Alert Fatigue
Alert Fatigue in Cybersecurity: How to Tackle Notification Overload in the SOC
Alert fatigue occurs when security teams are inundated with so many alerts that they become overwhelmed and desensitized. In our current SOC environments, tools including SIEMs, EDR, IDS and vulnerability scanners constantly generate alerts, many of which are false positives or duplicates.
This flood of notifications, often driven by overly sensitive detection rules and siloed systems without centralized prioritization, makes it increasingly difficult to distinguish real threats from noise.
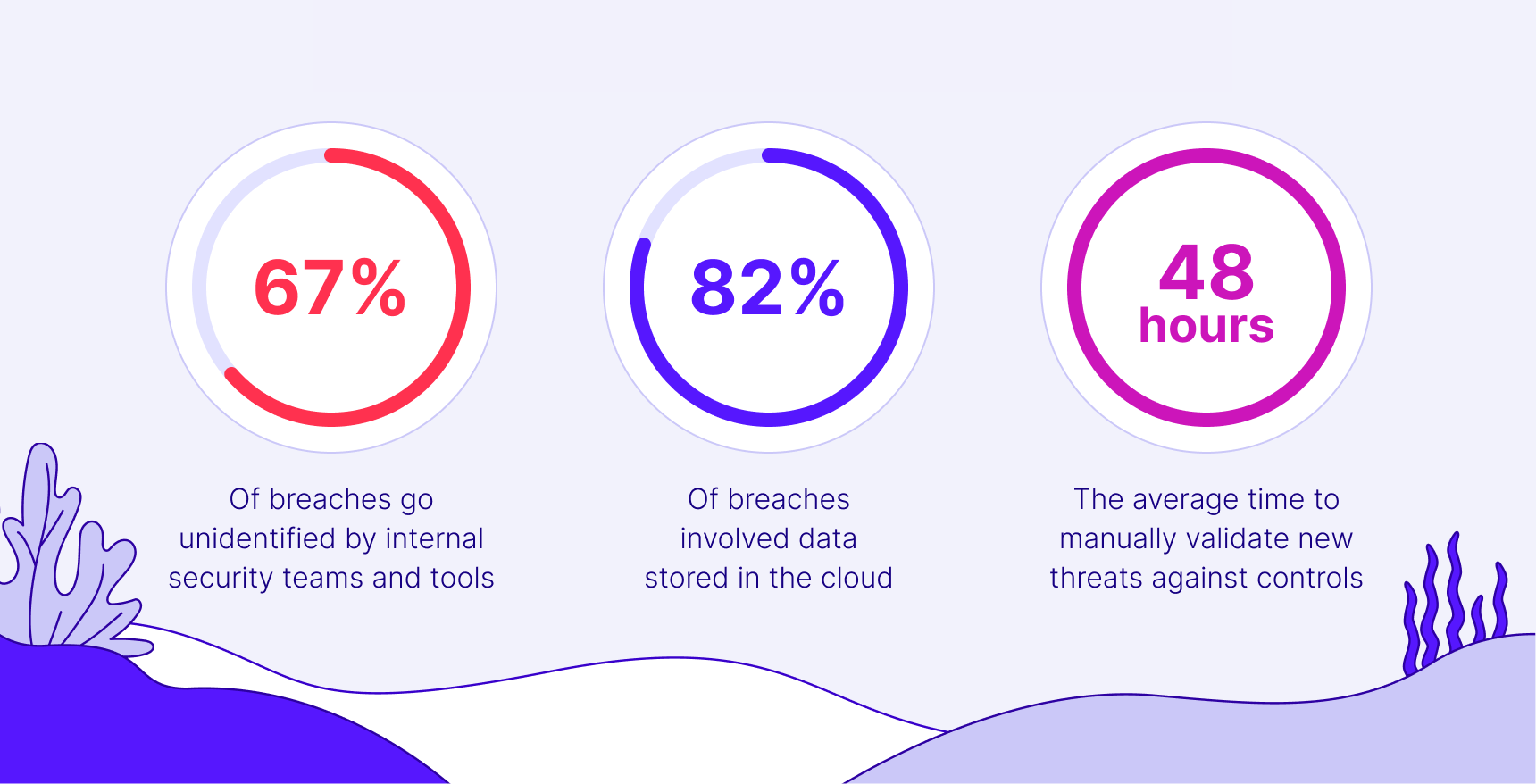
The impact is serious: analysts may start ignoring alerts or silencing systems just to cope, creating dangerous blind spots. Industry data shows that 25–30% of alerts go uninvestigated due to overload. For CISOs and SOC leaders, the result is slower response times and increased risk of missing critical threats.
