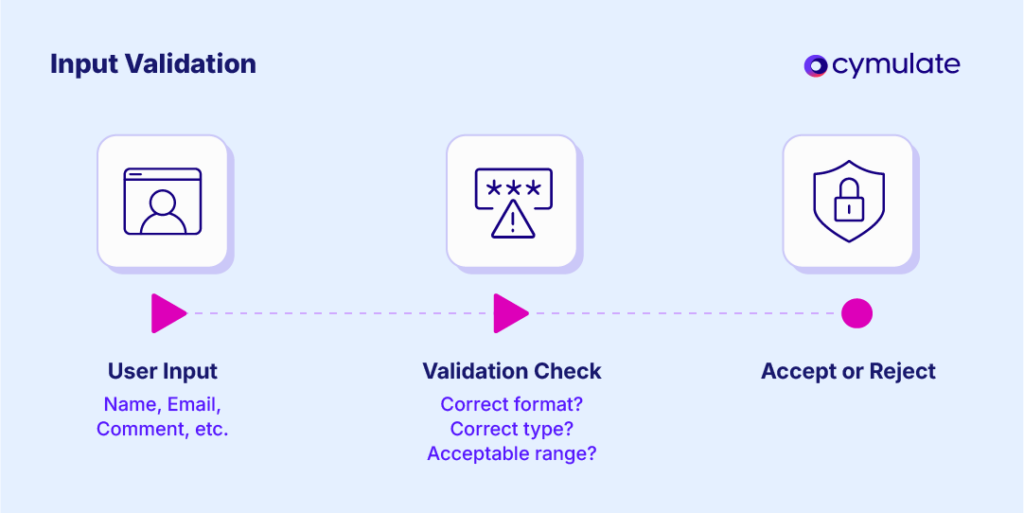
Input validation ensures data entered into systems, such as web forms or applications, meets predefined criteria like format, type and range.
This process is extremely important in input validation cybersecurity to block malicious inputs that could lead to attacks like SQL injection, where attackers manipulate database queries, or XSS, where scripts are injected into web pages.
With validation checks early in the data processing lifecycle, organizations can proactively identify and reject unauthorized or malicious input before it can be acted upon by the application.
This initial scrutiny is not merely a suggestion but a foundational element of any secure system, acting as the first line of defense against a multitude of threats.
The Importance of Input Validation in Cybersecurity
Input validation, also known as data validation, is the process of testing and ensuring that user or application-supplied input meets predefined rules (such as format, length and type) to prevent malicious or erroneous data entry.
It is a fundamental aspect of input validation cybersecurity, critical for protecting systems from attacks like SQL injection, cross-site scripting (XSS) and remote code execution (RCE).
The OWASP Cheat Sheet Series defines input validation as ensuring canonical encoding and using whitelisting, emphasizing its role in preventing injection attacks, which are prevalent in the OWASP Top 10 2021, ranked third with 94% testing coverage.
The Equifax data breach is an example of where inadequate validation of input related to the Apache Struts framework allowed attackers to gain unauthorized access to sensitive systems, resulting in the exposure of millions of individuals' personal information.
While not solely attributed to input validation failures, incidents like the MGM Resort breach and the data leak at First American Financial Corp underscore the potential for significant financial losses, reputational damage and regulatory scrutiny that can arise from weaknesses in security controls governing user interactions. These events highlight the tangible and often catastrophic impact of overlooking fundamental security practices.
Furthermore, secure input validation practices are not merely a matter of best practice; they are frequently emphasized and even mandated by various regulatory and compliance frameworks:
- OWASP Top 10 2021: Lists injection (including SQLi and XSS) as A03, with 33 CWEs mapped, second highest in occurrences, requiring secure input validation practices
- NIST SP 800-53 Rev. 5: Includes SI-10: Information Input Validation, mandating checks on input validity, such as syntax and semantics, to verify format and content
- ISO 27001: Annex A.12.2.1 requires validating application inputs to ensure correctness and appropriateness, aligning with compliance needs for secure coding.
Input validation operates through several key strategies to effectively prevent attacks. Understanding these different types and methods is crucial for implementing a comprehensive security approach.
Client-side vs. Server-side Validation: Why Server-side is Critical
One fundamental distinction in input validation is between client-side and server-side validation. Client-side validation occurs within the user's browser, typically before data is transmitted to the server.
