Runtime Security
Modern cloud-native environments are dynamic and ephemeral – containers spin up and down in seconds, serverless functions run on demand, and applications are updated continuously.
Traditional security tools that only check for vulnerabilities before runtime or rely on fixed perimeters cannot keep up with threats that manifest only at runtime, such as in-memory (fileless) malware or abuse of legitimate processes
Attackers increasingly exploit gaps after deployment – for instance, a new zero-day vulnerability might be exploited in a running application, or a misconfiguration could be abused at runtime.
Runtime security fills this gap by providing live protection and visibility in production environments. It plays a considerate role in cloud security (securing workloads running on platforms like AWS, Azure, GCP), container security (detecting threats inside Docker/Kubernetes environments), and application security (guarding applications during execution via techniques like Runtime Application Self-Protection (RASP)).
What is Runtime Security?
Runtime security is the practice of protecting applications, containers, and cloud workloads while they are running by continuously monitoring their behavior and intervening in real time to stop threats.
In contrast to traditional security measures that focus on code before deployment or securing the network perimeter, runtime security operates during the production phase – when software is executing and most vulnerable to active attacks
It involves instruments like agents or sensors that observe application behavior, system calls, memory usage, and other telemetry to detect anomalies or malicious actions as they happen.
By analyzing this activity in real time, a runtime security solution can alert on or even automatically block suspicious events (for example, killing a malicious process or quarantining a compromised container). This approach offers immediate, dynamic protection, complementing the “shift-left” practices (like code scanning) with “shift-right” defense.
Types of Runtime Security
Runtime security can be applied at multiple layers of the modern technology stack. Key categories include:
Cloud runtime security
Cloud runtime security focuses on protecting cloud workloads and infrastructure in real time. This means monitoring the execution of virtual machines, cloud services, and applications running in cloud environments for any malicious or abnormal activity.
Cloud providers offer native tools (like AWS GuardDuty or Azure Defender) to detect threats in cloud runtime, and third-party Cloud Workload Protection Platforms (CWPPs) add additional real-time defenses.
Cloud runtime security might catch things like suspicious process activity on a cloud VM, unauthorized API calls, or unusual network traffic within your cloud environment. The goal is to secure cloud workloads (VMs, serverless functions, etc.) against attacks as they occur, providing immediate detection and response within cloud platforms.
Kubernetes runtime security
Kubernetes runtime security is specifically about securing containerized applications orchestrated by Kubernetes during their execution. Kubernetes clusters are complex, with many moving parts (pods, containers, network policies, etc.), so specialized runtime security is needed to detect threats like a container breakout, a crypto mining payload running in a pod, or an attacker moving laterally in the cluster
Tools in this category (such as Falco or Kubernetes-native security agents) monitor system calls and Kubernetes API events to flag abnormal behavior in containers or the cluster.
For example, if a container suddenly spawns a process that is not in its normal profile (maybe a web server container starting a bash shell and downloading a file), the runtime security tool can alert or stop it.
Kubernetes runtime security ensures that running containers and the cluster’s components (like the kubelet, API server, etc.) are protected, complementing build-time checks (like image scanning) with real-time threat detection in the live environment
Container runtime security
Closely related to Kubernetes security, container runtime security refers to protecting any container platform (Docker, containered, CRI-O, etc.) during operation. Even if you’re not using full Kubernetes orchestration (for example, running Docker containers on VMs or using other container services), you need to monitor those containers at runtime.
Container runtime security tools watch the container’s processes, file system changes, and network usage for signs of compromise.
This might include detecting a shell spawned inside a container, a container making outbound network connections it never did before, or changes to files that should be immutable.
Runtime application self-protection (RASP)
Runtime Application Self-Protection (RASP) is a specific technology focused on securing applications from within while they run. RASP solutions embed instrumentation (agents or libraries) into an application’s runtime environment (often within the application server or the app’s code) to monitor and intercept attacks in real time.
Unlike external defenses like firewalls, RASP operates inside the application – it has insight into the code execution flow, inputs, and internal state. This enables it to detect things like injection attacks, attempts to exploit a function in memory, or other abnormal behaviors at the application level.
Why Is Runtime Security Crucial in Cloud Environments?
In cloud and hybrid environments, workloads are highly dynamic, scalable, and often short-lived. This brings unique security challenges that make runtime protection crucial:
1. Dynamic workloads & ephemeral infrastructure
Cloud instances, containers, and serverless functions can be created and destroyed on demand. Their configuration and behavior can change rapidly. Runtime security is needed to continuously adapt to these changes – providing protection even as new workloads spin up or environments shift.