What Is Alert Fatigue in Cybersecurity?
In a typical Security Operations Center (SOC), tools like firewalls, IDS/IPS, EDR/XDR, vulnerability scanners, cloud monitors and especially SIEMs generate thousands of daily alerts across various categories, failed logins, port scans, malware activity and more. Alert fatigue refers to a state where cybersecurity analysts become overwhelmed by the sheer volume of alerts, making it difficult to distinguish real threats from harmless noise.
Though these alerts are intended to enhance visibility, they often create an environment where meaningful signals are lost in the noise. For instance, an average enterprise SOC processes over 11,000 alerts daily. Analysts are expected to manually investigate each one, a mentally exhausting process that contributes to burnout and overlooked threats.
A notable example of alert fatigue in action is the 2013 Target breach. Target’s security tools flagged malware activity early on, but the alerts were buried in a sea of routine warnings. SOC analysts, having seen similar alerts repeatedly without issue, deprioritized them. This misjudgment gave attackers enough time to steal data from over 40 million payment cards.
Reports confirm that Target’s tools worked as intended, but the flood of alerts led analysts to overlook the ones that truly mattered. By the time the incident was discovered, the damage was already done.
This incident reveal a harsh reality: alert fatigue doesn’t just reduce efficiency; it can directly enable a breach. Whether it’s a headline-grabbing incident or an unnoticed compromise, the root cause often isn’t a failure of detection technology. It’s the inability to act on alerts buried in overwhelming volume.

Key Causes of Alert Fatigue
There are several common sources of alert fatigue, and it’s important to understand and identify them in your organization. These include:
- High False Positive Rates: Poorly tuned detection rules and default configurations often trigger alerts for benign activities. In many organizations, more than 50% of alerts are false positives, leading analysts to dismiss real threats under the assumption that “it’s probably nothing.”
- Multiple Overlapping Tools: Modern SOCs rely on numerous unintegrated tools. A single incident may trigger alerts from several systems such as an IDS, endpoint agent and cloud tool, creating redundant noise. This fragmented visibility hinders effective response and increases cognitive load.
- Lack of Context or Prioritization: Generic alerts like “suspicious activity detected” force analysts to investigate without clear direction. When all alerts appear equally critical, teams waste time on minor issues while high-risk incidents slip by unnoticed. Lack of contextual detail and risk scoring severely impairs triage.
- Inadequate Staffing and Processes: Organizations with immature response workflows or limited analyst coverage suffer the most. Without proper triage systems or enough trained personnel to handle 24/7 monitoring, alert queues grow unmanageable. Overburdened teams are more likely to make mistakes or miss critical events entirely.
Consequences and Risks of Alert Fatigue
Alert fatigue doesn’t just overwhelm analysts, it weakens the entire cybersecurity posture of an organization. When security teams are inundated with unfiltered alerts, the effects span from operational inefficiencies to long-term strategic risks.
Missed Threats and Increased Breach Risk
The most immediate danger is that real attacks go unnoticed. When analysts are forced to triage thousands of alerts, genuine threats can be missed or deprioritized. This increases dwell time, the period attackers remain undetected in a system, giving them ample opportunity to escalate privileges, spread malware, or steal data.
On average, it takes around 277 days to identify and contain a breach. The longer the delay, the higher the cost.
False Sense of Security
Ironically, too many alerts can lead teams to feel falsely reassured. As alert fatigue grows, teams may assume their security stack is working well simply because “nothing critical has happened,” even while serious threats are being ignored. This complacency creates dangerous blind spots.
Slower Response and Longer Dwell Time
Even when critical alerts are eventually addressed, the lag in response caused by fatigue can allow threats to escalate.
A malware alert buried under false positives might take hours or days to investigate. That delay can turn a containable incident into a full-blown compromise. Alert fatigue inflates both mean time to detect (MTTD) and mean time to remediate (MTTR).
