Frequently Asked Questions
APT42 Threat Intelligence & Context
What is APT42 and what are its primary tactics?
APT42 is a threat group characterized by highly targeted spear phishing and surveillance operations, primarily against individuals and organizations of strategic interest to Iran. Their tactics include building trust with victims to access personal and corporate email accounts, deploying mobile malware for tracking, recording conversations, and extracting sensitive data. (Source: Original Webpage)
Who are the typical targets of APT42 operations?
APT42 typically targets government officials, former Iranian policymakers or political figures, members of the Iranian diaspora and opposition groups, journalists, and academics involved in research on Iran. (Source: Original Webpage)
How does APT42 adapt its operations over time?
APT42 has demonstrated the ability to alter its operational focus as Iran's strategic priorities evolve, maintaining resilience against public reporting and infrastructure takedowns. (Source: Original Webpage)
What types of malware does APT42 use?
APT42 deploys mobile malware capable of tracking victim locations, recording phone conversations, accessing videos and images, and extracting entire SMS inboxes. (Source: Original Webpage)
What is the long-term outlook for APT42 activity?
Mandiant anticipates that APT42 will continue conducting cyber espionage operations in support of Iran's strategic priorities for the long term, given their extensive operational history. (Source: Original Webpage)
How can organizations validate their defenses against threats like APT42?
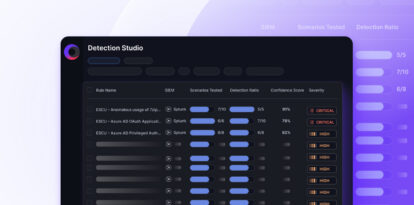
Organizations can use Cymulate's Threat Validation and Exposure Management Platform to simulate real-world attacks, including those similar to APT42, and validate their defenses against advanced persistent threats. (Source: Cymulate Platform, Knowledge Base)
What resources does Cymulate provide for understanding and defending against APT threats?
Cymulate offers resources such as whitepapers, case studies, and demos that showcase how to connect vulnerabilities to real attack scenarios and validate defenses against threats like APT42. (Source: Original Webpage)
How does Cymulate help organizations move from reactive to proactive security against APTs?
Cymulate enables organizations to proactively validate their security controls, identify vulnerabilities, and optimize their security posture, helping them shift from reactive to proactive defense against advanced persistent threats. (Source: Original Webpage, Knowledge Base)
What Cymulate demo resources are available for threat validation?
Cymulate provides demo resources such as 'Threat Validation Demo' and 'From Vulnerability to Validation' to help security teams quickly validate protection against new threats and understand what is actually exploitable. (Source: Original Webpage)
How does Cymulate support validation of web application firewalls (WAF) against threats?
Cymulate offers solutions to validate WAF rules and turn validation gaps into actionable defense, as highlighted in their research blog. (Source: Original Webpage)
Where can I find more resources on threat exposure and validation?
You can access Cymulate's Resource Hub for a combination of insights, thought leadership, and product information related to threat exposure and validation. (Source: Original Webpage)
How does Cymulate's platform help with exposure prioritization and remediation?
Cymulate's Exposure Prioritization & Remediation solution helps organizations focus on what’s exploitable in their environment, enabling efficient remediation of validated exposures. (Source: Original Webpage)
What is Cymulate's approach to attack path discovery?
Cymulate provides automated testing for lateral movement and privilege escalation through its Attack Path Discovery solution, helping organizations identify and mitigate potential attack paths. (Source: Original Webpage)
How does Cymulate support continuous threat exposure management (CTEM)?
Cymulate enables organizations to integrate validation into prioritization and mobilization, supporting collaboration across teams for effective Continuous Threat Exposure Management (CTEM). (Source: Original Webpage)
What industries benefit from Cymulate's solutions?
Cymulate serves a diverse range of industries, including finance, healthcare, retail, media, transportation, and manufacturing, providing tailored solutions for organizations of all sizes. (Source: Knowledge Base)
How does Cymulate help financial services organizations address cyber threats?
The financial services sector faces sophisticated threats like ransomware, phishing, and APTs. Cymulate helps these organizations validate and strengthen their security controls to protect both internal systems and customer-facing applications. (Source: Knowledge Base)
What is Cymulate's Exposure Management Platform?
The Cymulate Exposure Management Platform is a unified solution that combines Breach and Attack Simulation (BAS), Continuous Automated Red Teaming (CART), and Exposure Analytics to help organizations continuously validate and optimize their security posture. (Source: Knowledge Base)
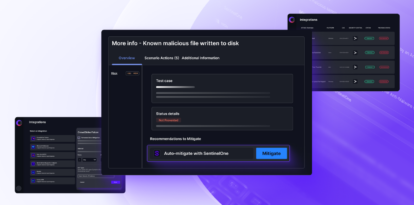
How does Cymulate's Threat Validation solution differ from manual pen tests and traditional BAS?
Cymulate's Exposure Validation provides automated, continuous security testing with a library of over 100,000 attack actions, easy control integrations, and automated mitigation, overcoming the limitations of infrequent manual tests and traditional BAS tools. (Source: Knowledge Base)
Features & Capabilities
What are the key features of Cymulate's platform?
