Spear Phishing: Understanding the Threat and How to Defend Against It
While traditional phishing tactics target a wide range of potential victims with generic, often suspicious messages, spear phishing takes a more calculated and dangerous approach. It specifically targets individuals or organizations with highly personalized and deceptive messages, designed to exploit their trust and curiosity.
With attackers using detailed information gathered through social engineering and other means, these attacks are much harder to detect, making them a significant threat to both personal and corporate security:
- Spear phishing is responsible for 66% of all data breaches, despite making up only 0.1% of all email-based phishing attacks. This statistic underscores the effectiveness of spear phishing in compromising security.
- 50% of organizations reported being victims of spear phishing in 2022, with an average of five spear-phishing emails received per day by typical organizations. This indicates a significant threat level faced by businesses.
- 36% of all data breaches involve phishing, which includes spear phishing attacks, demonstrating the widespread impact of these tactics on data security.
- 84% of organizations experienced at least one phishing attempt in 2022, reflecting the high frequency and commonality of these attacks across various sectors.
- The click rate for spear phishing emails is approximately 53.2%, significantly higher than the average click rate for general phishing emails, which was around 17.8% in 2021. This shows that targeted attacks are more likely to succeed.
What Exactly is Spear Phishing?
Spear phishing is a targeted form of cyber attack that involves customizing fraudulent emails, messages, or requests for information in order to deceive specific individuals or organizations.
Unlike broad phishing attempts, which typically cast a wide net hoping to catch many victims with a generic email, spear phishing attacks focus on a select few, using highly specific personal or professional information to increase the likelihood of success.
This could include details like the recipient’s name, job title, work relationships, or even recent business dealings, often gathered through social media, public databases or previous data breaches.
The primary goal of spear phishing is to steal sensitive data such as usernames, passwords, financial details, intellectual propert, or personal credentials.
In some cases, attackers may also use spear phishing as a gateway to plant malware or carry out fraudulent financial transactions within the targeted organization. These attacks are more sophisticated and personalized than traditional phishing, making them significantly harder to detect and more dangerous if successful.
Types and Examples of Spear Phishing Attacks
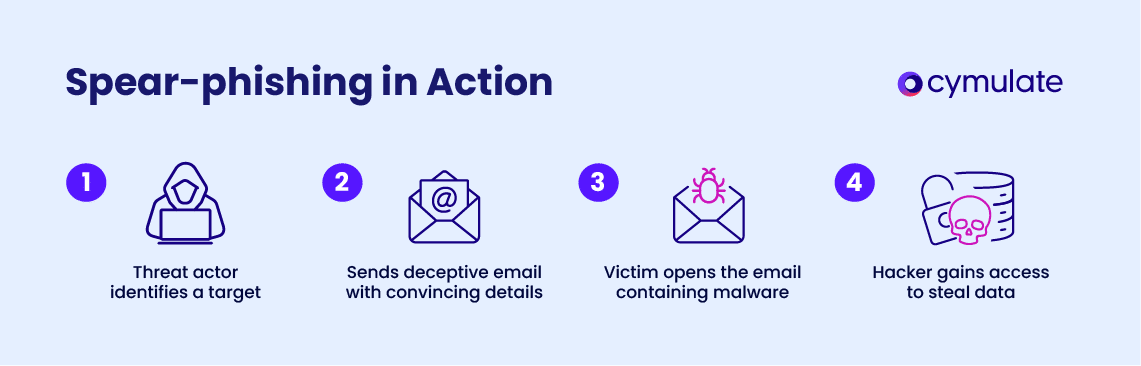
Spear phishing can take on several forms depending on the attacker's objective and the platform used to carry out the attack. Below are some of the most common spear phishing methods:
Email spear phishing
By far the most well-known type of spear phishing, this method involves sending deceptive emails that appear to be from trusted sources. These emails might ask for urgent actions like resetting a password or verifying account details.
They are carefully crafted, often using specific knowledge about the victim’s professional role, company events, or industry to appear legitimate.
This high level of personalization leads to a greater chance that the victim will click on malicious links, open infected attachments, or share confidential information.
Fake Invoices and payment requests
- Siemens (2024): Siemens lost €12 million when attackers impersonated a trusted supplier and sent a fake invoice to the finance department, leveraging personalized details to make the email appear legitimate.
- Ubiquiti Networks (2016): This American technology company fell victim to a spear phishing attack where hackers spoofed the CEO's email address, convincing the finance team to transfer $46.7 million to a fraudulent account.
