How to Harden Security Posture with Shrinking Security Budgets
Navigating Financial Constraints in Cybersecurity
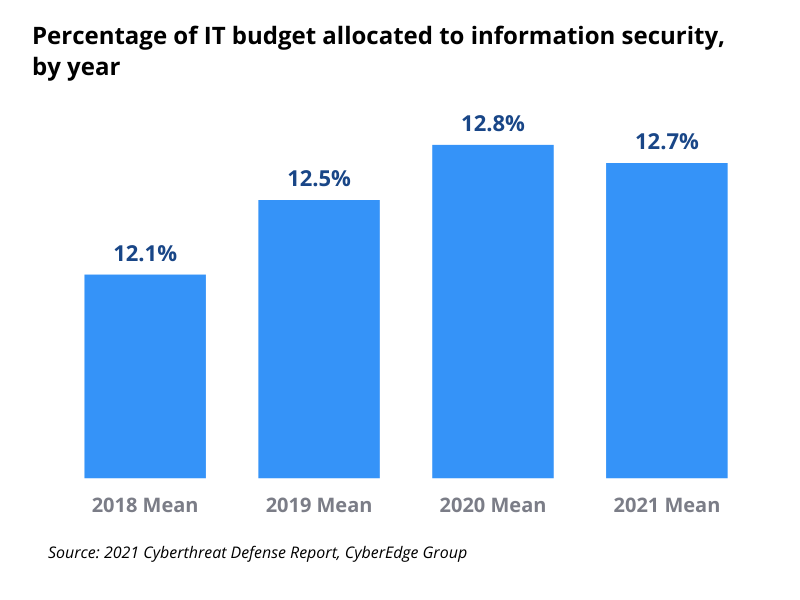
Between the rising price of fuel, persistent inflation, global supply chain challenges, and ongoing economic uncertainties, budget cuts are becoming inevitable. Cybersecurity budgets will not be spared, but the expectation to maintain a robust security posture remains. Security leaders, CISOs, and SOC managers must optimize existing resources and justify expenses while preventing security posture drift.
Strategies to Harden Security Posture on a Tight Budget
The first step to hardening your security posture is to understand exactly how easy or, hopefully, difficult it is for cyber attackers to gain an initial foothold into your infrastructure and progress laterally and vertically once they are in.
The frantic pace of threat landscape expansion and the frequent new deployments typical of agile methodology have drastically reduced the time validity of periodic penetration tests, due to their resulting rapid obsolescence.
As a result, defensive teams have to rely on monitoring tools to maintain visibility and assess security posture health. Yet, according to a recent Trend Micro report, the average of 29 monitoring tools (46 for organizations with over 10k employees) used by defensive teams turn into an unmanageable tool sprawl in more than half of the cases.
Though daunting at first glance, this situation can actually be rapidly and considerably improved, both in terms of risk reduction and cost optimization. Emerging comprehensive adversarial technologies eliminate overlapping security solutions lowering your budget without harming your security posture.
How to Harden Security Controls and Eliminate Gaps
Security gaps that weaken your security posture hide in several places, from unmonitored shadow IT to poorly configured security controls. Instead of adding more detection tools that increase complexity and false positives and completely ignore unmonitored exposed assets, it is far more efficient to continuously check the comprehensiveness of your defensive array and the performance of its security controls.
Today, this can be done quite easily with automated security posture validation tools that scour the internet to uncover exposed assets or run comprehensive sets of production-safe attacks to test the permeability of your security controls configuration. These assessments can be integrated with your existing defensive tools, which clearly and exhaustively identify which of your solutions detected, stopped, or mitigated which attacks, and which attack partially or entirely bypassed your security controls.
Armed with a map of the security gaps in your infrastructure, you can use the tool’s mitigation recommendations included in assessment reports to close them. As these assessments are automated, they can be run at no extra cost for each new deployment or to test resiliency to emerging threats. In addition, the correlation between the attacks’ success rate and the identification of each individual solution in detecting and stopping them identifies overlapping and missing capabilities.

With that information, rationalizing the tool stack is just a question of eliminating tools with overlapping capabilities and identifying missing ones. Combined with tightening security control configurations, the resulting tool stack rationalization has the added benefit of reducing complexity, streamlining the analyst's job and saving time, and shrinking the number of false positives, reducing the risks associated with alert fatigue.
This continuous security validation process facilitates risk reduction, minimizes the risk of unnoticed security drift, and even streamlines adjusting to your company’s evolving risk appetite reflecting fluctuating business imperatives.
Cutting down your cybersecurity budget
Once the tool stack is rationalized from a security posture hardening perspective, the cost-cutting results abound.
1. Directly reducing cybersecurity expenses
The most obvious budget reduction is, of course, eliminating overlapping tools and their associated costs. That alone can already significantly reduce expenses and is a no-brainer. Another way to reduce the budget is to replace expensive periodic penetration tests with more affordable – and more efficient – continuous security validation tools.
2. Indirectly reducing cybersecurity expenses
Factoring in the increased efficiency and hardened security posture, waterfall effects can open the door to additional cost-cutting opportunities. Every cybersecurity team is different, so those opportunities will vary between organizations but here are some ideas of waterfall benefits that can translate into reducing costs.
- By facilitating the work of cybersecurity analysts, the reduction in complexity focuses analysts’ attention on addressing actual issues instead of trying to find the pertinent data in the mass of irrelevant and often redundant information, eliminating wasted time.
- The reduced number of false positives not only minimizes alert fatigue but also cuts down on man-hours wasted on filtering through unnecessary data.
- Especially at a time when compliance regulators are increasingly focusing on assessment and resilience, continuous security validation reports thoroughly document both these aspects, cutting down on compliance procedures.
- Increased and continuously documented resilience can reduce cyber insurance premiums.
3. Sharing costs with the IT department
Adopting continuous security validation solutions enables using the Contextual Vulnerability Management (CVM) tool that can reduce the vulnerability patching workload by up to 50%, simply by assessing if compensating security controls effectively stop attacks. As patching vulnerabilities typically fall under the IT department’s responsibilities, the considerable potential workload reduction might induce them to pitch in.
There are other ways to use continuous security validation tools, such as the Cymulate’s Exposure Management and Security Validation platform can reduce costs for other departments, i.e., optimizing security vs. operability trade-off, preserving business continuity, automating part of compliance documentation, so opportunities to share costs with additional departments might be considered.
Cybersecurity budget breakdown
Though the primary role of cybersecurity is to stabilize security posture, the business value of their operation is not limited to risk reduction and compliance. The integration of comprehensive continuous security validation solutions extends additional business value for cybersecurity even as it improves and strengthens security posture despite cost reductions.
When structuring your cybersecurity breakdown, including both risk reduction impact and business value across the board might even impact the scope of the required budget reduction.
To see how the Cymulate Exposure Management and Security Validation platform can make all the difference for your enterprise, book a demo today