Higher Likelihood of Breaches
Multiple studies confirm that alert fatigue leads directly to breach risk. Up to 30% of alerts are never investigated, and among the 17,000 malware alerts an organization may receive weekly, only 19% are genuine.
With so much noise, even those critical few can be lost, making it statistically likely that at least one real threat slips through each week.
Analyst Burnout and High Turnover
On the human side, alert fatigue takes a heavy toll. Analysts tasked with 24/7 triage of mostly false positives face stress, fatigue, and frustration. Many report feeling like they’re "chasing ghosts" rather than doing meaningful security work.
Surveys show two-thirds of cybersecurity professionals experienced burnout in a year, and over half cite alert overload as the top stressor. High turnover disrupts SOC operations and leads to loss of institutional knowledge, creating a cycle of understaffing and worsening fatigue.
Reduced Productivity and Wasted Resources
Skilled security professionals should be threat hunting, not manually dismissing false alerts. Yet, many spend 25–30 minutes per false positive, adding up to hours of wasted time weekly. Globally, the cost of manual alert triage has been estimated at $3.3 billion annually. This inefficiency drains budgets and misuses expert talent.
Compliance Failures and Reputation Damage
Missed alerts don’t just pose security risks, they can lead to legal and reputational consequences. Regulators often require prompt breach detection and reporting.
If ignored alerts result in compromised customer data, companies may face penalties or fines. Worse, public trust can erode, especially if it’s revealed that the breach was due to internal oversight.
8 Best Practices for Reducing Alert Fatigue
Reducing alert fatigue requires a coordinated effort across technology, processes and people. Below are key strategies organizations can implement to restore focus and efficiency in the SOC.
1. Prioritize and Categorize Alerts
Not all alerts carry equal weight. Implement a severity-based system—Critical, High, Medium, Low—to help analysts triage intelligently.
High-impact incidents like active breaches should trigger immediate response, while routine policy violations can be handled later. Tie prioritization to asset value; alerts on sensitive systems should be elevated. Runbooks for each alert tier help ensure swift, consistent action.
2. Tune Detection Rules to Reduce False Positives
Constant review and adjustment of alert rules is essential. Identify noisy alerts and refine or suppress them. For example, if internal port scans trigger frequent false positives, create exceptions or adjust thresholds.
Focus SIEM ingestion on high-value logs, just 5–15% of data often yields the most actionable intelligence. A regular alert review cadence keeps your environment finely tuned and your analysts focused on real risks.
3. Correlate and Aggregate Alerts
Use correlation rules to group related alerts into single incidents. A malware infection may trigger alerts across multiple tools, consolidating them prevents duplicated efforts.
SIEMs and XDR platforms often offer built-in correlation capabilities that can be tailored to your environment. Grouping alerts by user, IP, or endpoint reveals context and reduces noise.
4. Automate Triage and Response
Security automation tools like SOAR can offload repetitive triage and enrichment tasks. Playbooks can automate actions such as isolating hosts or querying threat intel.
Machine learning can help filter out known false positives. Even lightweight automation, like auto-prioritization scripts or alert summarization via chatbot can enhance efficiency and reduce fatigue.
5. Strengthen Incident Response Processes
A robust, well-documented incident response plan is critical. Define clear roles, escalation paths and standard procedures for common alerts. Conduct regular drills and tabletop exercises to keep teams prepared.
Efficient, familiar workflows reduce decision fatigue and help ensure no alert is overlooked during high-volume periods.
6. Validate and Prioritize Exposures
Rather than reacting to every alert, reduce the volume at the source. Exposure validation tools can identify which vulnerabilities are exploitable in your environment.
Prioritize patching based on real-world risk, not theoretical severity. Validating exposures narrows the alert surface, improves focus, and aligns response efforts with true business impact.
7. Optimize Monitoring and Logging
Avoid alert overload by tailoring your monitoring to your actual threat model. Disable noisy or low-value alert rules and focus on logs that yield useful signals, such as authentication and critical server logs.
Continuously measure alert effectiveness: if a rule has a 0% true positive rate over time, consider removing it. Offload less critical monitoring tasks to managed services when possible.
8. Invest in Analyst Training and Wellbeing
Empower your team through continuous training in triage, tooling, and threat analysis. Encourage knowledge sharing to help analysts recognize recurring false positives and reduce duplicate effort.