- Turner Construction (2017): Attackers sent fake invoices that appeared to come from a trusted vendor, resulting in unauthorized fund transfers.
Social media spear phishing
In addition to email, spear phishing can also occur on social media platforms like LinkedIn, Facebook or Twitter.
Cybercriminals often exploit publicly available information from these sites to send convincing messages, such as fake job offers, friend requests or requests for sensitive information.
The social nature of these platforms means that people are often more trusting, making it easier for attackers to manipulate their targets.
Collaboration scams
- Google drive scam (2020): Scammers created a document with malicious links and tagged their targets in comments, prompting them to click on links leading to phishing sites. This method exploited Google’s notification system, tricking users into entering their credentials.
- Twitter accounts compromised (2020): A vishing attack led to the compromise of high-profile Twitter accounts, including those of Barack Obama and Joe Biden. Hackers used social engineering tactics over the phone to gain access to account credentials, resulting in unauthorized tweets and data access.
Business email compromise (BEC)
A more targeted form of spear phishing, Business Email Compromise (BEC) often focuses on senior-level executives, such as CEOs, CFOs or department heads.
Attackers impersonate these high-ranking individuals and send fraudulent requests to lower-level employees, such as asking for wire transfers or confidential financial data.
Since these emails appear to come from a trusted authority, they carry significant weight, making them much harder to resist.
CEO Fraud
- Pathé Cinema Group (2019): The French cinema giant lost €19.2 million when attackers impersonated the CEO through email, requesting fund transfers to a fraudulent entity in Dubai.
- City of Atlanta (2018): A ransomware attack was initiated through spear phishing emails sent from compromised accounts of trusted contacts within the city government, leading to significant operational disruptions and data loss.
- Seagate Technology (2016): The company was targeted with an email that appeared to be from the IRS requesting employee W-2 forms, resulting in the theft of sensitive employee information.
How Does Spear Phishing Differ from Standard Phishing?
While spear phishing is a form of phishing, it is fundamentally different from standard phishing in several ways:
1. Sophistication
Spear phishing is much more sophisticated than traditional phishing. While standard phishing often involves generic messages such as “Your account has been compromised. Click here to reset your password,” spear phishing emails are personalized, incorporating specific details like the recipient’s name, company, job role, or recent interactions. This personalization makes them far more difficult to detect.
2. Targeting
These phishing attacks are highly targeted, aimed at specific individuals or organizations. Cybercriminals may focus on employees with access to critical data or financial systems.
In contrast, standard phishing attempts often target large groups of people with no specific goal or focus.
3. Clone Phishing
Clone phishing, a related tactic, involves creating near-identical copies of legitimate emails previously sent to the victim. The attacker replaces legitimate attachments or links with malicious ones, tricking recipients into thinking the message is simply a follow-up or resend. Clone phishing often complements spear phishing attacks by leveraging trust established through earlier communications.
4. Detection challenges
Because spear phishing emails are personalized and tailored, they can bypass traditional security tools such as spam filters, which are designed to detect generic phishing messages.
These emails often appear legitimate because they come from trusted sources or use information that the victim believes to be credible.
