Remote Working and Cybersecurity Risk
With the rise of hybrid and remote work, companies are now more reliant than ever on distributed workforces. While this flexibility boosts productivity and employee satisfaction, it also introduces significant cybersecurity challenges. Organizations must ensure that employees can securely access company resources without exposing sensitive data or increasing the risk of cyberattacks.
Remote work inherently expands the attack surface, as employees operate outside the corporate network’s traditional security perimeter. Without proper safeguards, organizations face heightened threats from phishing attacks, unsecured endpoints, and compromised VPN connections. However, by implementing the right security controls, companies can minimize these risks while maintaining efficiency.
Benefits of Working Remotely
Remote work has a great number of benefits - especially during a crisis of this nature - but also comes with significant cybersecurity drawbacks that should be addressed as quickly as possible. Let’s take a look at several of the most common cyber issues facing companies that are suddenly grappling with keeping their employees both healthy and safe through remote work.
Once outside of the defined security perimeter of a corporate network, employees must still have access to resources and data stores, but without the benefit of direct, controlled connectivity or fully managed endpoints. While some factors become beyond the control of corporate IT, there are ways to reduce the overall risk.
VPN Connectivity
A virtual private network (VPN) can allow remote employees to securely communicate with company resources. VPN’s essentially create an encrypted connection known as a tunnel between their laptop/desktop/mobile and the secured perimeter of the corporate network. Data going across this tunnel isn’t usable by anyone else on the employee’s home network or anyone listening in on the public Internet that those communications travel over.
Endpoint Protection
While a VPN is a definite benefit to cybersecurity, it’s not an all-inclusive security control set. Since it essentially creates a direct connection into your secured networks, it is vitally important that a threat actor cannot gain the same level of access by compromising the employee’s endpoint.
To start, every employee device that is permitted to access company data (including email and file-sharing services), should have a robust and complete anti-malware solution. Currently, behavioral-based detection platforms combined with more traditional signature and heuristic-based scanner is the best practice.
Policies and Rules
Many employees who are working remotely may never have worked outside of the office setting. In addition to helping with best practices and coaching on a personal level, companies must make rules and policies around data connectivity clear and easily understandable.
This includes digital enforcement through things like Group Policy Objects and the use of certificates in Windows networks (such as those tools available in Active Directory and Azure AD); as well as a concise, written policy document distributed to each remote employee. One email outlining how, where, and with what devices employees are allowed to perform remote work can save the company from massive security issues in the weeks to come.
These policies and rules should explicitly mention things like password policies, any 2FA/MFA solutions in active use, and the importance of locking or logging out of any company devices whenever they step away from them. GPO’s should enforce automatic locking of endpoints if idle for several minutes, restriction of access to company resources to known devices only, and enforcement of software update policies.
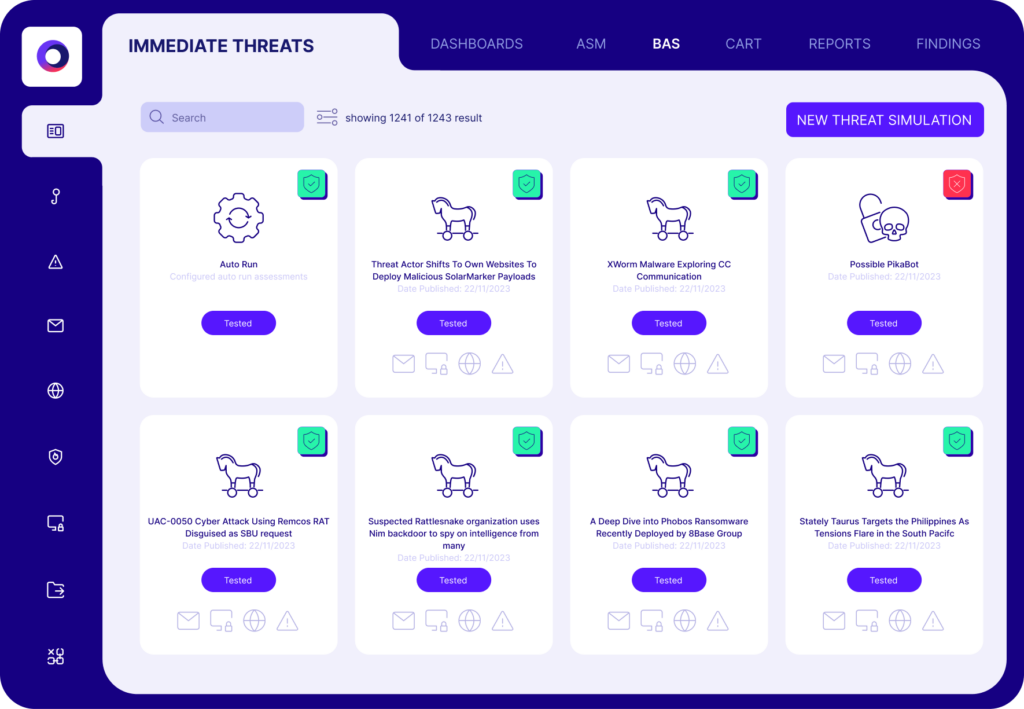
Expanded Testing
As employees begin to work outside the borders of the secured company facility, testing strategies to confirm proper security control effectiveness also must change. Cymulate’s Email Gateway, Phishing Awareness, Endpoint Protection, and Immediate Threats Intelligence simulation tools can work equally effectively when the simulations are performed outside the corporate network as they do internally.
Testing should be accelerated during these troubling times in light of new corona-related malware and phishing campaigns.
See how you can test the effectiveness of your security controls against a new immediate threat.
Placing an Agent on a remote device can extend the testing strategy beyond a controlled network and ensure that the policies and tools you are putting in place are working as expected. Combined with spot-checking that employees are using approved devices and connecting via VPN - and that their endpoint defenses are kept up to date - you can ensure that your security controls are just as effective with a distributed workforce as with a traditional concentrated workforce.
Continuous Security Testing
Adjusting to the imminent reality of working from home (at least for the foreseeable future) might seem a bit inconvenient, but it’s reassuring to know that continuous security testing can be performed remotely without the need to travel or leave the comfort of your home. SaaS-based Breach and Attack Simulation can be done independently, anytime, anywhere.
With just a few clicks, Cymulate challenges your security controls by initiating thousands of attack simulations, showing you exactly where you’re exposed and how to fix it—24/7 regardless of where you are. Whether you’re working from the comfort of your living room, at a local café, or even while relaxing on the beach.