This process enhances the user experience by providing immediate feedback on input errors. However, client-side validation can be easily bypassed by attackers who disable JavaScript or manipulate HTTP requests directly.
As a result, server-side validation, which happens after data submission on the application server, is the critical layer for ensuring security. Server-side validation serves as the definitive gatekeeper, ensuring that all data processed by the application meets the required security and business logic criteria.
Whitelist vs. Blacklist Validation: Why Whitelisting is More Secure
Another crucial distinction in input validation involves the choice between whitelist and blacklist validation. Blacklist validation seeks to identify and block specific malicious characters or patterns. While this approach can be effective, it is inherently flawed, as attackers may devise new ways to bypass these filters.
On the other hand, whitelist validation operates on the principle of explicitly defining what is permitted, and by default, rejecting anything that does not conform to the allowed set of characters, formats or values.
Whitelisting is generally considered a more secure strategy because it significantly reduces the attack surface by only accepting input that is explicitly trusted.
Sanitization vs. Validation: The Role of Each in Preventing Attacks
It is essential to differentiate between sanitization and validation, as both serve important but distinct roles in protecting applications. Validation is the process of ensuring that input data adheres to a predefined set of rules, confirming its correctness in terms of format, type, and length.
Sanitization, on the other hand, modifies the input to remove or encode potentially harmful characters or code, ensuring that the data is safe for processing and display. While validation verifies input conformity, sanitization ensures that any potentially harmful elements are neutralized before they can be executed or stored. These processes are often used in tandem to provide comprehensive protection against a wide range of attack vectors.
Methods for Secure Input Validation
To achieve its objectives, secure input validation employs various methods, each tailored to specific needs and data types.
Regex-based Validation
Regular expressions (regex) are powerful tools used to define intricate patterns that input data must match. This method is particularly effective for validating structured data formats, such as email addresses, phone numbers, and zip codes.
| Input Type | Regex Pattern | Description |
| Email Address | ^[a-zA-Z0-9._%+-]+@[a-zA-Z0-9.-]+\.[a-zA-Z]{2,}$ | Validates a standard email format. |
| US Phone Number | [2-9]\d{2}-\d{3}-\d{4} | Validates a hyphen-separated US phone number. |
| 5-Digit Zip Code | ^[0-9]{5}$ | Validates a 5-digit zip code. |
| Alphanumeric Only | ^[a-zA-Z0-9]+$ | Validates a string containing only letters and digits. |
Length Restrictions
Enforcing minimum and maximum lengths for input fields is another essential method in secure input validation.
These restrictions help prevent buffer overflow attacks and mitigate the risk of denial-of-service attempts. By limiting the size of the input, applications can avoid memory corruption issues and ensure efficient resource utilization.
Encoding User Input
Encoding is a vital technique, particularly in preventing cross-site scripting (XSS) attacks. It transforms potentially harmful characters into a safe format, ensuring that they are displayed as text rather than being executed as code by the browser.
This step is crucial for maintaining the integrity and security of user data when displayed in the application’s UI.
Mitigating Common Input Validation Vulnerabilities
| Vulnerability | Exploitation Method | Mitigation Strategy |
| SQL Injection (SQLi) | Manipulates database queries via unsanitized input | Use prepared statements and parameterized queries, separating code from data. |
| Cross-Site Scripting (XSS) | Injects scripts into web applications, exploiting poor validation | Implement output encoding and strict input sanitization, using libraries like DOMPurify. |
| Buffer Overflow Attacks | Overwrites memory with excessive input, leading to code execution | Enforce input length restrictions and use secure coding with bounds checking. |
| Command Injection Attacks | Executes shell commands via unsanitized input | Use allowlists for commands and avoid direct input execution in system calls. |
| Cross-Site Request Forgery (CSRF) | Forges requests on behalf of users due to weak validation | Implement anti-CSRF tokens and strict referrer validation to ensure legitimacy. |
Several common vulnerabilities arise from inadequate input validation, each requiring specific mitigation strategies.
SQL Injection (SQLi)
SQL Injection (SQLi) occurs when attackers exploit weak input validation to insert malicious SQL code into application inputs, thereby manipulating database queries. For instance, an attacker might input ' OR '1'='1 into a username field to bypass authentication.