Phishing, Spear Phishing, Whaling and Vishing: Key Differences
| Feature | Spear Phishing | Phishing | Whaling | Vishing |
| Targeting | Specific individuals or organizations | Broad, random targets | Senior executives or high-level employees | Individuals via phone calls or voice messages |
| Personalization | Highly personalized (using specific details about the victim) | Generic messages with little or no personal information | Customized to exploit the authority of top executives | Often personalized, but focused on voice manipulation |
| Medium | Email, social media | Email or other online communication methods | Email or other digital communication methods | Phone calls or voicemail |
| Attack Goal | Steal sensitive data, plant malware, financial fraud | Steal login credentials, personal data | Financial fraud or sensitive data theft | Extract sensitive information through voice interaction |
| Success Rate | Higher, due to personalization and targeting | Lower, as generic messages are often filtered out | Higher, due to trust in senior authority figures | Moderate, as trust is exploited via voice interaction |
| Sophistication | Highly sophisticated, exploiting specific vulnerabilities | Basic, often easy to identify with generic content | Highly sophisticated, using authority manipulation | Often simpler, relies on social engineering and persuasion |
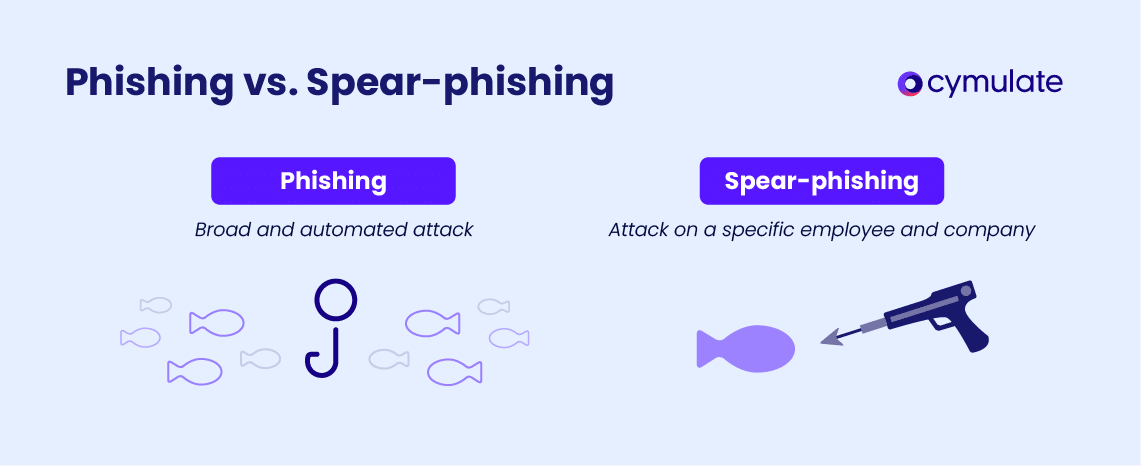
Spear phishing vs. phishing
Spear Phishing involves highly targeted attacks where the attacker tailors their message to a specific individual or organization, using personalized information. It typically has a higher success rate because the message appears credible.
Phishing is a broader attack, where attackers send generic messages to a large group of people, hoping that some will fall for the scam. It is less personalized and more likely to be caught by spam filters.
Spear phishing vs. whaling
Spear Phishing targets specific individuals within an organization, regardless of their seniority. The goal is often to steal sensitive data or plant malware.
Whaling is a subtype of spear phishing, specifically aimed at high-level executives (like CEOs or CFOs). The attacker exploits their authority to carry out financial fraud or steal high-value data, making whaling a more financially motivated and often more sophisticated attack.
Spear Phishing vs. vishing
Spear Phishing uses email or social media to deceive victims, often by impersonating trusted individuals or companies.
Vishing (voice phishing) relies on phone calls or voice messages to trick victims into providing sensitive information. It’s typically less sophisticated than spear phishing but still relies on manipulation and trust to extract data.
Spear Phishing Prevention & Mitigation: Best Practices
Spear phishing prevention requires a combination of human awareness and technical solutions. Here are some best practices to help organizations mitigate the risks:
- Employee training: Training employees to recognize suspicious emails, social media messages, and phone calls is one of the most effective ways to reduce the risk of spear phishing. Employees should be taught to verify unusual requests or messages before taking any action.
- Simulated phishing: Running simulated phishing campaigns can help test how employees respond to phishing attempts and provide insights into potential vulnerabilities in your security protocols.
- SLAM method: The SLAM method (Stop, Look, Ask, and Move) is a simple approach employees can use when reviewing suspicious messages. It encourages them to stop and think before clicking links or responding to emails.
- Multi-factor authentication (MFA): Implementing multi-factor authentication ensures that even if attackers obtain login credentials through spear phishing, they won’t be able to access sensitive systems without the second layer of authentication.
- Advanced email filters and anti-phishing software: These tools can detect and block spear phishing emails before they reach the inbox, providing an additional layer of defense against these attacks.
How Cymulate Can Help Combat Spear Phishing?
Cymulate continuous security validation platform is designed to help organizations combat spear phishing and other cyber threats through proactive measures.
Key features
- Phishing Simulations: Realistic simulations that mimic actual spear phishing attacks to assess employee responses and improve awareness.
- Risk Assessments: Comprehensive evaluations of existing security controls to identify vulnerabilities and enhance overall security performance.
- Exposure Management: Visualization of the attack surface to identify critical vulnerabilities, allowing organizations to prioritize remediation efforts effectively.
Cymulate provides the tools necessary for organizations to continuously test, assess and improve their cybersecurity posture.
To explore how Cymulate can strengthen your defenses against spear phishing, book a demo now!