Traditional static security (like one-time scans or predefined firewall rules) may miss threats in such a fluid environment, whereas runtime monitoring adjusts in real time to each workload’s lifecycle.
2. Increased attack surface from microservices
Modern cloud applications often use microservices architectures and rely on numerous third-party services or open-source components. This distributed design means many more moving parts that attackers can target.
A vulnerability in one microservice or a misconfigured permission between services might only be exploitable once everything is deployed and interacting.
3. Threats that bypass pre-deployment controls
Some attacks manifest purely at runtime, such as fileless malware that resides in memory, or a malicious insider abusing credentials at runtime. These don’t involve adding new files or code that a scanner could catch beforehand.
Similarly, a container breakout (where a process escapes the container to the host) can only be detected by watching running processes and system calls.
4. Compliance and visibility
Many compliance frameworks such as General Data Protection Regulation (GDPR) and require organizations to monitor their systems and maintain audit logs of activity. Ensuring continuous security monitoring in production is often a compliance mandate. For instance, financial regulations and standards demand real-time auditing and detailed logs of system access and changes.
Key Tools and Frameworks
A variety of tools and technologies can help implement runtime security. Some focus on providing visibility, others on enforcement, and some on validation of security. Key examples include:
eBPF (Extended berkeley packet filter)
eBPF is a powerful Linux kernel technology that enables programs to run inside the kernel space safely. Many modern runtime security tools leverage eBPF to gain deep visibility into system calls and kernel events without significant performance overhead.
By attaching eBPF programs to events (like file access, process execution, or network sockets), security tools can monitor and even filter behavior in real time.
Falco (CNCF falco)
Falco is an open-source runtime security tool (a Cloud Native Computing Foundation project) specifically designed for containers and Kubernetes. It uses either a kernel module or eBPF probe to tap into system calls, and it applies a set of rules to identify suspicious behavior.
Security teams can define Falco rules such as “alert if any container process spawns a shell” or “alert if a container tries to open a sensitive file like /etc/shadow.” Falco will then generate real-time alerts when such events occur, indicating a possible breach or policy violation.
Cloud workload protection platforms (CWPPs)
CWPP is a category of security products (often commercial) that provide unified runtime protection for workloads across VMs, containers, and serverless. Examples include Prisma Cloud (Palo Alto Networks), Sysdig Secure, Aqua Security, Trend Micro Cloud One, and others.
These platforms typically combine multiple capabilities: they might do vulnerability scanning (pre-runtime) and runtime defense like anomaly detection, firewalling, and anti-malware. At runtime, CWPPs can monitor file integrity, detect exploit attempts, enforce application allow-lists, and more.
Compliance and Regulations Affecting Runtime Security
Organizations operating in regulated industries have an added incentive to implement runtime security—various laws and standards either explicitly require or implicitly benefit from continuous runtime monitoring.
GDPR (General data protection regulation)
GDPR mandates that organizations protect personal data with “appropriate technical and organizational measures” and report breaches within 72 hours.
While GDPR does not prescribe specific security technologies, runtime security plays a crucial role in meeting its requirements.
PCI-DSS (Payment card industry data security standard)
PCI-DSS, which governs credit card data security, has explicit requirements that align with runtime security. For instance:
- Requirement 11 mandates regular security testing, which can be fulfilled by continuous security validation of runtime defenses. Breach and Attack Simulation (BAS) platforms automate this process by continuously assessing security controls against real-world attack techniques. By simulating sophisticated cyber threats in a controlled environment, BAS enables organizations to identify gaps in runtime defenses, validate their effectiveness, and ensure compliance with Requirement 11.
- PCI-DSS requires file integrity monitoring and intrusion detection, often achieved using runtime security agents that monitor processes, logins, and file changes in real time.
- Organizations must detect and mitigate unauthorized access and malware at runtime, ensuring compliance with PCI’s mandate to “detect and address failures of critical security controls.”
NIST 800-53 and NIST 800-190 (container security guidelines)
The NIST 800-53 framework establishes security and privacy controls for federal information systems. Key runtime security-related controls include:
- SI-4 (System Monitoring): Requires continuous monitoring of system activities.
- IR-5 (Incident Monitoring): Mandates real-time threat detection and response capabilities.
Additionally, NIST 800-190 (focused on container security) specifically recommends runtime monitoring tools to detect threats like container escapes or privilege escalation attempts.
CIS Benchmarks (center for internet security)
CIS Benchmarks define security best practices for platforms like Windows, Linux, Kubernetes, Docker, and cloud accounts. While CIS primarily focuses on preventative measures, runtime security complements these controls by providing real-time monitoring and threat response. For example:
- CIS Kubernetes Benchmark recommends audit logging, a runtime security best practice that improves visibility into real-time activities within Kubernetes clusters.