Address burnout proactively with rotations, breaks, and support systems. Motivated, well-trained analysts are better equipped to manage workload and improve alert handling.
Cymulate Helps You Cut Through Alert Fatigue and Focus on Real Threats
Cymulate Validation-led Exposure Management provides a unique exposure prioritization based on robust Security Control Validation and Attack Simulation expertise, which allows to increase the security operation efficiency and save time.
With automated and robust automated remediation, Cymulate will increase efficiency, save more time, and reduce frustration of the security operation from alert fatigue, and allows to track and measure the ROI of the security defenses built around the organization.
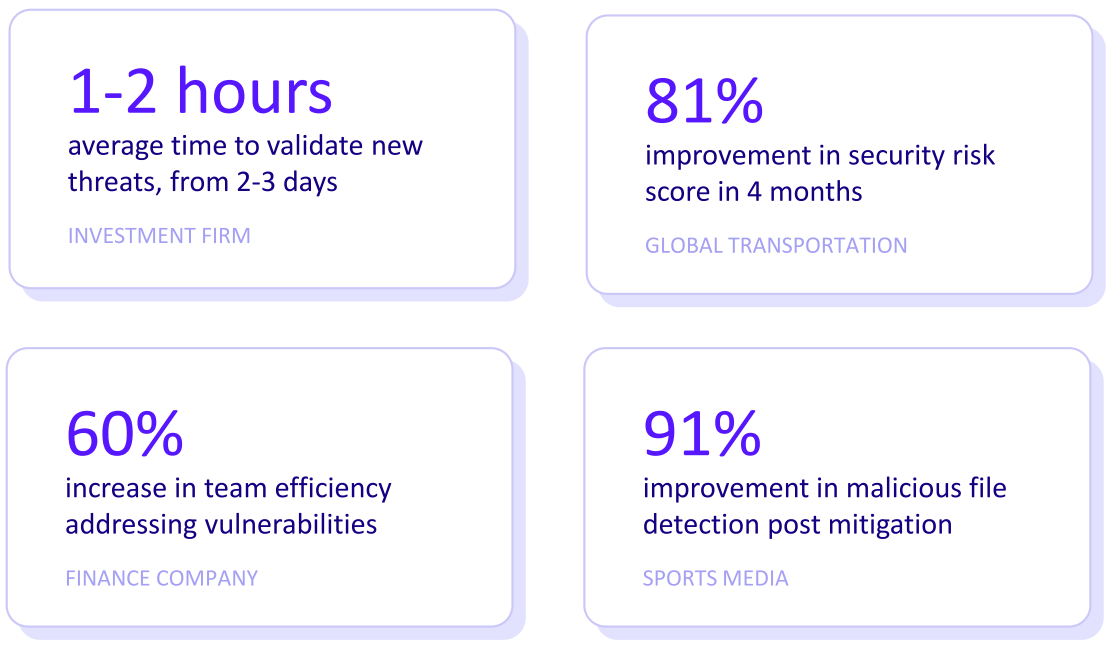
Exposure validation and prioritization is central to the Cymulate approach. Rather than treating every vulnerability as critical, the platform simulates real-world attacks to determine which exposures are actually exploitable.
This filters out non-critical findings, enabling your SOC to prioritize alerts that represent real risk. Fewer false alerts means less noise and more focus.
Security control validation ensures tools like SIEMs and detection rules are working as intended. The platform continuously tests SIEM logic and correlation rules, identifying broken detections, excessive noise, and blind spots.
This tuning process reduces false positives and improves alert accuracy, transforming your detection stack into a high-signal environment analysts can trust.
With continuous automated testing, Cymulate validates controls against evolving threats on an ongoing basis. This helps detect gaps before attackers exploit them, reducing surprise alerts and keeping your alert pipeline consistent.
It also adjusts for environmental changes, such as new systems or configurations, ensuring your security posture remains aligned with alerting goals.
The platform also enhances alerts with contextual intelligence, helping analysts understand why an exposure or detection is significant. Instead of raw data, teams receive actionable alerts tied to threat actor techniques, exploit paths, or business-critical assets. This reduces cognitive load and enables faster, more informed decisions.