The primary mitigation for SQLi is the use of prepared statements and parameterized queries. These techniques separate the SQL code structure from the user-supplied data, ensuring that the input is treated as data and not as executable code, thus preventing the injection of malicious commands.
Cross-Site Scripting (XSS)
These vulnerabilities arise when attackers inject malicious scripts, often JavaScript, into web applications, which are then executed in the browsers of other users. A common example is injecting <script>alert('XSS')</script> into a comment field.
Mitigation strategies include implementing output encoding, which converts special characters into their HTML entities, preventing them from being interpreted as executable code.
Additionally, strict input sanitization, especially for user-authored HTML content, using libraries like DOMPurify, can effectively remove or neutralize malicious scripts.
Buffer Overflow Attacks
Such attacks occur when an application attempts to store more data in a buffer than it was designed to hold, leading to the overwriting of adjacent memory locations, potentially corrupting data or allowing for the execution of malicious code.
For example, providing an input string longer than the allocated buffer for a password can overwrite other parts of memory.
Mitigation primarily involves enforcing input length restrictions to ensure that the size of the input does not exceed the buffer's capacity. Adhering to secure coding practices, such as using memory-safe functions and languages with built-in bounds checking, is also crucial.
Command Injection Attacks
Command Injection Attacks happen when unsanitized user input is directly incorporated into commands executed by the system shell, allowing attackers to run arbitrary commands on the host operating system.
An attacker might append ; ls to a filename input to execute the list directory command. Mitigation involves using allowlists to restrict the characters and values allowed in the input and avoiding the direct execution of user-provided data in system commands.
Employing safer alternatives, such as using built-in library functions for specific tasks instead of relying on shell commands, is highly recommended.
Cross-Site Request Forgery (CSRF)
CSRF vulnerabilities enable attackers to trick authenticated users into performing unintended actions on a web application.
For instance, an attacker could craft a malicious link that, when clicked by a logged-in user, initiates a bank transfer without their knowledge.
Mitigation strategies include implementing anti-CSRF tokens, such as the Synchronizer Token Pattern (STP), which involves generating a unique, unpredictable token for each user session and verifying it with every state-changing request.
The use of SameSite cookies can also provide an additional layer of defense by restricting when cookies are sent with cross-site requests.
Common Input Validation Mistakes to Avoid
Security professionals must avoid these common pitfalls:
- Relying Solely on Client-Side Validation: Easily bypassed, as seen in the BitGrail breach, requiring server-side checks. While it can improve user experience by providing immediate feedback, client-side validation is easily bypassed by attackers who can manipulate requests directly, making it an insufficient security control on its own.
- Using Blacklist Filtering Instead of Whitelisting: Blacklists are incomplete, missing new attack vectors, while whitelisting is more secure. Blacklists, which attempt to block known malicious inputs, are often incomplete and can be circumvented by novel attack techniques, whereas whitelists provide a more secure approach by explicitly defining what is allowed.
- Failing to Normalize Input Before Validation: Attackers can use encoding tricks (e.g., %20 for spaces) to bypass checks, necessitating normalization. For example, a semicolon, used to separate commands in some injection attacks, can have various URL-encoded forms.
- Not Enforcing Strict Data Types: Allowing free text input where a specific data type, such as a number, is expected can open doors for various injection attacks or unexpected application behavior.
- Ignoring Error Handling Best Practices: Overly verbose error messages might reveal sensitive system information to potential attackers, while generic or unhelpful messages can hinder legitimate users and make debugging difficult.
These mistakes, if unaddressed, can undermine security, emphasizing the need for comprehensive validation strategies.
Assessing Input Validation Effectiveness Through Security Control Validation
Cymulate’s Exposure Validation Platform is a powerful tool that includes security control validation for testing defenses against input validation vulnerabilities.
The solution offers automated simulations for threats like SQLi, XSS and Log4j, enabling continuous testing of security controls. Key features include:
- Network Security Validation: Tests resilience against exploits, aligning with MITRE ATT&CK and NIST 800-53 frameworks, using heatmaps to visualize control effectiveness.
- Application Security Testing: Validates protection against emerging threats, with daily threat feed updates and 81% automated validation, as noted in user testimonials highlighting faster validation and comprehensive testing
Security teams can use the Cymulate platform to identify gaps, strengthen defenses and ensure compliance, making it an essential resource for validating input validation controls.