- CIS also advises minimal privileges for containers, reducing the risk of exploitable vulnerabilities at runtime.
- Many CIS frameworks require host-based intrusion detection, reinforcing the need for real-time runtime monitoring.
How Runtime Security Integrates with Other Security Solutions
Runtime security is most effective when integrated into a broader security ecosystem. SIEM centralizes real-time alerts and correlates runtime security data with network and identity activity for better threat detection. XDR extends this by integrating endpoint, cloud, and runtime security data for automated cross-domain responses.
Breach and Attack Simulation (BAS) platforms like Cymulate validate runtime security by simulating threats to ensure effective detection and reduce false positives. Runtime security also integrates with CI/CD pipelines, ITSM systems, and APIs, allowing security policies to scale dynamically.
Optimizing Runtime Security with Cymulate
Implementing runtime security is just the beginning—continuous validation is essential to ensure its effectiveness.
The Cymulate Security Validation Platform, enables organizations to test and optimize runtime security through simulated cyberattacks in cloud, container, and hybrid environments.
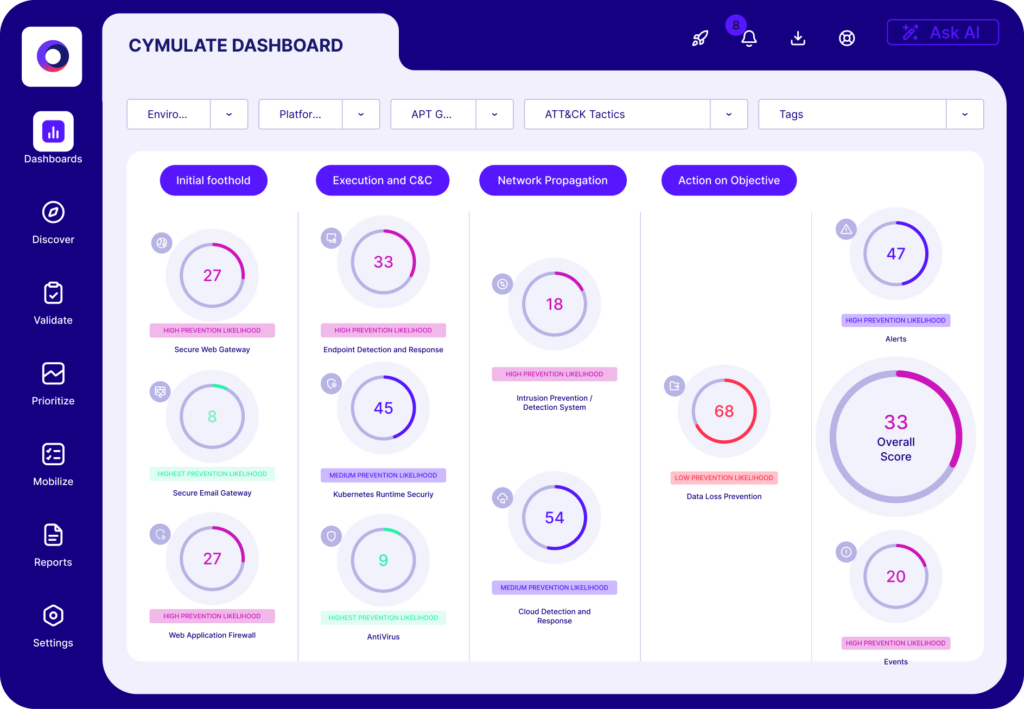
The platform simulates real-world threats (e.g., malware infections, privilege escalation, container breakouts) in a controlled environment to assess if runtime security tools detect and respond correctly. If threats go unnoticed, security teams can identify gaps and refine configurations.
- Continuous validation across cloud & hybrid setups: Cymulate validates security controls across applications, containers, and cloud workloads, ensuring consistent runtime defense in on-premises, multi-cloud, and hybrid infrastructures.
- Benefits of breach and attack simulation (BAS): Regular runtime security testing helps organizations identify misconfigurations, fine-tune detection rules, and reduce false positives/negatives. This continuous feedback loop strengthens security posture and improves response readiness.
- Integration with DevSecOps & CI/CD: Organizations can automate Cymulate simulations in CI/CD pipelines or staging environments, treating security tests like unit tests. Failed tests trigger immediate remediation, ensuring proactive detection and rapid issue resolution before attackers can exploit vulnerabilities.