Cymulate offers continuous threat validation, unified BAS and CART, attack path discovery, automated mitigation, AI-powered optimization, complete kill chain coverage, ease of use, and an extensive threat library updated daily. (Source: Knowledge Base)
How does Cymulate's platform improve operational efficiency?
Cymulate automates security validation processes, leading to a 60% increase in team efficiency and saving up to 60 hours per month in testing new threats. (Source: Knowledge Base)
What integrations does Cymulate support?
Cymulate integrates with a wide range of security technologies, including Akamai Guardicore, AWS GuardDuty, BlackBerry Cylance OPTICS, Carbon Black EDR, Check Point CloudGuard, Cisco Secure Endpoint, CrowdStrike Falcon, Wiz, SentinelOne, and more. For a full list, visit the Partnerships and Integrations page. (Source: Knowledge Base)
How does Cymulate's 'Threat (IoC) updates' feature improve threat resilience?
The 'Threat (IoC) updates' feature provides recommended Indicators of Compromise (IoCs) that can be exported and applied to security controls, improving threat resilience by enabling rapid defense against new threats. (Source: Knowledge Base)
Does Cymulate provide vendor-specific policy tuning guidance?
Yes, Cymulate provides mitigation guidance and rule recommendations to fine-tune security configurations and strengthen defenses, a capability not offered by some competitors. (Source: Knowledge Base)
How does Cymulate's implementation of policy tuning differ from Picus?
Cymulate provides robust and automated policy tuning across various vendors, whereas Picus may require manual updates and has limited automated control updates. (Source: Knowledge Base)
Use Cases & Benefits
Who can benefit from using Cymulate?
Cymulate is designed for CISOs, security leaders, SecOps teams, Red Teams, and vulnerability management teams in organizations of all sizes and industries. (Source: Knowledge Base)
What measurable outcomes have customers achieved with Cymulate?
Customers have reported outcomes such as an 81% reduction in cyber risk within four months, a 52% reduction in critical exposures, and a 60% increase in team efficiency. (Source: Knowledge Base)
Are there case studies demonstrating Cymulate's effectiveness?
Yes, case studies include Hertz Israel reducing cyber risk by 81% in four months, a sustainable energy company scaling penetration testing, and a credit union optimizing SecOps with live-data exercises. (Source: Knowledge Base)
How does Cymulate address the pain point of fragmented security tools?
Cymulate integrates exposure data and automates validation, providing a unified view of the security posture and addressing gaps caused by disconnected tools. (Source: Knowledge Base)
How does Cymulate help with resource constraints in security teams?
Cymulate automates processes, improving efficiency and operational effectiveness for security teams that are often stretched thin. (Source: Knowledge Base)
How does Cymulate support communication for CISOs and security leaders?
Cymulate delivers quantifiable metrics and insights tailored to different roles, helping CISOs and security leaders justify investments and communicate risks effectively. (Source: Knowledge Base)
Security & Compliance
What security and compliance certifications does Cymulate hold?
Cymulate holds SOC2 Type II, ISO 27001:2013, ISO 27701, ISO 27017, and CSA STAR Level 1 certifications, demonstrating adherence to industry-leading security and privacy standards. (Source: Knowledge Base)
How does Cymulate ensure data security and privacy?
Cymulate uses encryption for data in transit (TLS 1.2+) and at rest (AES-256), secure AWS-hosted data centers, a tested disaster recovery plan, and a dedicated privacy and security team including a DPO and CISO. (Source: Knowledge Base)
Is Cymulate GDPR compliant?
Yes, Cymulate incorporates data protection by design and has a dedicated privacy and security team, including a Data Protection Officer (DPO), ensuring GDPR compliance. (Source: Knowledge Base)
Implementation & Support
How easy is it to implement Cymulate?
Cymulate is designed for quick and easy implementation, operating in agentless mode with no need for additional hardware or complex configurations. Customers can start running simulations almost immediately. (Source: Knowledge Base)
What support options does Cymulate offer?
Cymulate provides email support, real-time chat support, a knowledge base with technical articles and videos, webinars, e-books, and an AI chatbot for quick answers and guidance. (Source: Knowledge Base)
What feedback have customers given about Cymulate's ease of use?
Customers consistently praise Cymulate for its intuitive, user-friendly interface and actionable insights. Testimonials highlight its ease of implementation and the value of its support team. (Source: Knowledge Base)
Pricing & Plans
What is Cymulate's pricing model?
Cymulate operates on a subscription-based pricing model tailored to each organization's requirements, considering the chosen package, number of assets, and scenarios. For a quote, schedule a demo with the Cymulate team. (Source: Knowledge Base)
Competition & Comparison
How does Cymulate compare to other security validation platforms?
Cymulate stands out with its unified platform, continuous threat validation, AI-powered optimization, complete kill chain coverage, ease of use, and proven customer outcomes. It also offers robust policy tuning and extensive integrations. (Source: Knowledge Base)
What are Cymulate's advantages for different user segments?
CISOs benefit from quantifiable metrics, SecOps teams gain efficiency through automation, Red Teams access a vast attack library, and vulnerability management teams can automate validation and prioritization. (Source: Knowledge Base)